Contents
Keycloak Single Sign-On (SSO) in WordPress with OAuth Authentication
Keycloak Single Sign-On (SSO) for WordPress uses OAuth Authorization flow to provide users secure access to WordPress site. With our WordPress OAuth Single Sign-On (SSO) plugin, Keycloak acts as the OpenID Connect and OAuth provider, ensuring secure login for WordPress websites.
The integration of WordPress with Keycloak simplifies and secures the login process using Keycloak OAuth. This solution allows employees to access their WordPress sites with a single click using their Keycloak credentials, completely removing the need to store, remember, and reset multiple passwords.
In addition to offering Keycloak SSO functionality, the plugin extends its support to various IDPs, including Azure AD, Office 365, and specialized providers, offering robust Single Sign-On (SSO) capabilities like multi-tenant login, role mapping, and user profile attribute mapping. For further insights into the array of features we offer within the WP OAuth & OpenID Connect Client plugin, kindly refer here. You can follow the below steps to setup Keycloak Single Sign-On (SSO) with WordPress
In addition to offering Keycloak SSO functionality, the plugin extends its support to various IDPs, including Azure AD, Office 365, and specialized providers, offering robust SSO capabilities like multi-tenant login, role mapping, and user profile attribute mapping. For further insights into the array of features we offer within the WP OAuth & OpenID Connect Client plugin, kindly refer here. You can follow the below steps to setup Keycloak Single Sign-On (SSO) with WordPress.
Prerequisites: Download and Installation
- Log into your WordPress instance as an admin.
- Go to the WordPress Dashboard -> Plugins and click on Add New.
- Search for a WordPress OAuth Single Sign-On (SSO) plugin and click on Install Now.
- Once installed click on Activate.
Steps to configure Keycloak Single Sign-On (SSO) in WordPress OAuth
1. Setup Keycloak as OAuth Provider
- First of all, Download Keycloak and install it.
- Start the keycloak server based on your keycloak version. (See table below)
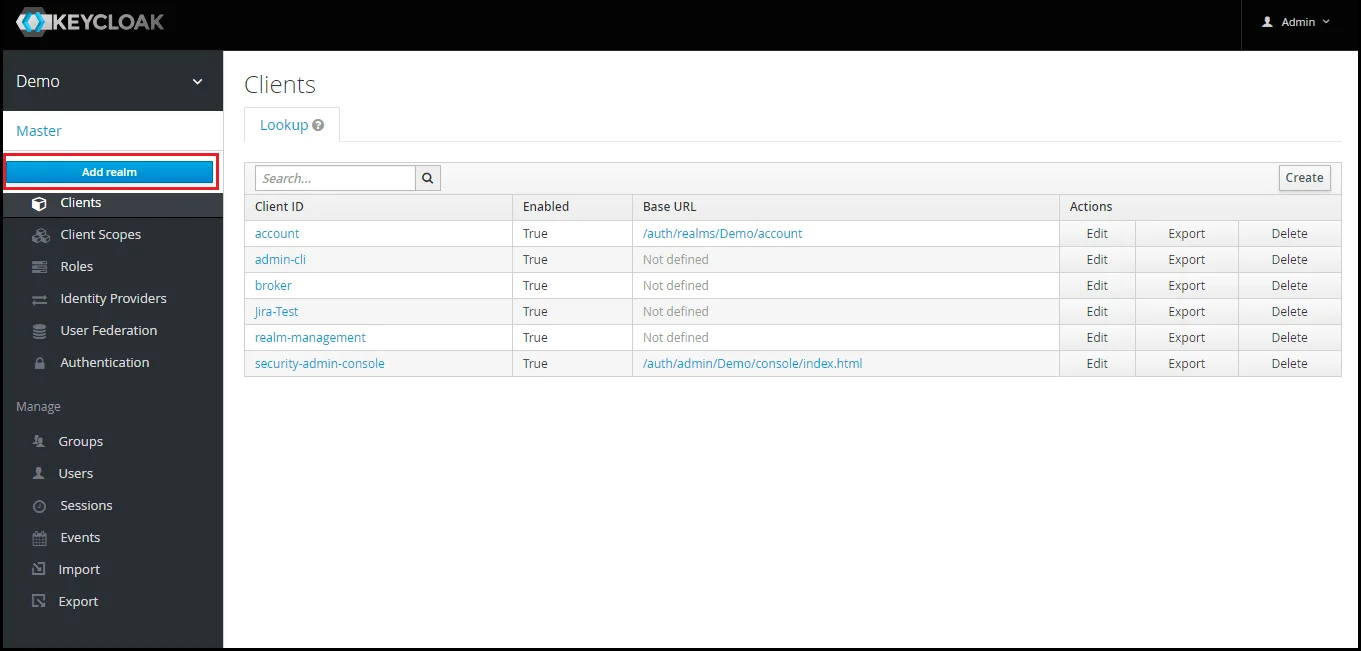
- Add Realm : Now login to keycloak administration console and navigate to your desired realm. You can add new realm by selecting Add Realm option.
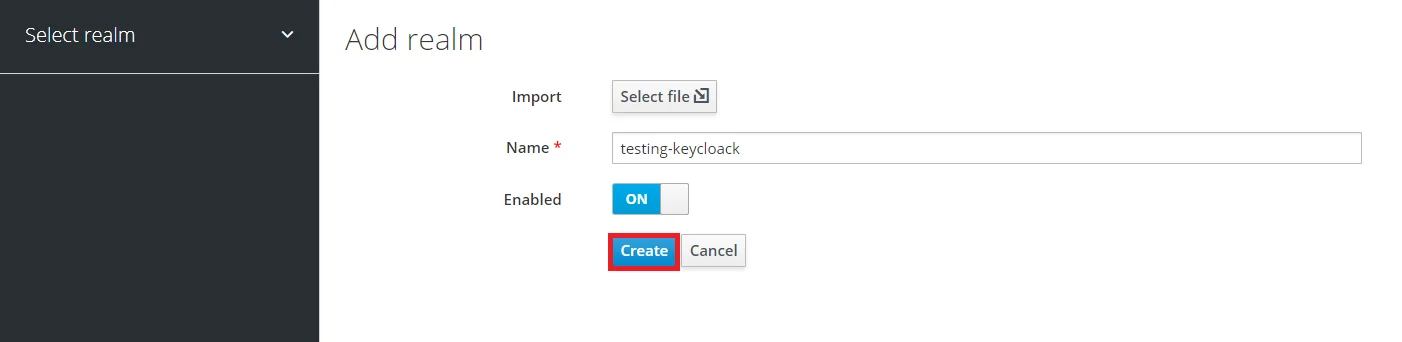
- Create realm: Enter Realm Name and keep the realm name handy as it will required later to configure the Realm under the OAuth Client plugin. Click on CREATE to add realm.
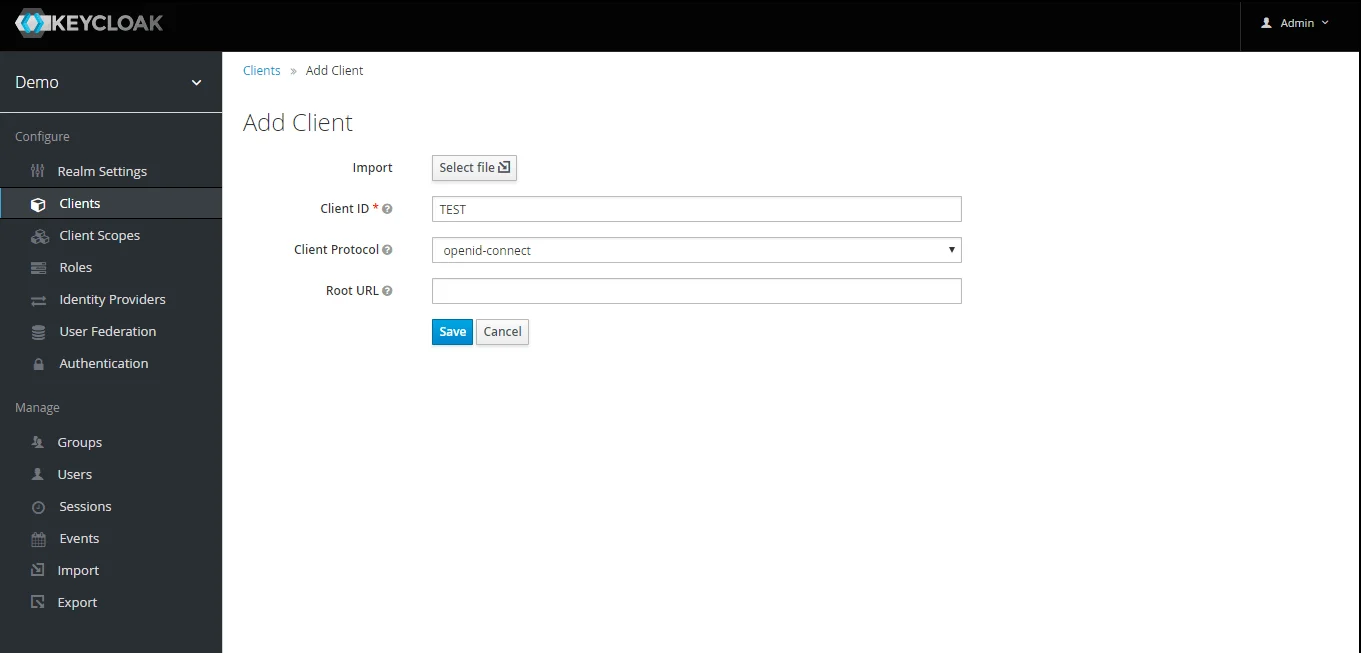
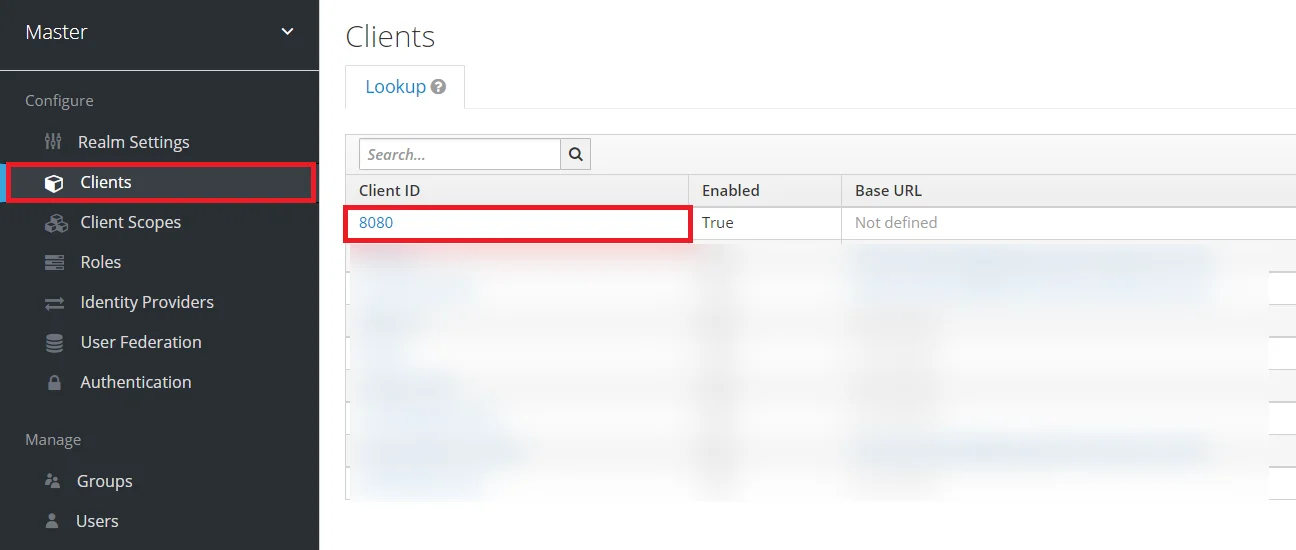
- Create OpenID client: Click on the Clients and choose create to create a new client. Enter client id and select client protocol openeid-connect and select Save.
