Confluence SAML app gives the ability to enable SAML Single Sign On for Confluence Software. Confluence Software is compatible with all SAML Identity Providers. Here we will go through a guide to configure SSO between Confluence and your Identity Provider. By the end of this guide, users from your Identity Provider should be able to login and register to Confluence Software.
Pre-requisites
To integrate your Identity Provider(IDP) with Confluence, you need the following items:
- Confluence should be installed and configured.
- Admin credentials are set up in Confluence.
- Confluence server is https enabled (optional).
- Valid Confluence Server and Data center Licence.
Download And Installation
- Log into your Confluence instance as an admin.
- Navigate to the settings menu and Click Manage Apps.
- Click Find new apps or Find new add-ons from the left-hand side of the page.
- Locate Confluence SSO/ Single Sign On, SAML SSO via search.
- Click Try free to begin a new trial or Buy now to purchase a license for Confluence SSO/ Single Sign On, SAML SSO.
- Enter your information and click Generate license when redirected to MyAtlassian.
- Click Apply license.
Step 2: Setup Confluence as Service Provider
Configure Identity Provider
Step 1. Adding IDP settings in add-on
- With the information you have been given by your IDP, you can configure IdP settings in 3 ways.
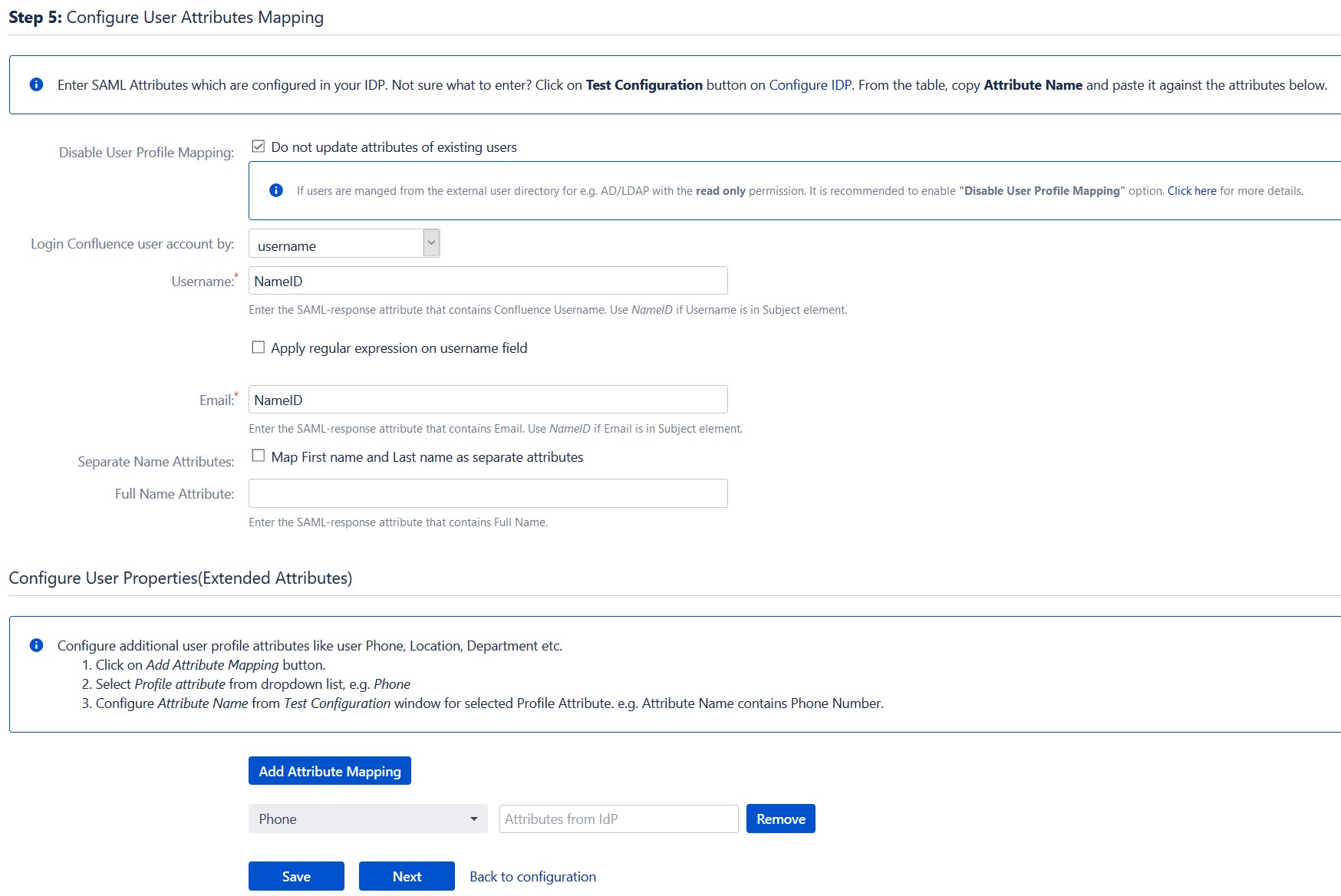
Step 3: Setting up Confluence user profile attributes
We will be setting up user profile attributes for Confluence. If your users are stored in a directory that is Read Only, please check Disable User Profile Mapping in User Profile tab and follow steps given in Matching a User.
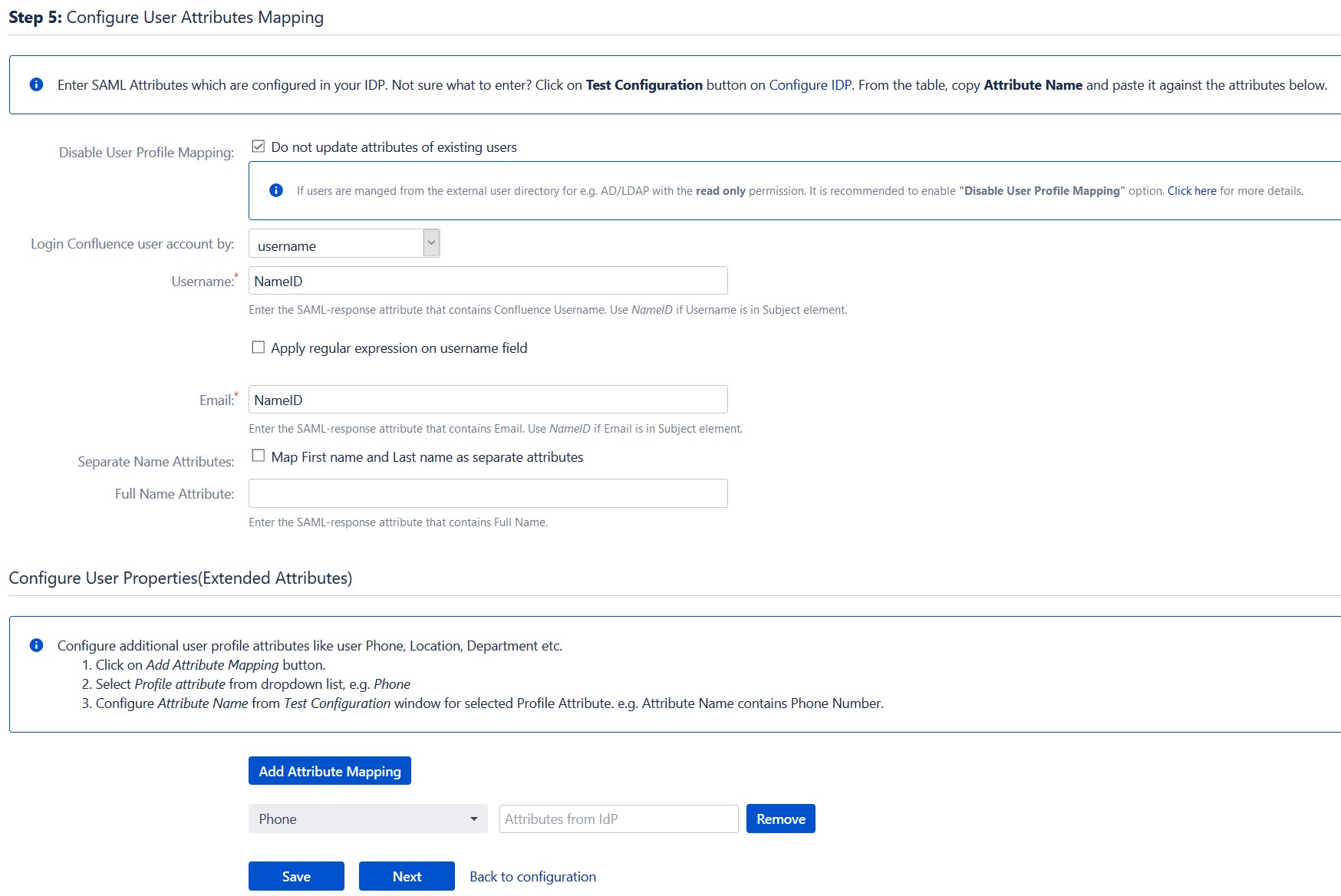
a. Finding correct attributes
- Go to Configure IDP tab. Scroll down and click on Test Configuration.
- You will see all the values returned by your IDP to Confluence in a table. If you don’t see value for First Name, Last Name, Email or Username, make the required settings in your IDP to return this information.
- Once you see all the values in Test Configuration, keep the window open and go to User Profile tab.
b. Setting profile attributes
- In this tab, fill the values by matching the name of the attribute. For instance, if the Attribute Name in the Test Configuration window is NameID, enter NameID against Username
- Setting up both Username and Email is required if you want to let users register. If you want existing users to only login, configure the attribute using which you will match user in Confluence.
c. Matching a User
When user logs into Confluence, one of the user’s data/attribute coming in from the IDP is used to search the user in Confluence. This is used to detect the user in Confluence and login the user to the same account.
- Go to User Profile tab
- Select Username or Email for Login/Search Confluence user account by
- Enter the attribute name from IDP which corresponds to Username or Email using Finding Correct Attributes.
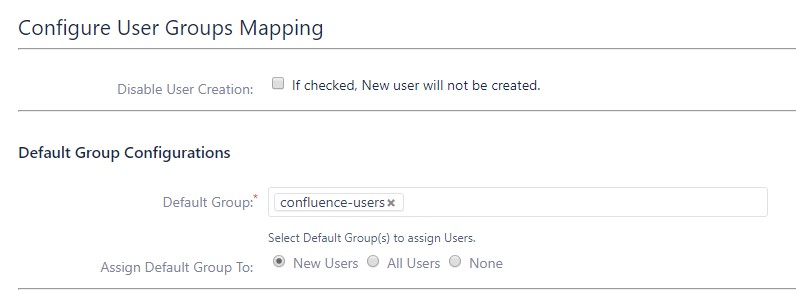
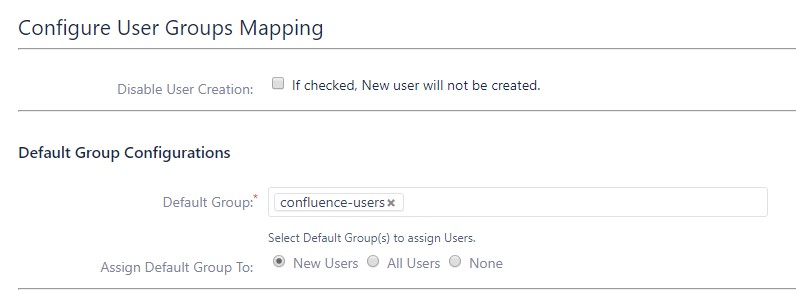
Step 4: Assigning groups to users
We will be setting up user group attributes for Confluence. If your users are stored in a directory that is Read Only, please check Disable Group Mapping in User Groups tab and skip to Setting default group.
a. Setting default group
- Select the users' Default Group in the tab User Groups. If no group is mapped, users are added by default to this group.
- You can enable default groups for All Users or New Users using the option.Select None if you don't want to assign any default group to SSO users. Using the option Enable Default Groups for.
b. Finding Group Attribute
- Just like we found Attribute Name for User Profile attributes, we find group attribute.
- Go to Configure IDP tab. Scroll down and click on Test Configuration.
- You will see all the values returned by your IDP to Confluence in a table. If you don't see value with groups, make the required settings in your IDP to return group names.
- Once you see all the values in Test Configuration, keep the window open and go to User Groups tab.
- Enter the Attribute Name of group against Group Attribute.
- Check Disable Group Mapping option if you don't want to update groups of existing users.
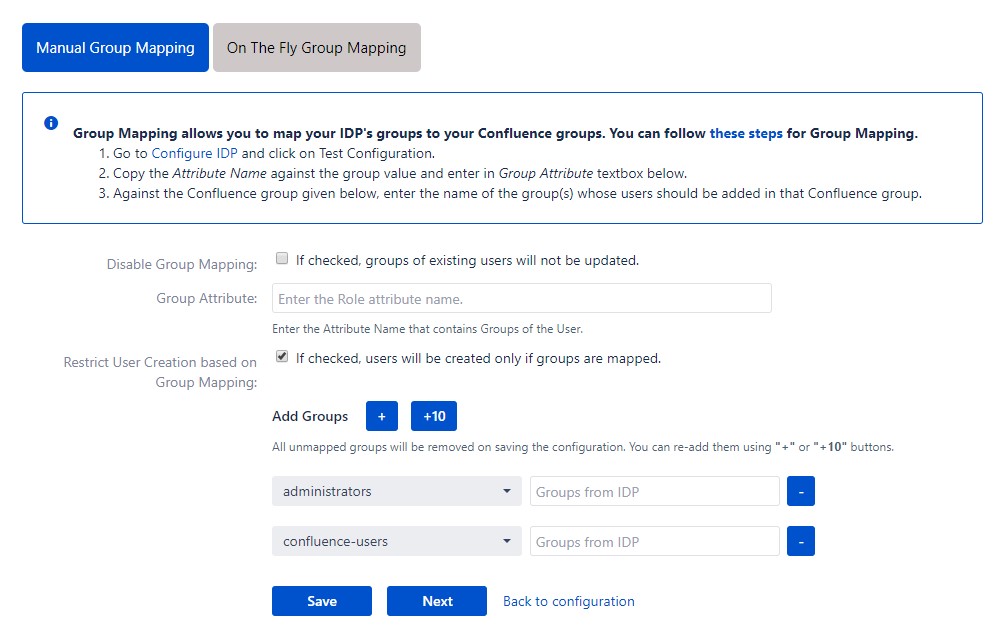
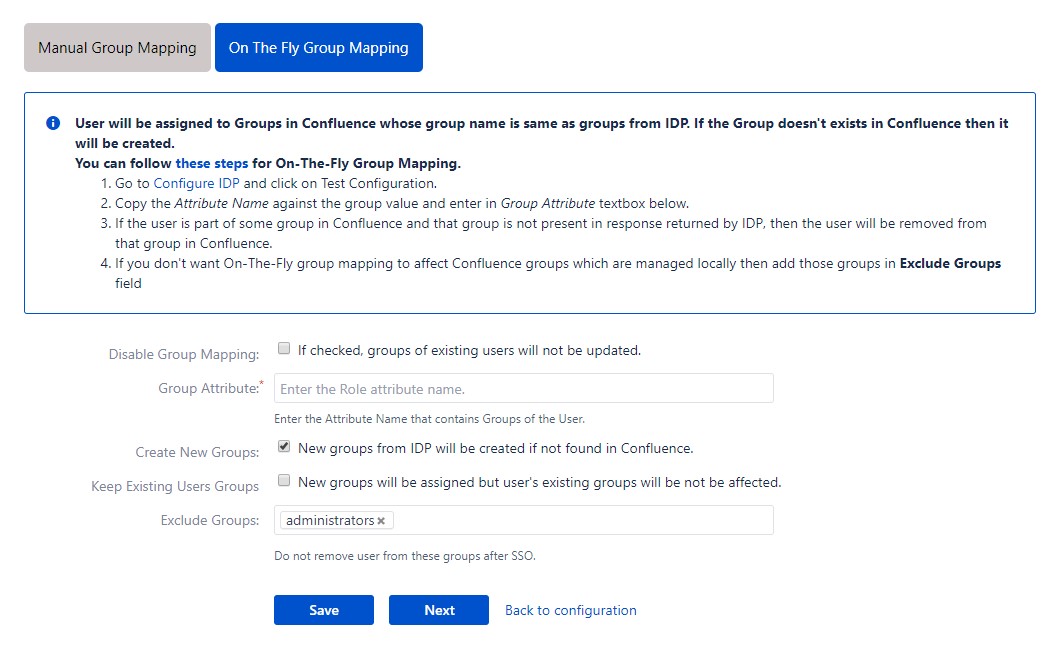
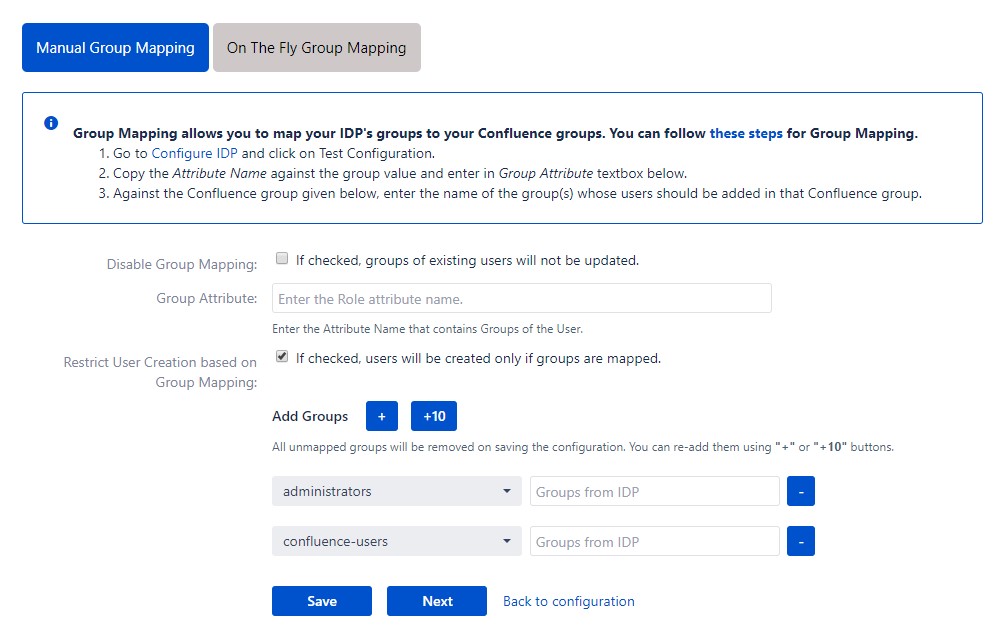
c. Group Mapping
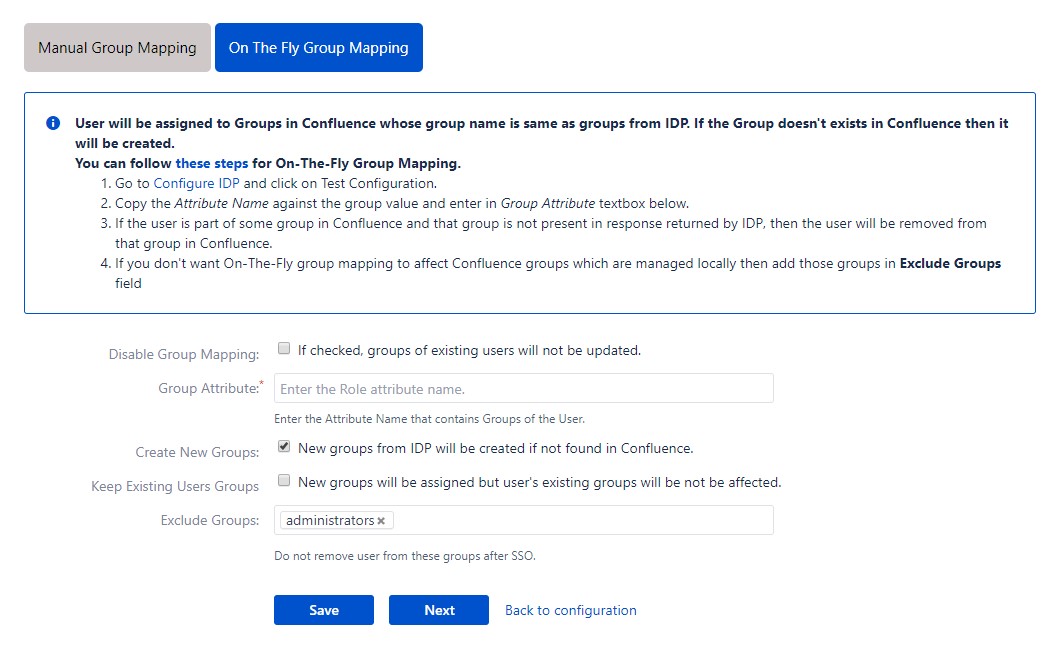
Group Mapping can be done in two ways:
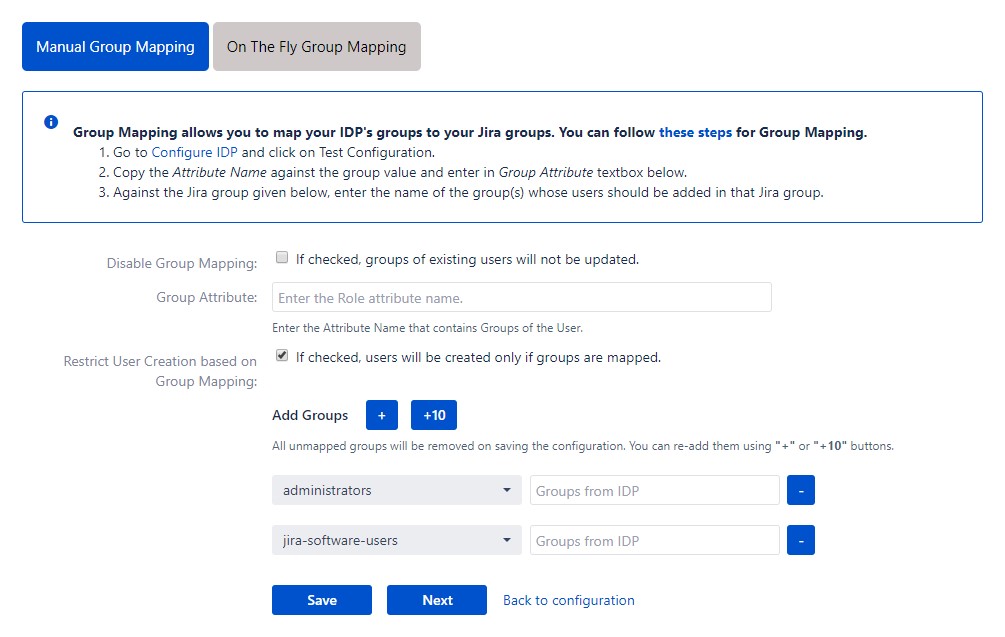
- Manual group mapping: If the names of groups in Confluence are different than the corresponding groups in IDP, then you should use Manual group mapping.
