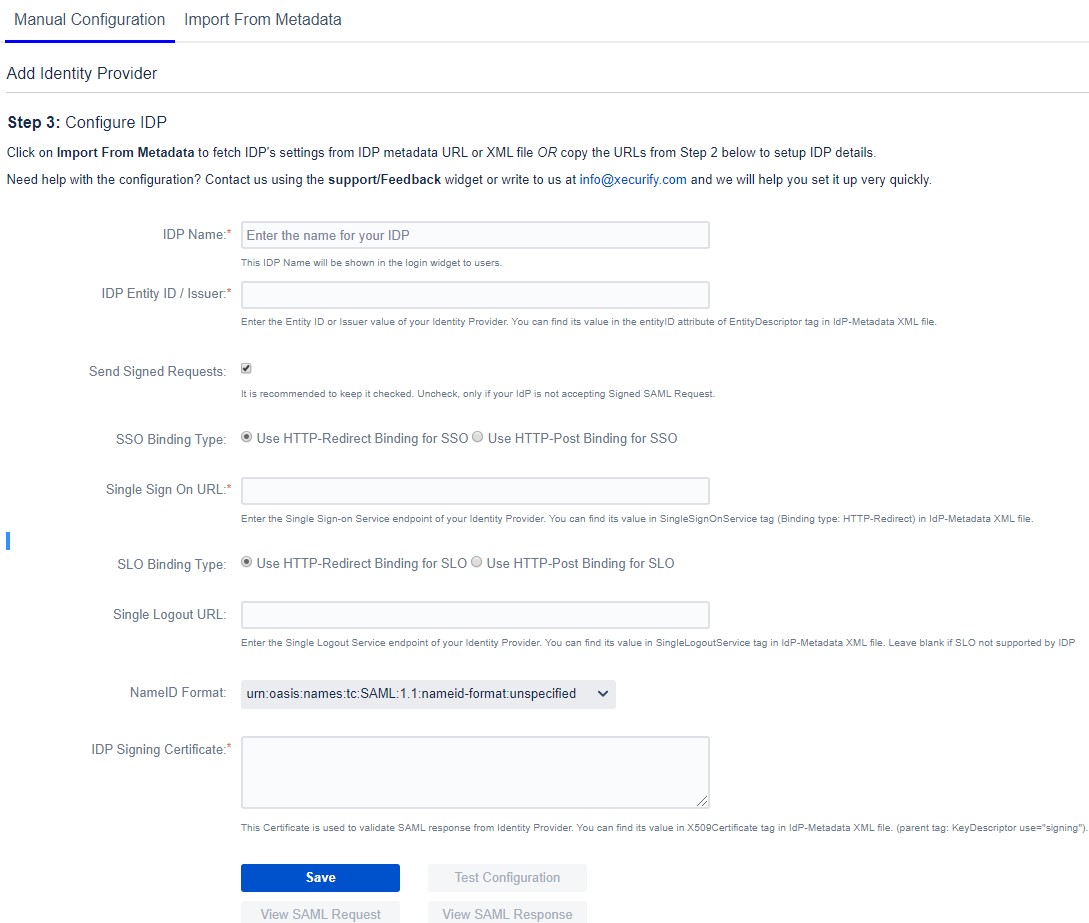
Configure New IDP
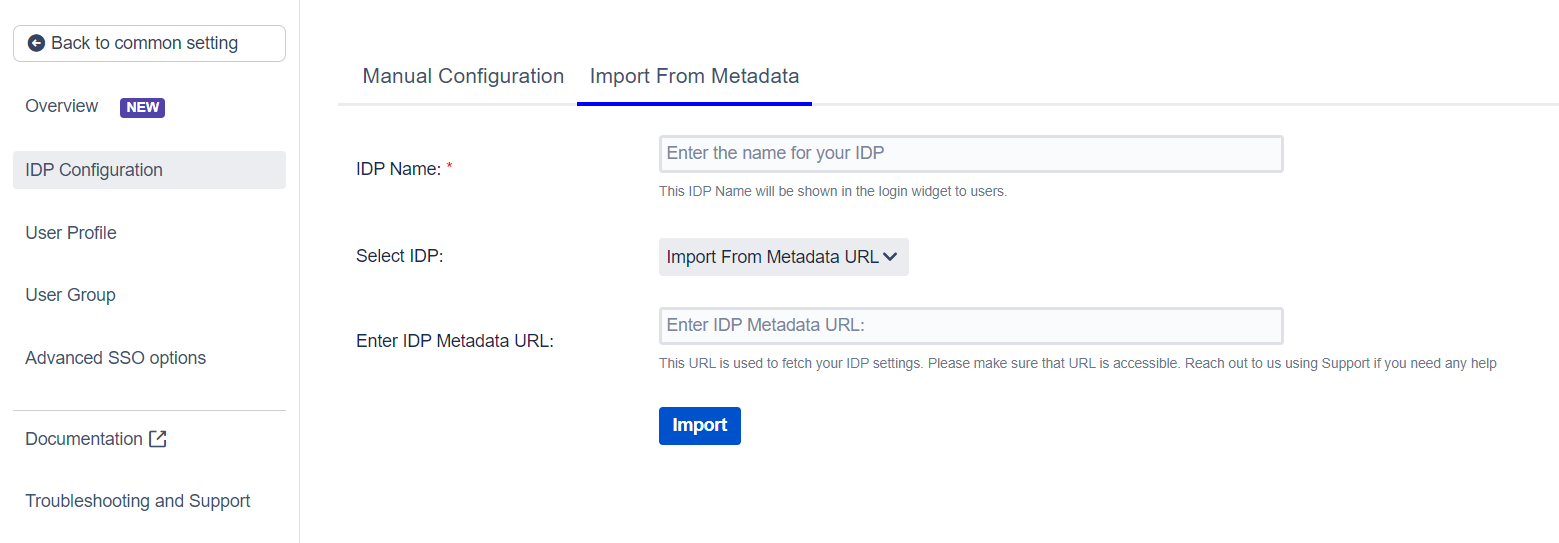
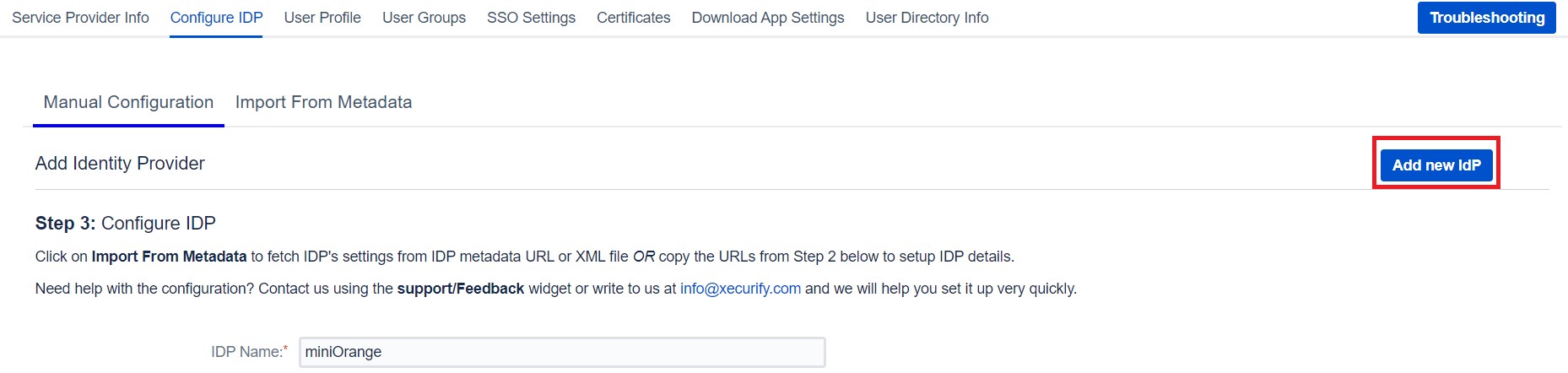
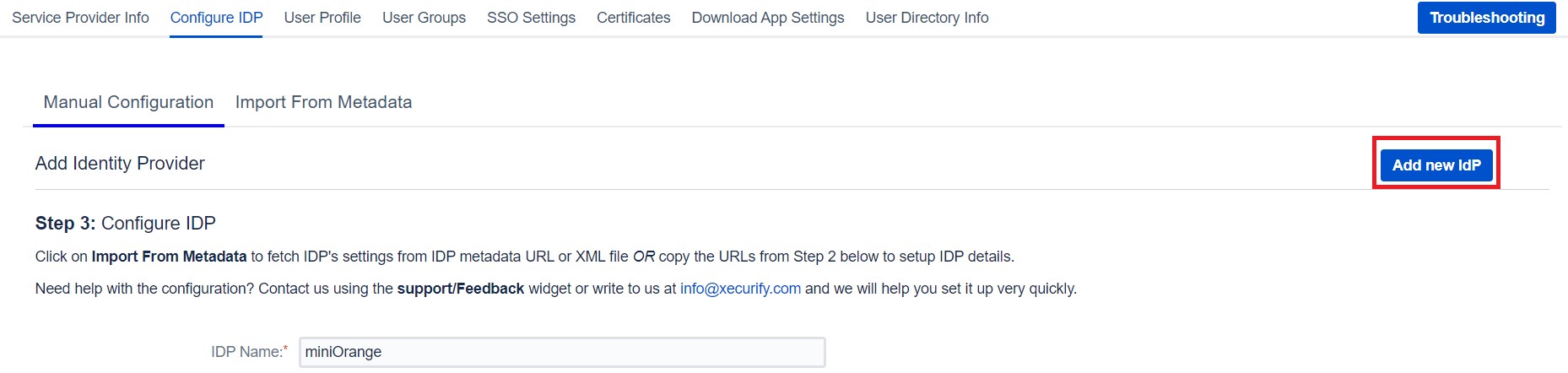
If you already have one IDP & you are looking to add Second IDP then you can do it by performing the following steps.