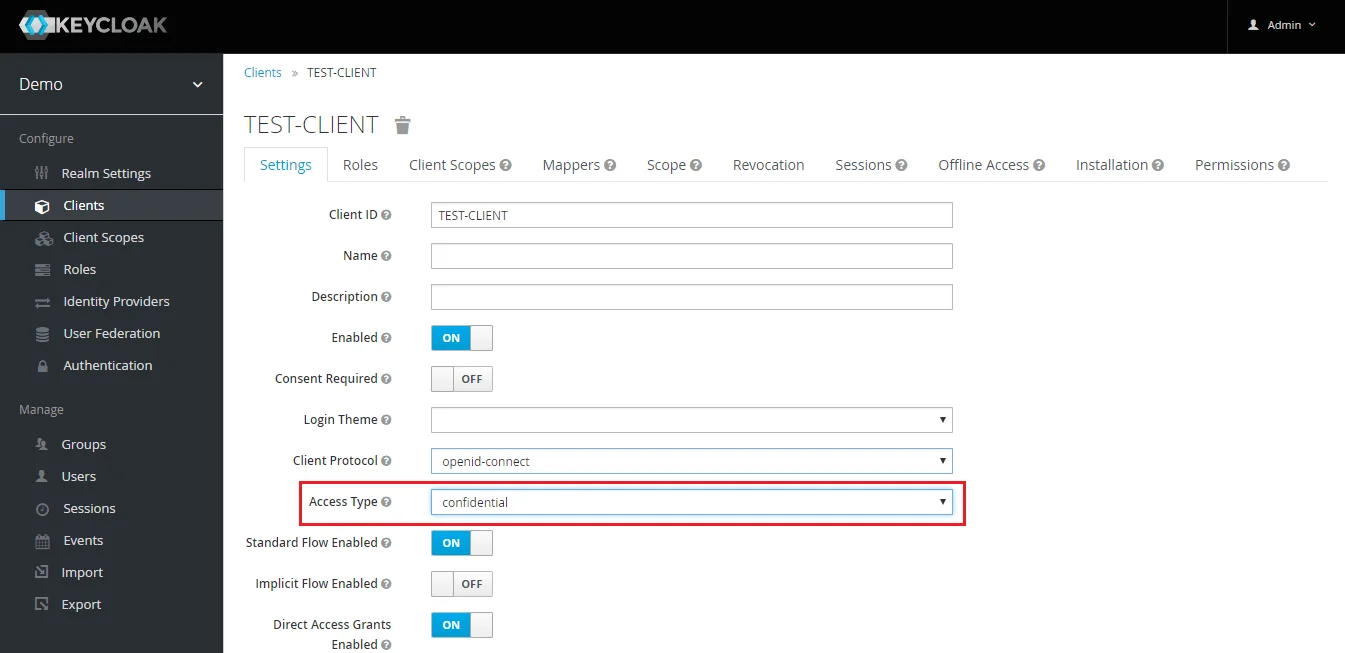
- Change Access type: After client is created change its access type to confidential.
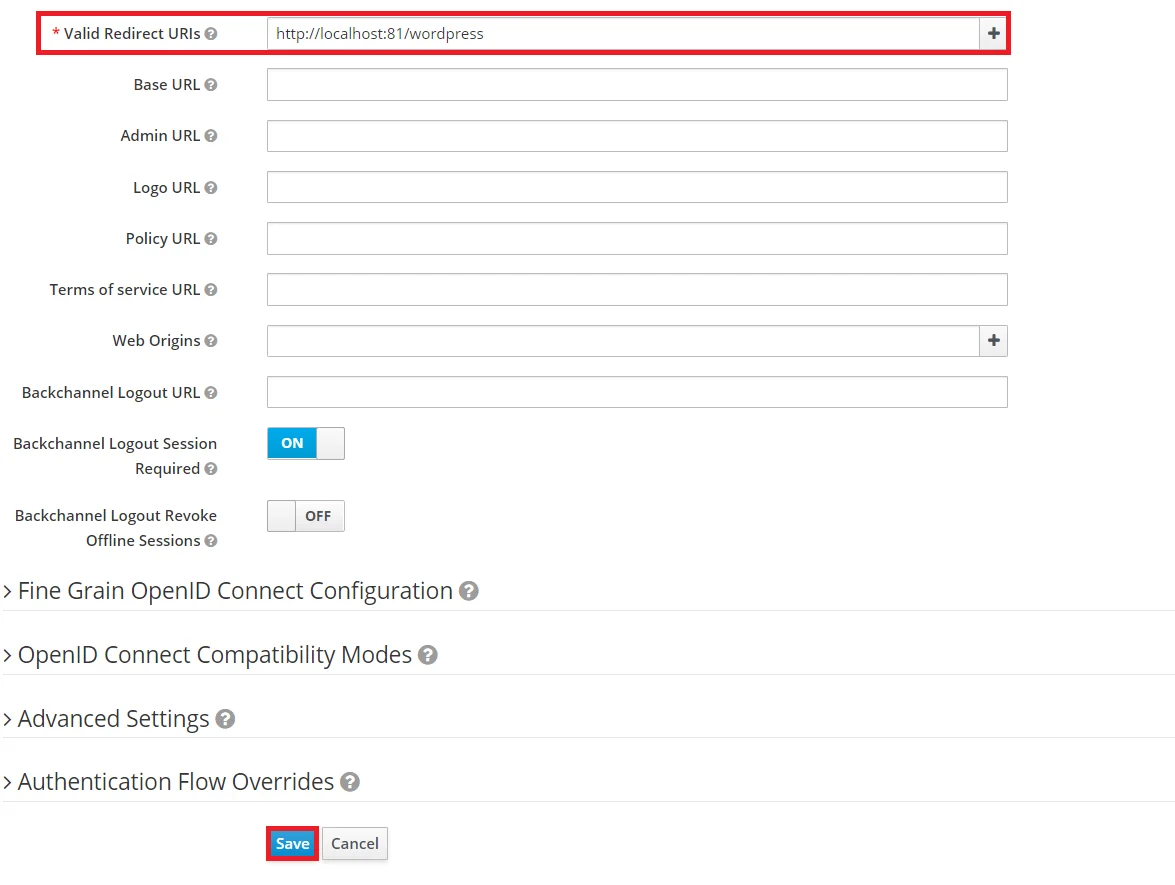
- Enter Valid Redirect URIs: Copy Callback
URL from plugin and then click on SAVE. Ex --
https://
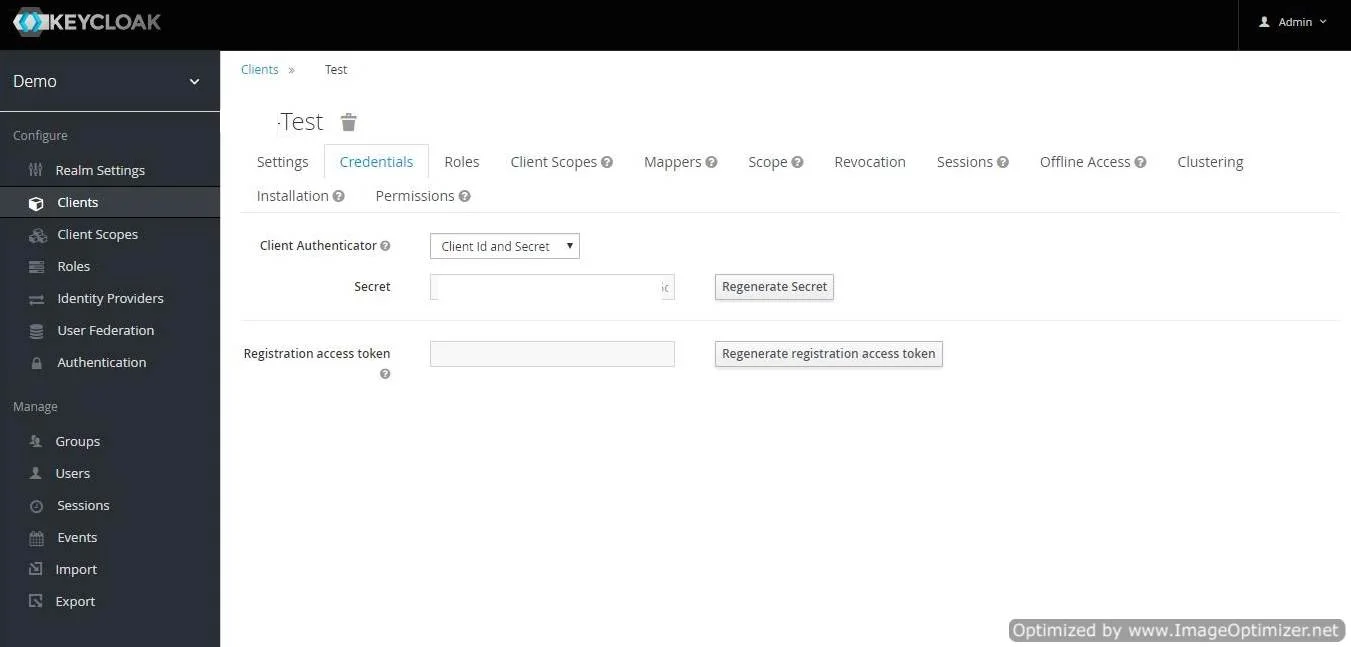
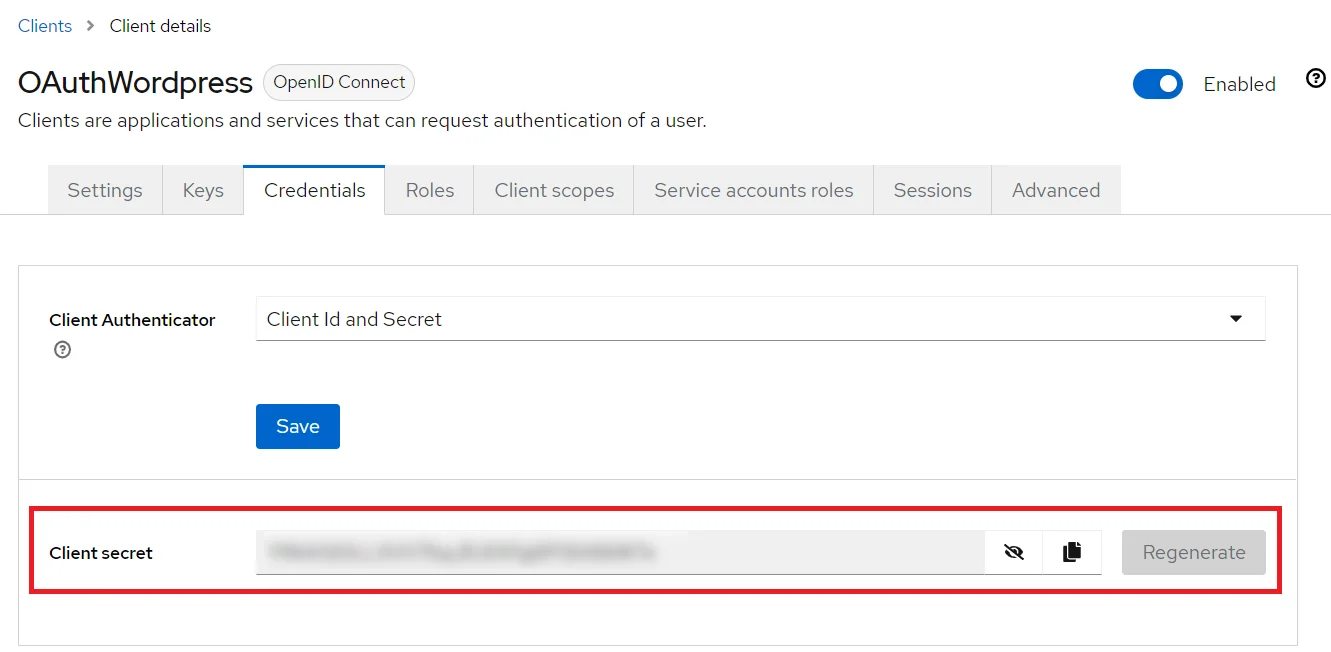
/oauth/callback - Get Client Secret: Now we need to get client secret. So select Clients and select credentials and copy your secret from here.