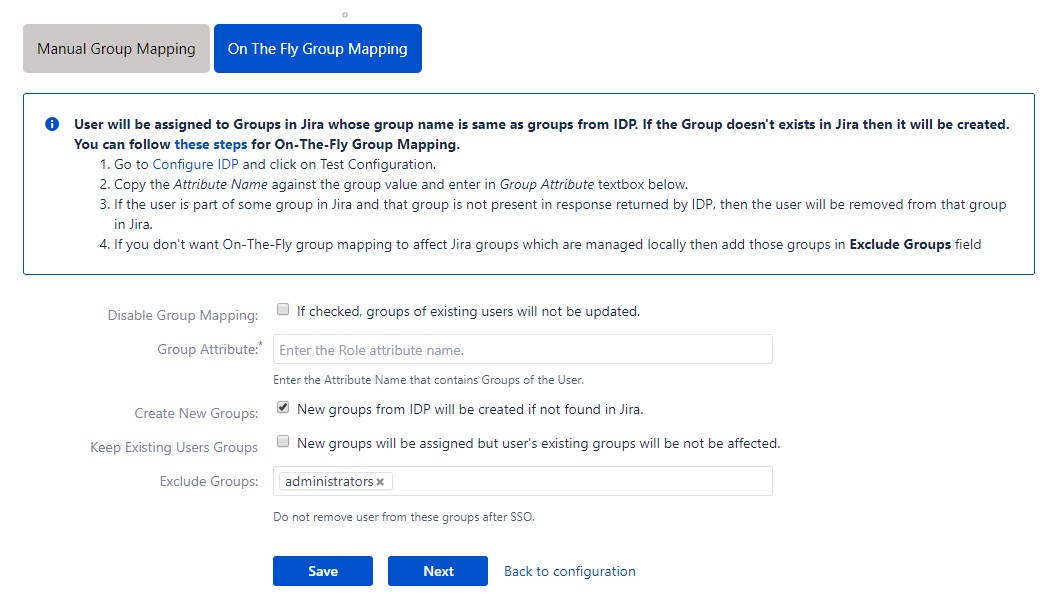
- On-The-Fly group mapping: If the names of groups in Confluence and IDP are same, you should use On-The-Fly group mapping.
I. Manual Group Mapping
- Check Restrict User Creation Based on Group Mapping option if you want new users to be created only if at least one of the user's IDP groups is mapped to a group in the application.
- For mapping, first select a Confluence group from the dropdown which lists all groups present in Confluence and then enter the name of the IDP group to be mapped in the textbox beside
- For example, if you want all users in 'dev' group in IDP to be added to confluence-users, you will need to select confluence-users from the dropdown and enter 'dev' against confluence-users.
- Use '+1' and '+10' buttons to add extra mapping fields.
- Use '-' button next to each mapping to delete that mapping.
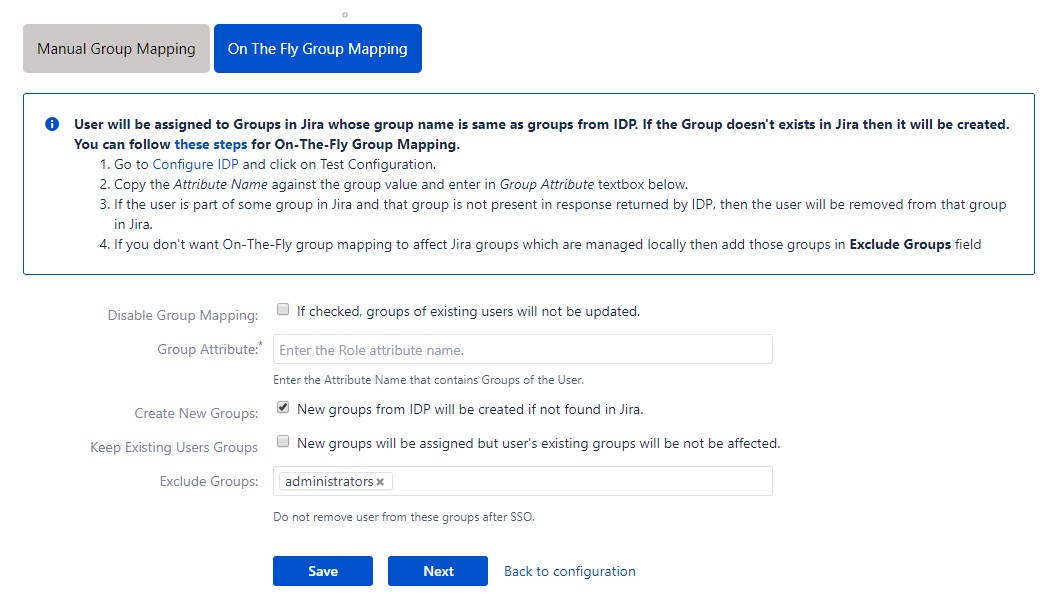
II. On-The Fly Group Mapping
- Check Create New Groups option if you want new groups from IDP to be created if not found in Confluence.
- If the user is part of some group in Confluence and that group is not present in the SAML response returned by IDP, then the user will be removed from that group in Confluence.
- If you don't want On-The-Fly group mapping to affect Confluence groups which are managed locally then add those groups in Exclude Groups field.
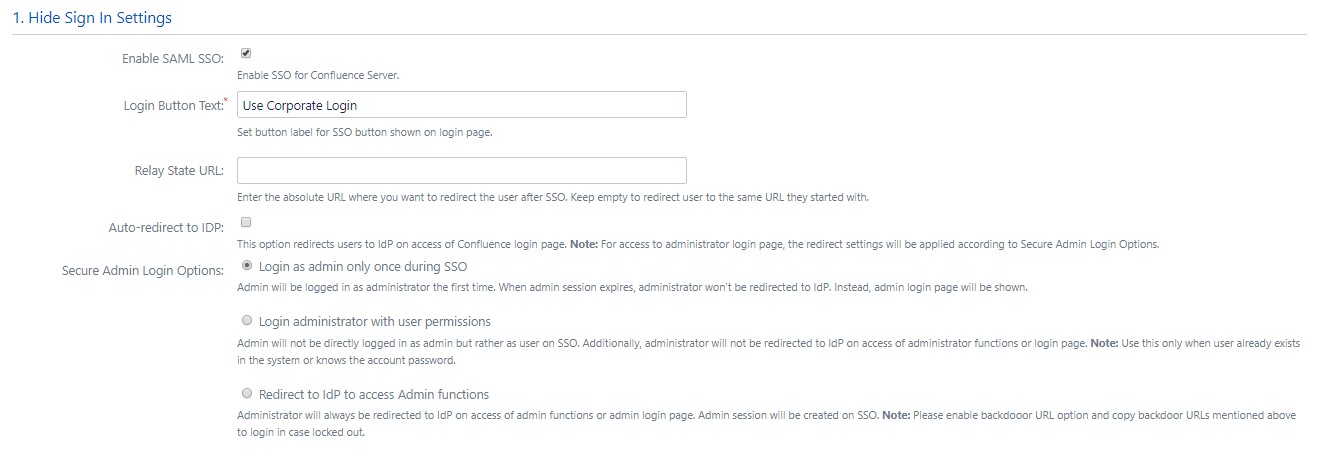
Step 5: SSO Settings
The settings in Sign In Settings tab define the user experience for Single Sign On
a. Sign In Settings
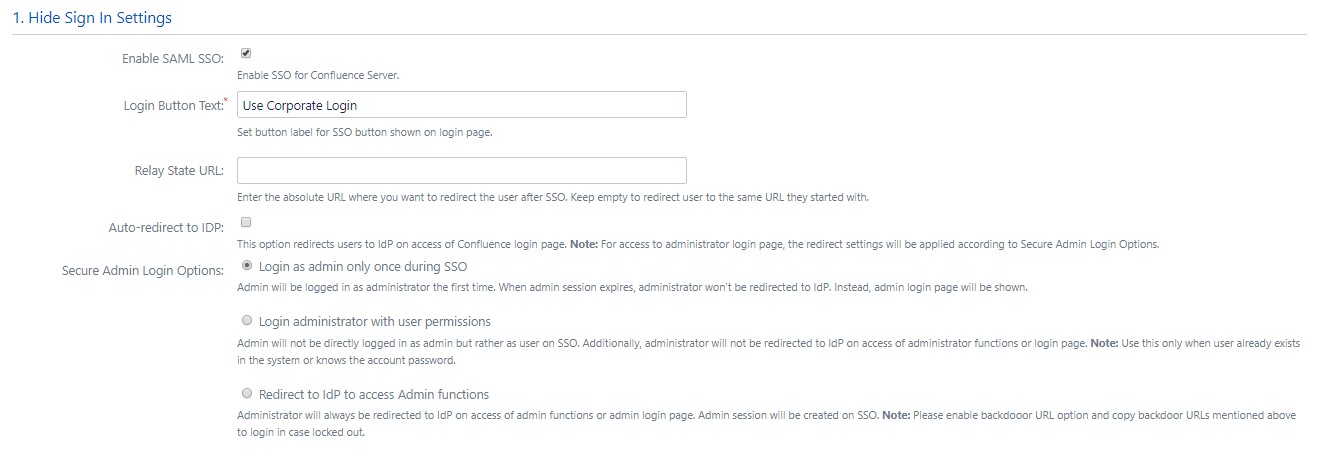
- Set button text for button on login page using Login Button Text
- Set redirect URL after login using Relay State. Keep this empty for coming back to the same page user started from
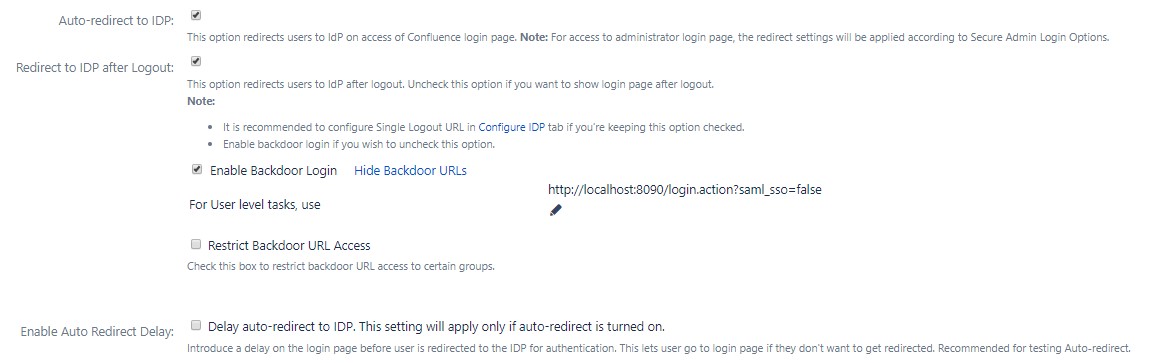
- Enable Auto-redirect to IDP if you want to allow users to login only using IDP. Enable backdoor for emergency
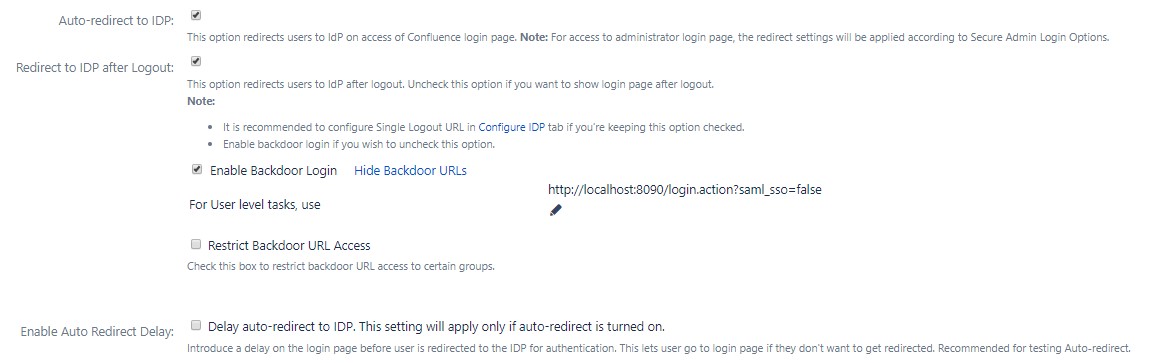
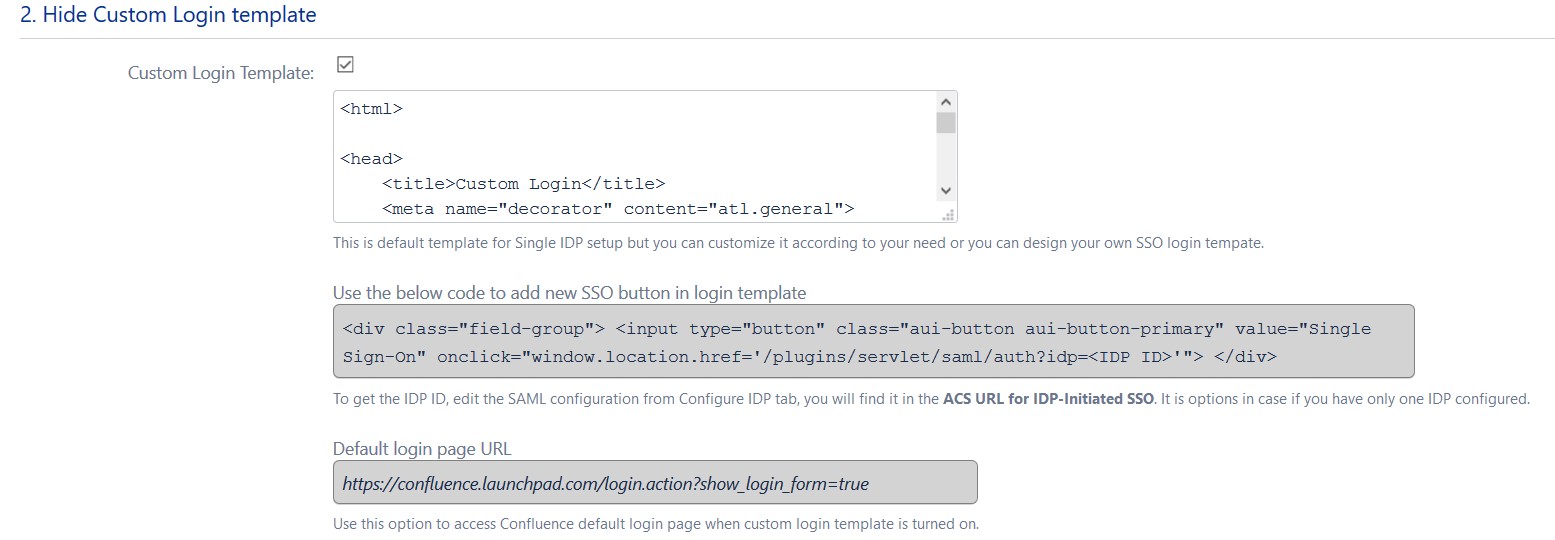
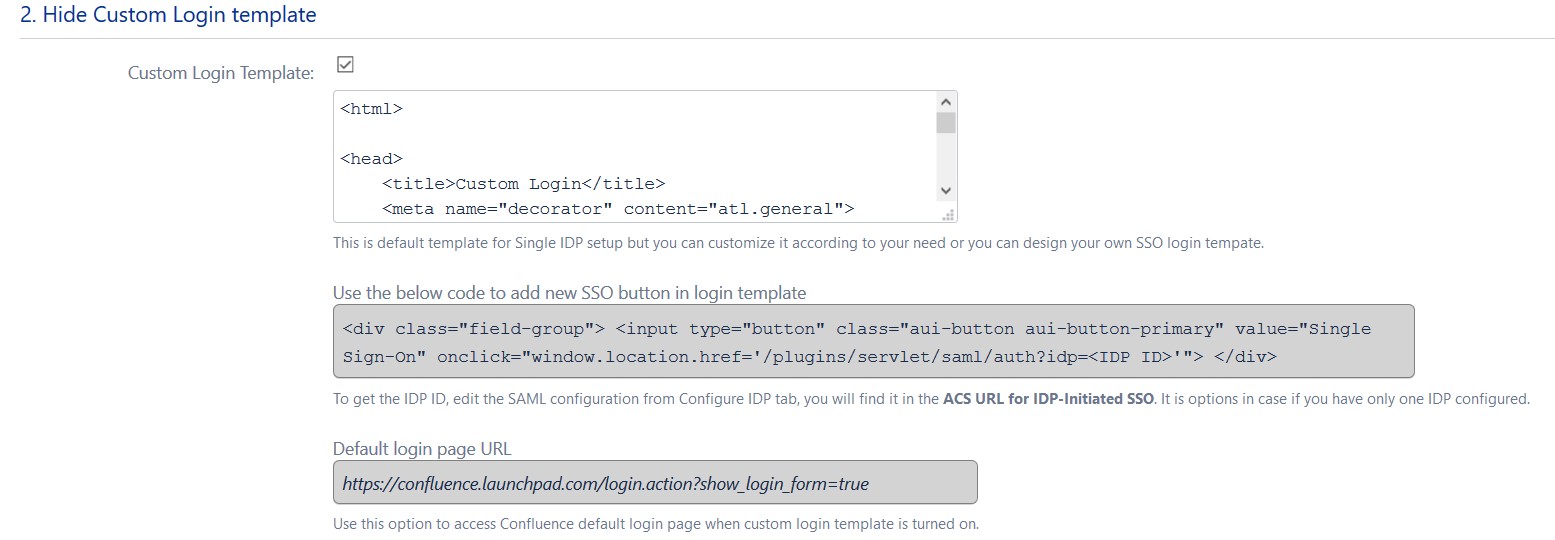
b. Custom Login Template
- Set custom login template to redirect users to a custom login page instead of Confluence default login page. This won't work if you have Auto-redirect to IDP enabled.