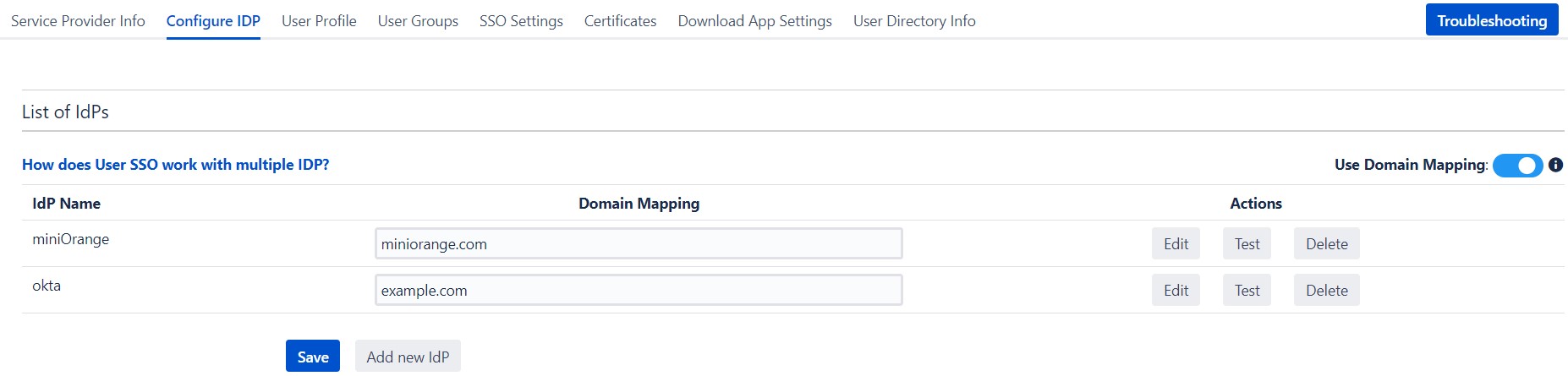
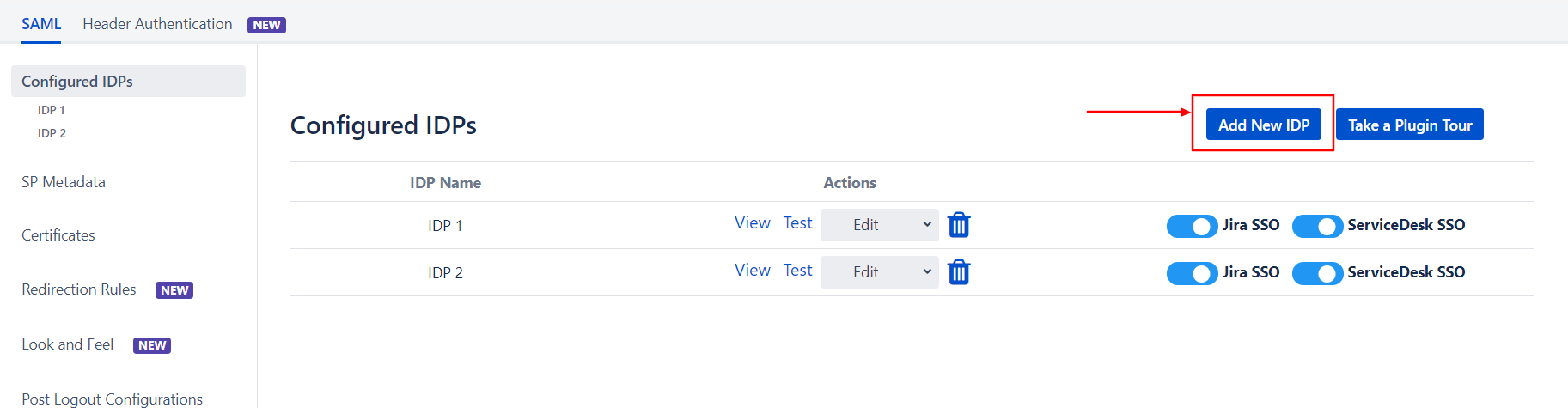
- Navigate to Configure IDP tab.
- Click on Add new IDP.
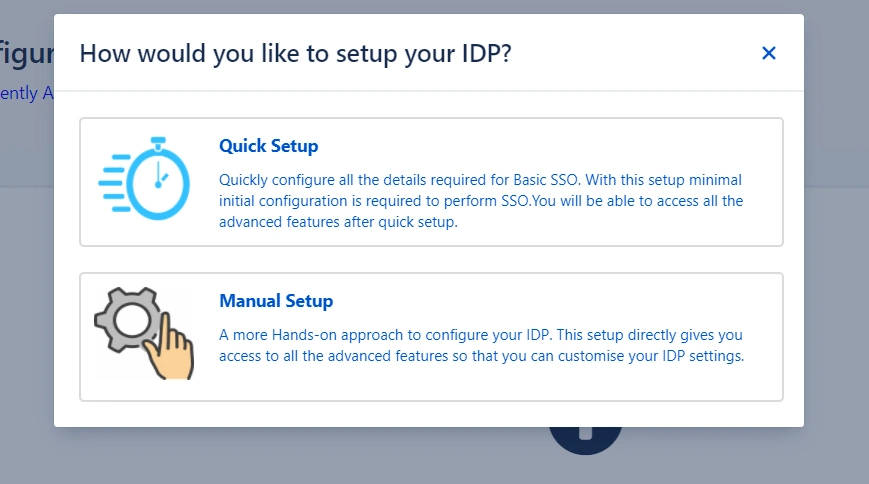
- It will present a blank form & you can configure new IDP using steps from Single IdP Setup.