- Plugin Configuration: Enter copied Client Secret under Client secret field in the OAuth Client plugin, and enter the Client Name under the Client ID field.
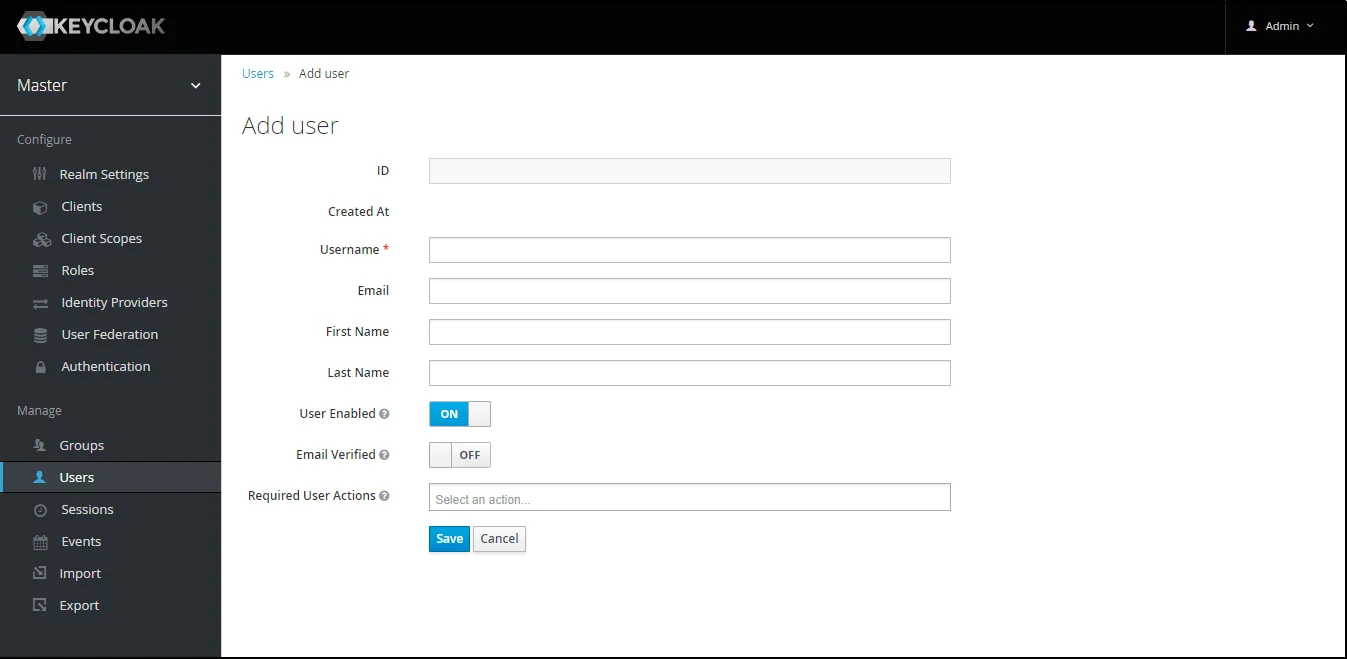
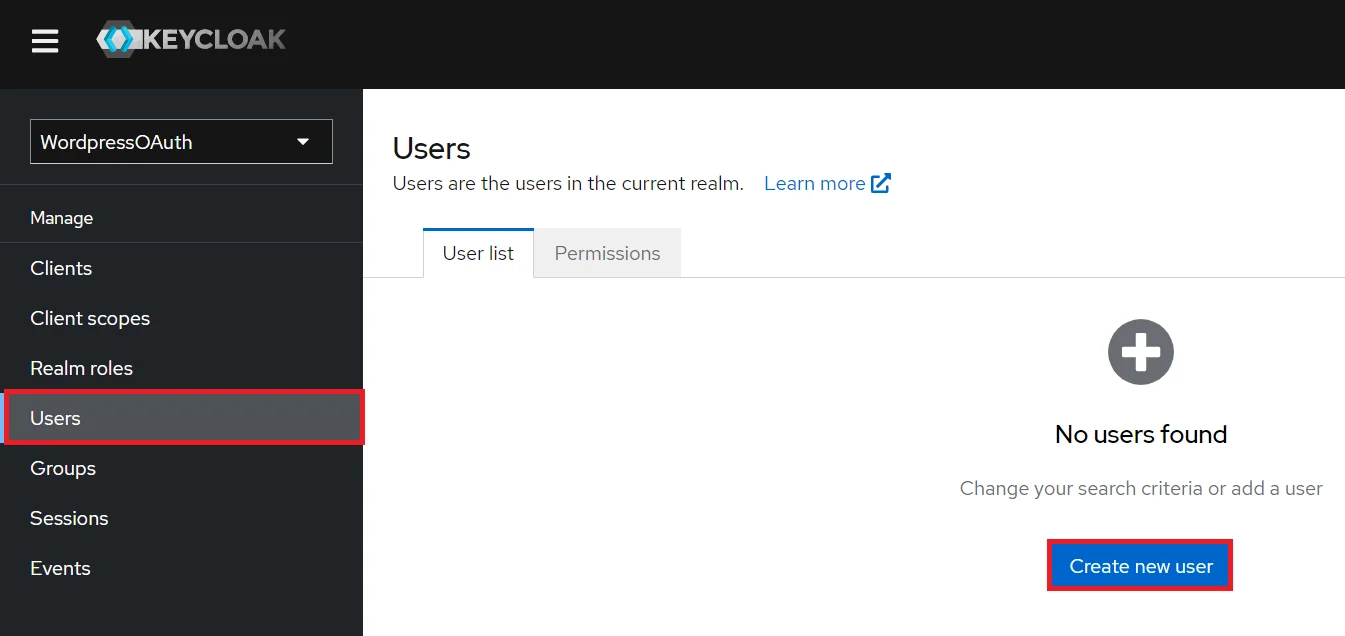
- Add User: We need to add users to realm who will be able to access the resources of realm. Click on the Users and choose to Add a new User.
- User Configuration: After user is created following action needs to be performed on it.