- Don't forget to copy default login page URL in case of emergency.
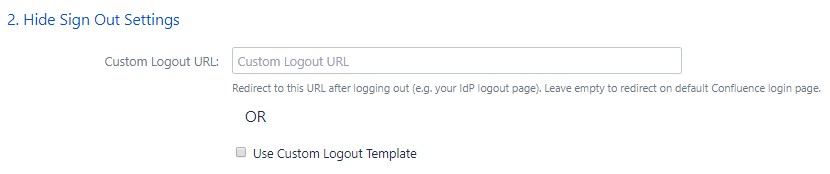
c. Sign Out Settings
- Enter a custom logout URL to redirect your users to a pre-defined logout page
- Set a custom logout template to show custom logout page to users on logout
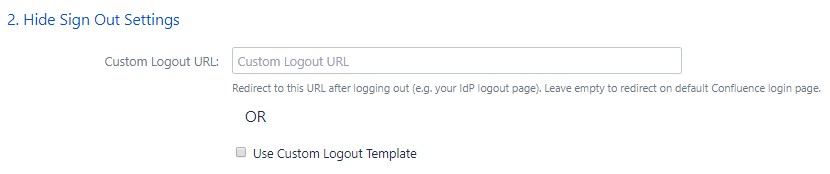
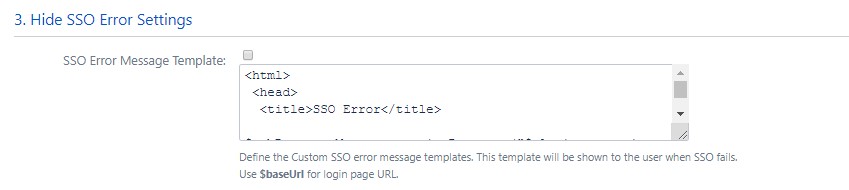
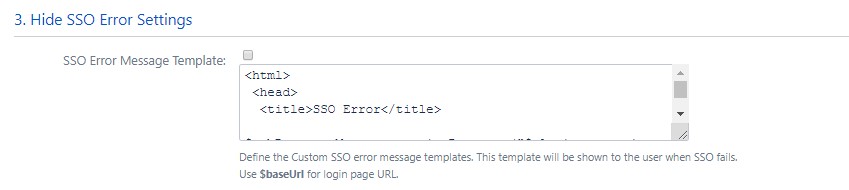
d. SSO Error Settings
- Set error template to redirect users to a custom error page instead of login page. Use this if you have Auto-redirect to IDP enabled.
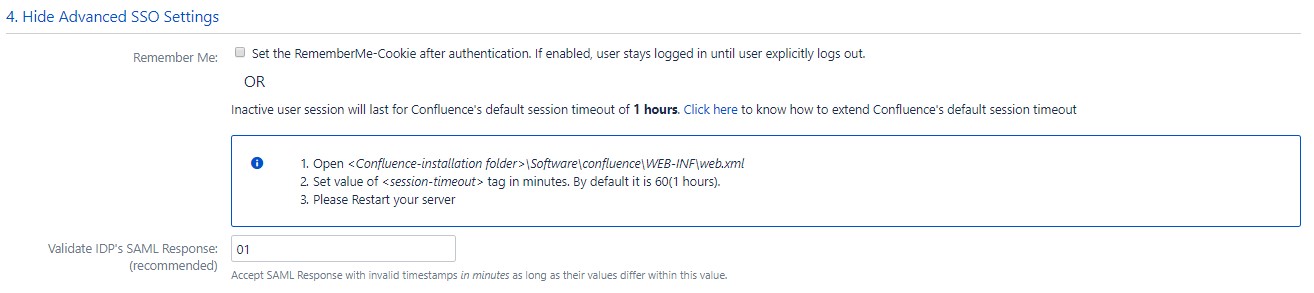
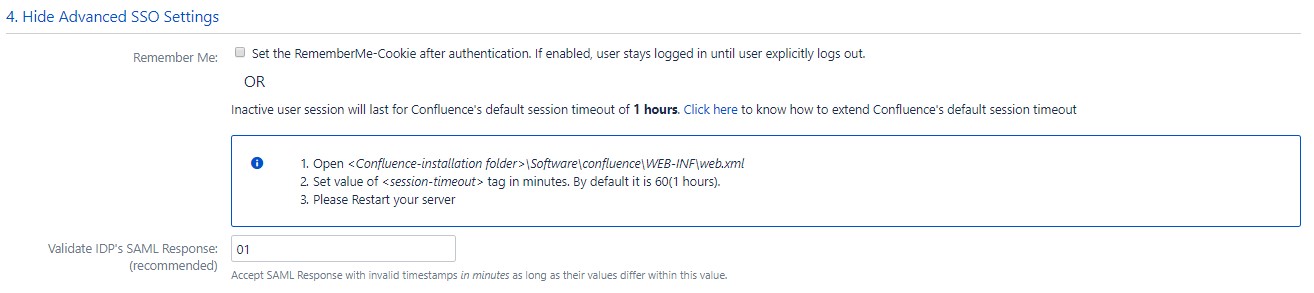
e. Advanced Settings
- Remember Me: If enabled, user stays logged in until user explicitly logs out.
- You can extend Confluence default session timeout using these steps. By default it is set to 60 minutes.
- Validate IDP's SAML Response: Configure time difference(in minute) here In case Confluence server time is not in sync with your IDP's time.
With the Quick Setup method, you can get the SP metadata from the first step of adding an IDP.
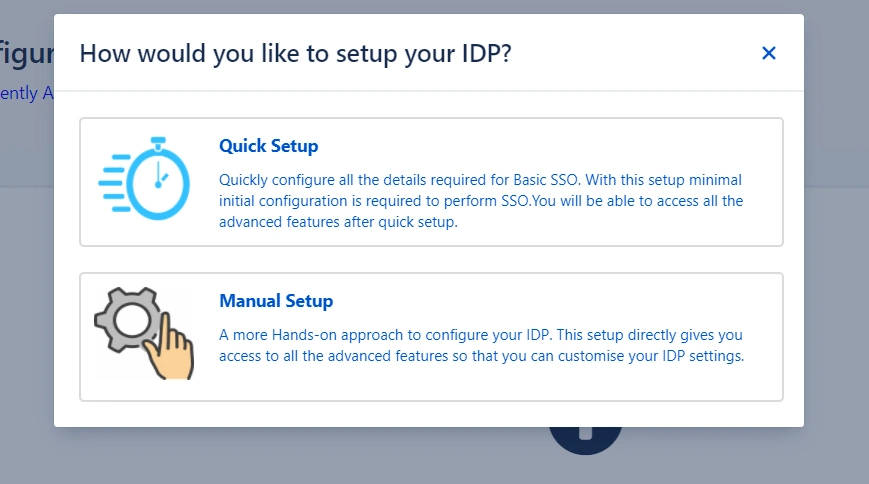
The steps to initiate Quick Setup are given below :
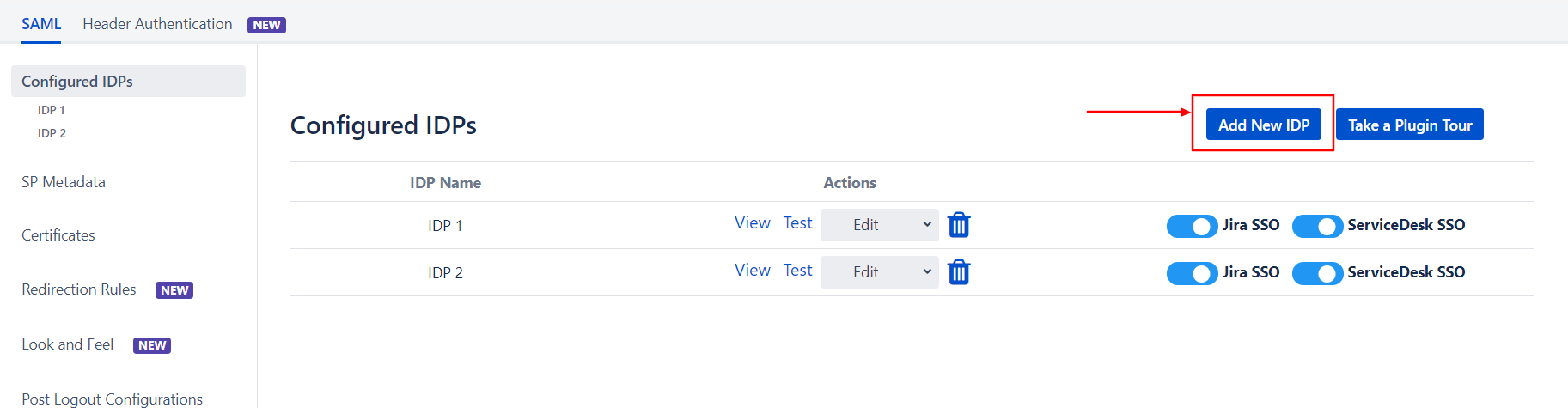
- Click on the Add New IDP button in the Configured IDPs section
- Select the Quick Setup option in the pop-up that opens
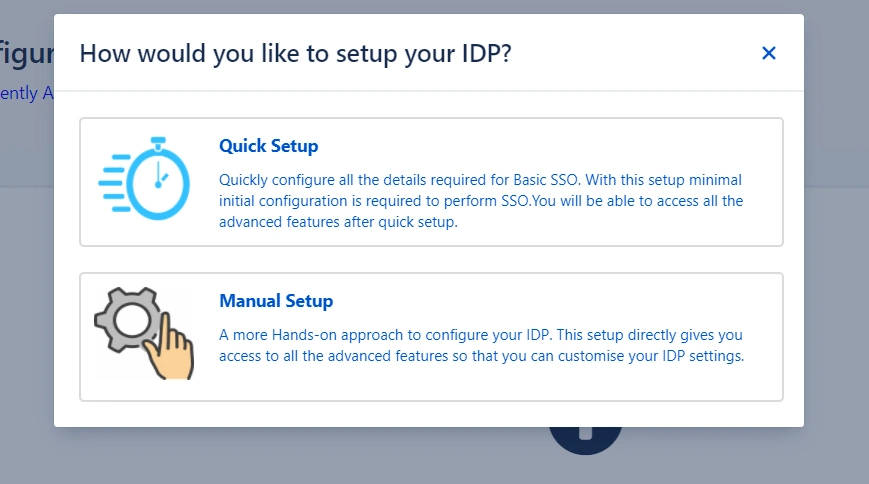
- Select your IDP from the list of IDPs displayed
After completing the above steps, you will see the first step of the Quick Setup process. This step
deals
with setting up your IDP.
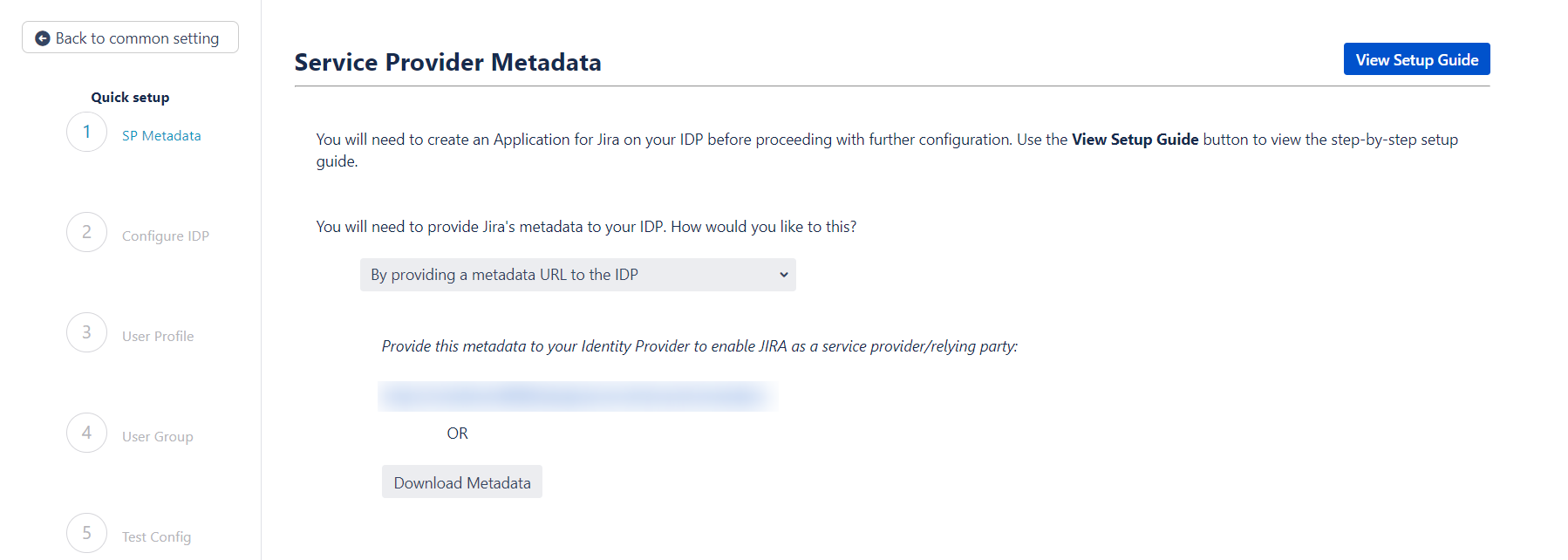
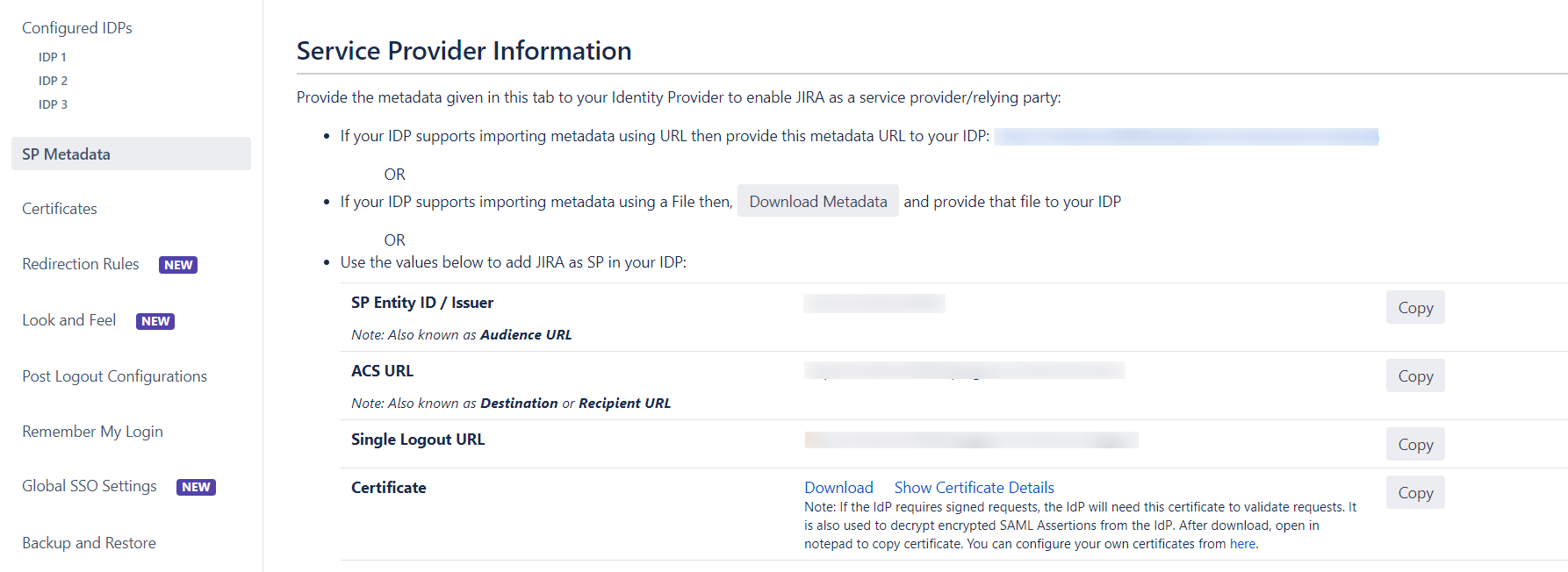
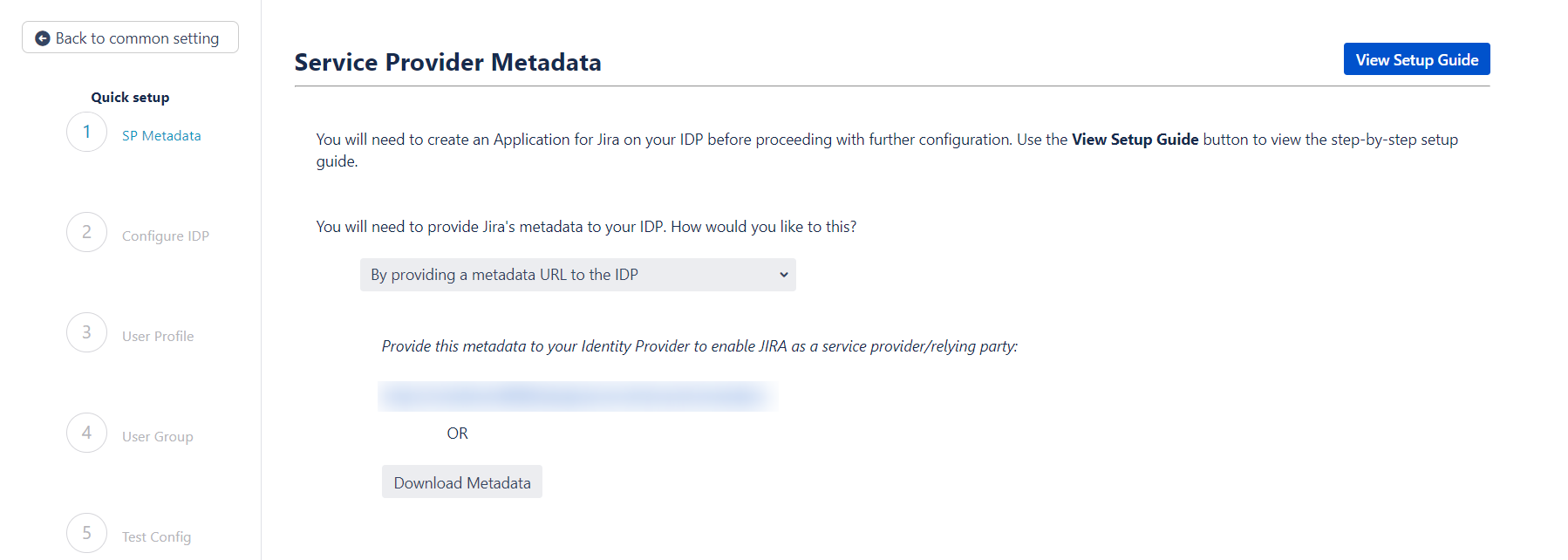
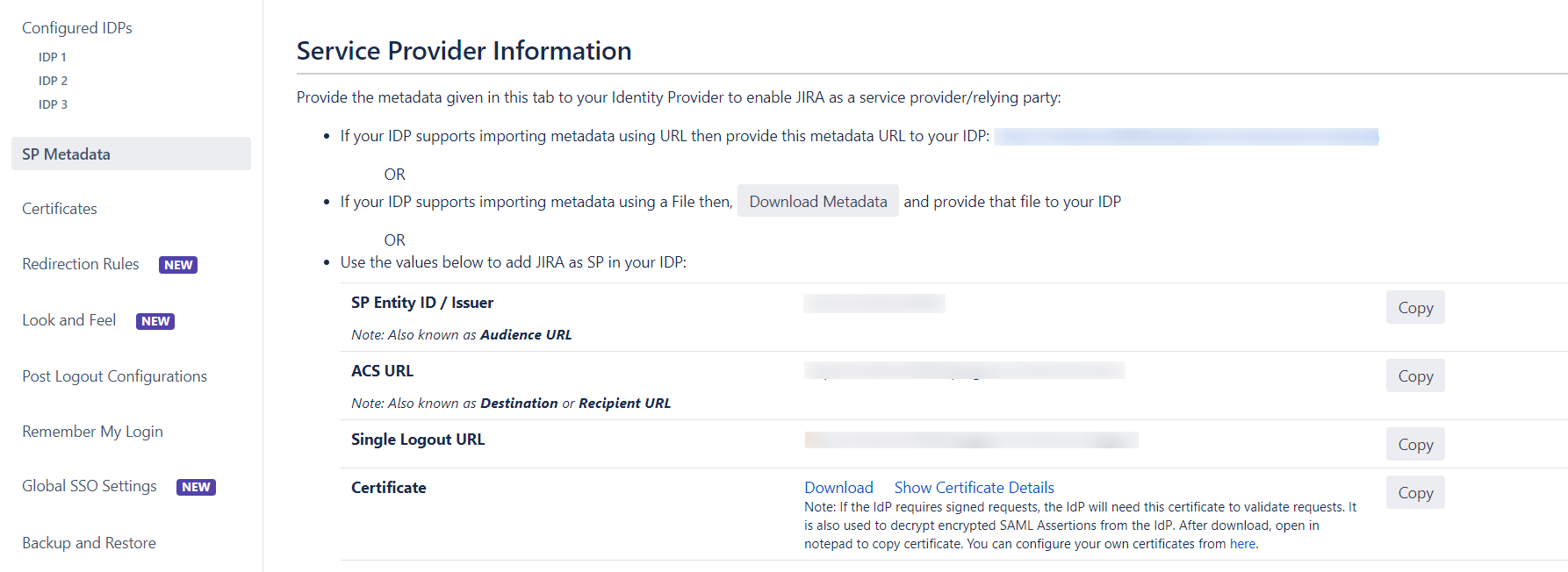
Step 2.1: Service Provider Metadata
Here you will find your SP's metadata. You will need to provide this metadata to your IDP.