 Configure multiple IDPs
Configure multiple IDPs
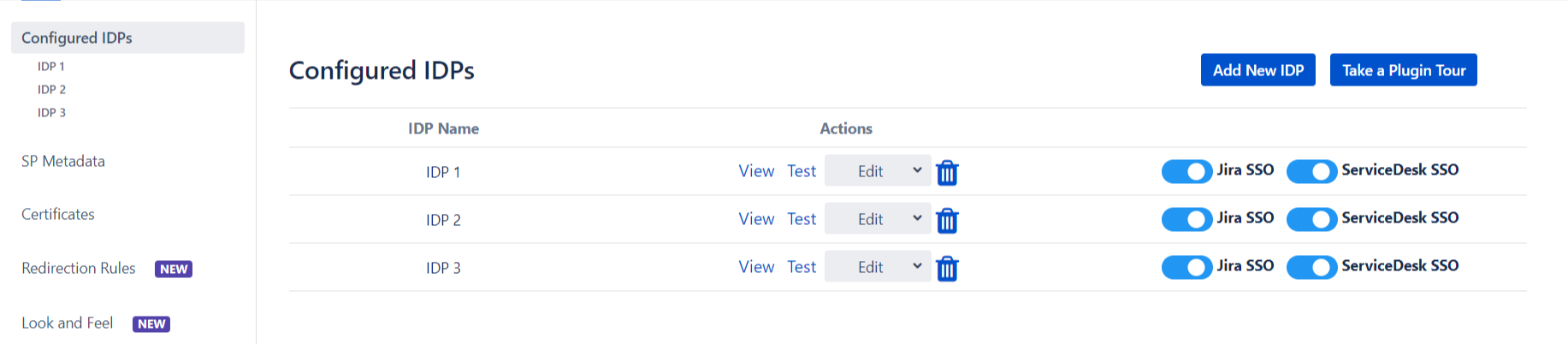
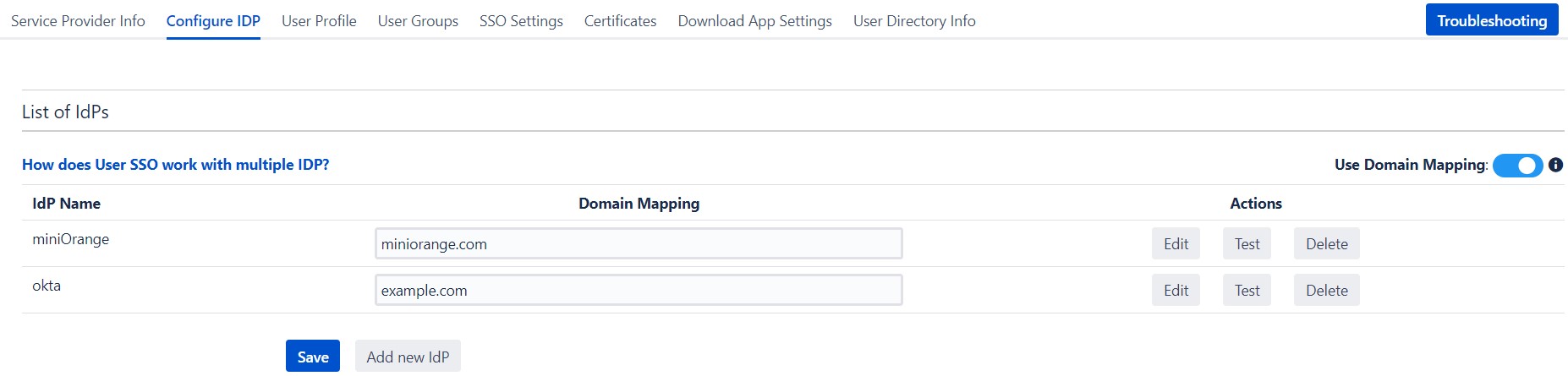
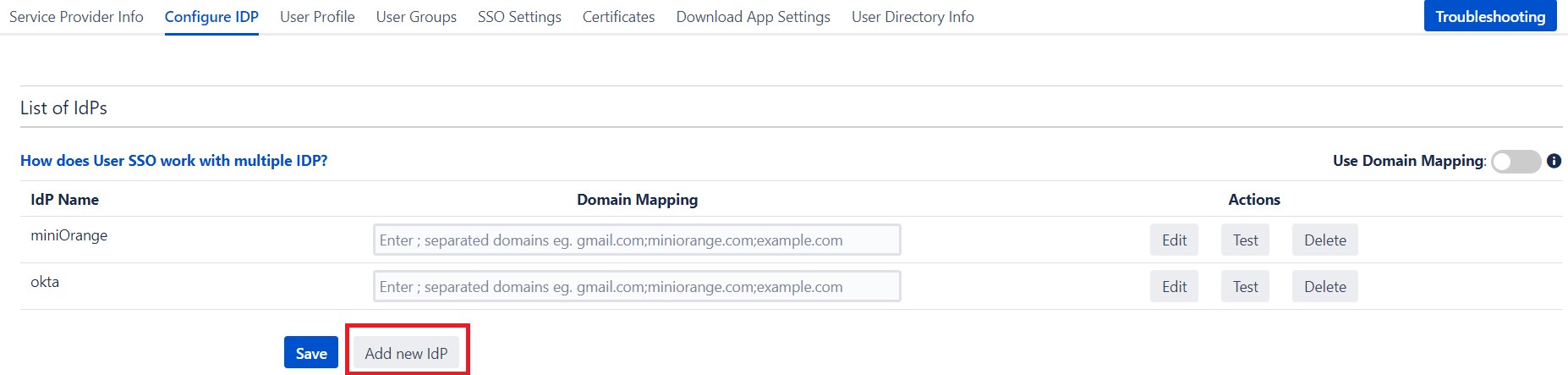
If you have configured more than two IDPs then it will show you the list of IDP that you have configured with Jira.
Click on
Add new IdP button for adding new IDP on Jira. The steps for adding new IDP will remain the same.
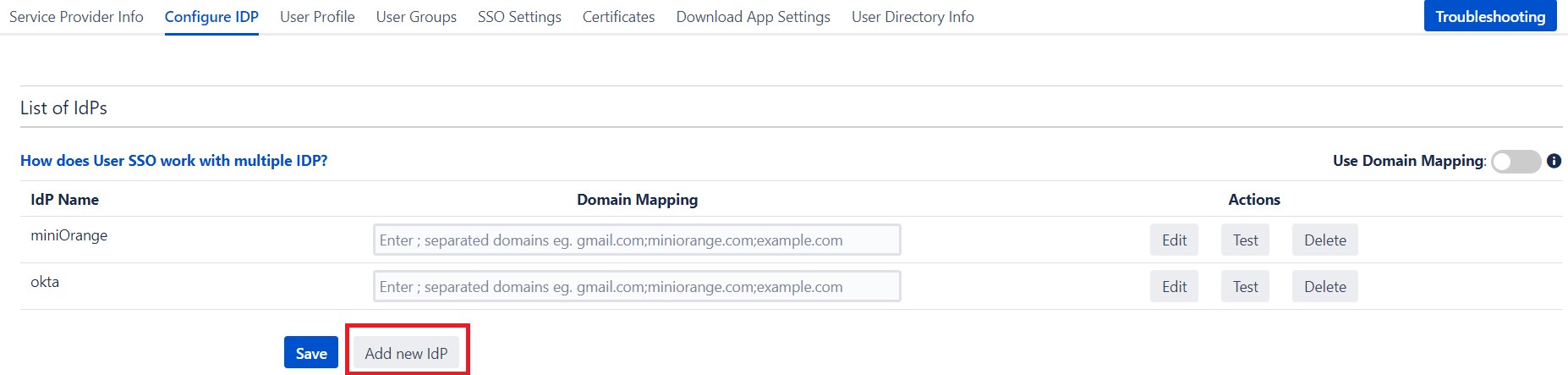
An operation that you can perform with List of IdPs page.
- Add / delete Identity Provider.
- Test Connection between Jira & IdP by click on Test button for respective IDP.
- Edit the IdP configuration by clicking on the Edit button.
- You can allow an only specific set of users to access Jira by using Domain Mapping.
