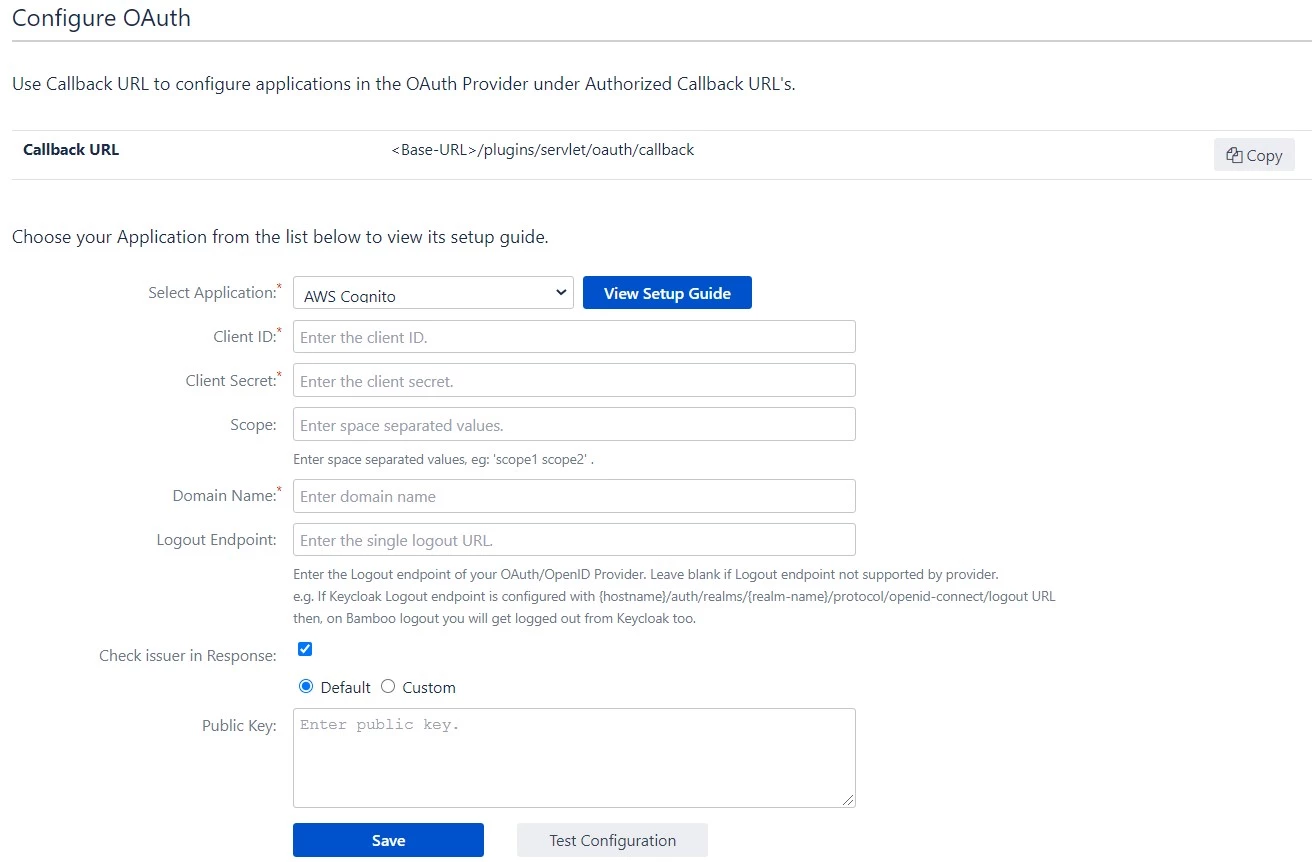
Bamboo OAuth app gives the ability to enable OAuth Single Sign On for Bamboo Software. Bamboo OAuth app is
compatible with all OAuth OAuth/OIDC providers. Here we will go through a guide to configure SSO between Bamboo
and your OAuth/OIDC providers. By the end of this guide, users from your OAuth/OIDC providers users should be
able to login and register to Bamboo Software.
Pre-requisites
To integrate your OAuth/OIDC providers with Bamboo, you need the following items:
- Bamboo should be installed and configured.
- Bamboo Server is https enabled (optional).
- Admin credentials are set up in Bamboo .
- Valid Bamboo Server or data center Licence.
Download And Installation
- Log into your Bamboo instance as an admin.
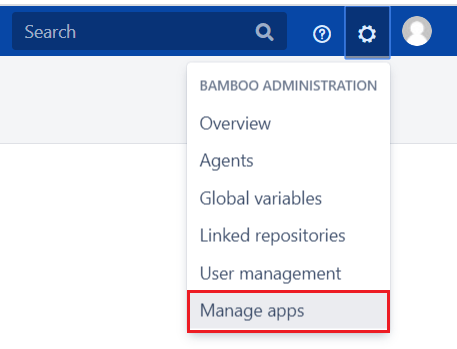
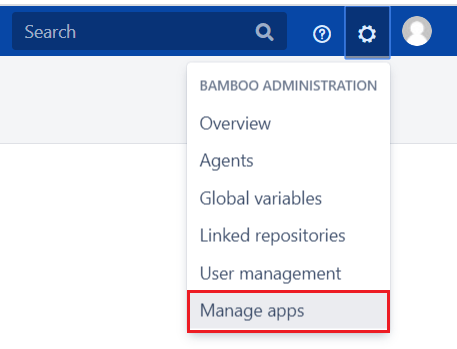
- Navigate to the settings menu and Click Manage Apps.
- Click Find new apps or Find new add-ons from the left-hand side of the page.
- Locate mO OAuth/OpenID Connect (OIDC) for Bamboo SSO via search.
- Click Try free to begin a new trial or Buy now to purchase a license for mO
OAuth/OpenID Connect (OIDC) for Bamboo SSO.
- Enter your information and click Generate license when redirected to MyAtlassian.
- Click Apply licence.