There
are two ways to add this metadata to your IDP.
 Import the metadata
Import the metadata
- If your IDP supports importing the metadata, then you can choose By
providing a
metadata URL to the IDP.
- Depending on how your IDP accepts the metadata, you can either provide the metadata
URL
or you can use the Download Metadata button to download an XML file
for the same.
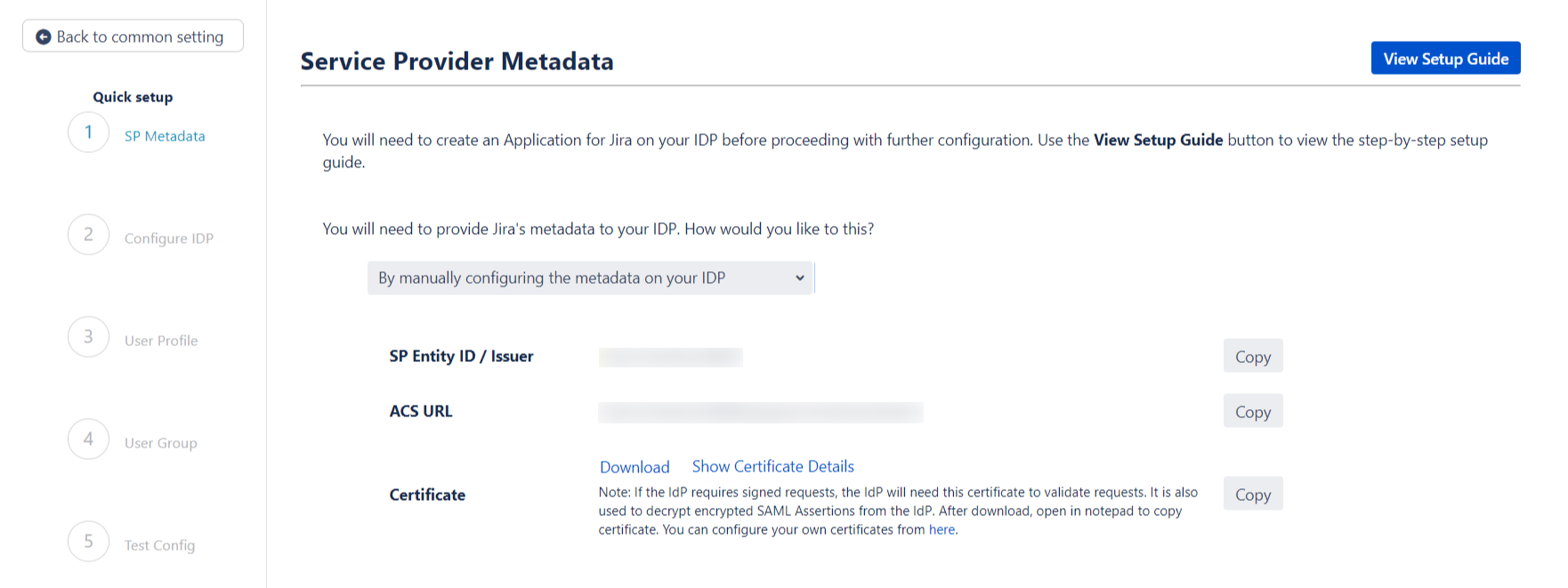
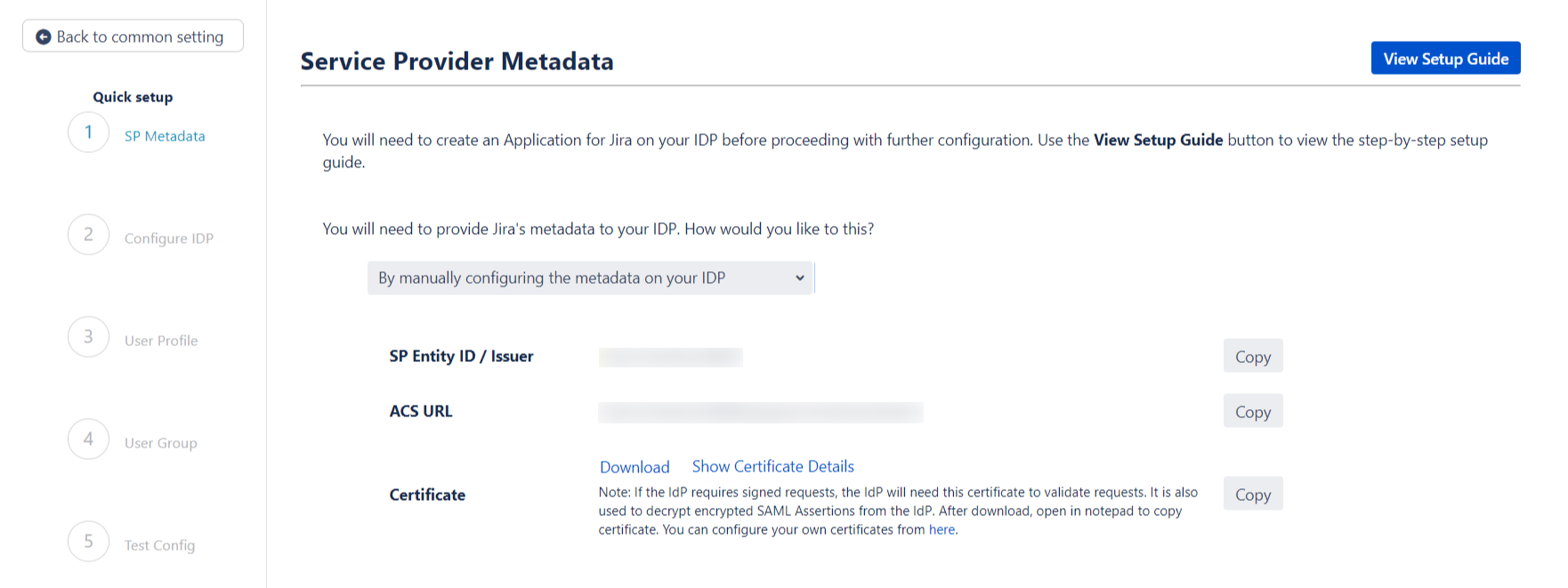
 Manually add the metadata
Manually add the metadata
If you wish to add the metadata manually, then you can choose By manually
configuring the metadata on your IDP
You will find the following information. These details will need to be provided to your
IDP
- SP Entity ID
- ACS URL
- SP Certificate
The next step of the Quick Setup flow deals with setting up IDP metadata on SP. We will pick this up
in the next section of the setup guide.
If you have chosen to add your IDP using the Quick Setup flow then you have already completed the
first step, which is to add SP metadata to your IDP.
Now you can proceed with the second step of the Quick Setup method
Step 2.2: Configuring your Identity Provider
This step is where you will be adding your IDP metadata.
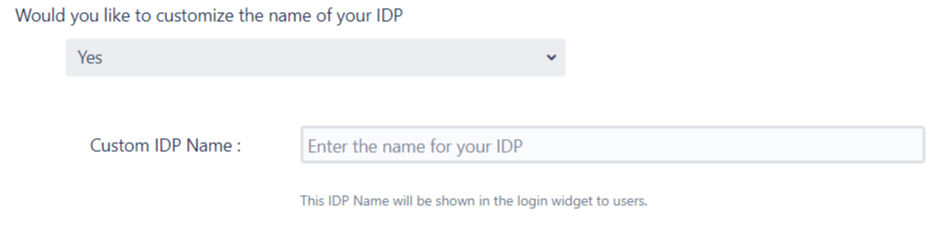
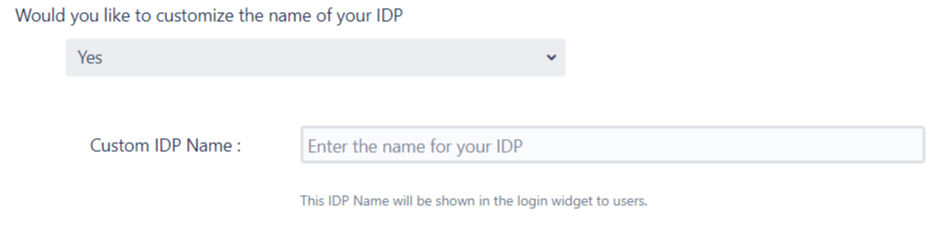
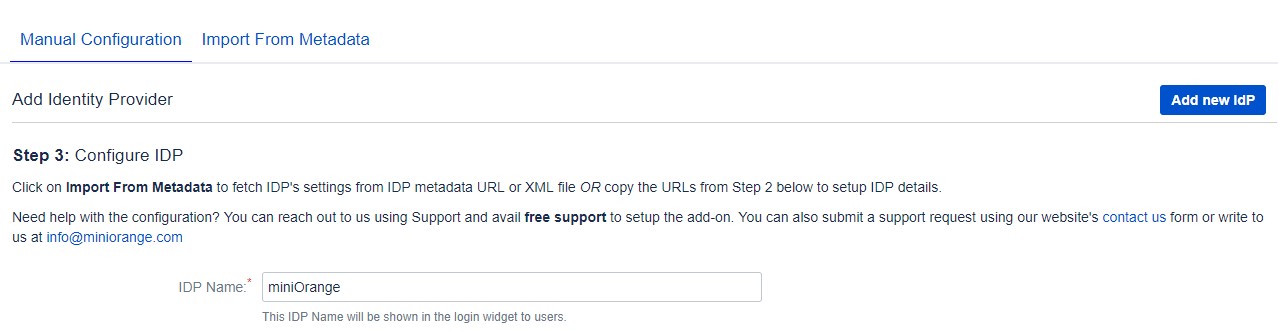
 Custom IDP name
Custom IDP name
- You can enter a name for your IDP int the Custom IDP Name field.
In-case your use-case requires multiple IDPs, the SSO button for this IDP on the login
page will display the custom name.
If you do not wish to add a custom name, simply click on the corresponding drop-down and
select no.
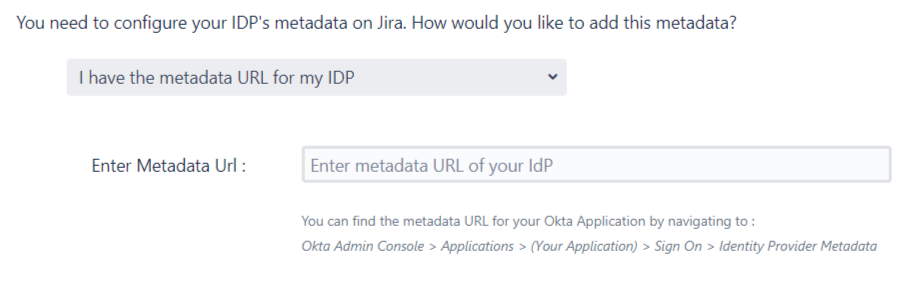
 Adding the IDP metadata
Adding the IDP metadata
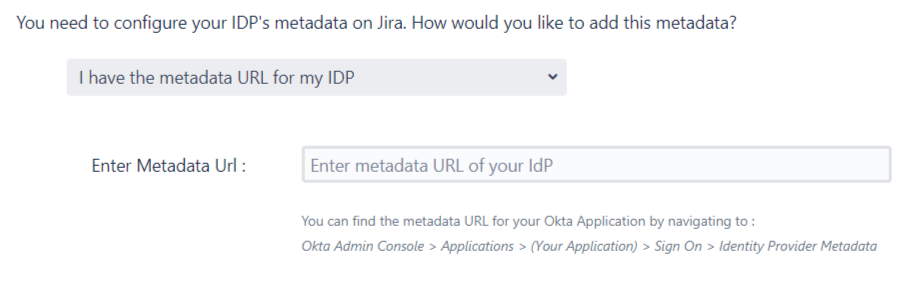
There are 3 ways in which you can add your IDP metadata. Use the drop-down to select any of
the following methods :
-
I have the metadata URL for my IDP
Add your metadata URL in the Enter Metadata URL field.
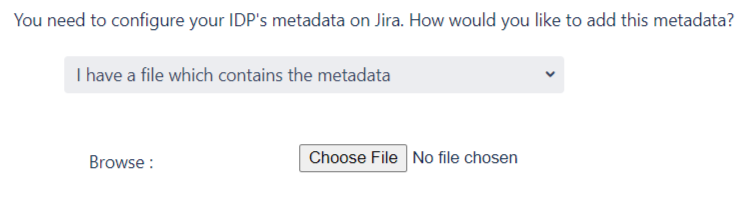
-
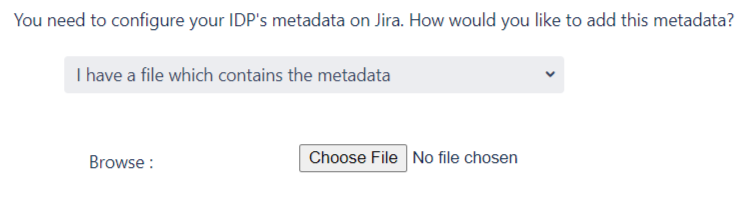
I have a file which contains the metadata
Use the Choose File button to browse for your metadata file.
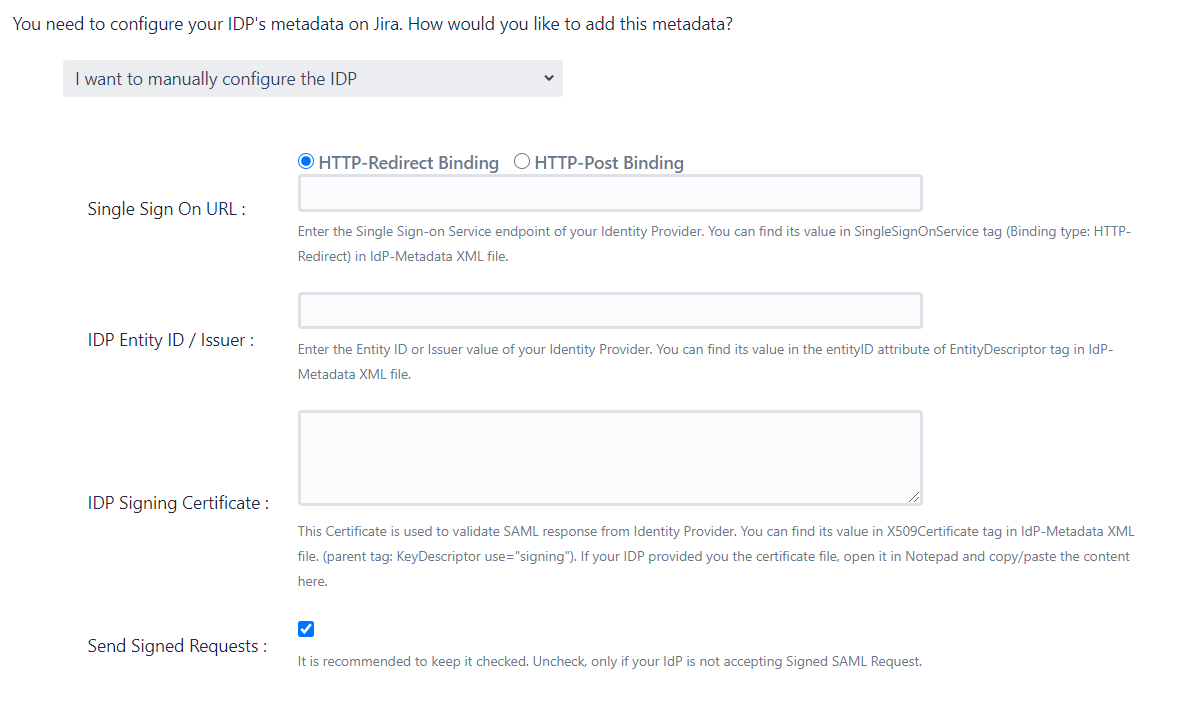
-
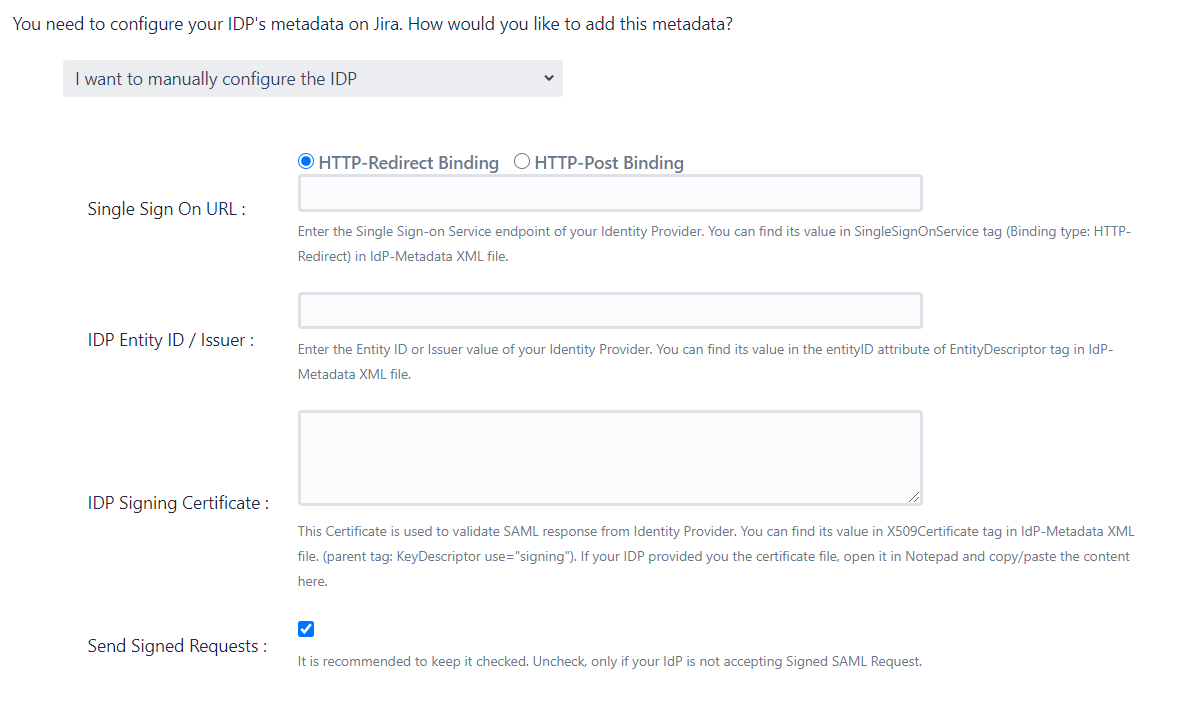
I want to manually configure the IDP
To configure the IDP manually, you will need to have the following details from your
IDP's metadata.