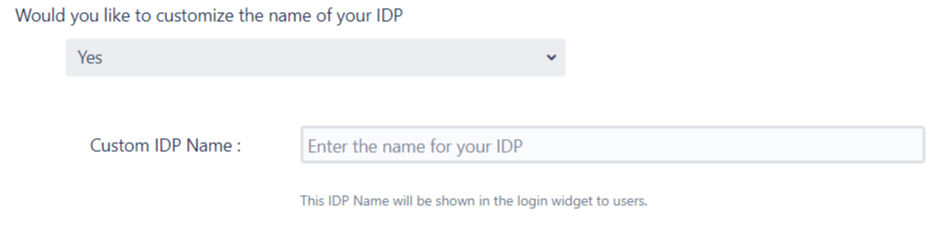
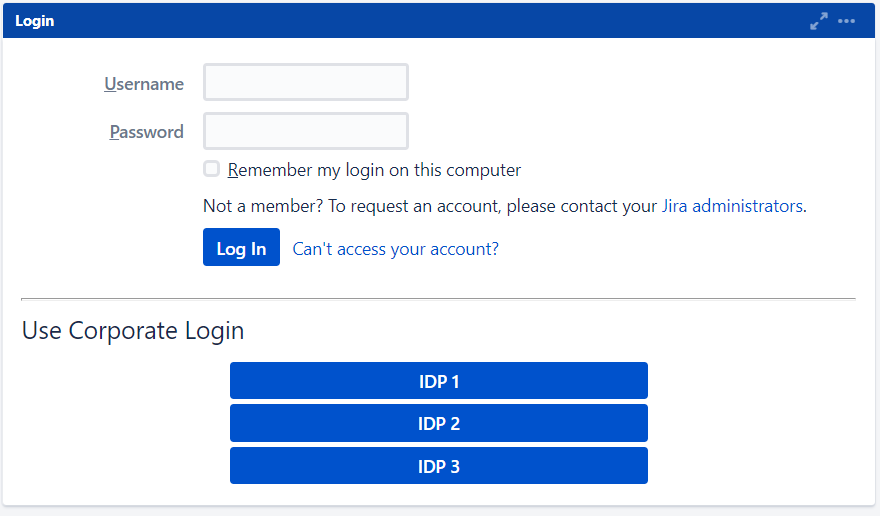
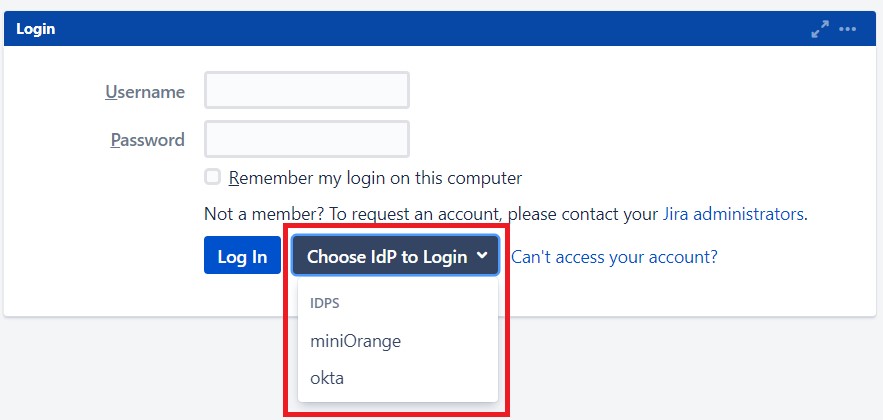
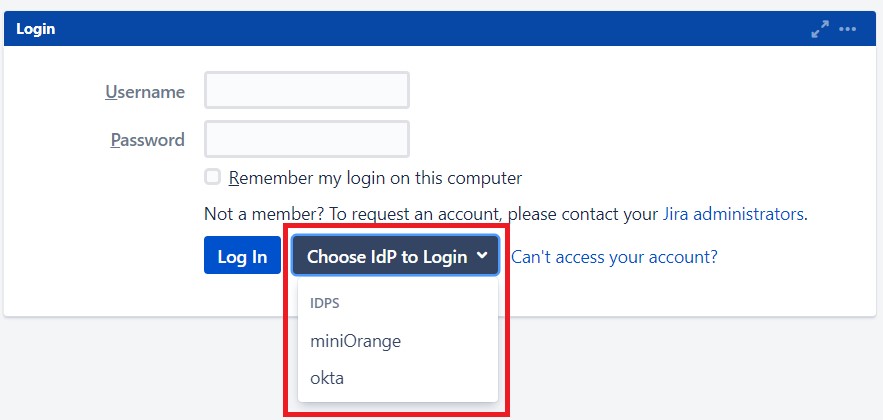
Single Sign-On with Multiple Identity Provider(IDP)
Select your IdP from the list. It will redirect you to selected IdP login page.
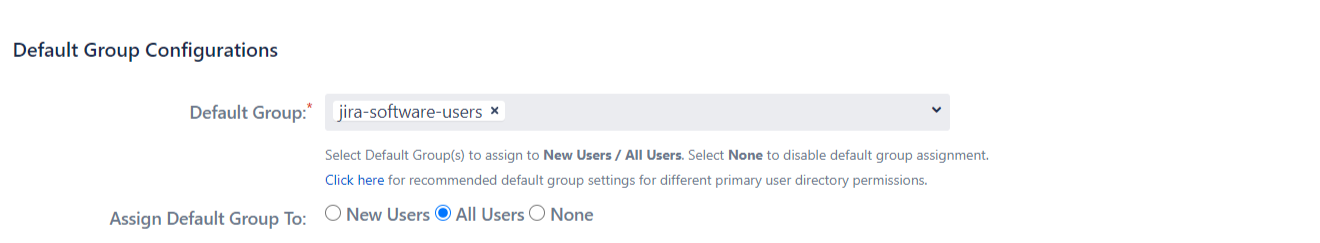
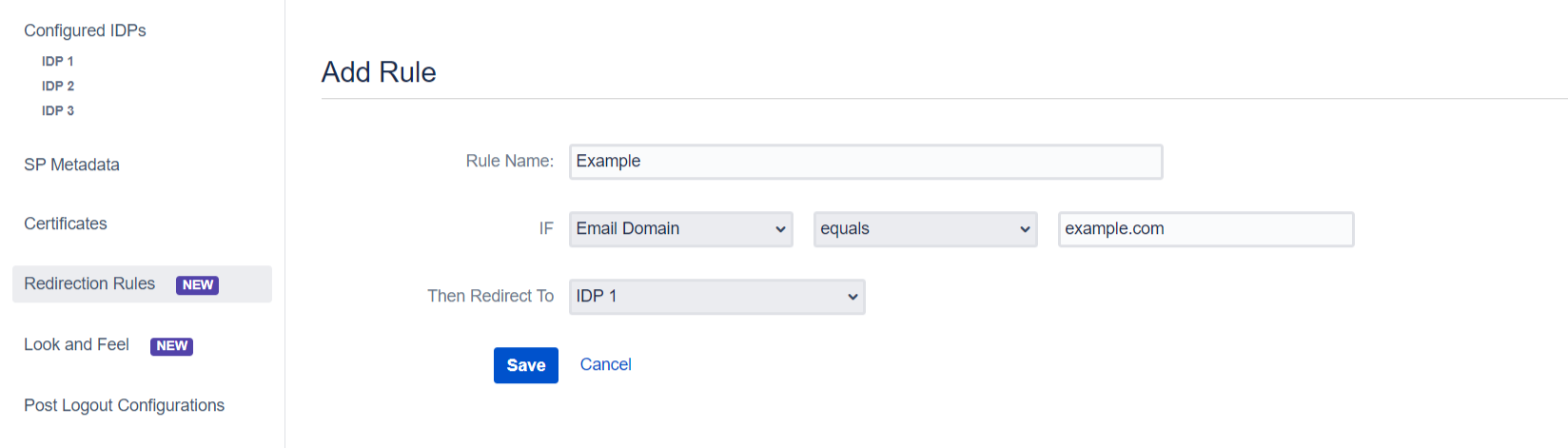
 Configure Domain Mapping
Configure Domain Mapping
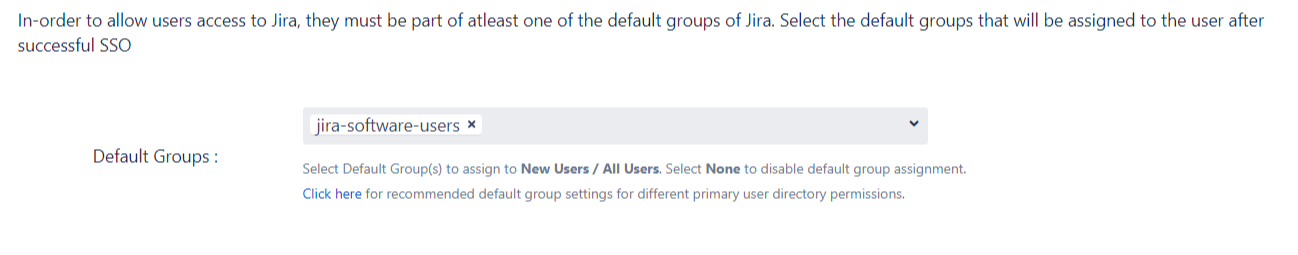
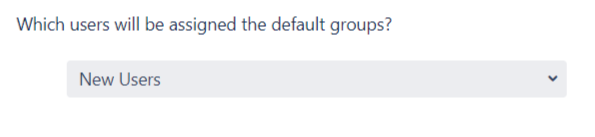
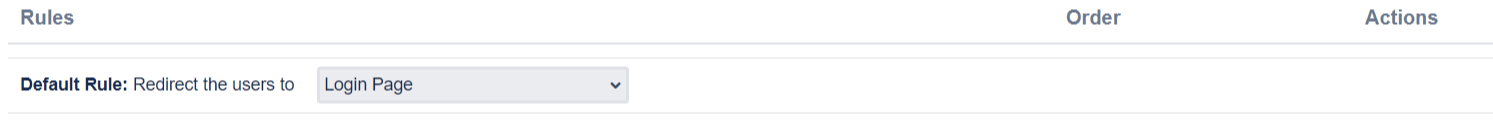
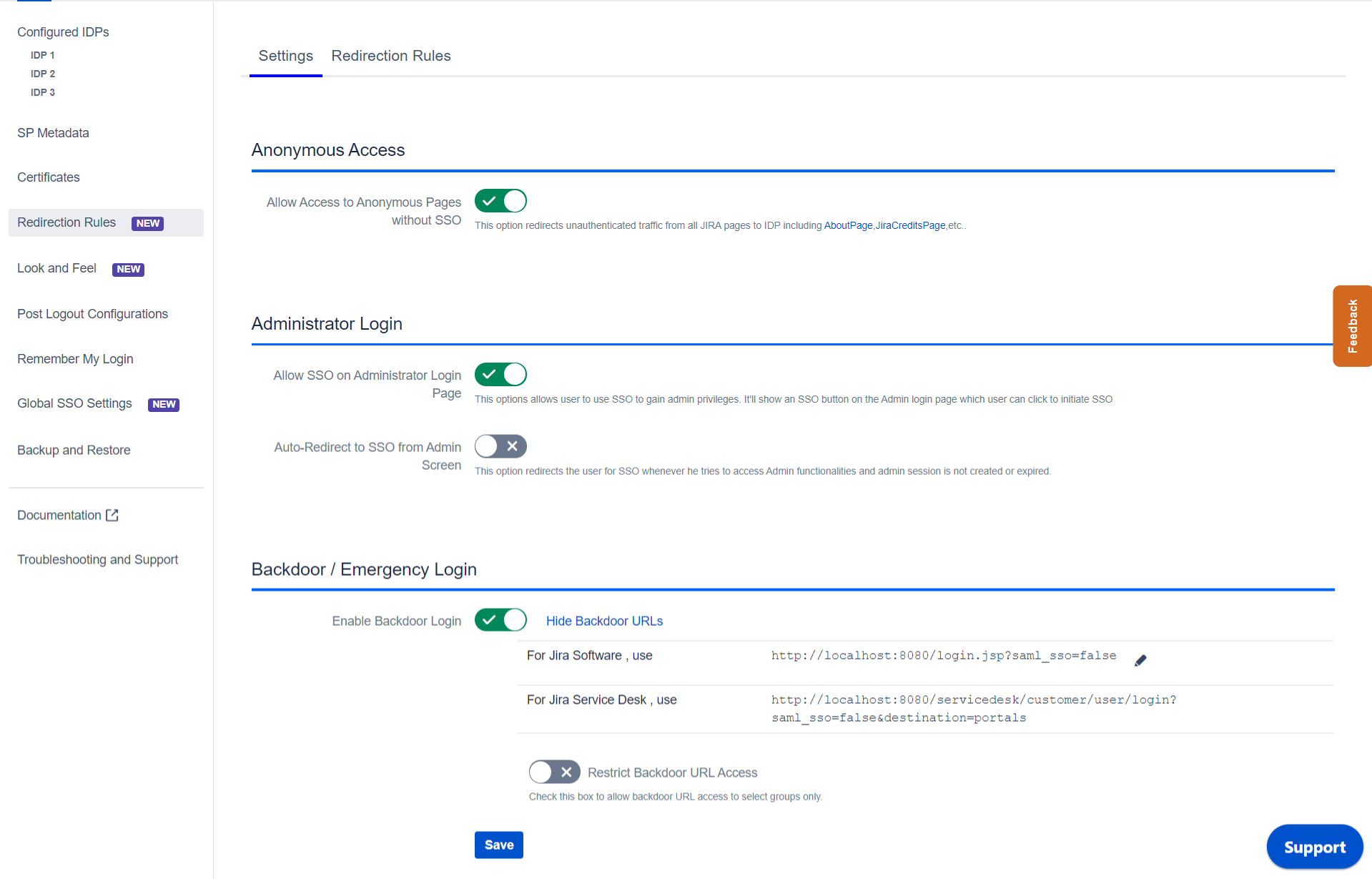
You can enable domain mapping using