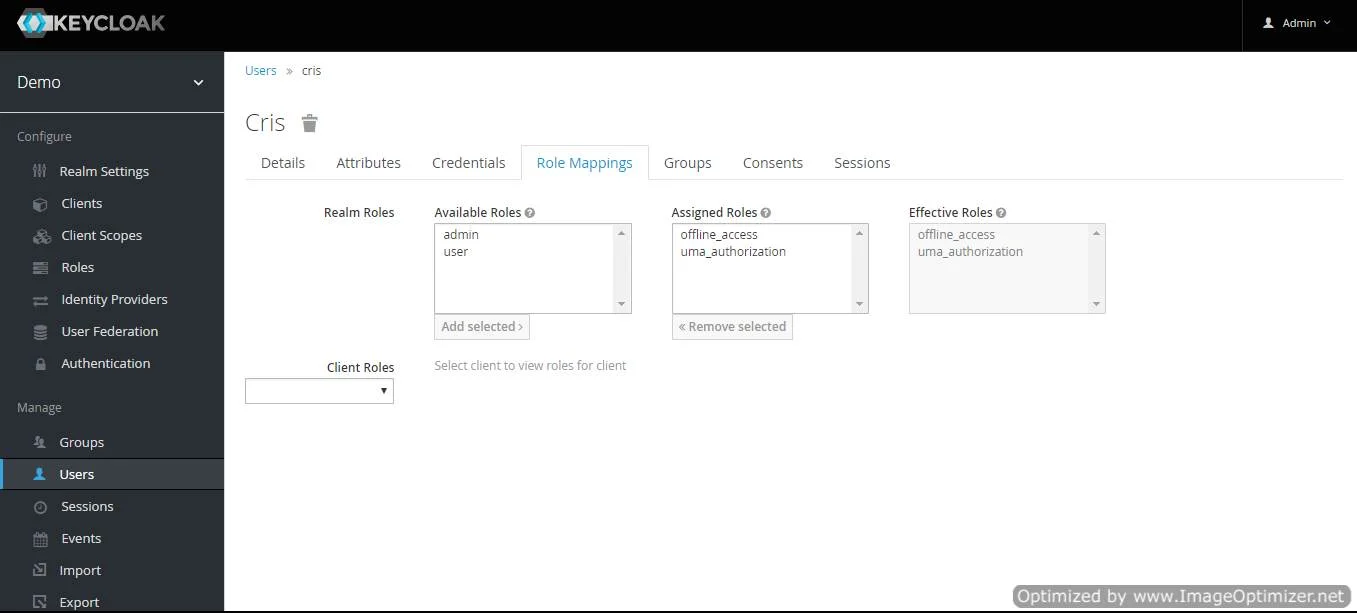
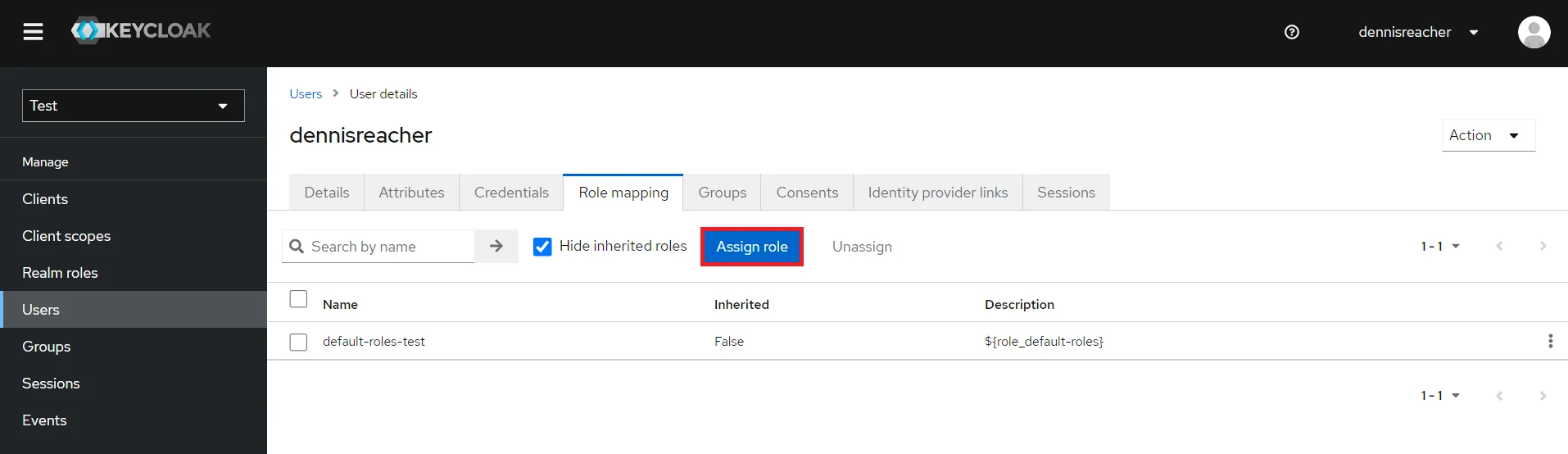
- Map User: We need to map user to a role. Click on Role Mappings and assign the user desired role from available roles and clicking on add selected.
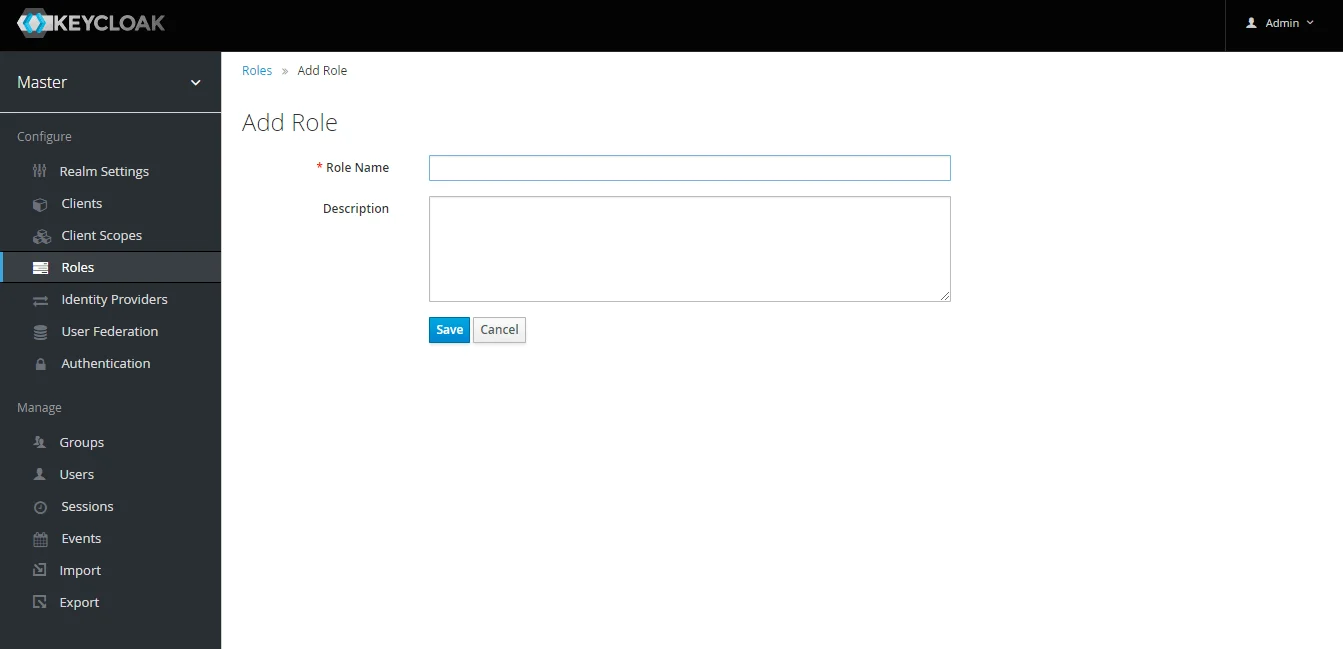
- Create ROLE: The Role will be used by your applications to define which users will be authorized to access the application. Click on the Roles and choose Add Role.
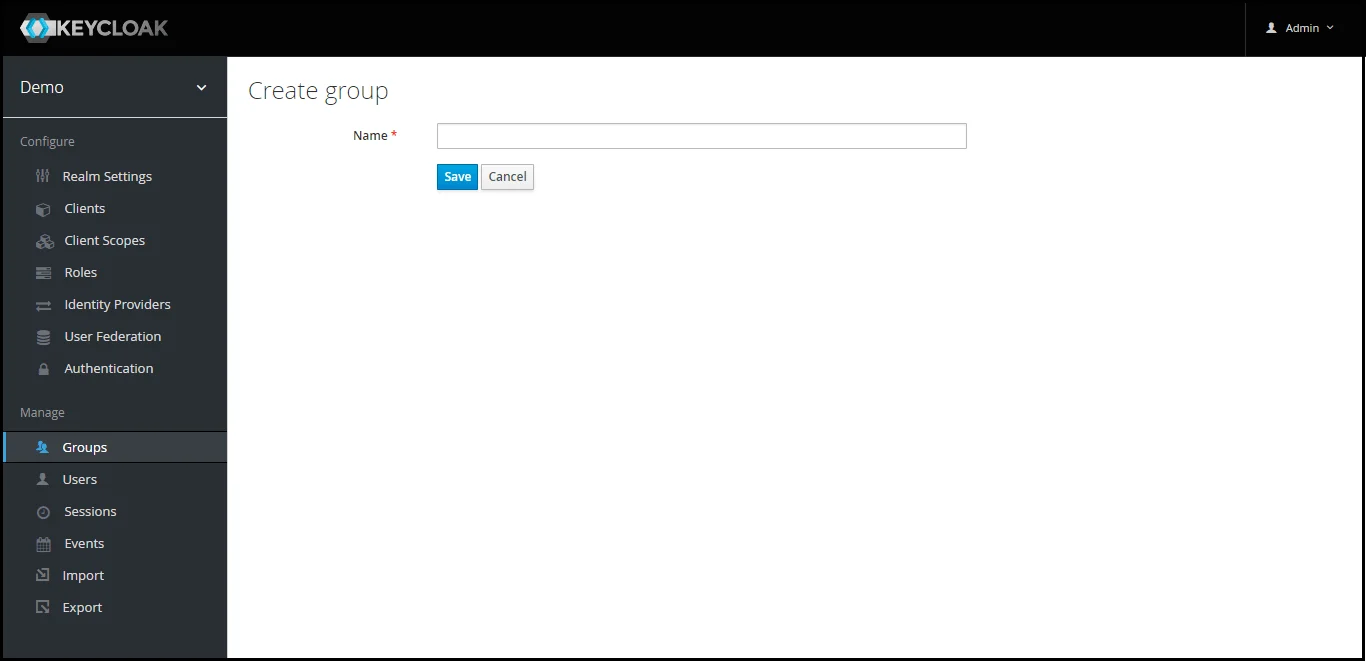
- Create groups: Click on the Groups and choose New to create a new group.
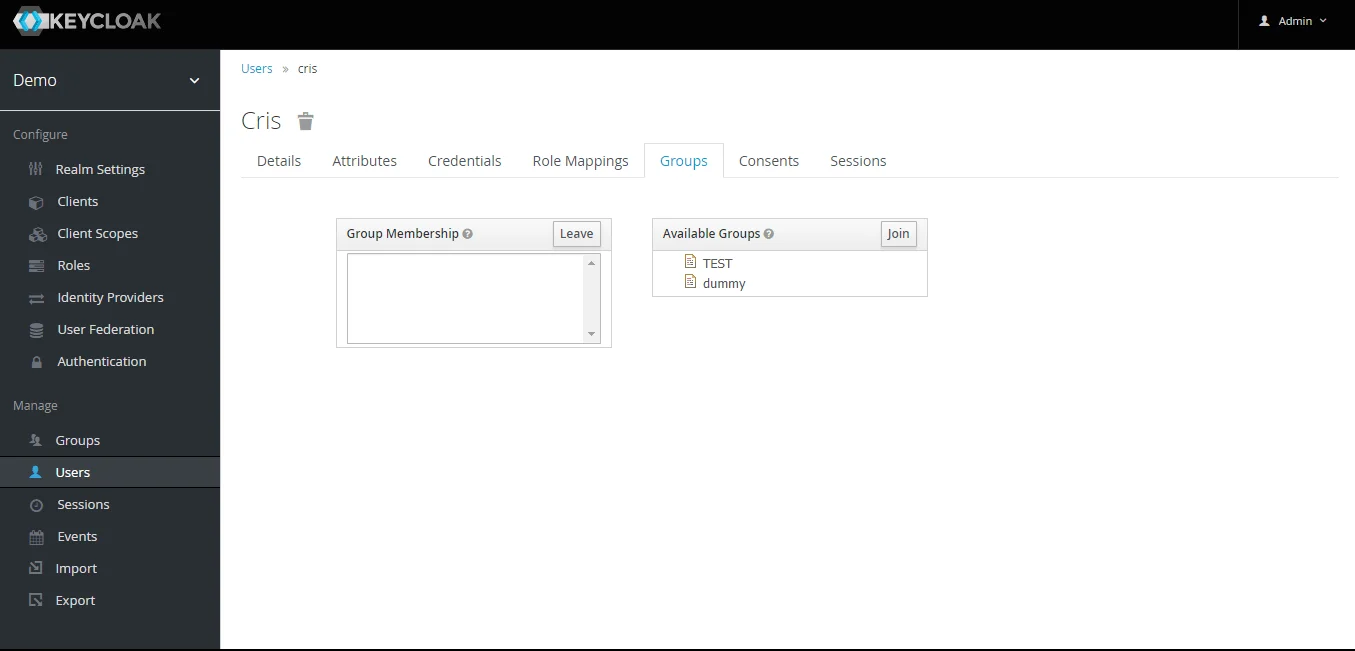
- Assign user to group: Select the user whom you want to add in group. Choose Groups option from tab and then select the group-name and click on join.