- Single Sign On URL
- IDP Entity ID
- IDP Signing Certificate
-
Testing the configuration
Once you have added the IDP metadata, click on Save. If the IDP has been added
successfully, then you will see a Test and Get Attributes
button.
Click on this button to test if the IDP was added successfully.
Step 2.3: User Profile
In this step you will be setting up basic user profile attributes for your SP
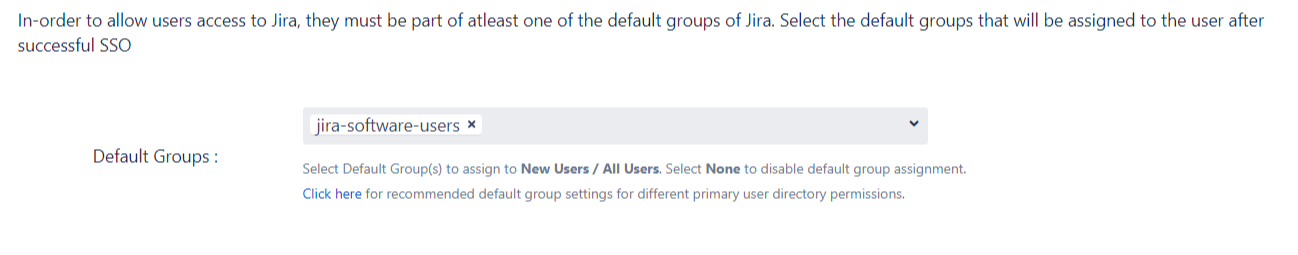
step 2.4: User Groups - Default groups
- Select the users's default groups in this step. You can use the Default
Groups
to do this. Multiple groups can be
set as default groups. The user will be assigned to these groups by default after
successfully
logging in via SSO.
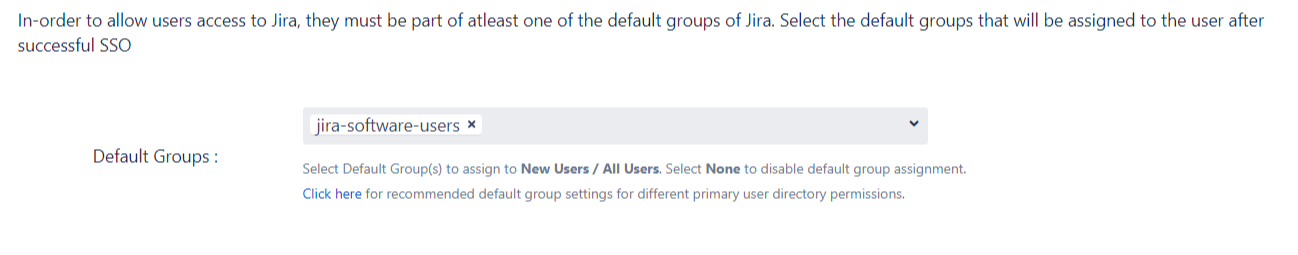
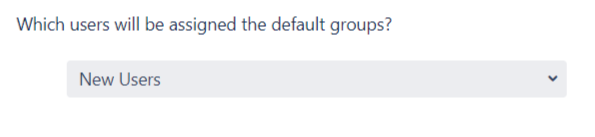
- You can enable default groups for All Users or New Users
using the Enable Default Groups for drop-down. Select None
if you don't want to assign any default group to SSO users.
Step 2.5: Troubleshooting and Support
- This step marks the end of the Quick Setup flow. In case you faced any issues or encountered
any
errors while setting
up your IDP you can use the steps given in the Troubleshooting section to
get
in touch with us.
- You will also be able to see the results of a successful test configuration on this page.
This
includes the attributes received
from your IDP, the SAML request sent and the SAML response received.
- Adding your IDP via this method will setup basic SSO for your end-users. You can always
customise
your setup further using the
full set of features that we provide. To do this use the Edit drop-down for
your
IDP in the Configured IDPspage.
From here you will be able to access your SP Metadata and customise your User
Profile and User Groups settings.
You can read more about these settings in the Custom Setup section of this
guide.
Step 2.1: Service Provider Metadata
If you plan on customizing your IDP setup from the get go, you can find the metadata in the
SP Metadata. Here you will find your SP's metadata. You will need to provide this metadata to your IDP. There
are multiple ways to add this metadata to your IDP :
 Import the metadata
Import the metadata
Depending on how your IDP accepts the metadata, you can either provide the metadata URL or you can use the Download Metadata button to download an XML file for the same.
 Manually add the metadata
Manually add the metadata
If you wish to add the metadata manually,you will find the following information in this section. These details will need to be
provided to your IDP.
- SP Entity ID
- ACS URL
- SP Certificate
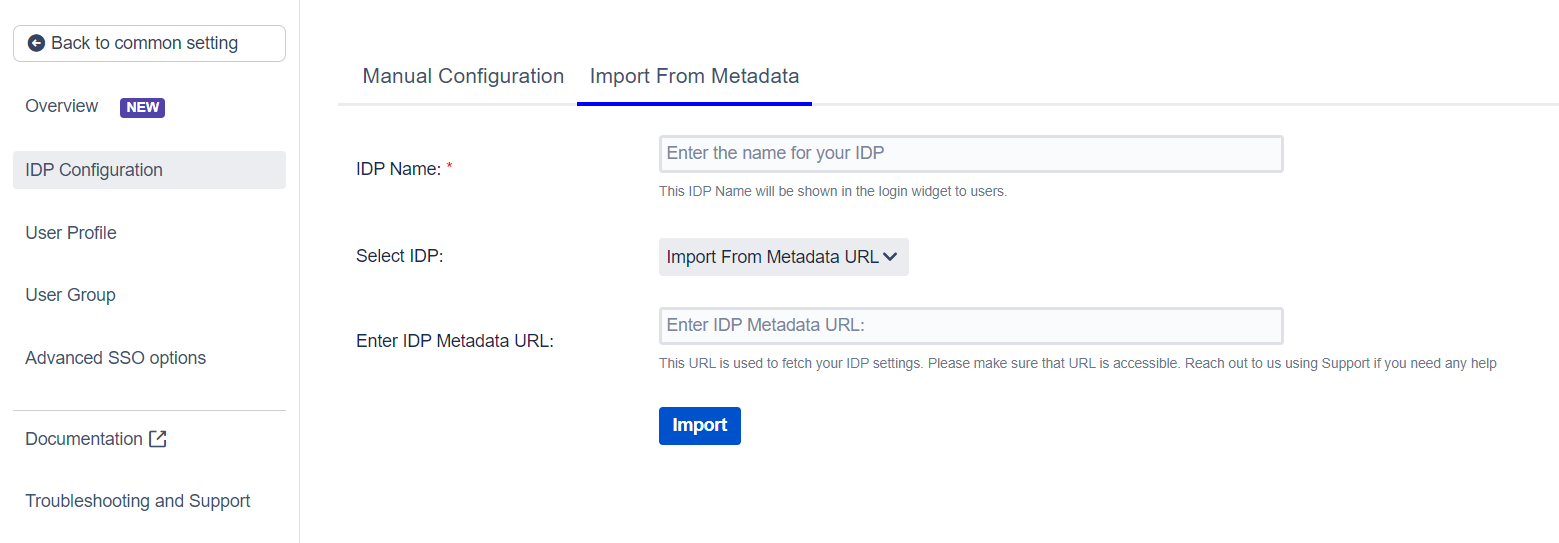
Step 2.2: Configuring your Identity Provider
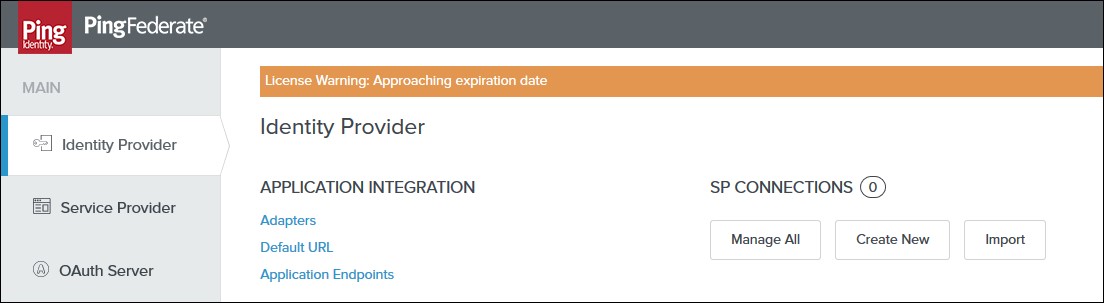
The custom setup flow allows you to dive into the complete set of configurations that we provide to add a SAML Identity Provider. The steps to configure an IDP using the Custom Setup option are :
 Adding IDP Metadata
Adding IDP Metadata
With the information you have been given by Your IDP team, you can configure IDP settings in 3 ways:
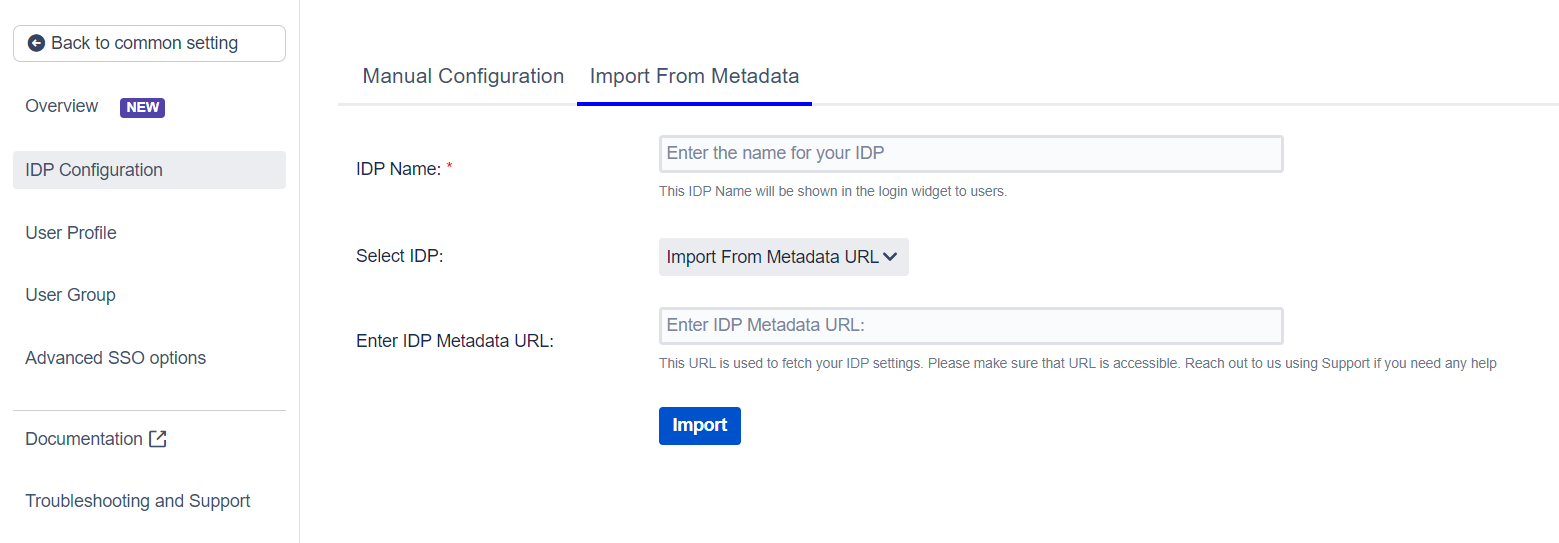
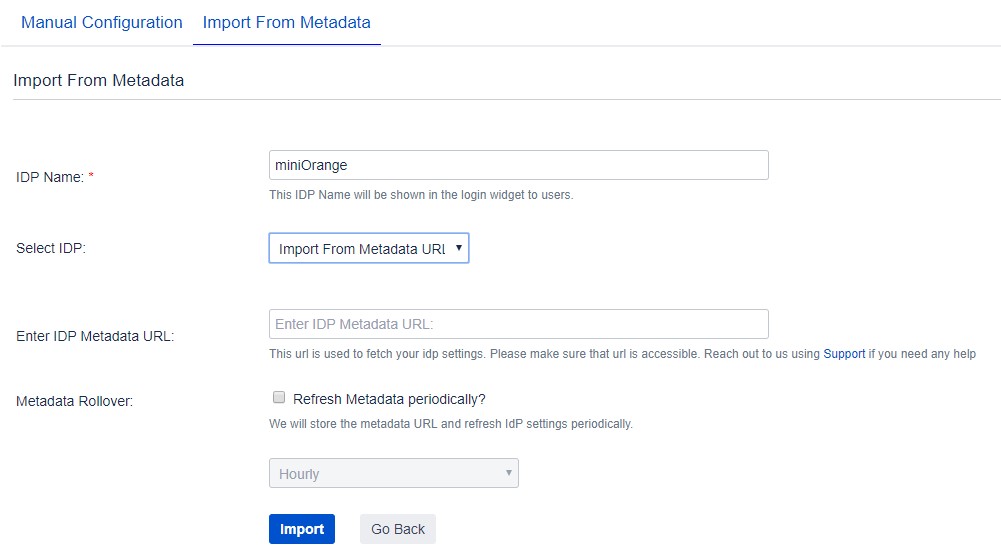
 By Metadata URL
By Metadata URL
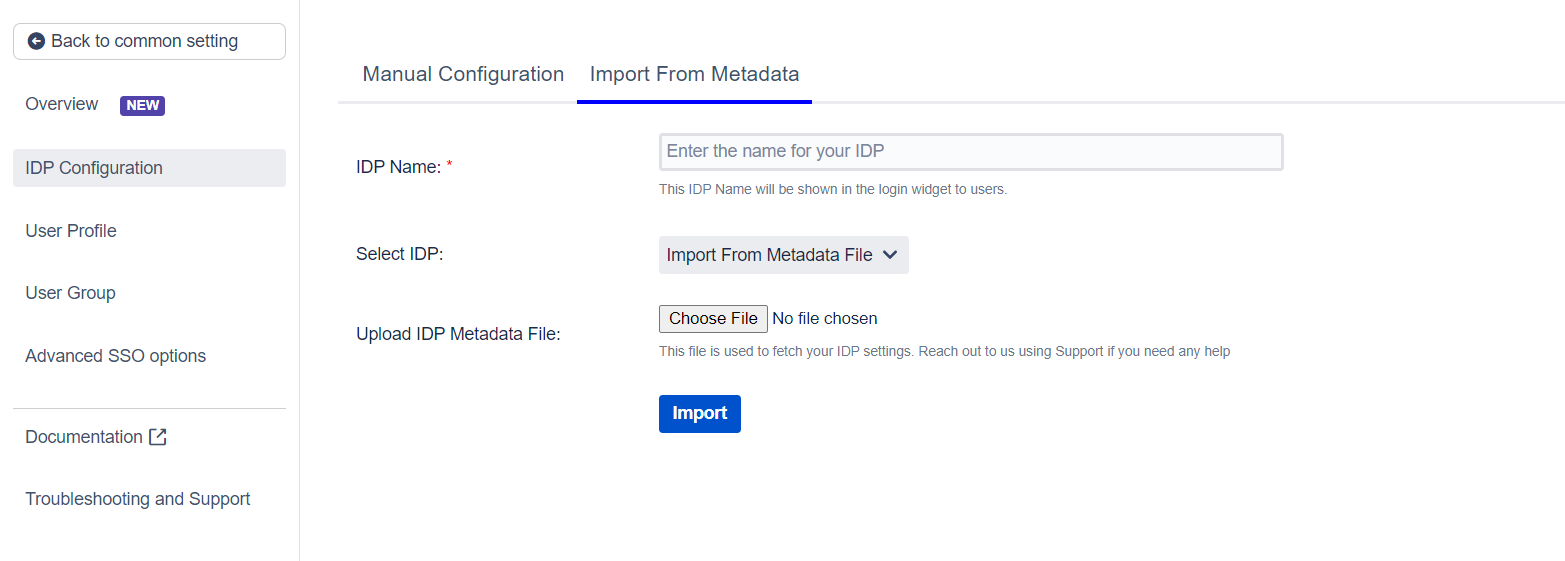
- Click on the Import from Metadata tab.
- Select IDP: Import From Metadata URL.
- Enter IDP metadata URL: Enter your metadata URL.
- If your IDP changes certificates at intervals (Eg. Azure AD), you can refresh your IDP metadata accordingly :
- Navigate to the Advanced SSO options from the menu on the left-hand side of the page.
- Enter your metadata URL in the Certificate Rollover field.
- Select the Refresh Certificate periodically option.
- Use the drop-down provided to set the interval for a periodic refresh.Select 5 minutes for the best results.
- Click Import.