Use Domain Mapping option.
Once enable it, you need add domain name against each IDP.
After enabling Domain Mapping it allows SSO only for those users whose domain matches with the specified one.
 Single Sign-On using Domain mapping
Single Sign-On using Domain mapping
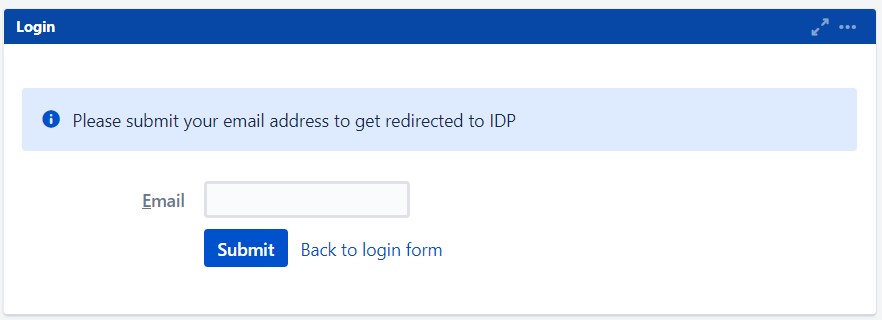
Enter the user email address. It will check your domain name with the configured domain if it matches then it will redirect you to the respective Identity Provider Login page.
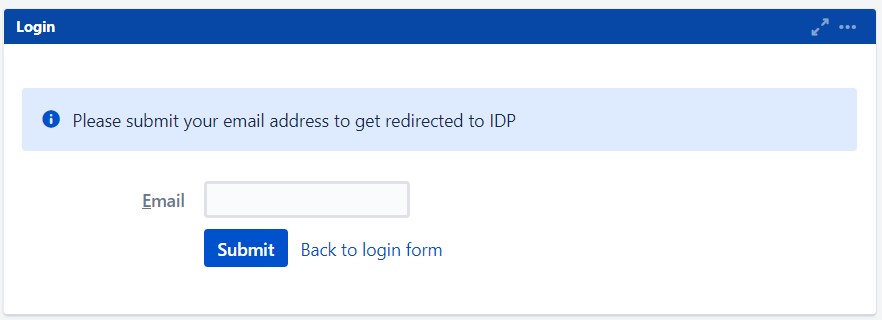
This is how the login screen would appear after enabling domain mapping.