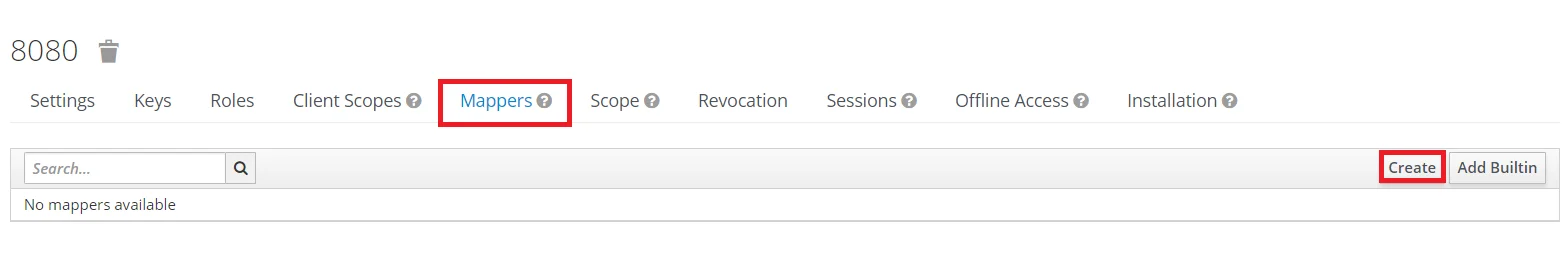
- Keycloak Group Mapper: Now to get group details we need to perform its client mapping with group membership else group details will not be fetched. So in Client section, select your client and then click on mapper->create.
- Now, select mapper type as Group Membership and enter the name and token claim name i.e the attribute name corresponding to which groups will be fetched. Turn Off the full group path, Add to ID token and Add to access token options, and click on Save.
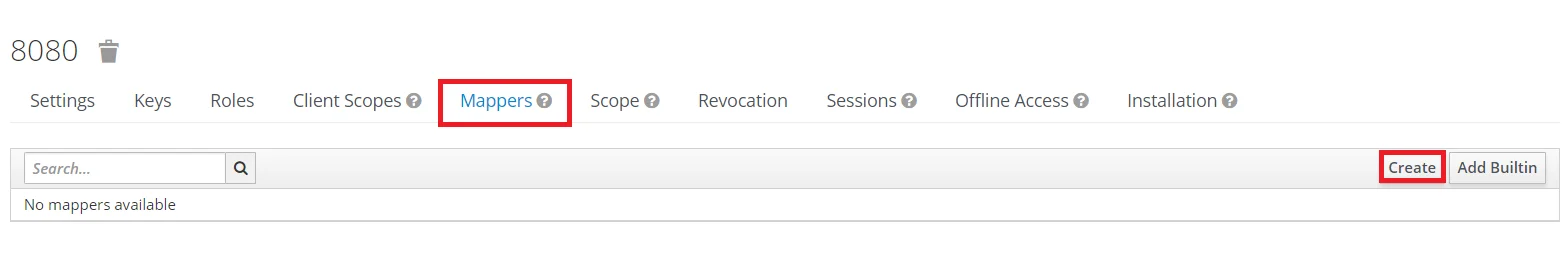
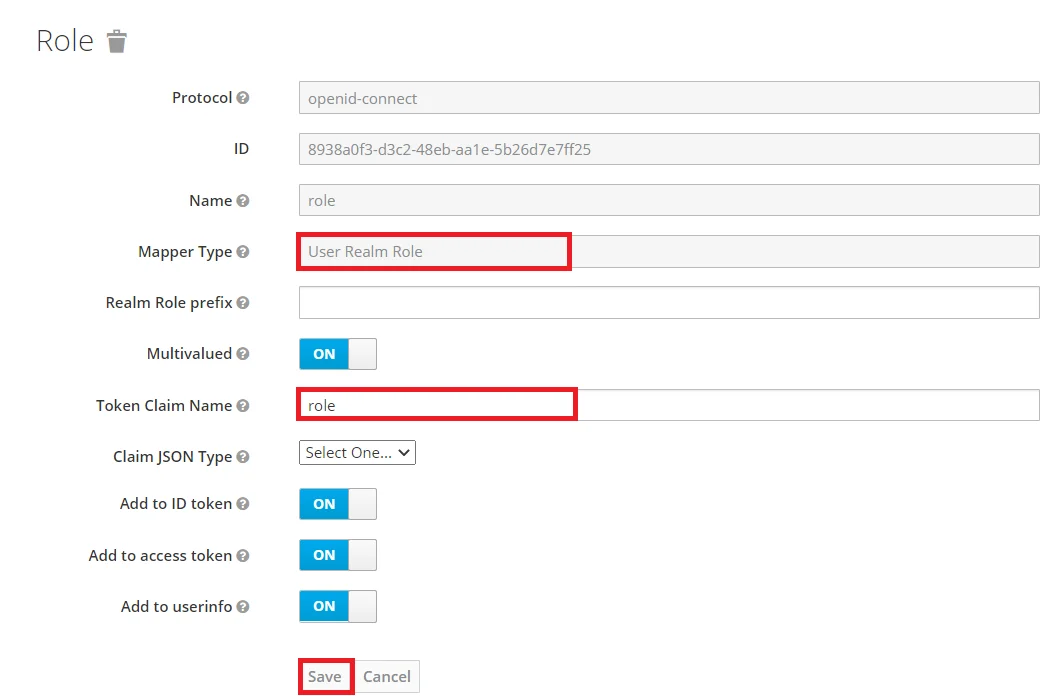
- Keycloak Role Mapper: Now to get role details for a successful Keycloak Single Sign-On (SSO) we need to perform its client mapping with role membership else role details will not be fetched. So in Client section, select your client and then click on mapper->create.
- Now, select mapper type as user realm Role Membership and enter the name. and token claim name i.e the attribute name corresponding to which groups will be fetched. Add to ID token and Add to access token options, and click on Save.
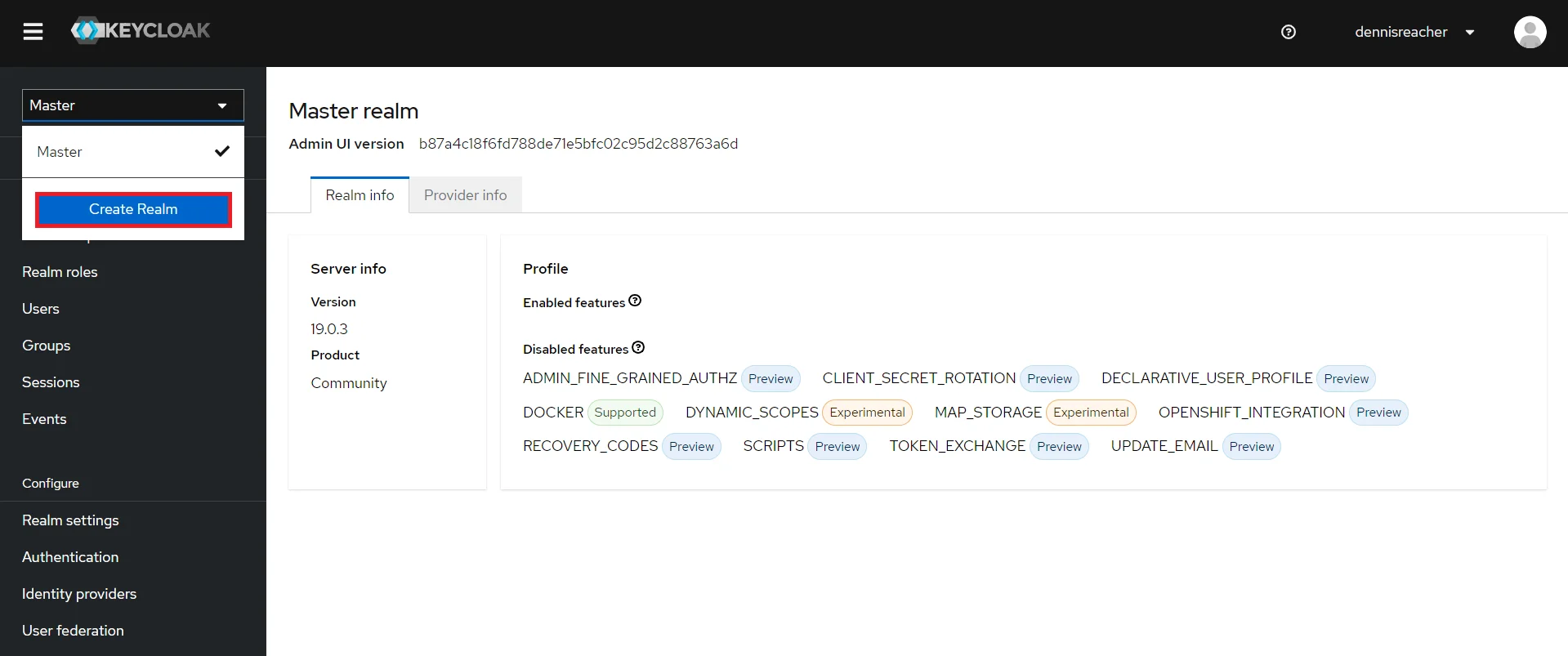
- Add Realm : Now login to keycloak administration console and navigate to your desired realm. You can add new realm by selecting Create Realm option.