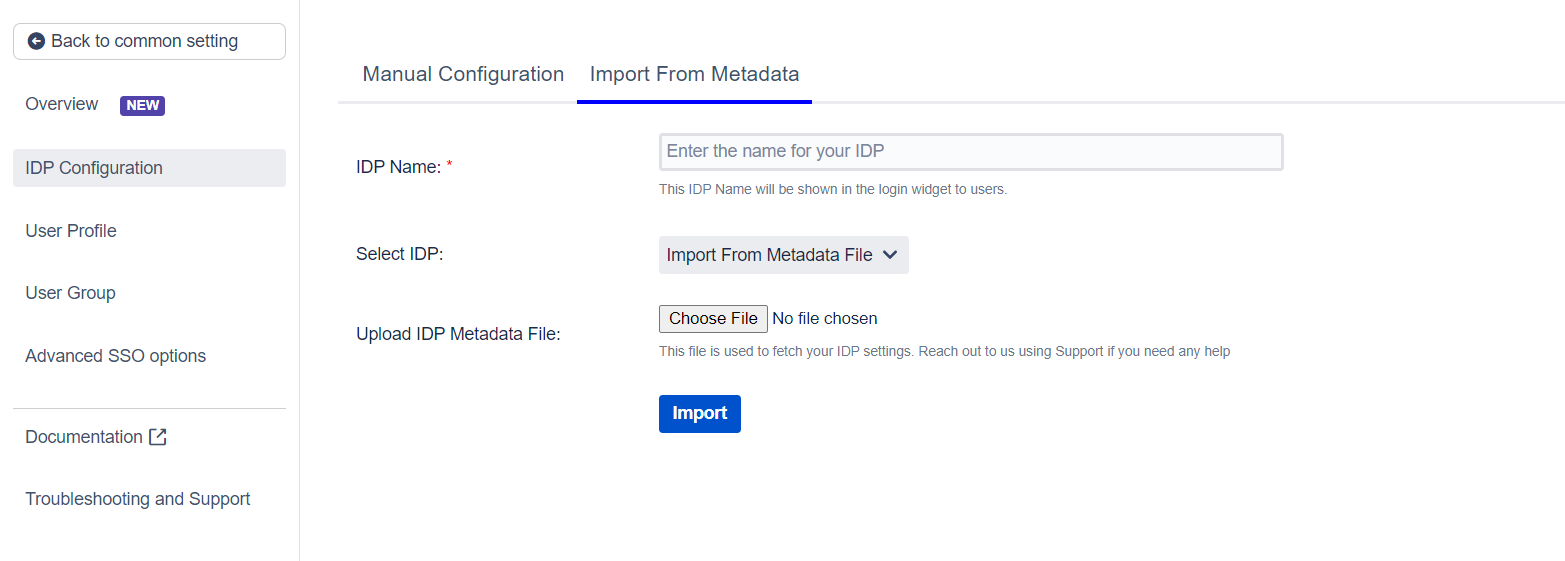
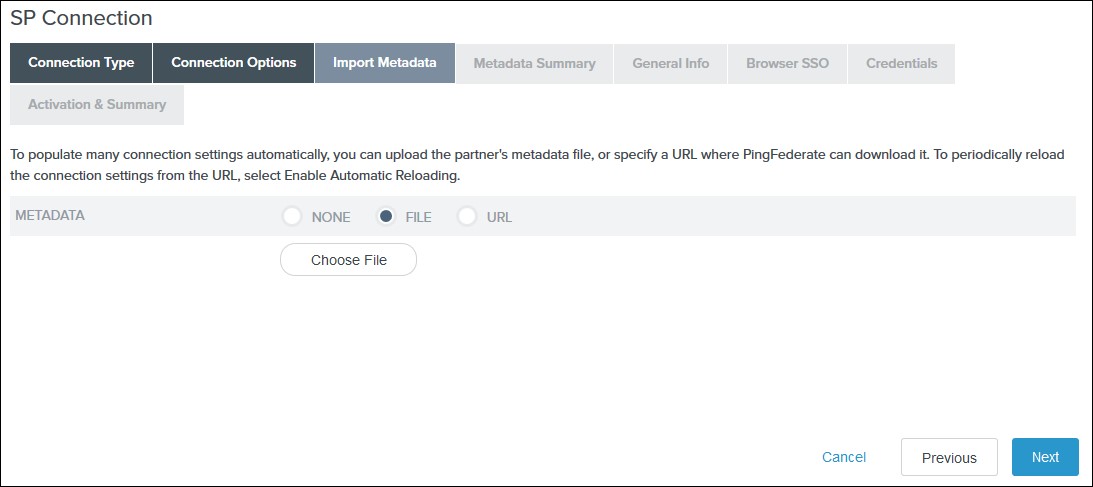
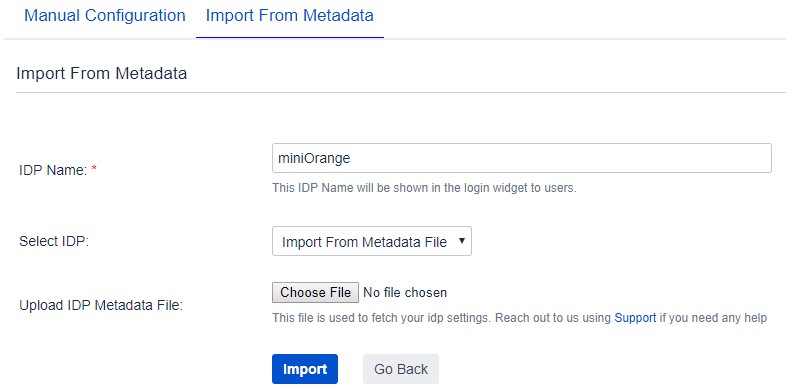
 By Uploading Metadata XML File
By Uploading Metadata XML File
- Click on the Import from Metadata tab.
- Select IDP: Import from Metadata File.
- Upload metadata file.
- Click Import.
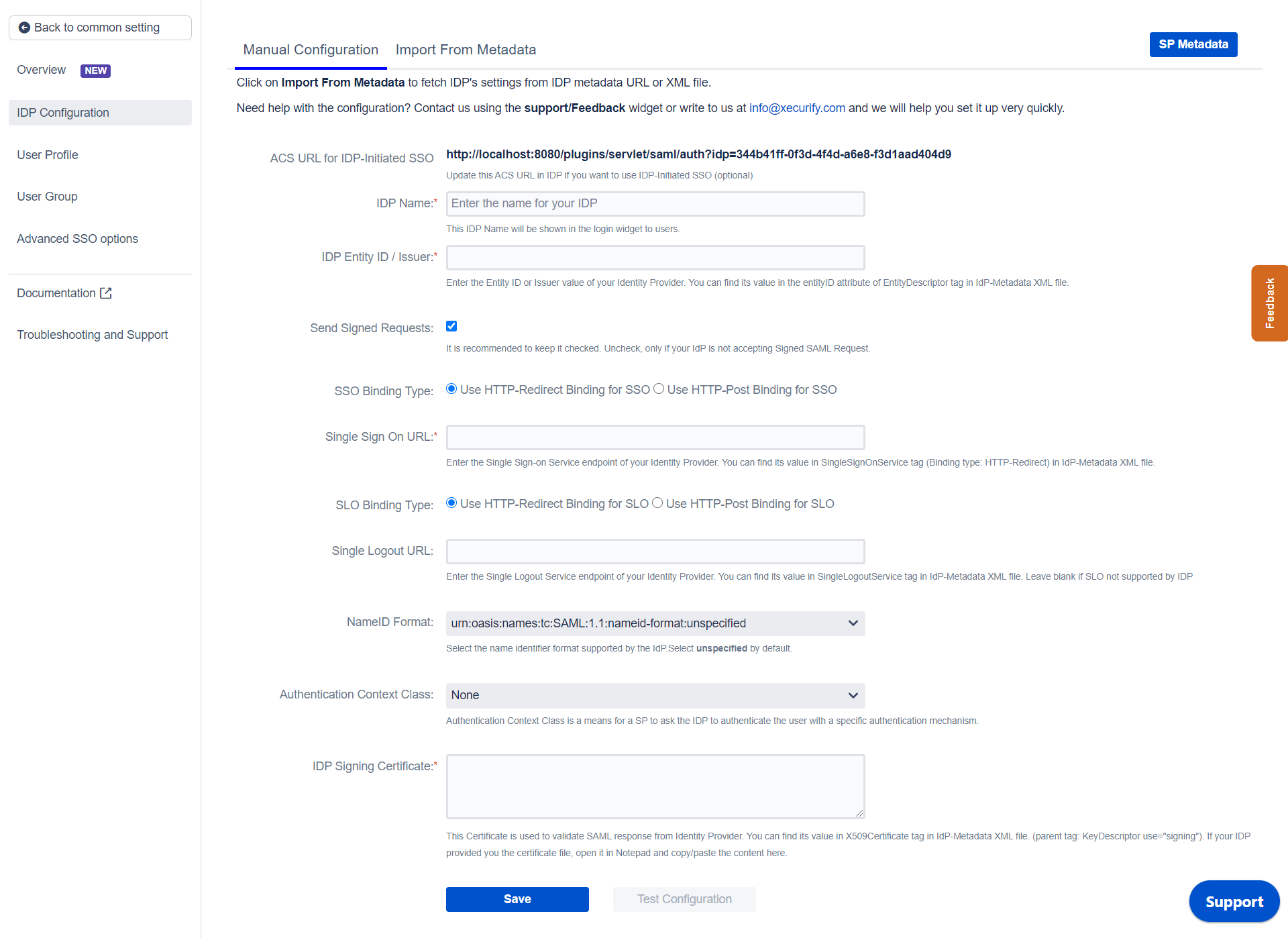
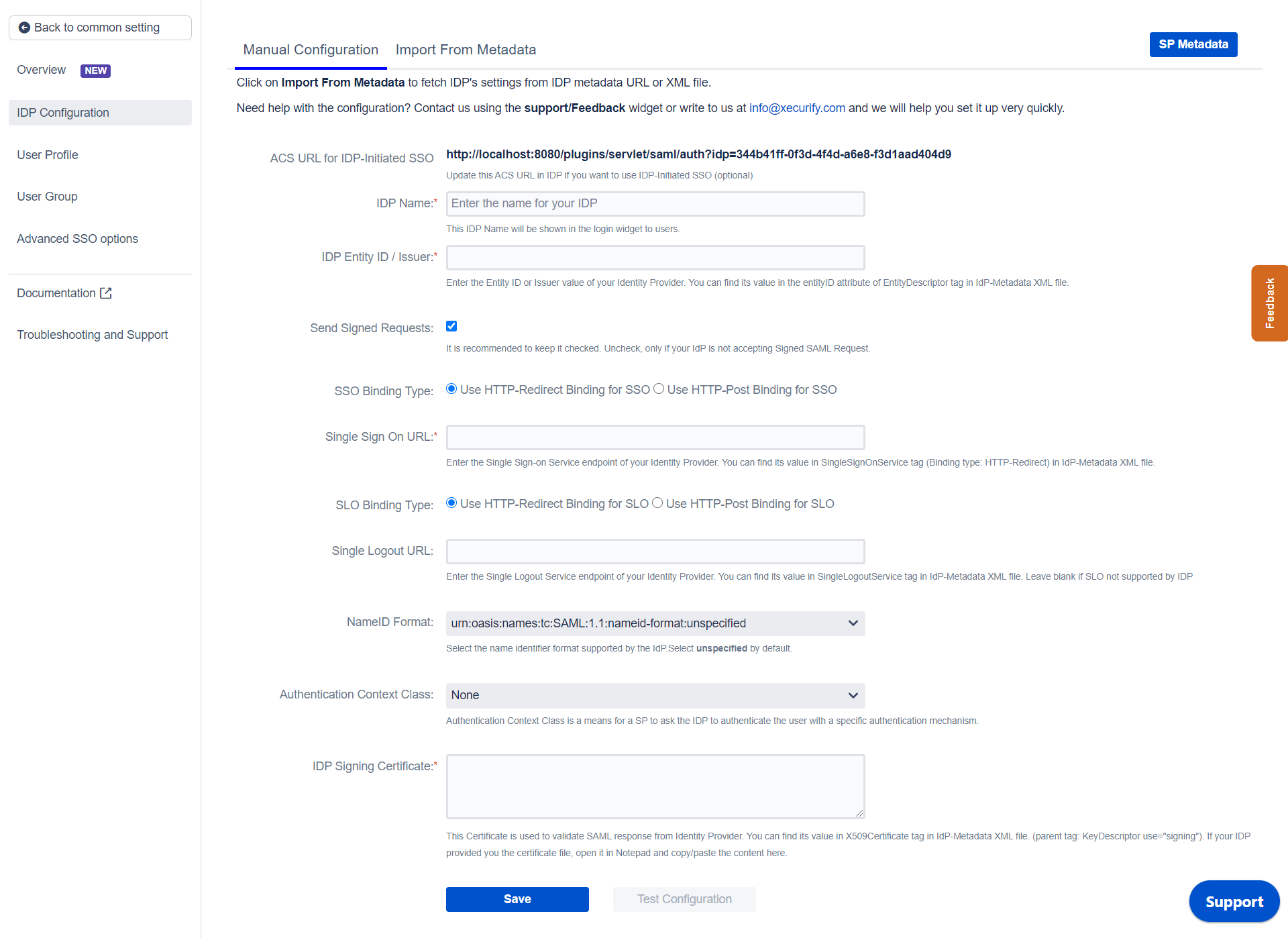
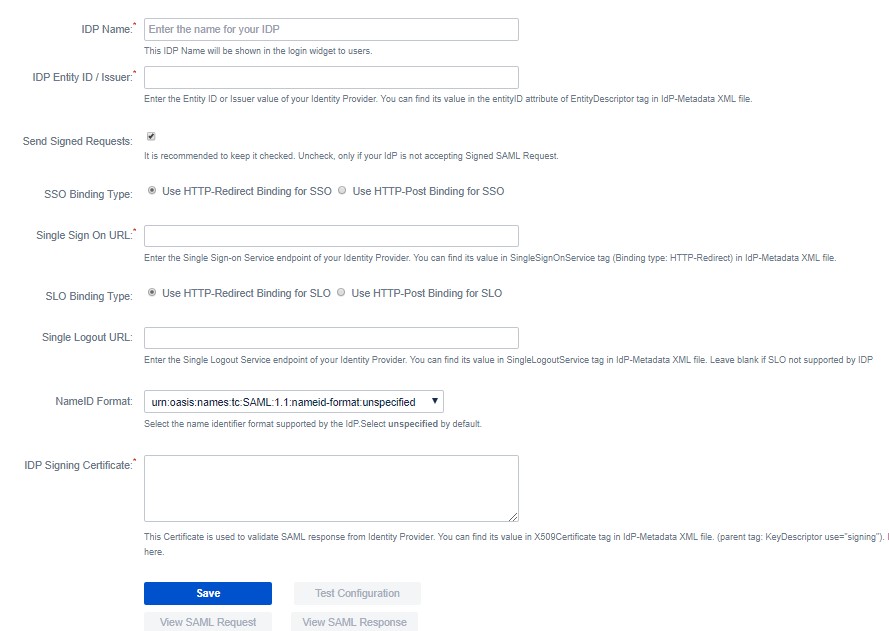
 Manual Configuration
Manual Configuration
Go to Manual Configuration tab and enter the following details:
- IDP Entity ID
- Single Sign On URL
- Single Logout URL
- X.509 Certificate
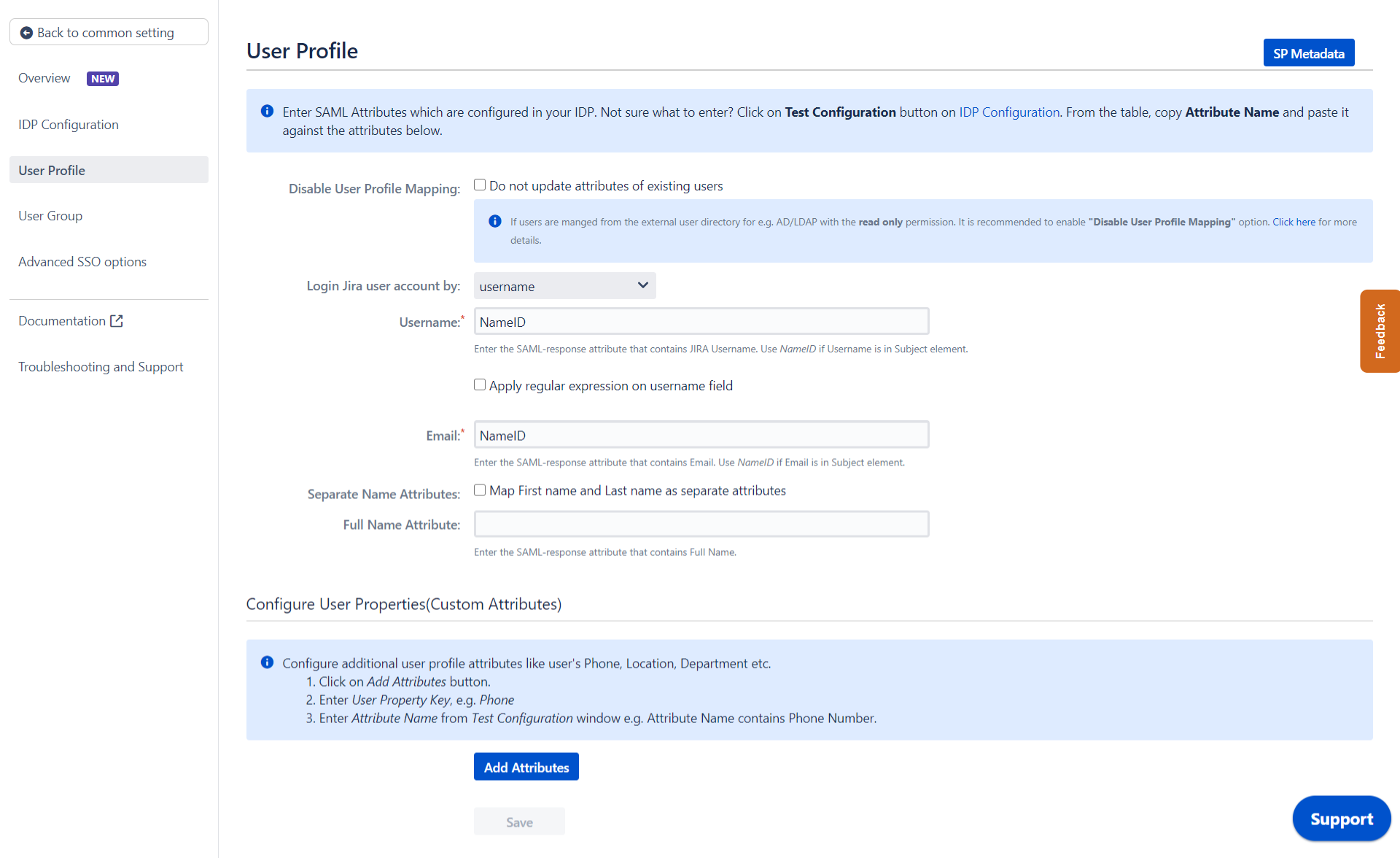
Step 2.3: User Profile
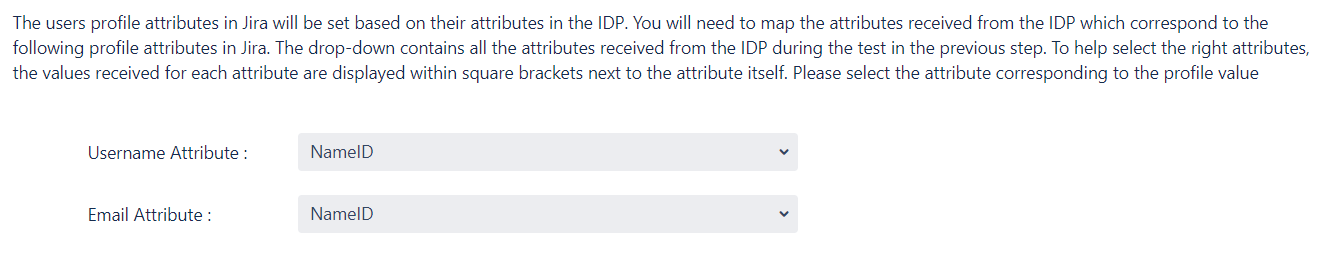
Next we will be setting up user profile attributes for Jira. The settings for this can be found in the User Profile section.
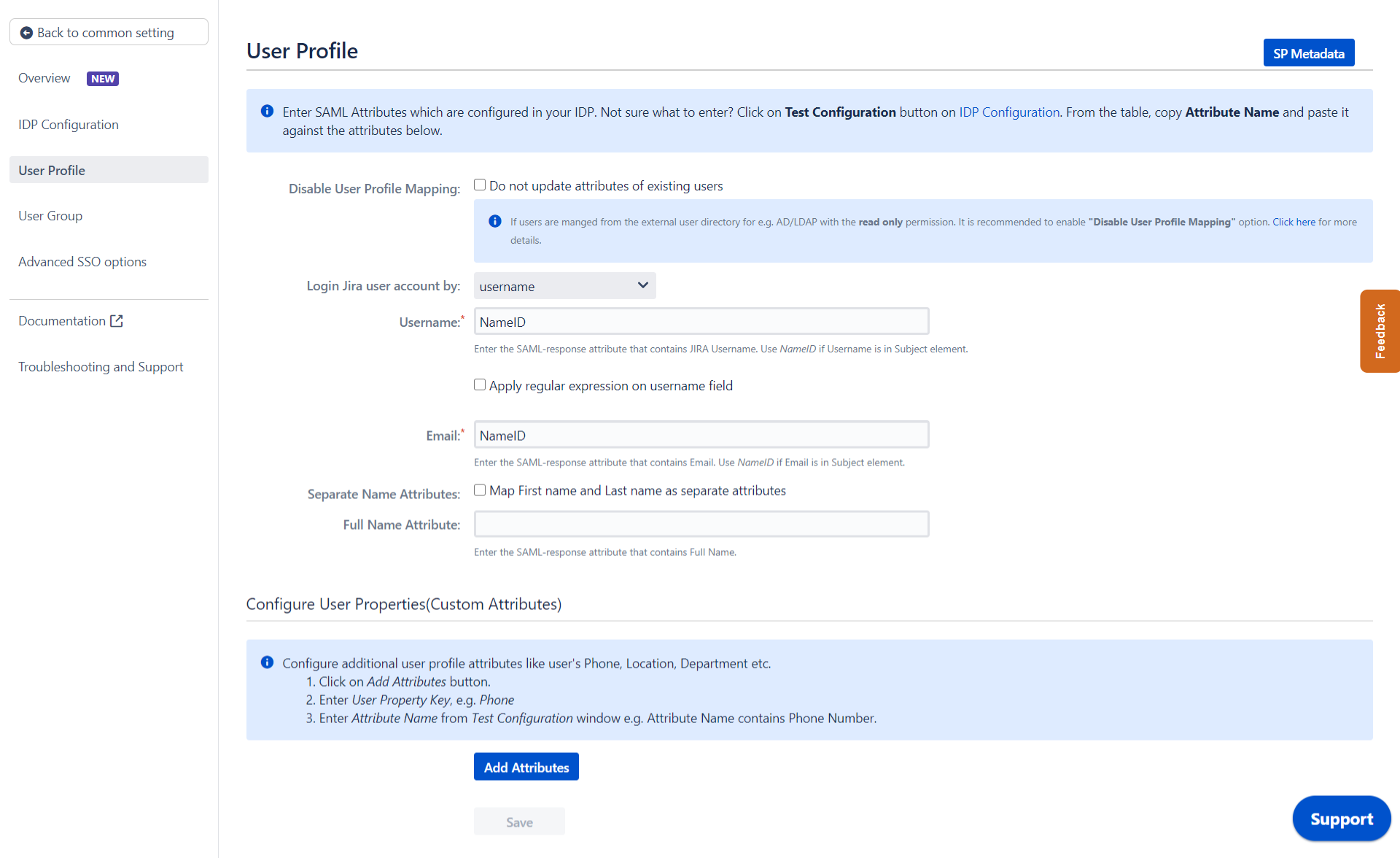
a. Finding correct attributes
- Go to IDP Configuration section. Scroll down and click on Test Configuration.