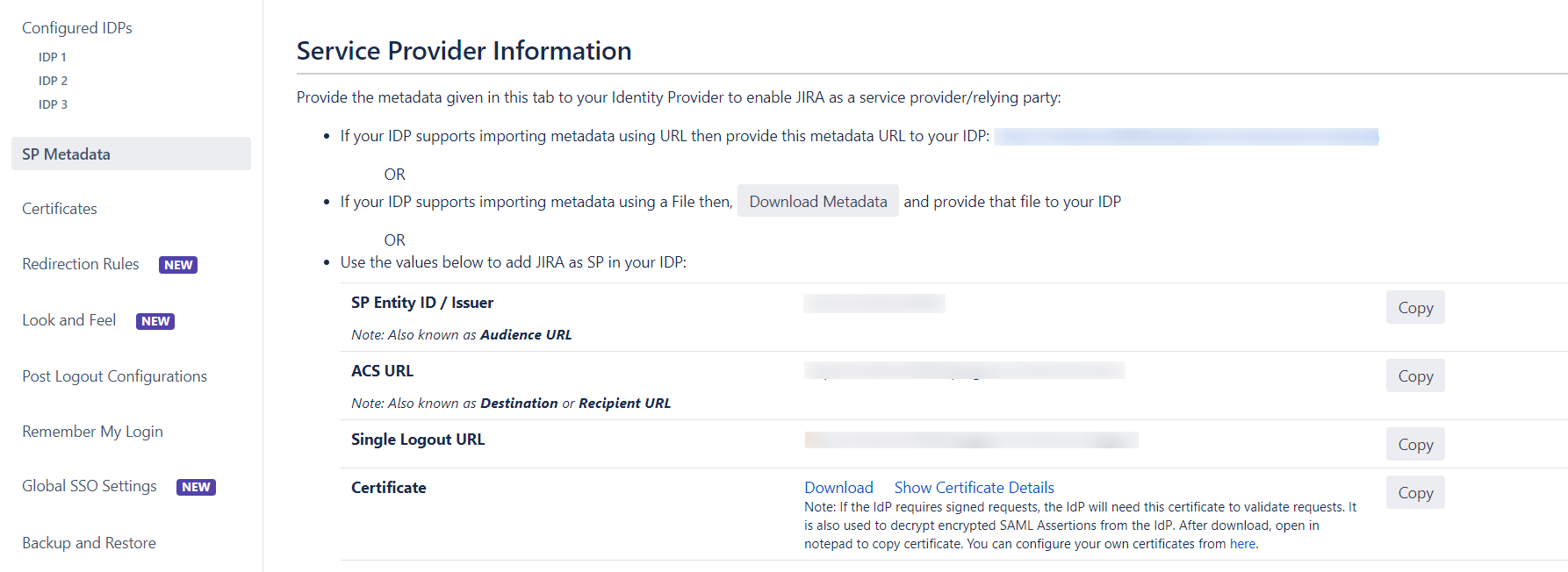
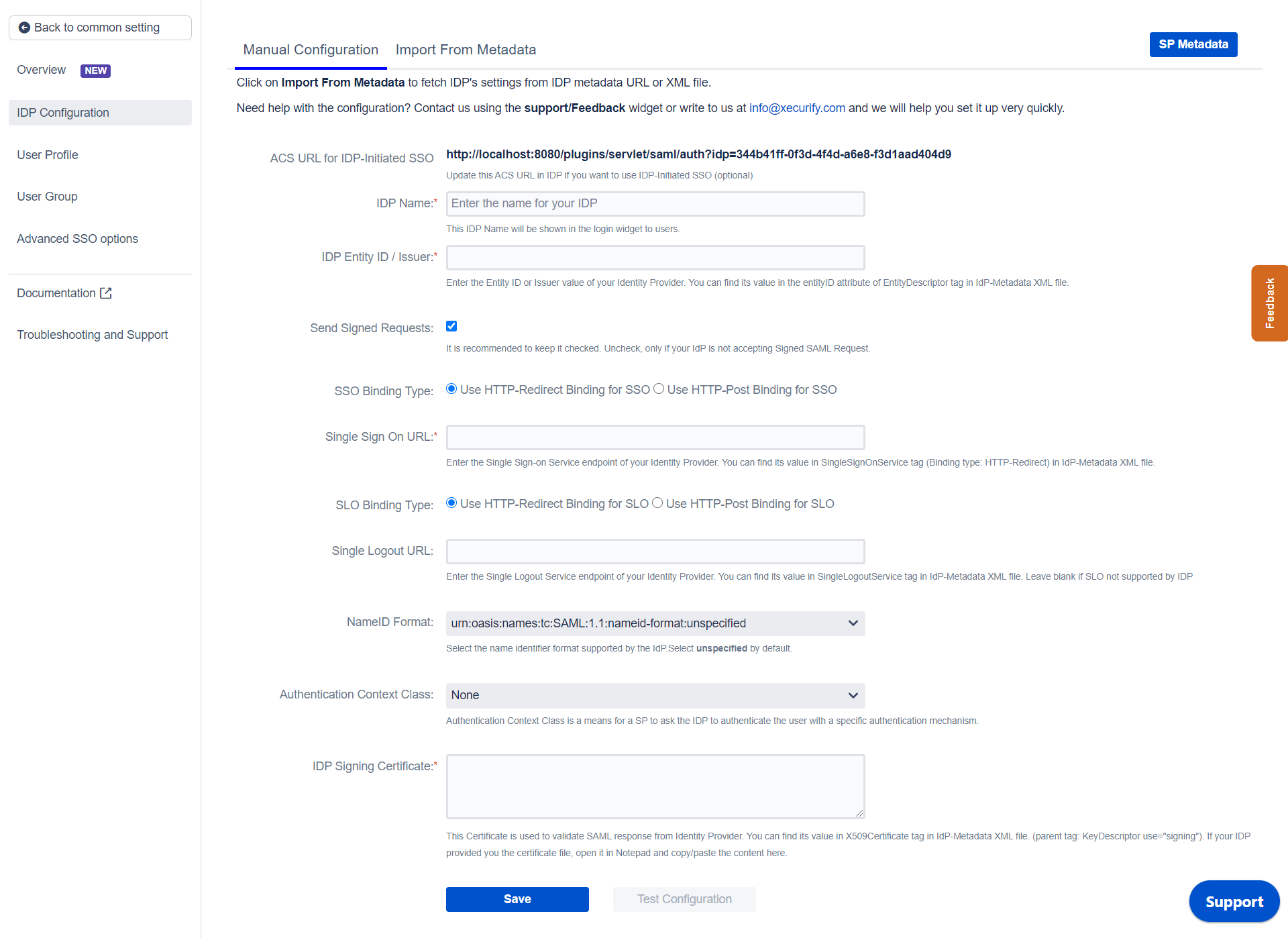
 Prerequisites:
Prerequisites: 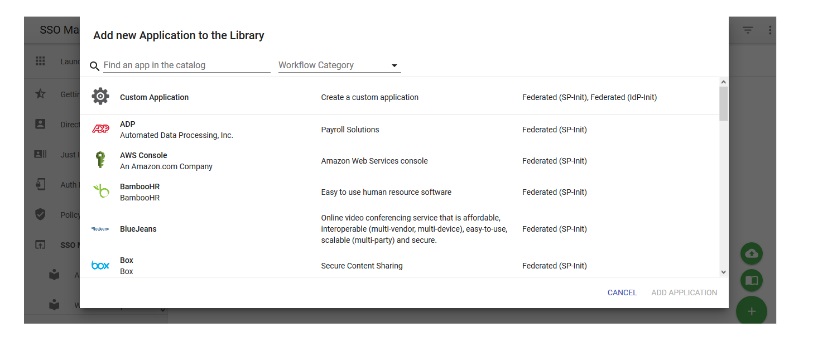
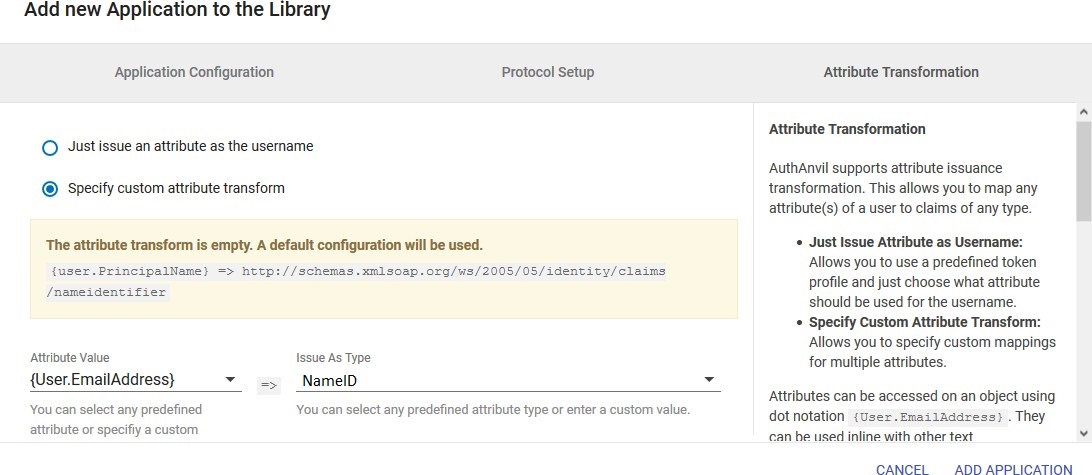
