Crowd OAuth/OIDC app gives the ability to enable OAuth/OIDC Single Sign-On for JIRA, Confluence, Bitbucket, Bamboo, Fisheye, and other connected applications from any OAuth/OpenID Identity Providers. Here we will go through a guide to configure SSO between Crowd and Identity Provider. By the end of this guide, your IdP users should be able to log in and register to Crowd Software.
Pre-requisites
To configure your Identity Provider integration with Crowd OAuth/OIDC SSO, you need the following items:
- Crowd should be installed and configured.
- Admin credentials are set up in Crowd.
- Crowd Server is HTTPS enabled (optional).
- Valid Crowd Server or Datacenter Licence.
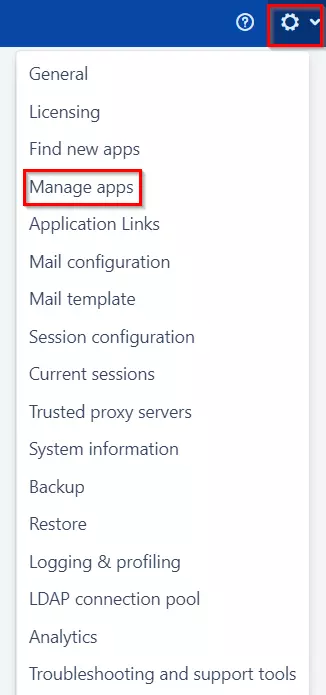
Download And Installation


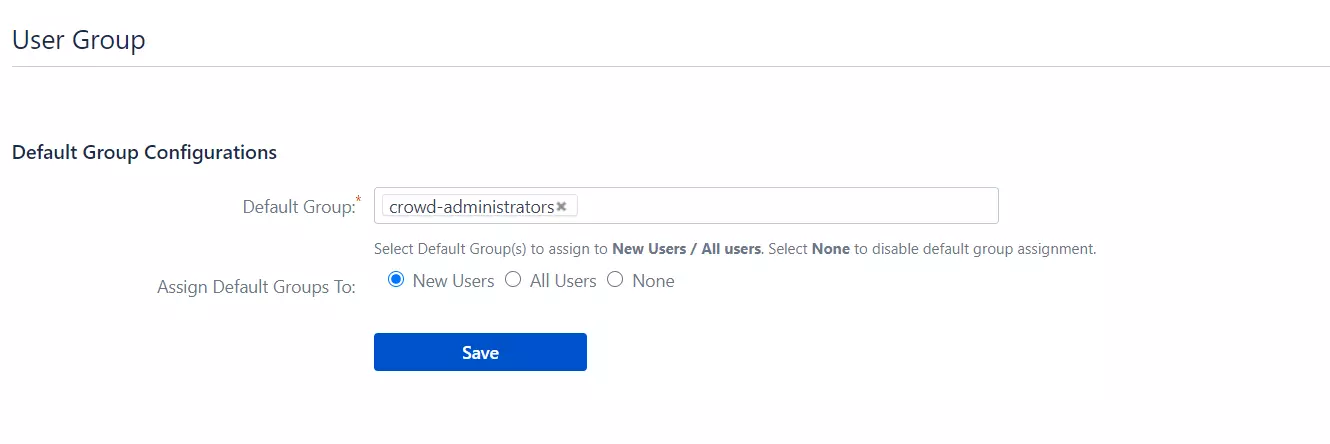
 Setting default group
Setting default group