- You will see all the values returned by your IDP to Jira in a table. If you don't see value for First Name,Last Name, Email or Username, make the required settings in your IDP to return this information.
- Once you see all the values in Test Configuration, keep the window open and go back to theUser Profile section.
b. Setting profile attributes
- In this tab, fill the values by matching the name of the attribute. For instance, if the Attribute Name in the Test Configuration window is NameID, enter NameID against Username
- Setting up both Username and Email is required if you want to let users register. If you want existing users to only login, configure the attribute using which you will match the user in Jira.
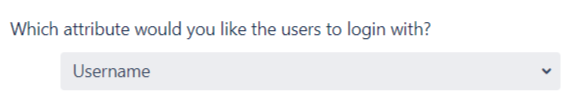
c. Matching a User
When the user logs into
Jira, one of the user's data/attribute coming in from the IDP is used to search the user in Jira. This is used to detect the user in Jira and log in the user to the same account.
You can configure it using steps given below:
- Select Username or Email for Login user account by
- Enter the attribute name from IDP which corresponds to Username or Email using Finding Correct Attributes
Step 2.4: User Groups
Now we will be setting up user group attributes for Jira. You can replicate your user's groups present on IDP in your SP. There are multiple ways of doing this.
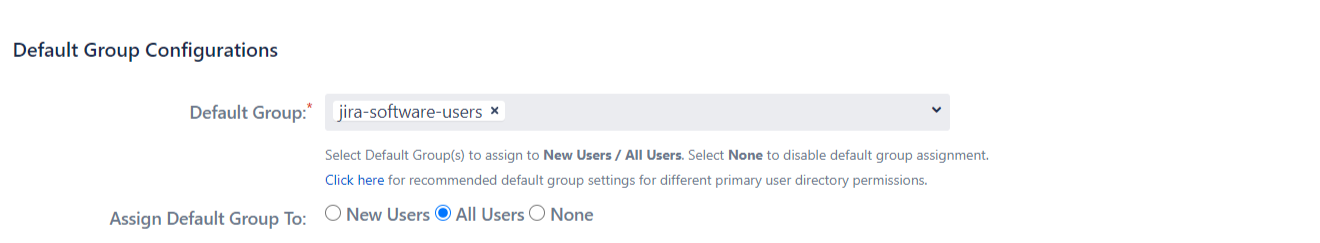
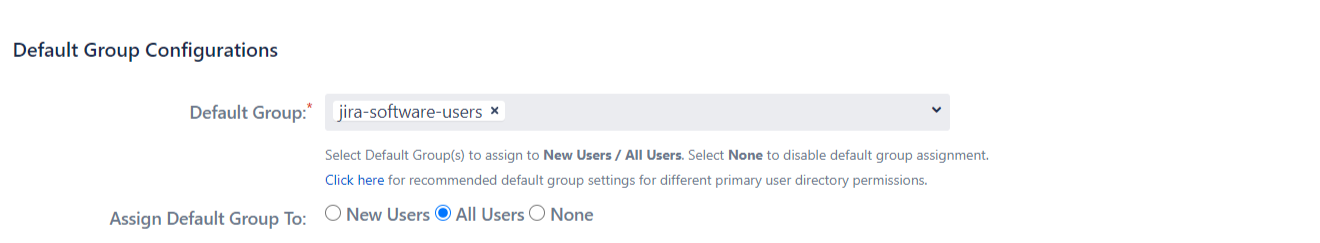
a. Setting default group
- Select the users' Default Group in the tab User Groups. If no group is mapped, users are added by default to this group.
- You can enable default groups for All Users or New Users using the option.Select None if you don't want to assign any default group to SSO users. Using the option Enable Default Groups for.
b. Finding Group Attribute
- Just like we found Attribute Name for User Profile attributes, we find the group attribute.
- Go to IDP Configuration section. Scroll down and click on Test Configuration.
- You will see all the values returned by your IDP to Jira in a table. If you don't see value with groups, make the required settings in your IDP to return group names.
- Once you see all the values in Test Configuration, keep the window open and go to User Groups tab.
- Enter the Attribute Name of group against Group Attribute.
- Check Disable Group Mapping option if you don't want to update groups of existing users.
c. Group Mapping
Group Mapping can be done in two ways:
- Manual group mapping: If the names of groups in Jira are different than the corresponding groups in IDP, then you should use Manual group mapping.
- On-The-Fly group mapping: If the names of groups in Jira and IDP are same, you should use On-The-Fly group mapping.
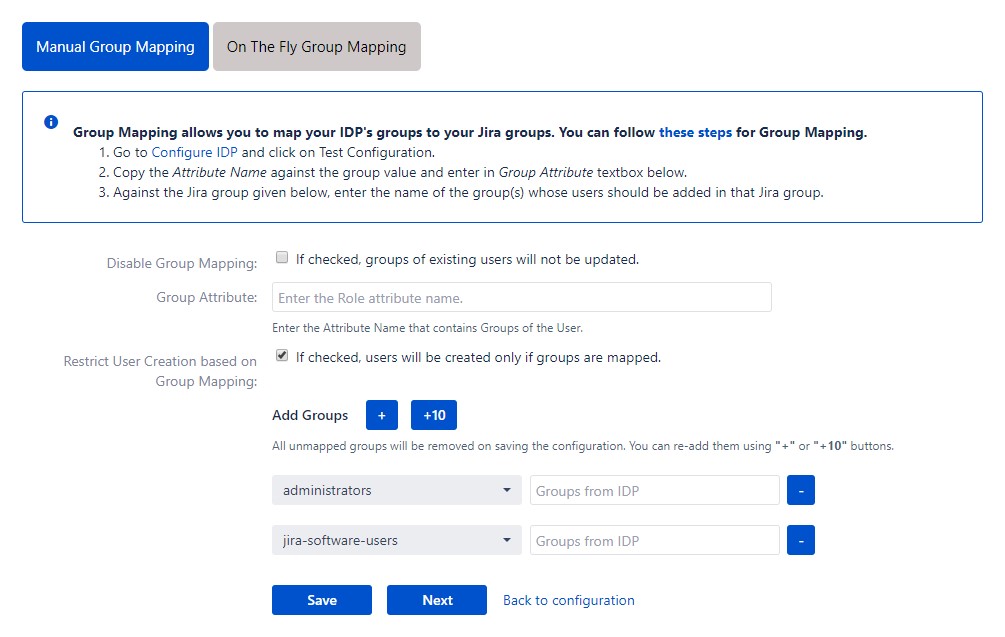
I. Manual Group Mapping
- Check Restrict User Creation Based on Group Mapping option if you want new users to be created only if at least one of the user's IDP groups is mapped to a group in the application.
- For mapping, first select a Jira group from the dropdown which lists all groups present in Jira and then enter the name of the IDP group to be mapped in the textbox beside.
- For example, if you want all users in 'dev' group in IDP to be added to jira-software-users, you will need to select jira-software-users from the dropdown and enter 'dev' against jira-software-users.
- Use '+1' and '+10' buttons to add extra mapping fields.
- Use '-' button next to each mapping to delete that mapping.
II. On-The Fly Group Mapping
- Check Create New Groups option if you want new groups from IDP to be created if not found in Jira.
- If the user is part of some group in Jira and that group is not present in the SAML response returned by IDP, then the user will be removed from that group in Jira.
- If you don't want On-The-Fly group mapping to affect Jira groups which are managed locally then add those groups in Exclude Groups field.
Step 2.5: Troubleshooting and Support
- You can verify if your SAML SSO configuration is correct by clicking the Test Configuration button on the IDP configuration tab of the plugin.
- After the successful test configuration, you will also be able to see the results on the Troubleshooting and Support page. This includes the attributes received from your IDP, the SAML request sent and the SAML response received.
- In case you faced any issues or encountered any errors while setting up your IDP you can use the steps given in the Troubleshooting section to get in touch with us.
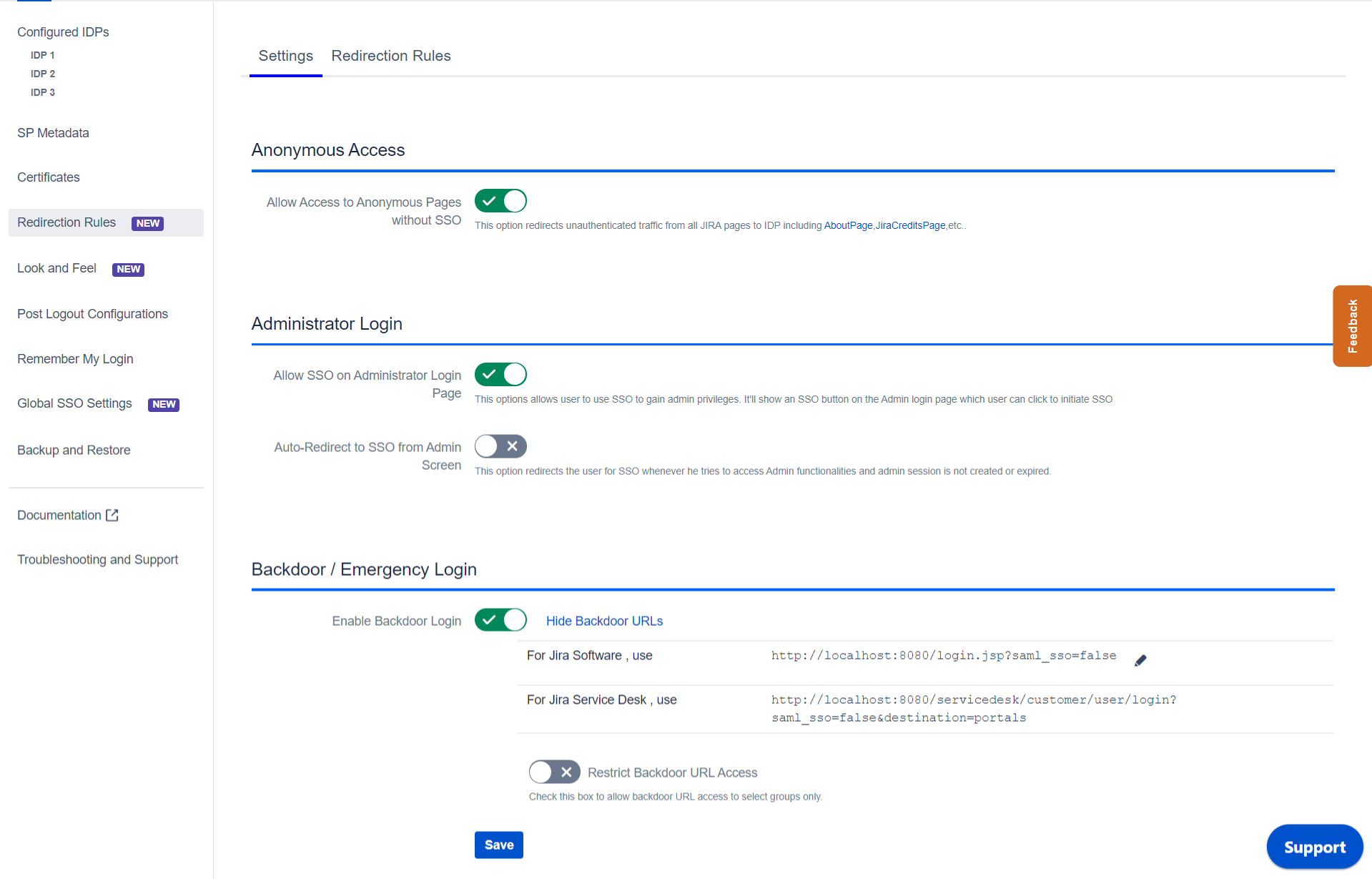
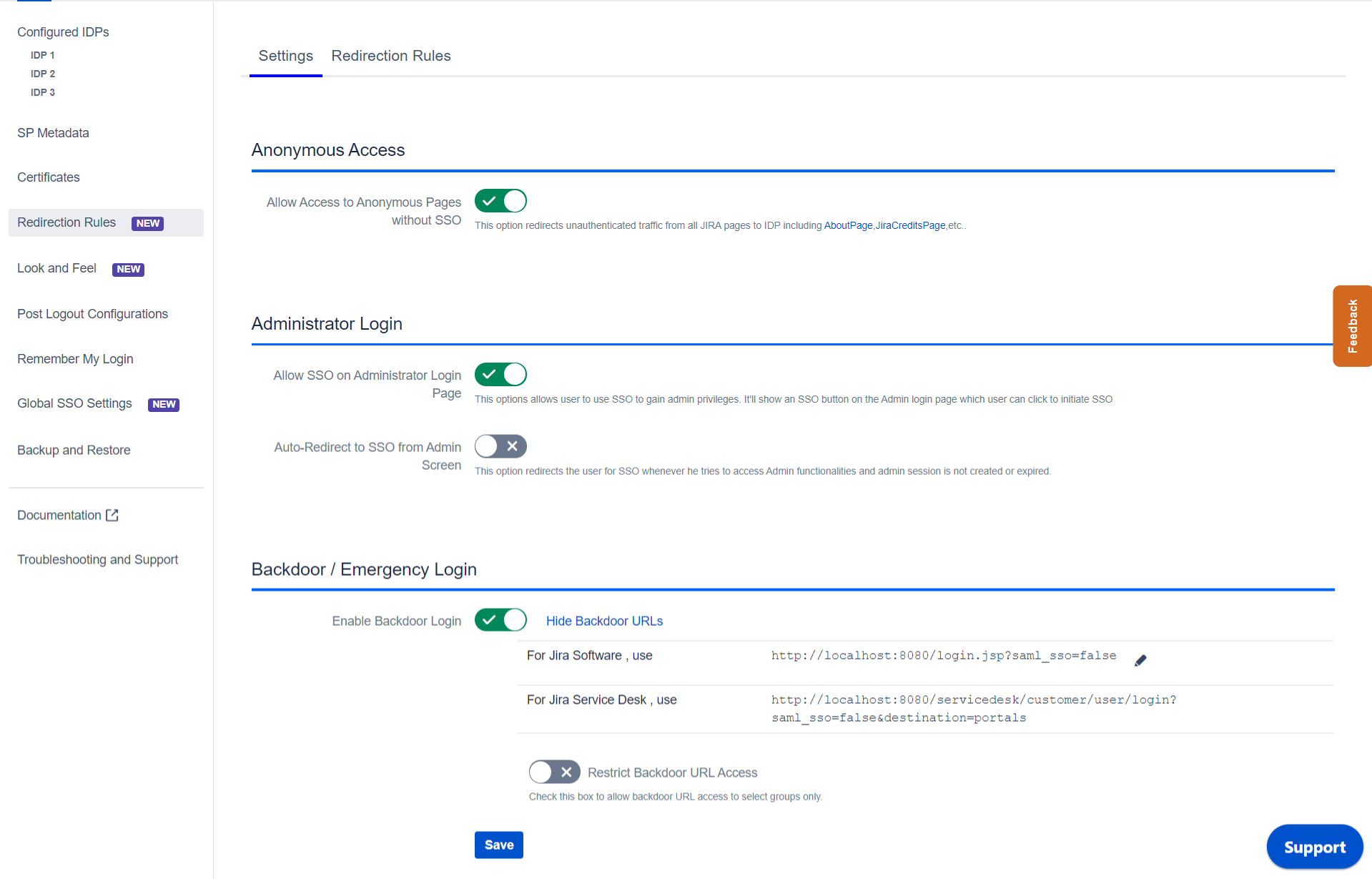
Step 3: Redirection on Login Page
- If you have only one IDP configured, then you can use the features provided on the SSO Settings tab and Redirection tab of the plugin to manage the redirection on the login page.
- Enable the Auto Redirect to IDP option on the SSO Settings tab if you want to allow users to log in only using IDP.
- Use the Emergency/Backdoor Login URL to allow all admins to access the Jira's/Confluence's default login page and log in using Jira local credentials. You can also Restrict the access of this URL to some specific set of users (i.e users of particular groups).
- Use the settings given on Redirection Rules tab to redirect the users on login page based on their email domains, groups and directories. This feature is more useful in case you have multiple IDPs configured. Please refer to the next section.