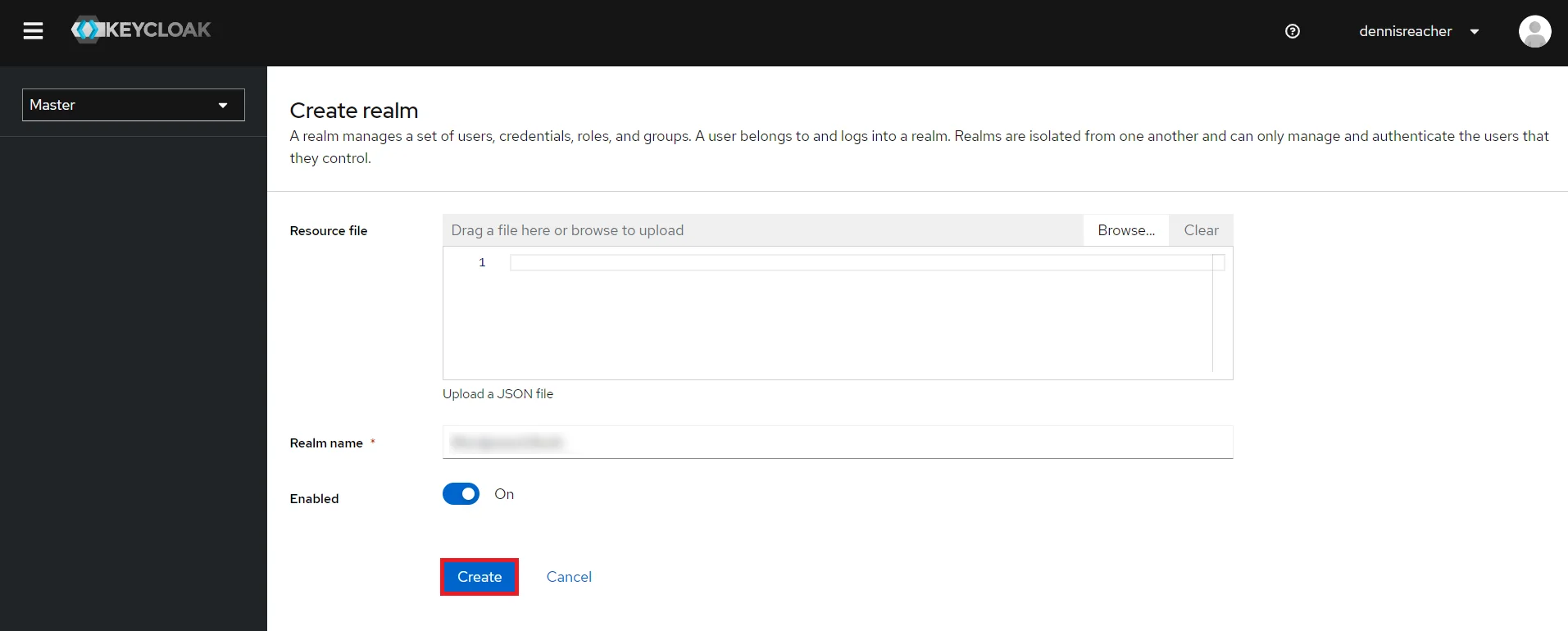
- Create realm: Enter Realm Name and keep the realm name handy as it will required later to configure the Realm under the OAuth Client plugin. Click on CREATE to add realm.
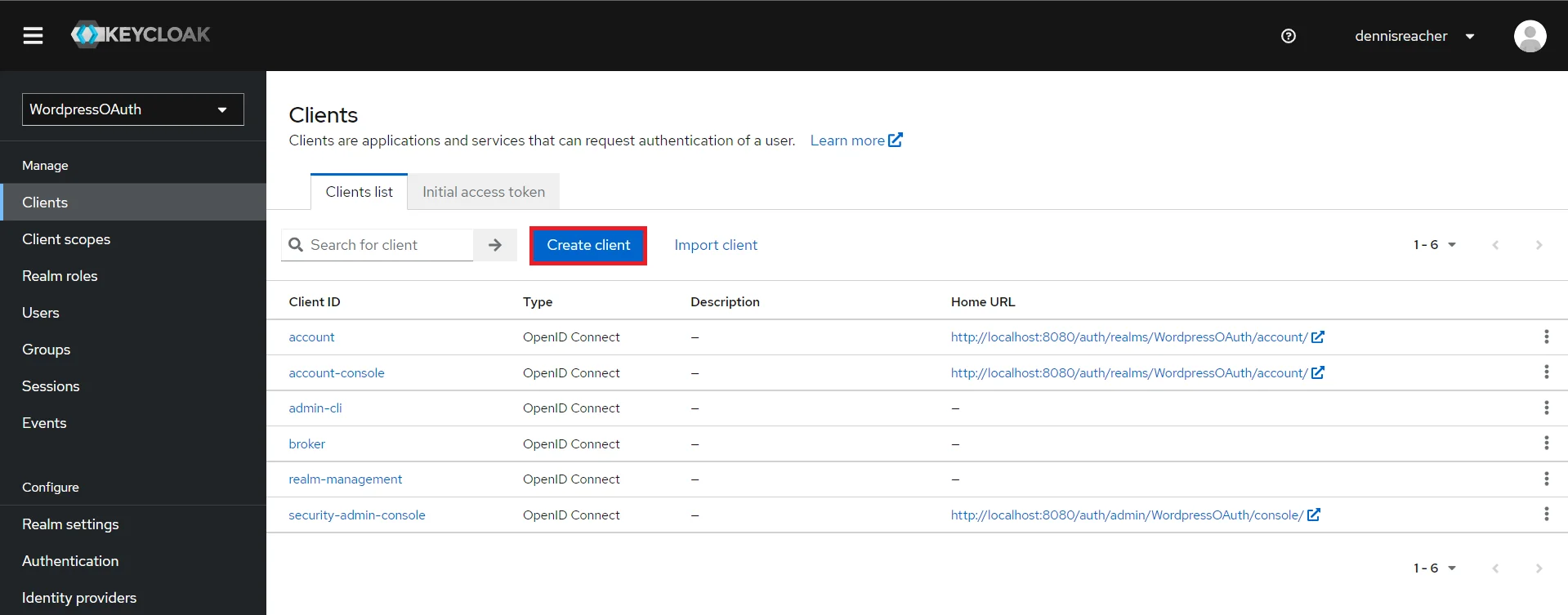
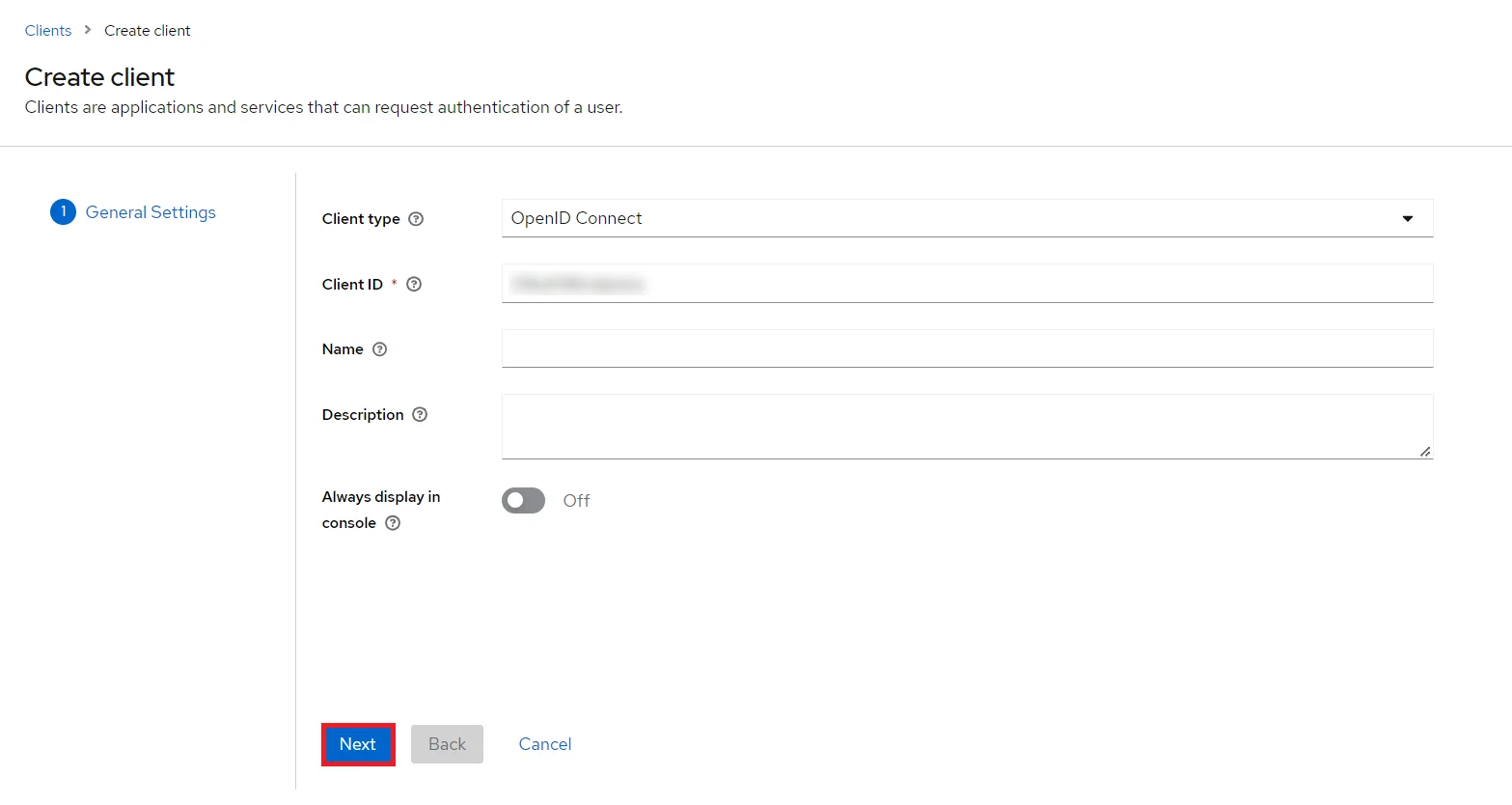
- Create OpenID client: Click on the Clients and choose Create Client to create a new client. Enter Client id and select client protocol openid-connect and Click Next.