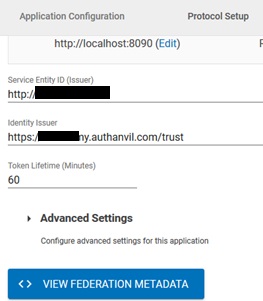
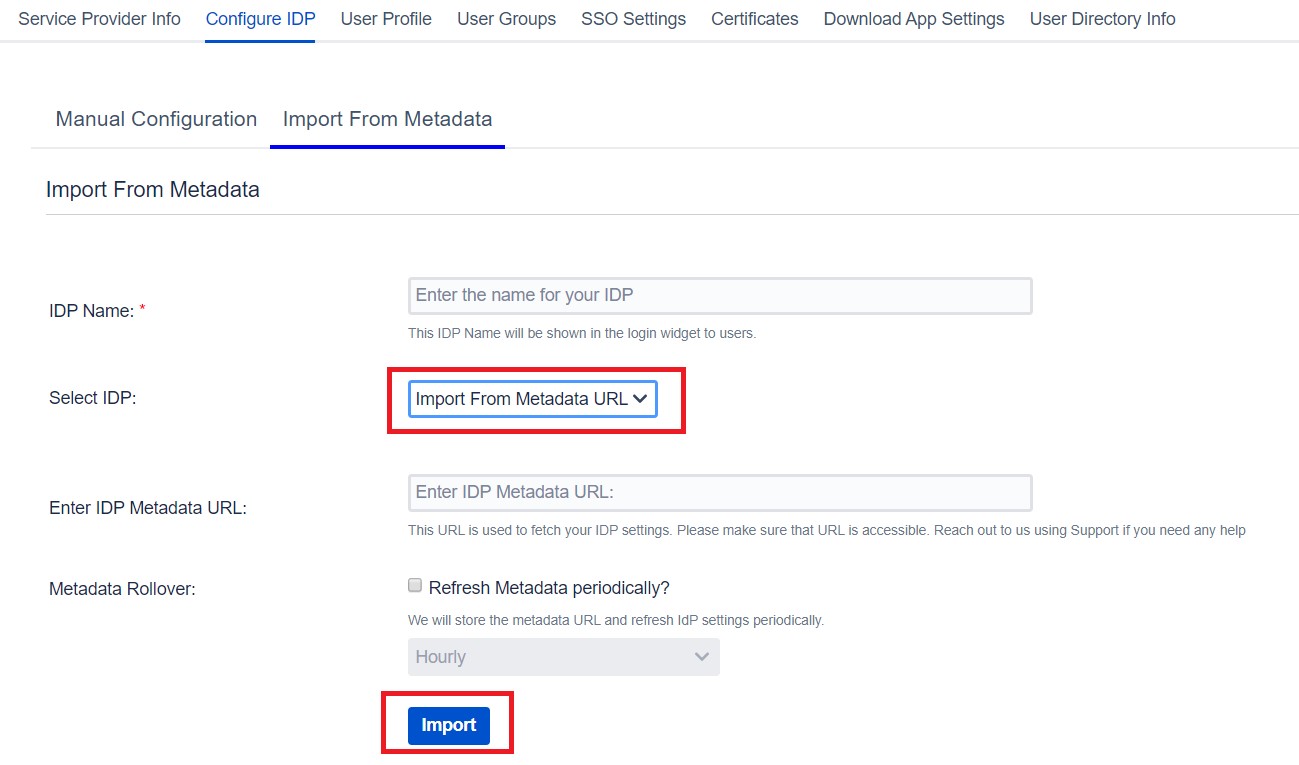
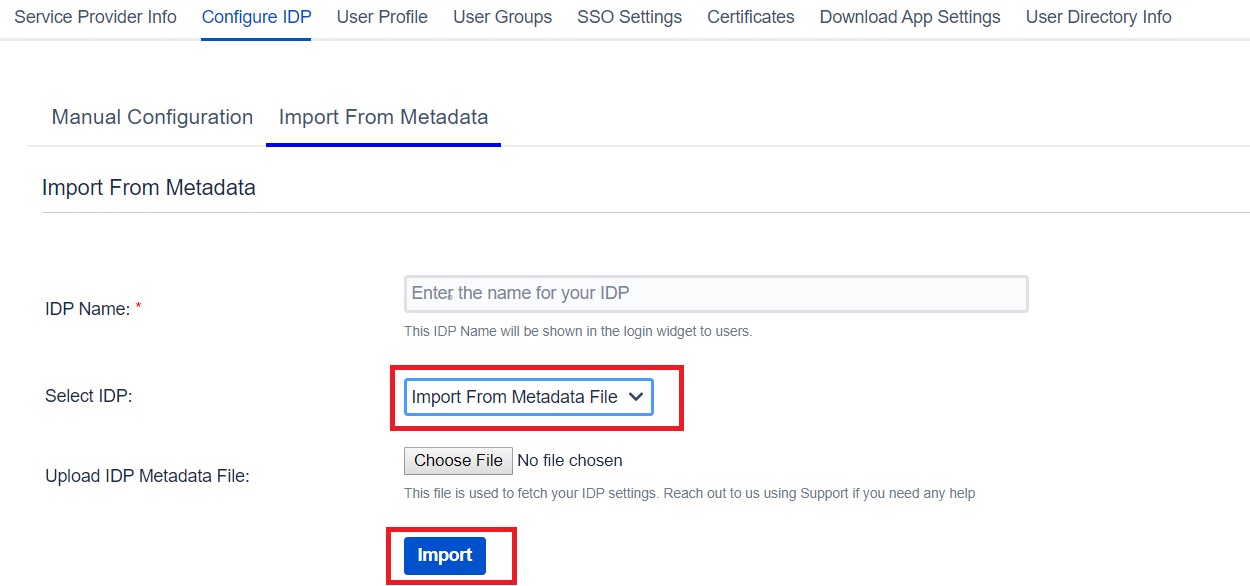
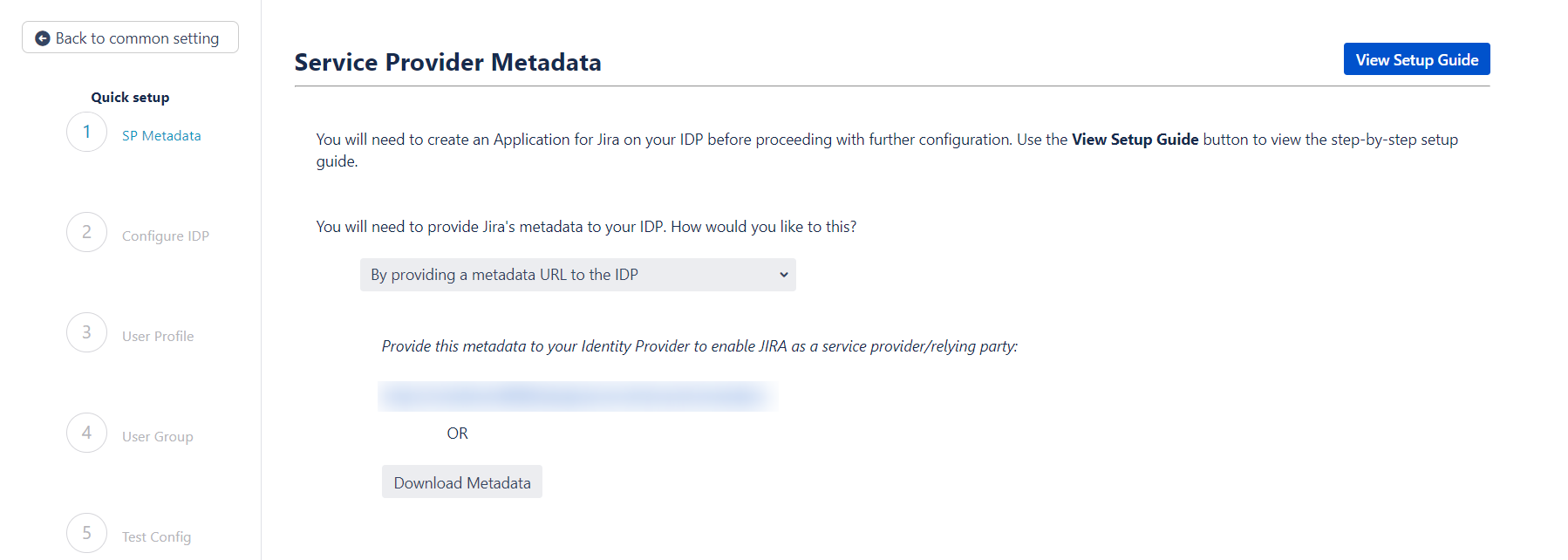
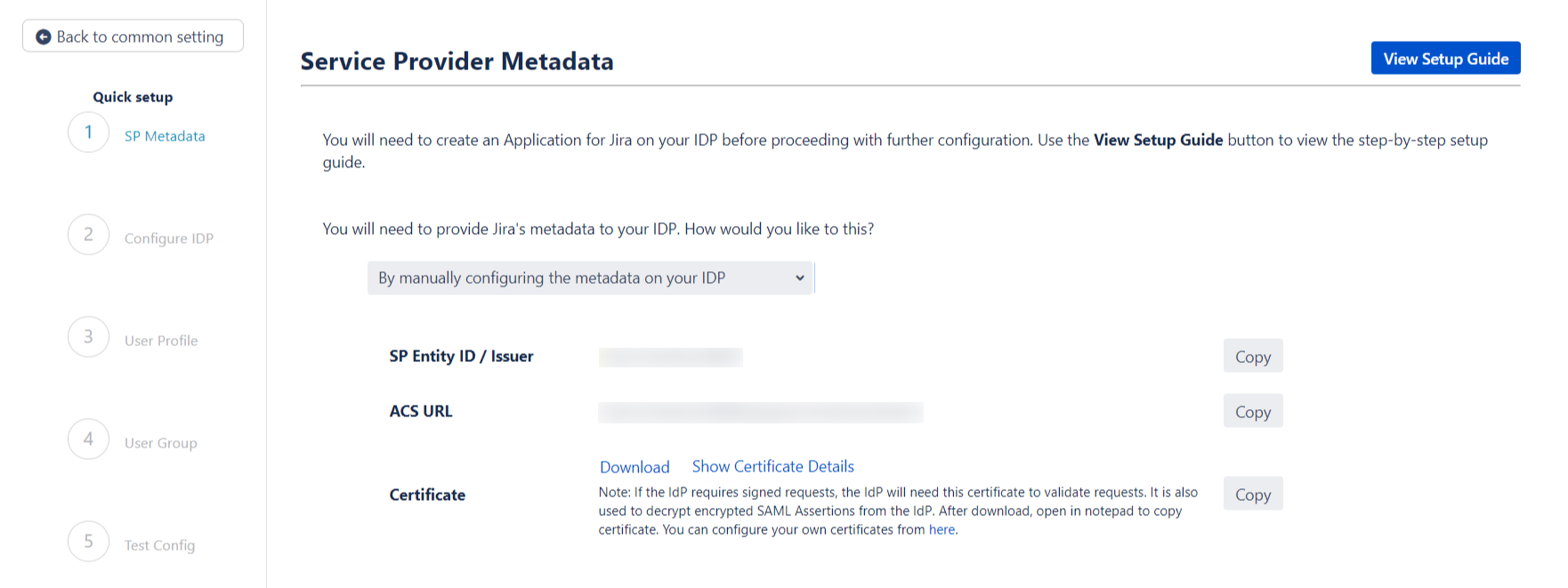
