Bamboo SAML app gives the ability to enable SAML Single Sign On for Bamboo Software. Bamboo Software is compatible with all SAML Identity Providers. Here we will go through a guide to configure SSO between Bamboo and your Identity Provider. By the end of this guide, users from your Identity Provider users should be able to login and register to Bamboo Software.
Pre-requisites
To integrate your Identity Provider(IDP) with Bamboo, you need the following items:
- Bamboo should be installed and configured.
- Bamboo Server is https enabled (optional).
- Admin credentials are set up in Bamboo .
- Valid Bamboo Server Licence.
Download And Installation
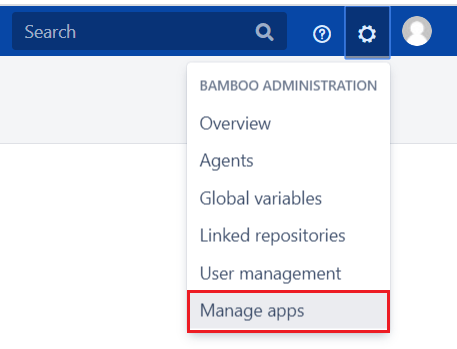
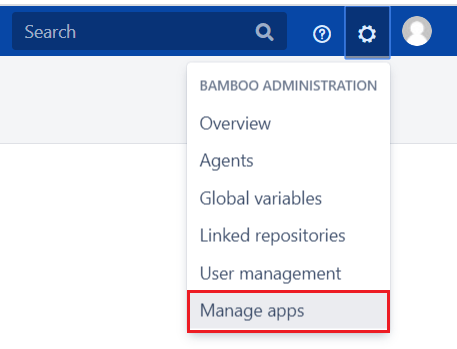
- Log into your Bamboo instance as an admin.