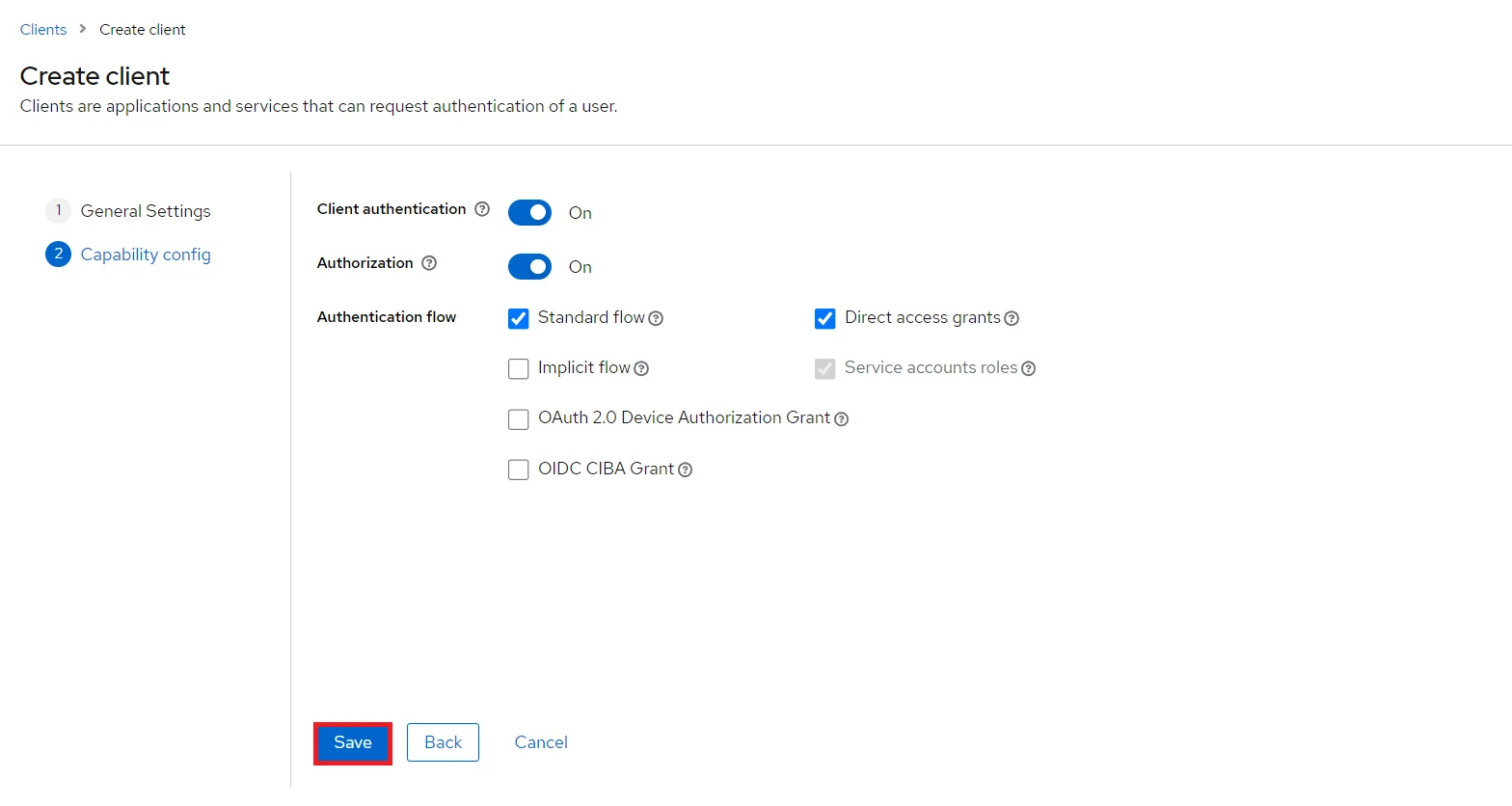
- Enable the Client Authentication and Authorization toggle.
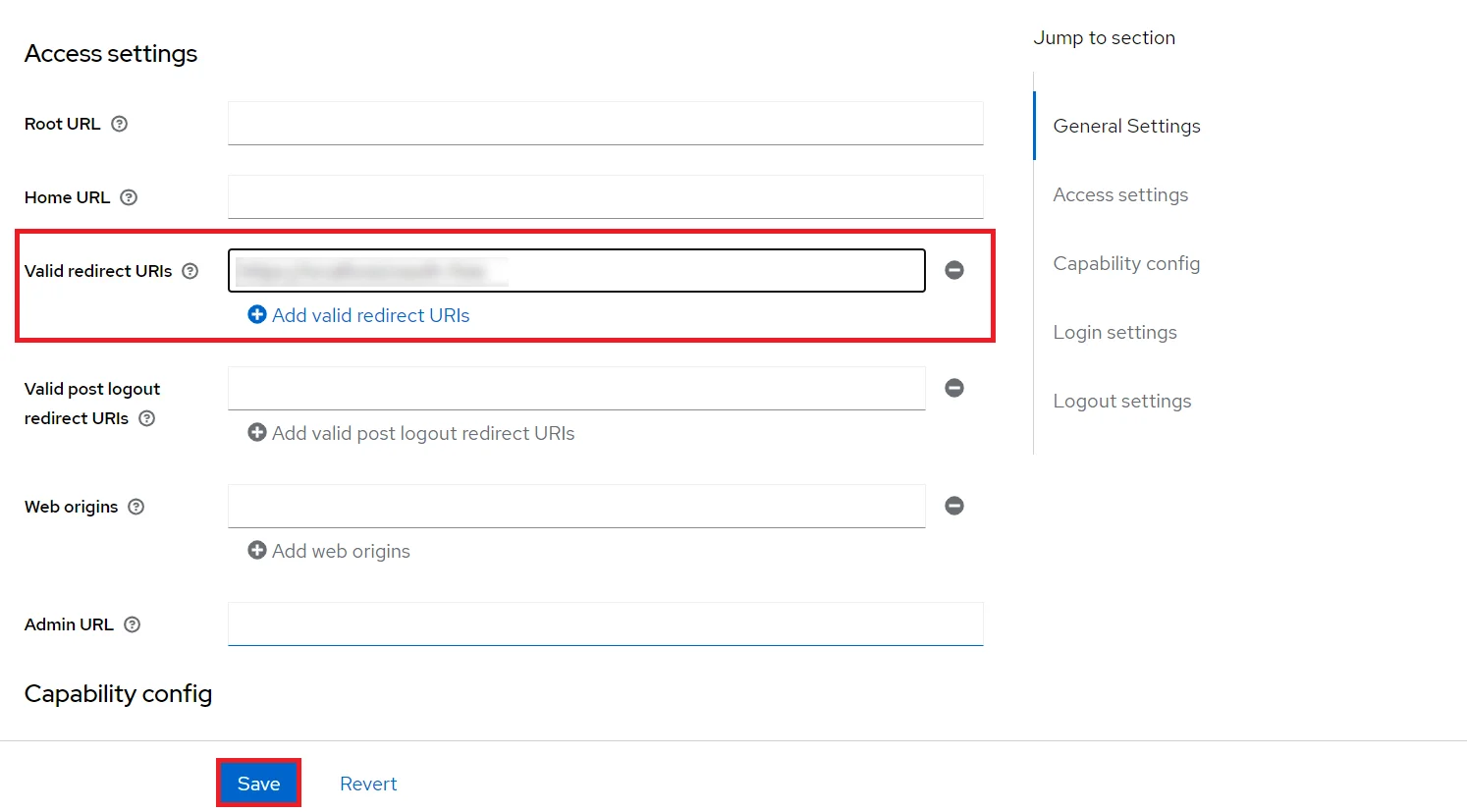
- Scroll down to the Access settings and enter your Callback/Redirect URL which you will get from your miniOrange plugin present on your Client side under the CallBack URLs text-field.
- Go to the Credentials tab, copy the Client Secret and keep it handy as we will require it later while configuring WordPress OAuth Single Sign-On plugin.
- Plugin Configuration: Enter copied Client Secret under Client secret field in the OAuth Client plugin, and enter the Client ID under the Client ID field.
- Add User: We need to add users to realm who will be able to access the resources of realm. Click on the Users and Click on Create new user to Add a new User.
- User Configuration: After user is created following action needs to be performed on it.
- Map User: We need to map user to a role. Click on Role Mappings and assign the user desired role from available roles.
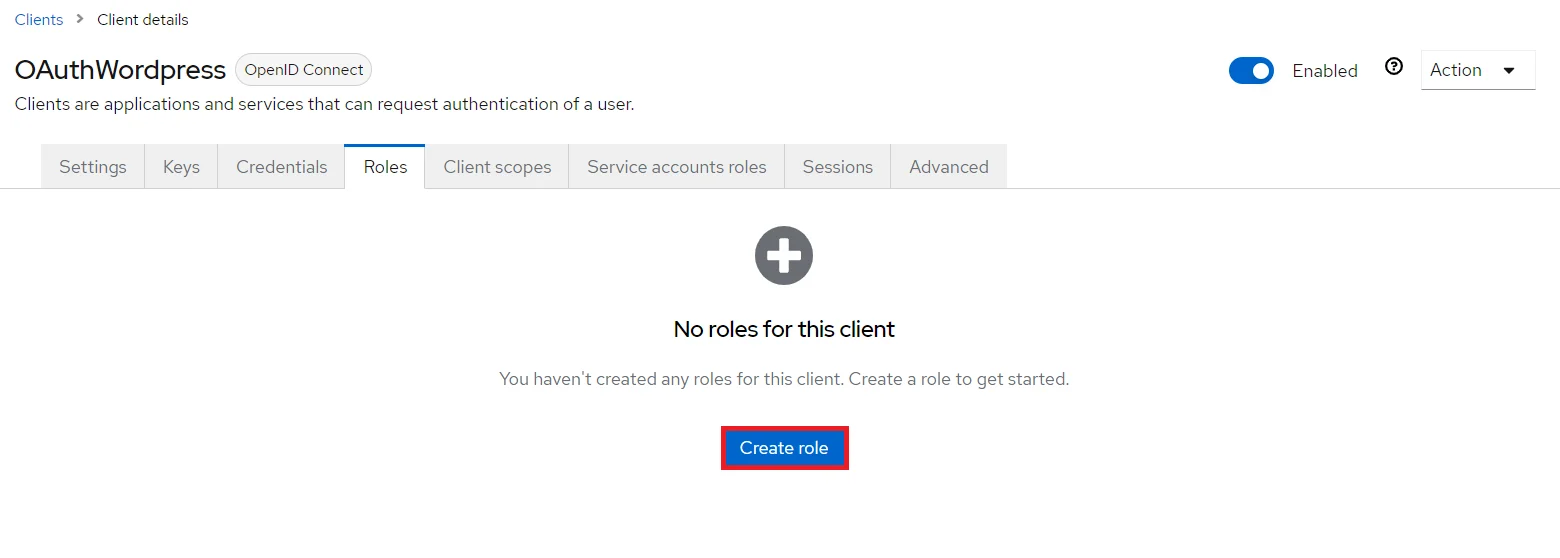
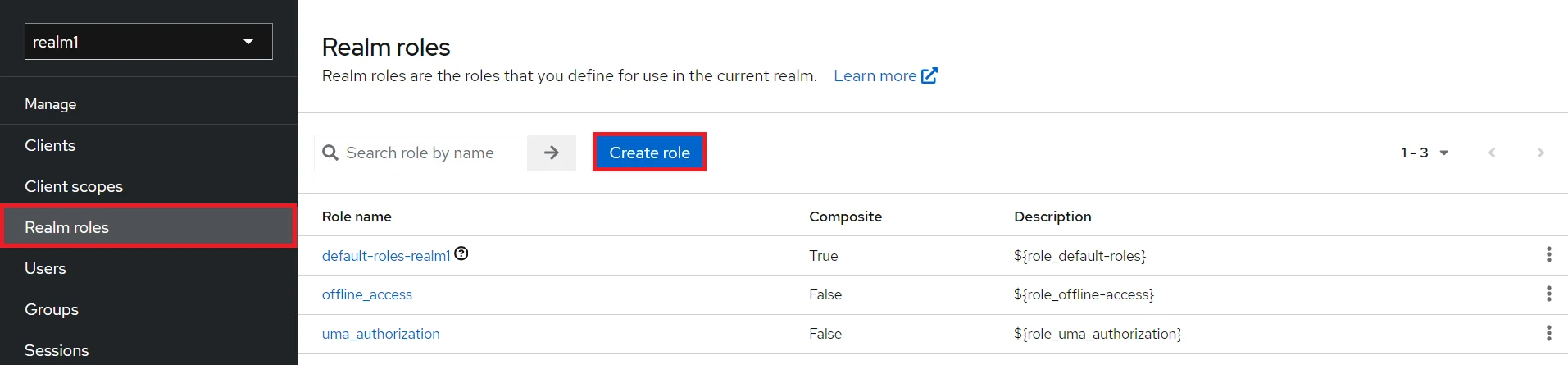
- Create ROLE: The Role will be used by your applications to define which users will be authorised to access the application. Click on the Roles and choose Create Role.
