Hi! Do you need help with this guide?
Hi! Do you need help with this guide?
Thank you for your response. We will get back to you soon.
Something went wrong. Please submit your query again
Recommended Add-Ons

Two Factor Authentication
Enable 2FA/MFA for users & groups and let users configure 2FA during their first login.
Know More
Bulk User Management
Bulk Activate, De-activate and Delete inactive users and save the license for Crowd Server.
Know More
Jira Crowd Connector
Crowd SAML & Connectors is the only SSO solution for Crowd SSO-enabled Atlassian apps.
Know More

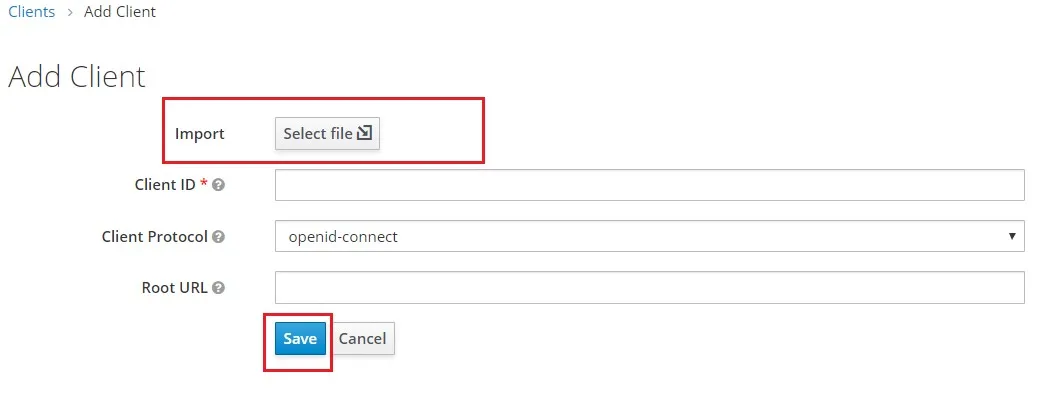
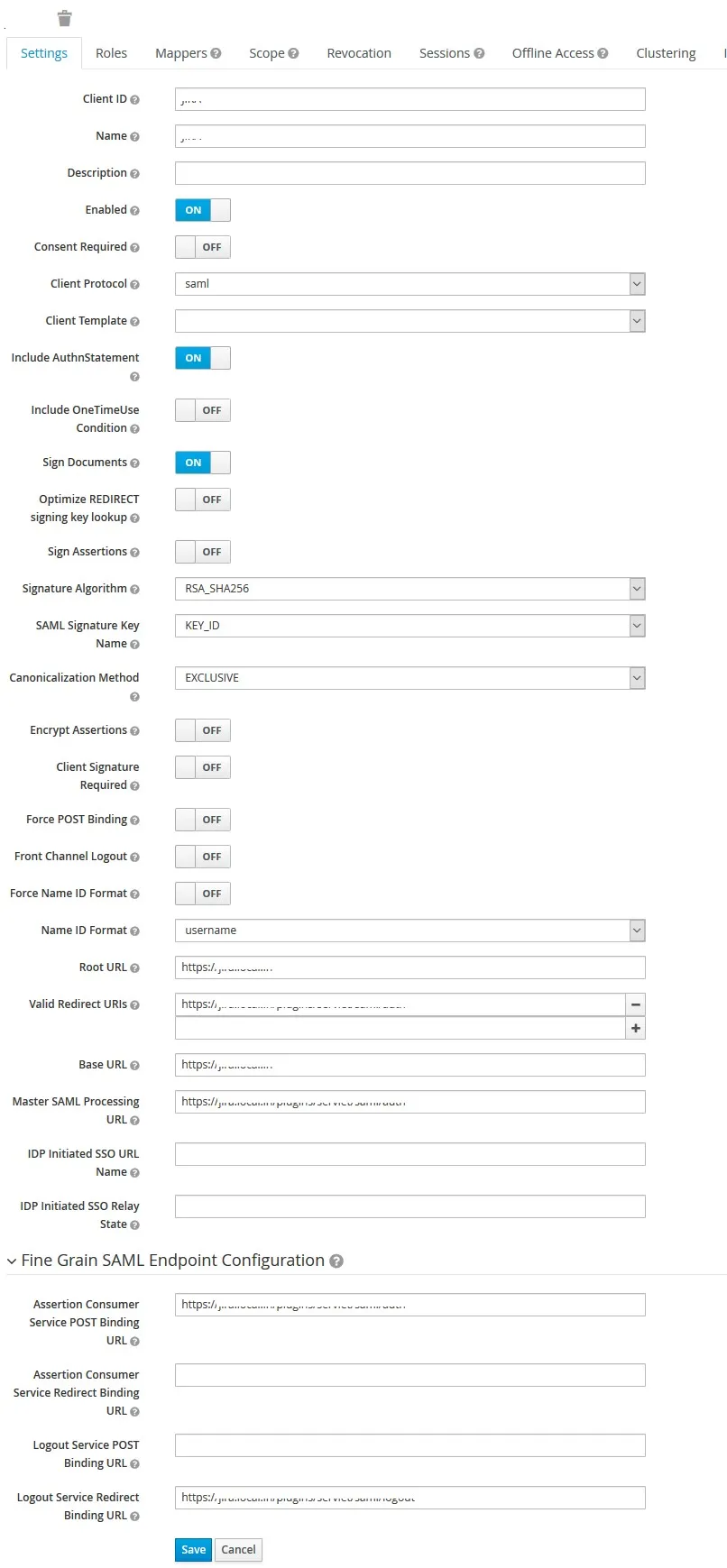
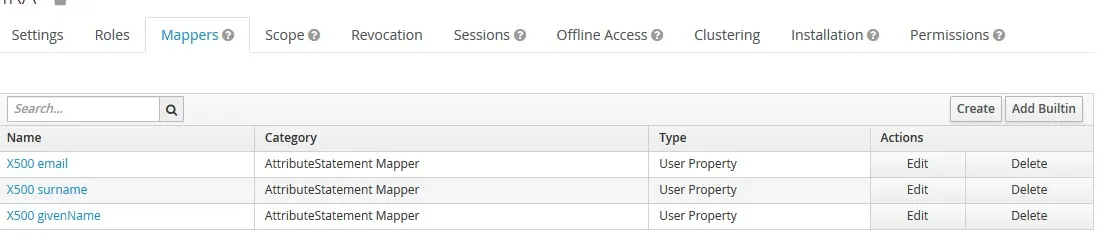
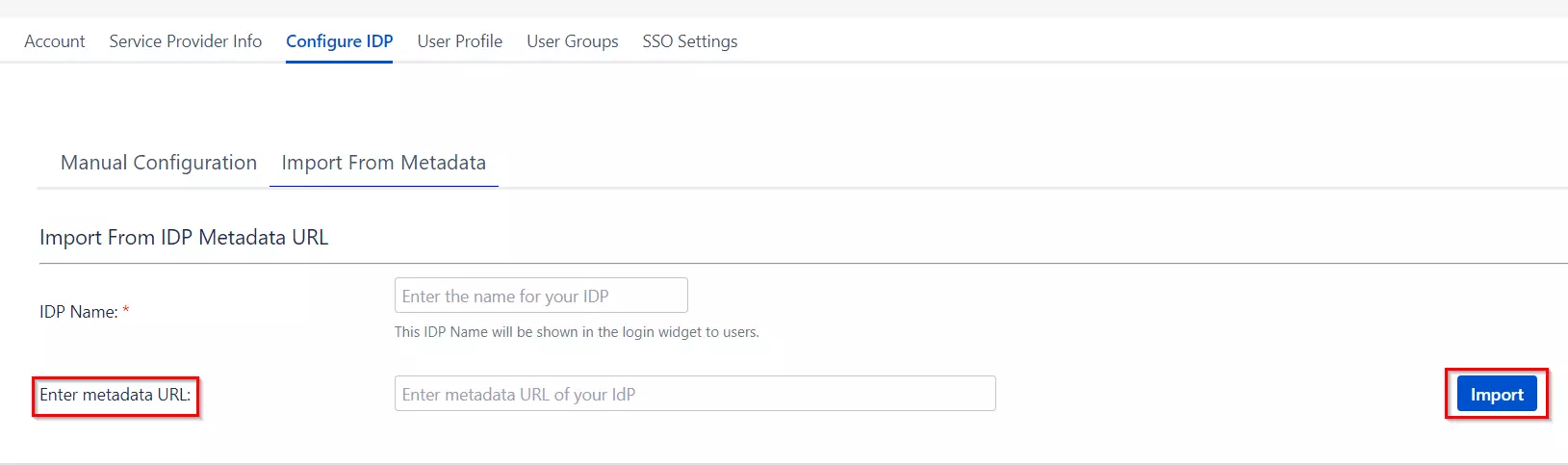
 Method 1: Upload SP Metadata
Method 1: Upload SP Metadata