- Navigate to the settings menu and Click Manage Apps.
- Click Find new apps or Find new add-ons from the left-hand side of the page.
- Locate Bamboo SAML Single Sign On/SSO, SAML SSO via search.
- Click Try free to begin a new trial or Buy now to purchase a license for Bamboo SAML Single Sign On/SSO, SAML SSO.
- Enter your information and click Generate license when redirected to MyAtlassian.
- Click Apply license.


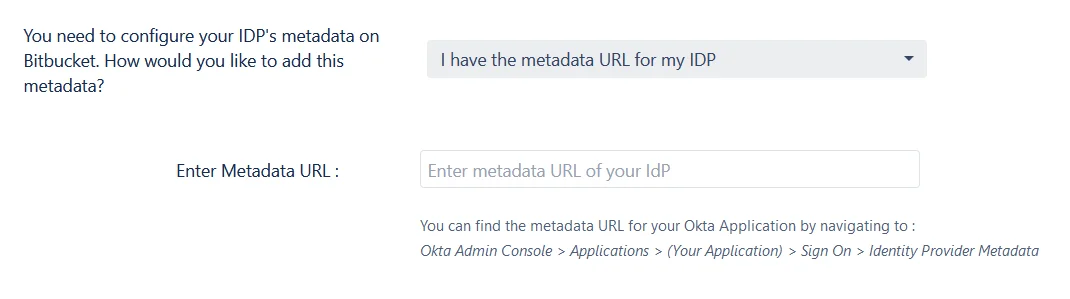
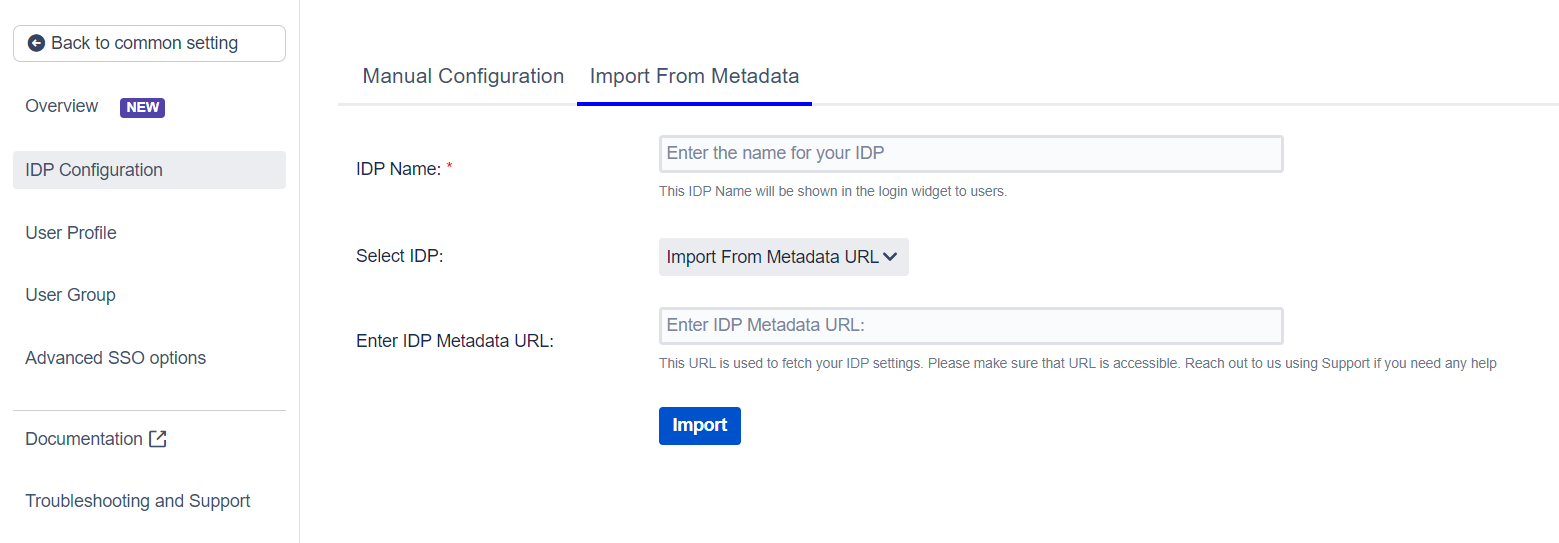
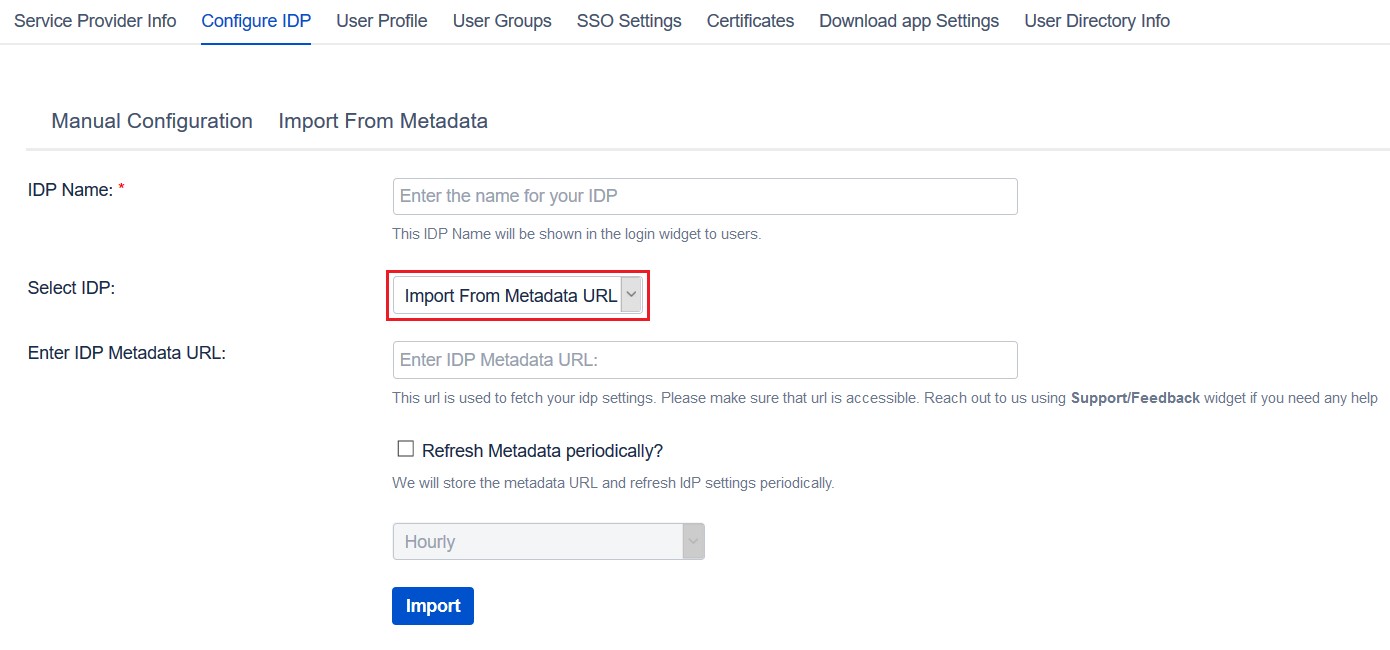
 Using Metadata URL
Using Metadata URL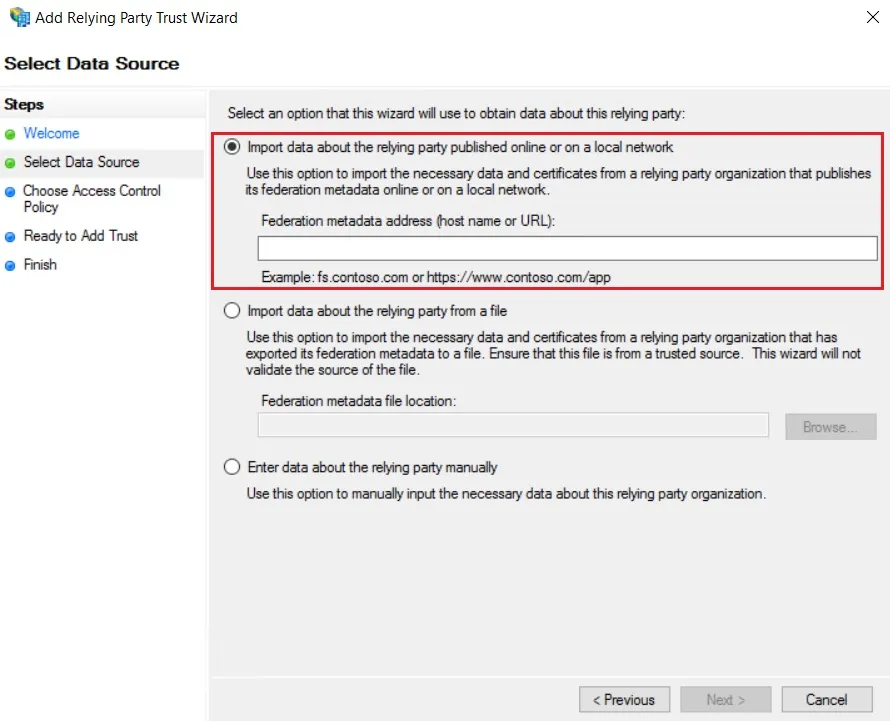
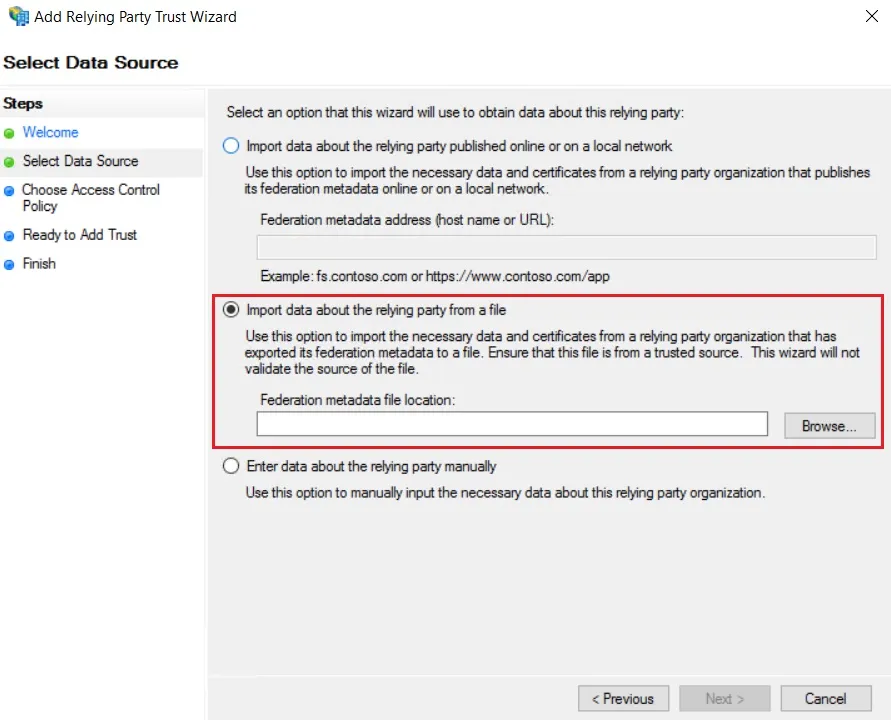
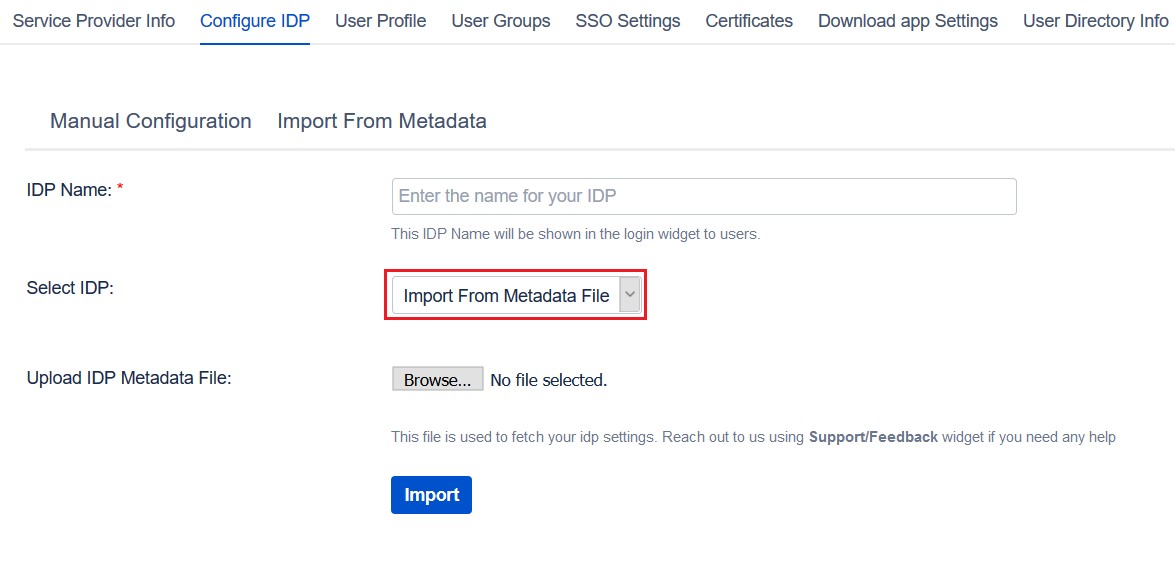
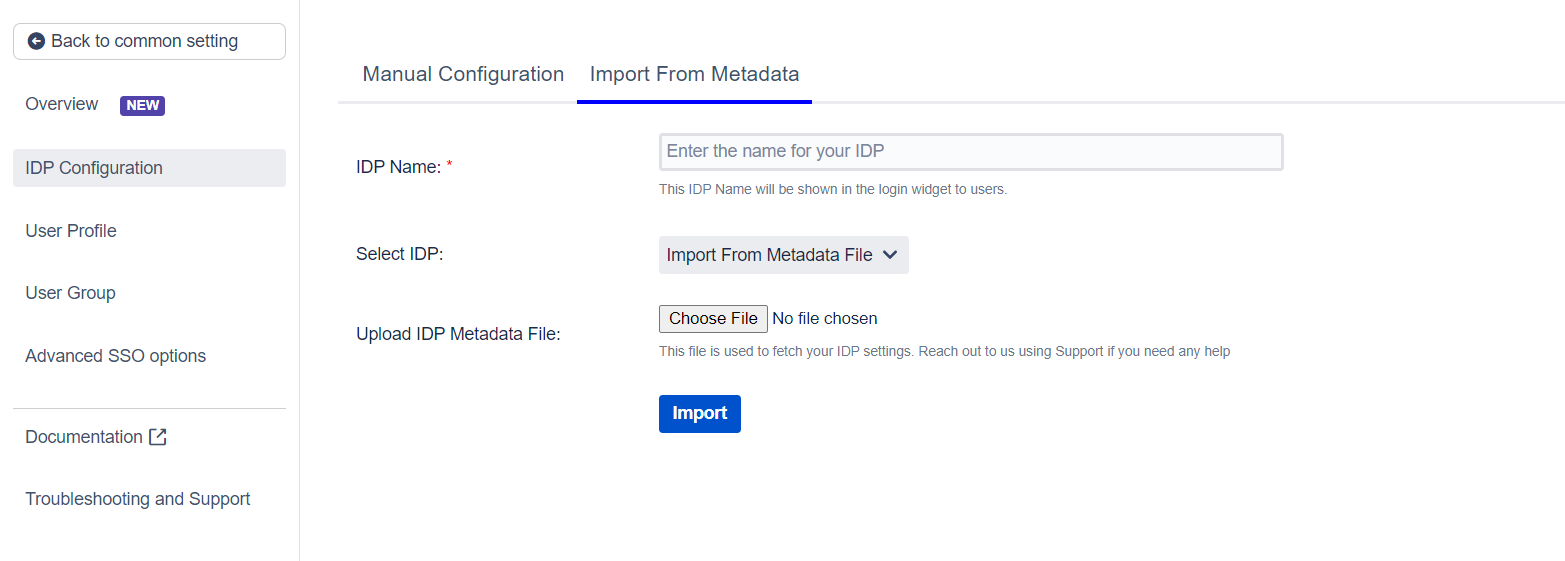
 Import the metadata
Import the metadata