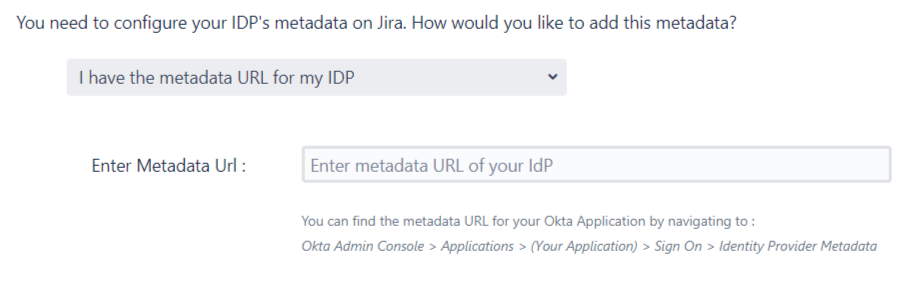
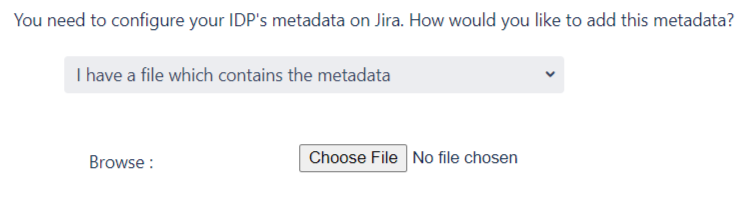
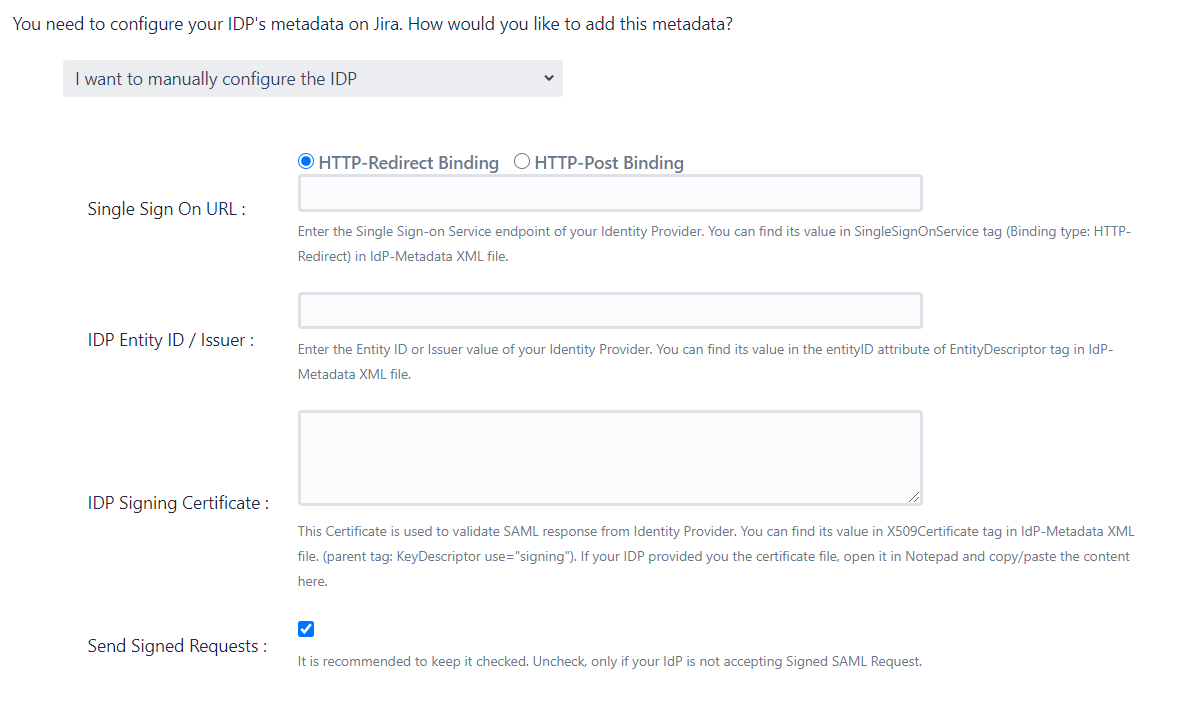
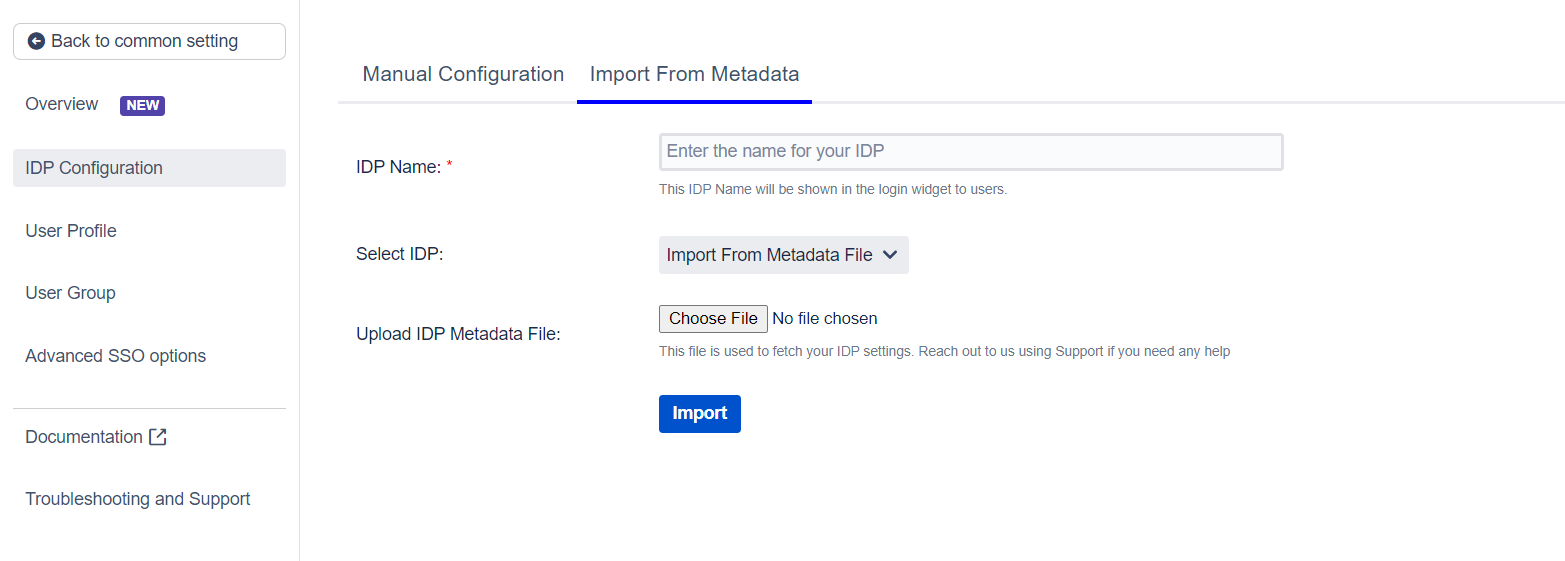
 Import the metadata
Import the metadata