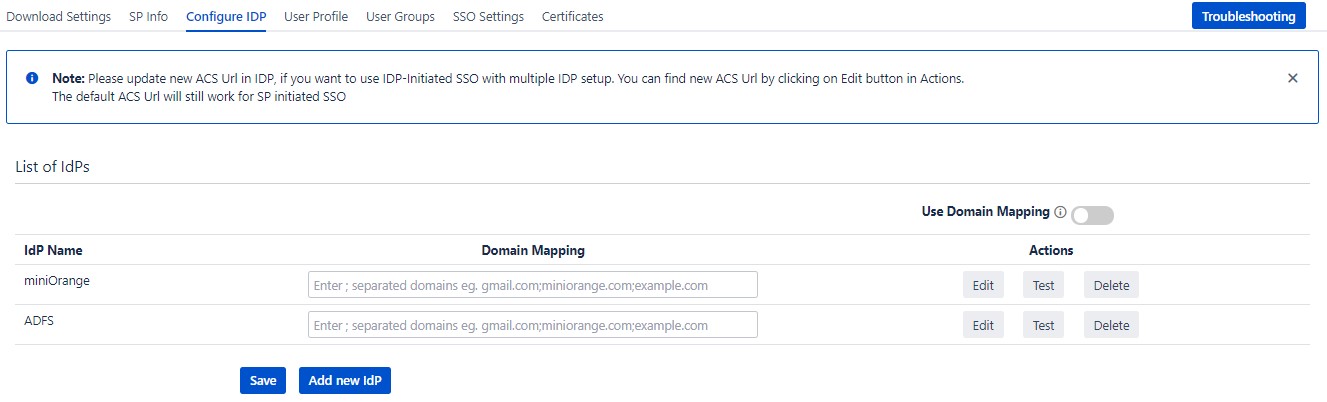
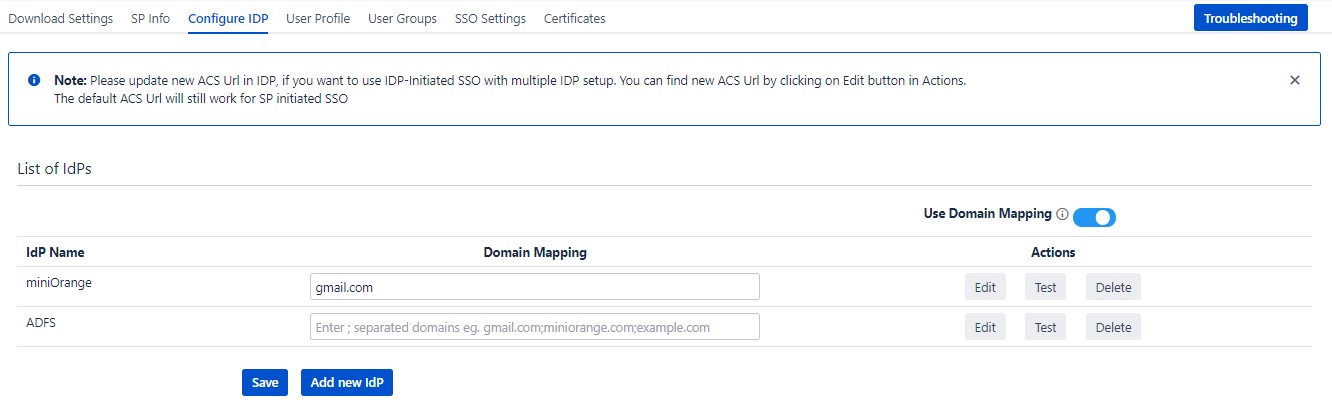
Step 4: Multiple IDPs
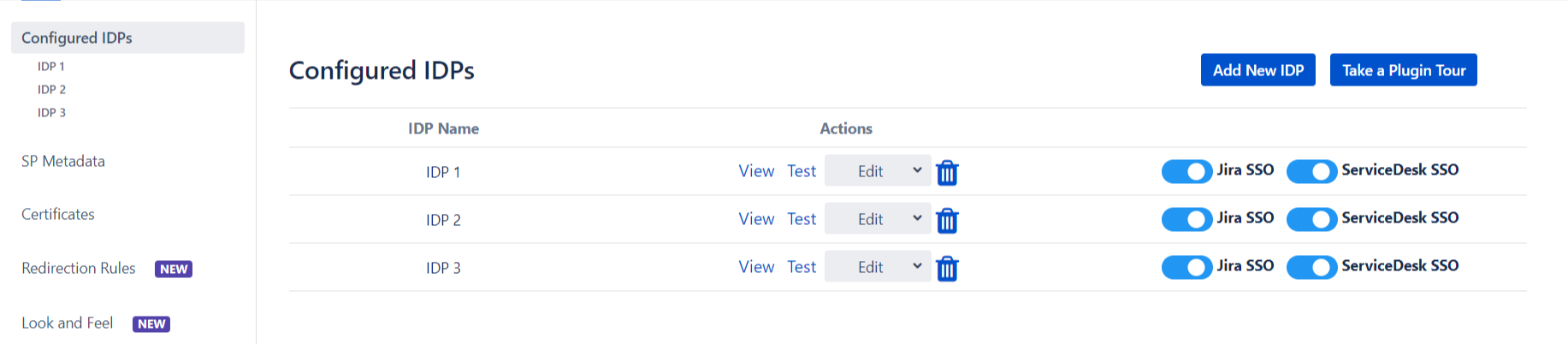
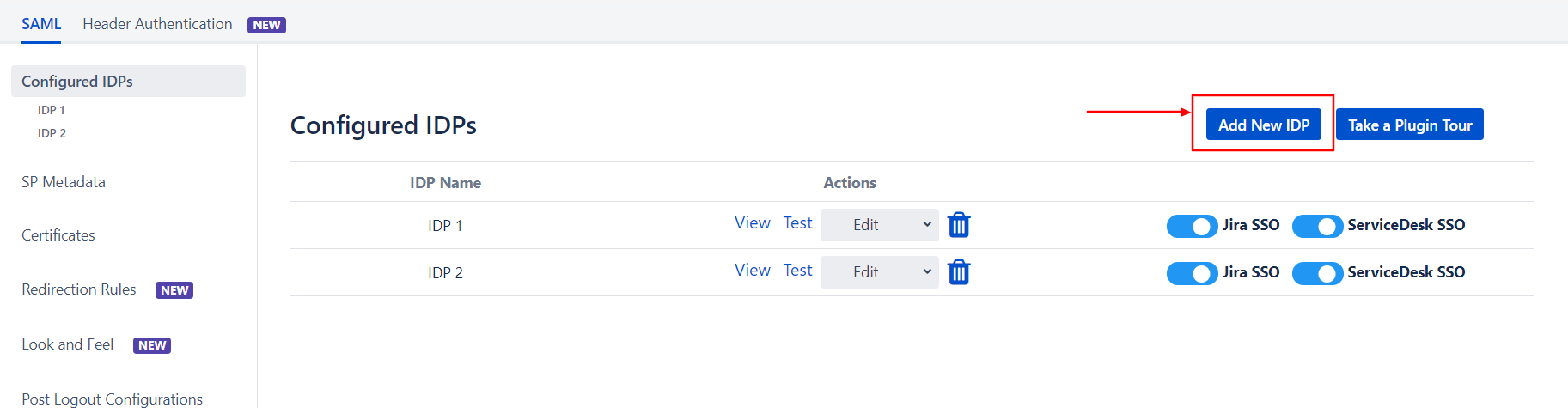
Step 4.1: Configuring Multiple IDPs
- If your use case requires Multiple IDPs to be configured on your SP, the plugin
supports that as well. You can add another IDP by going to the Configured IDPs section and
using the Add New IDP button.
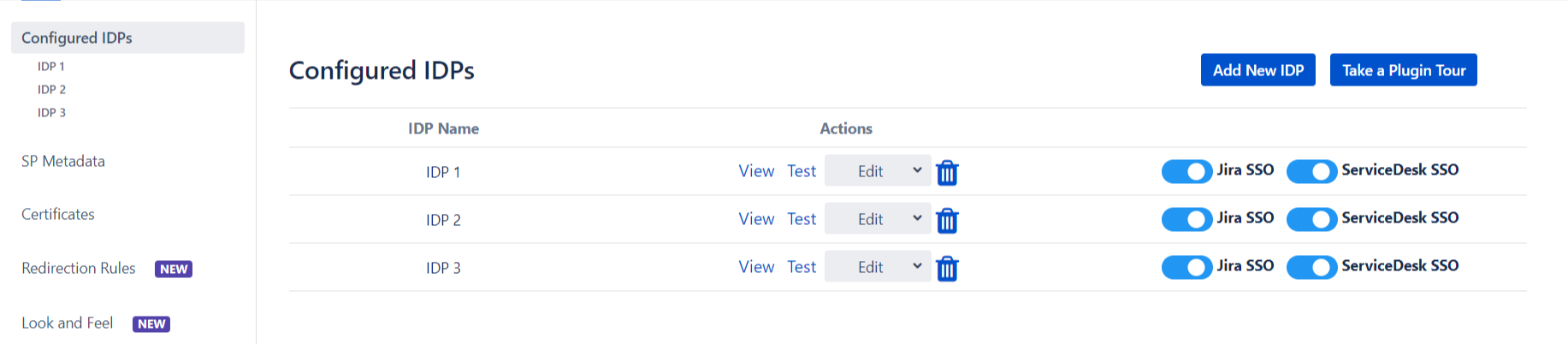
Step 4.2: Managing SSO with Multiple IDPs
-
If you have multiple IDPs configured, you can choose how you want your end users to
use these IDPs to perform SSO.
IDPs
to perform SSO.
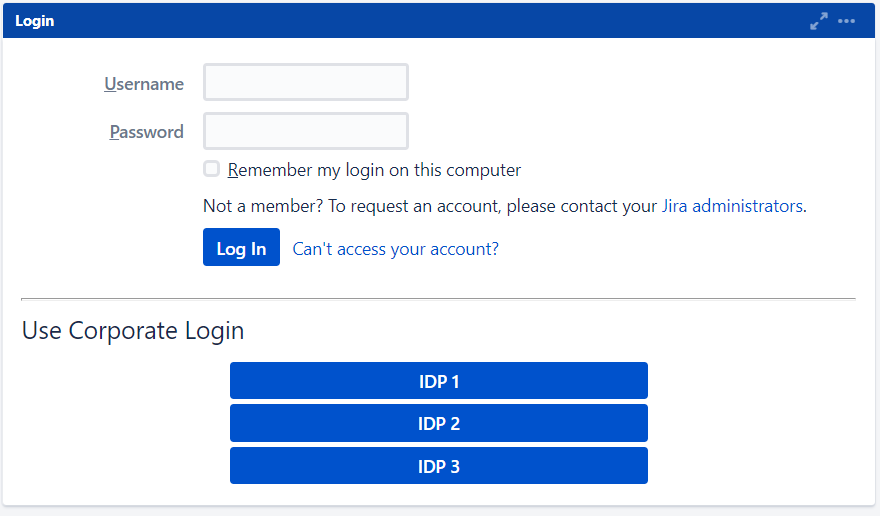
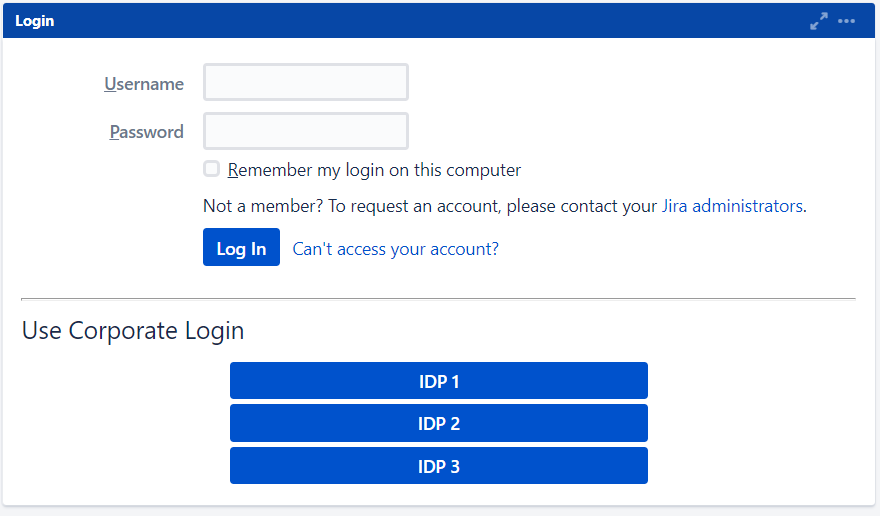
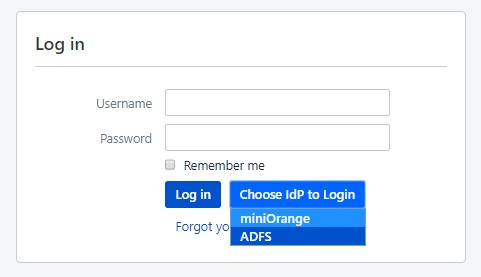
- For example you can
show the buttons for the different IDPs configured on the login page nad let the
users decide
which
IDP to use for SSO.
-
Or you could force certain users to user a specific IDP based on the domain of their
username/email.
- You will be able to configure
these rules in the Redirection Rules section, under the Redirection
Rules tab.
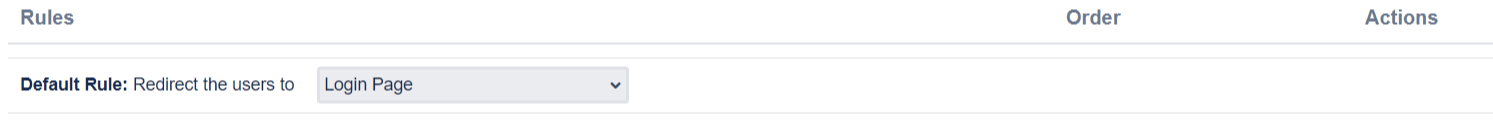
- By default one rule is always configured that will be applicable to all the users,
irrespective
of
their user domains.
-
For instance, if you want to display the login page with SSO buttons for each of the
IDPs then
your
Default Rule will be as follows :
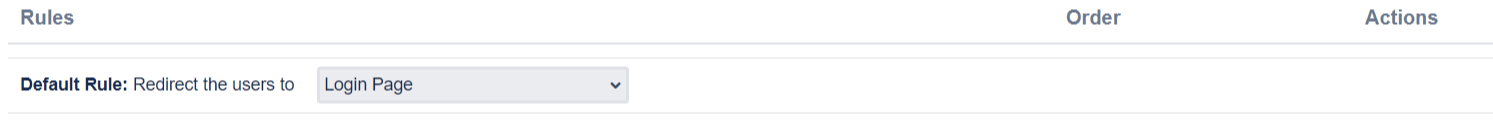
- Based on the default rule mentioned above, the login form will contain buttons for
each IDP. The
users will be free to choose
whichever IDP they want to use to initiate SSO.
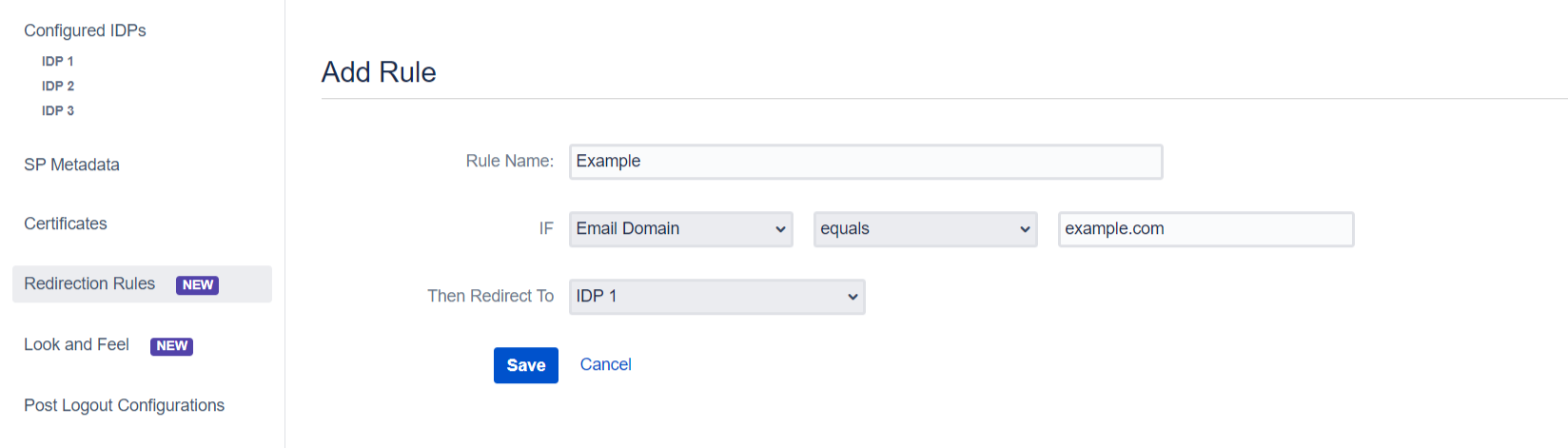
- You can also configure a rule so that your users will automatically be redirected to
an IDP
based on
their email domains.
-
For example, if you want users with example.com as domain to be redirected to
IDP
1
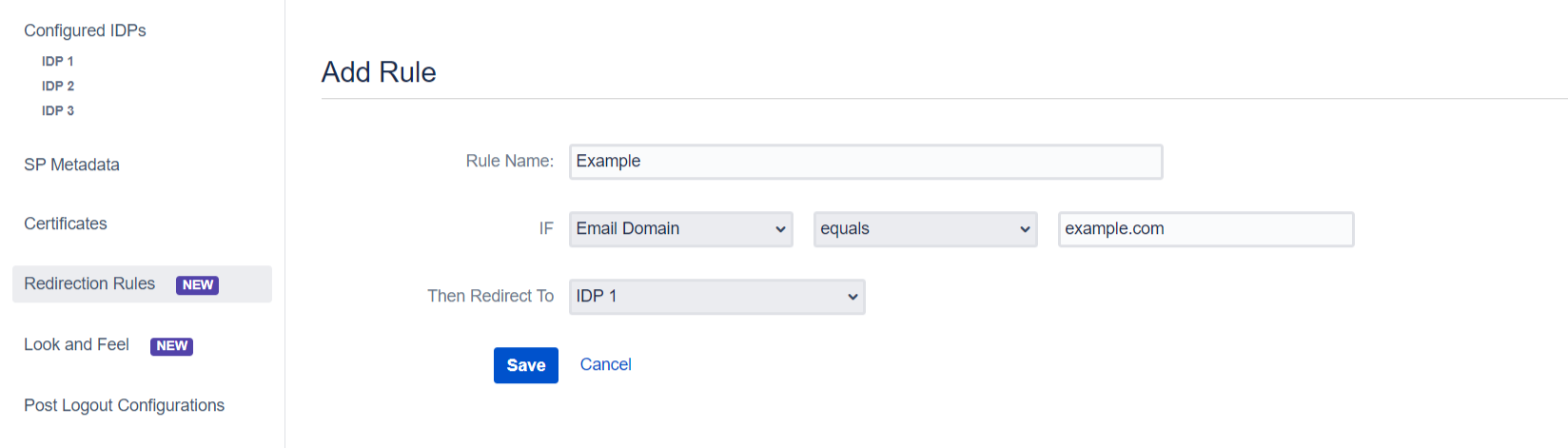
you can add a rule by :
- Click on the Add Rule button in the Redirection
Rules
tab
- Enter a name for your rule in Rule Name
- In the IF statement select Email Domain in
the first
drop-down
- For the same statement select equals in the second
drop-down.
- In the last field of the IF statement, enter the email
domain(example.com
for
the purpose of this example)
- In the Then Redirect To drop-down, select the IDP you want
the users
with
example.com to be redirected to(IDP 1 in this case)
- Click on Save
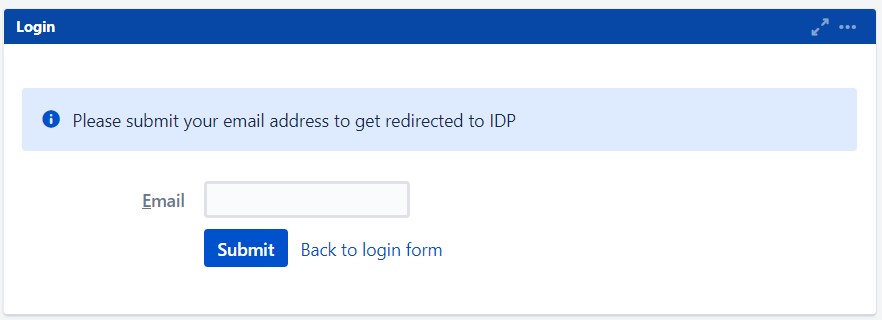
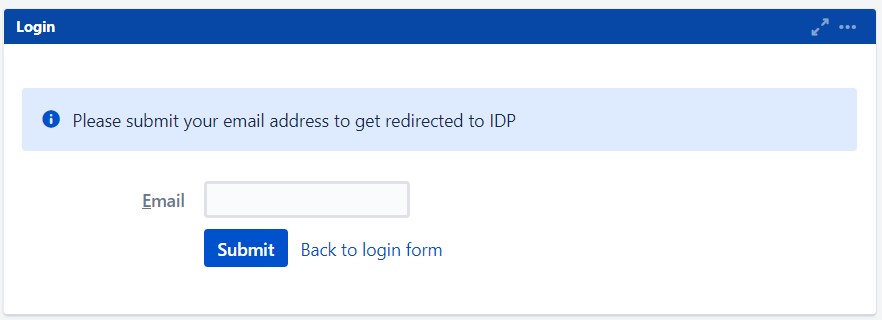
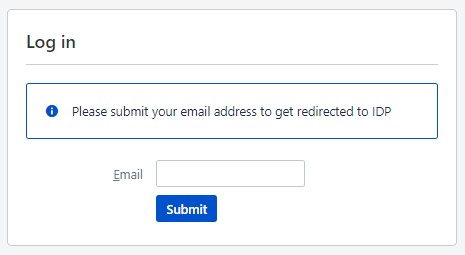
- When a rule such as an example given above is configured, a login form will be
displayed to the
users where they will have to input
their email address.
- In this section you will also configure SSO for admin users, access to anonymous
pages and an
emergency URL to by-pass SSO.
These settings can be found under the Settings tab of this section.
 Hi! Do you need help with this guide?
Hi! Do you need help with this guide?


 By Metadata URL:
By Metadata URL:
 Import the metadata
Import the metadata