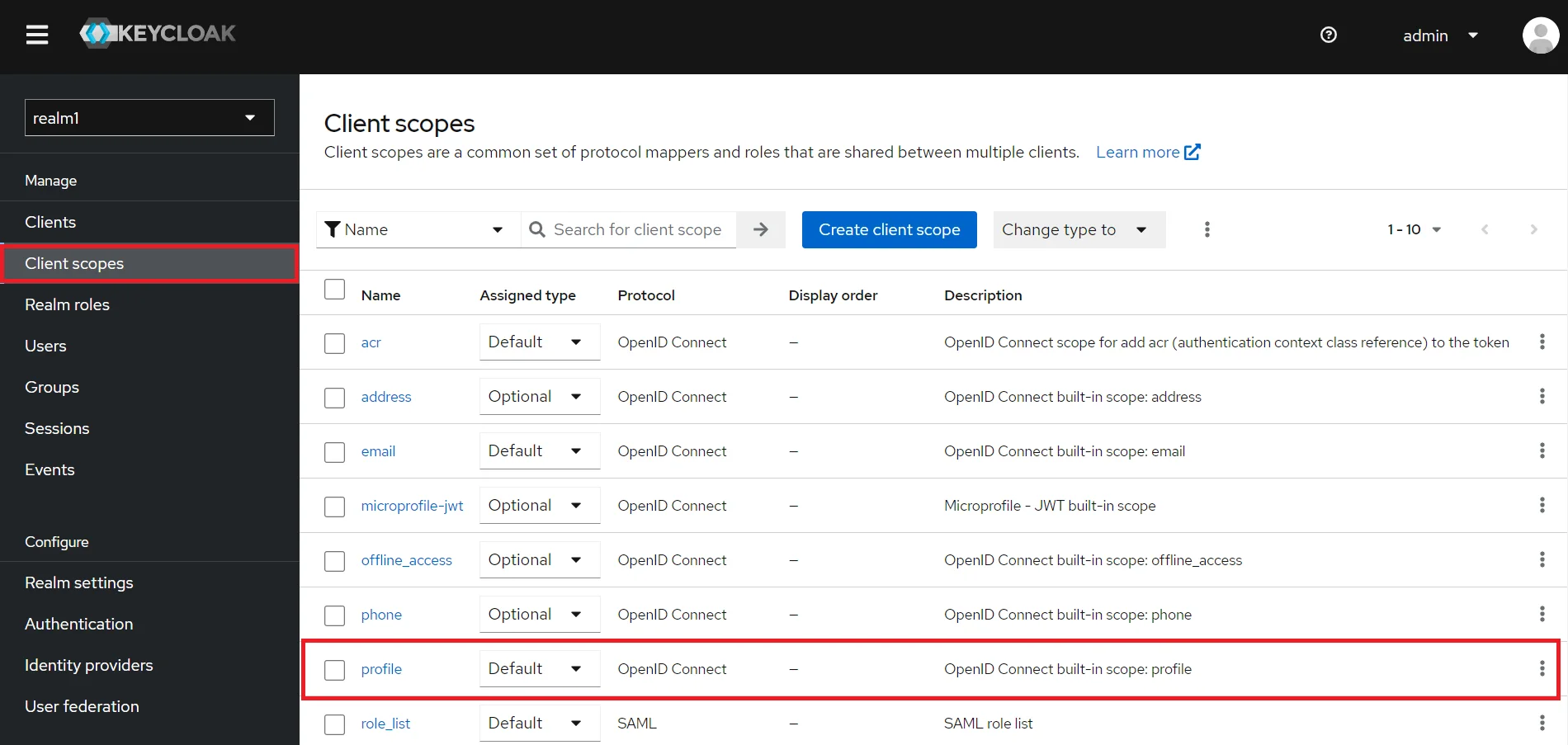
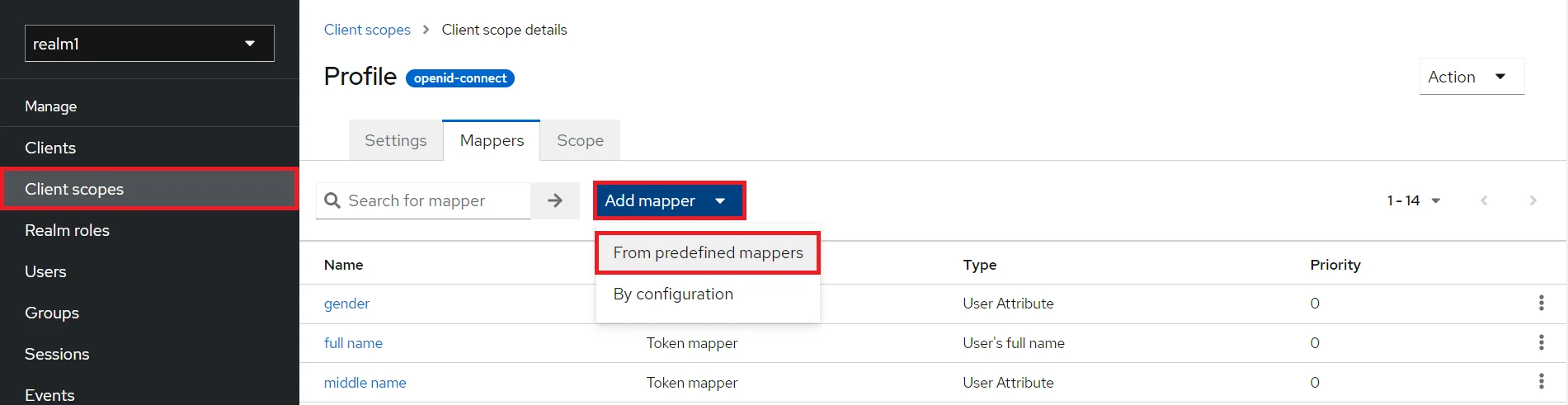
- Click on Client Scopes and select the Profile scope from the list.
- In the Mappers tab, choose From predefined mappers option from the Add mapper dropdown.
- Check the Group mapping from the list.
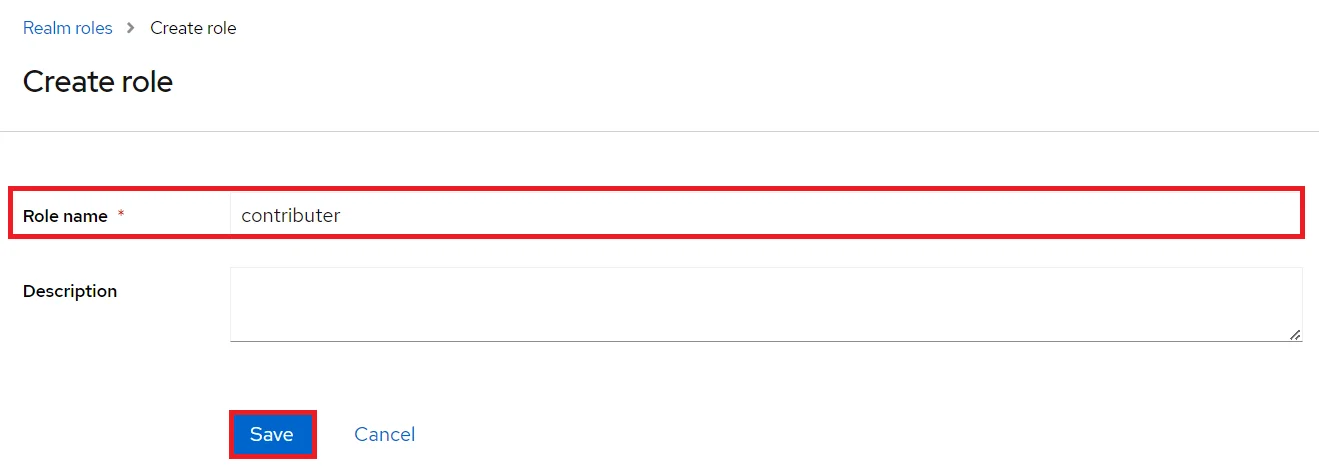
- Now, go to the Realm roles tab , click on Create role button.
- Enter the Role name and click on Save button.
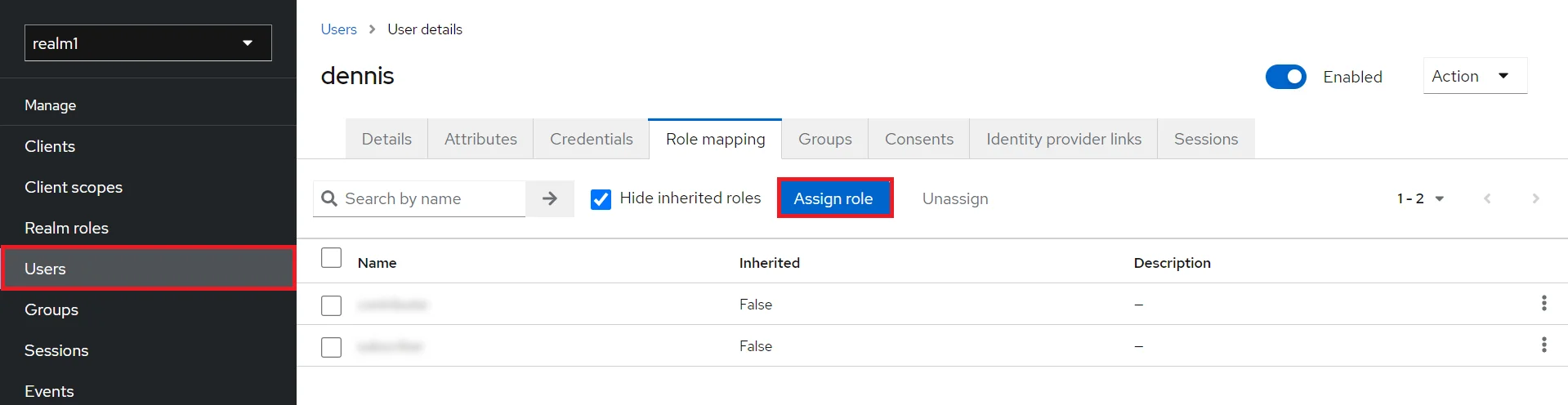
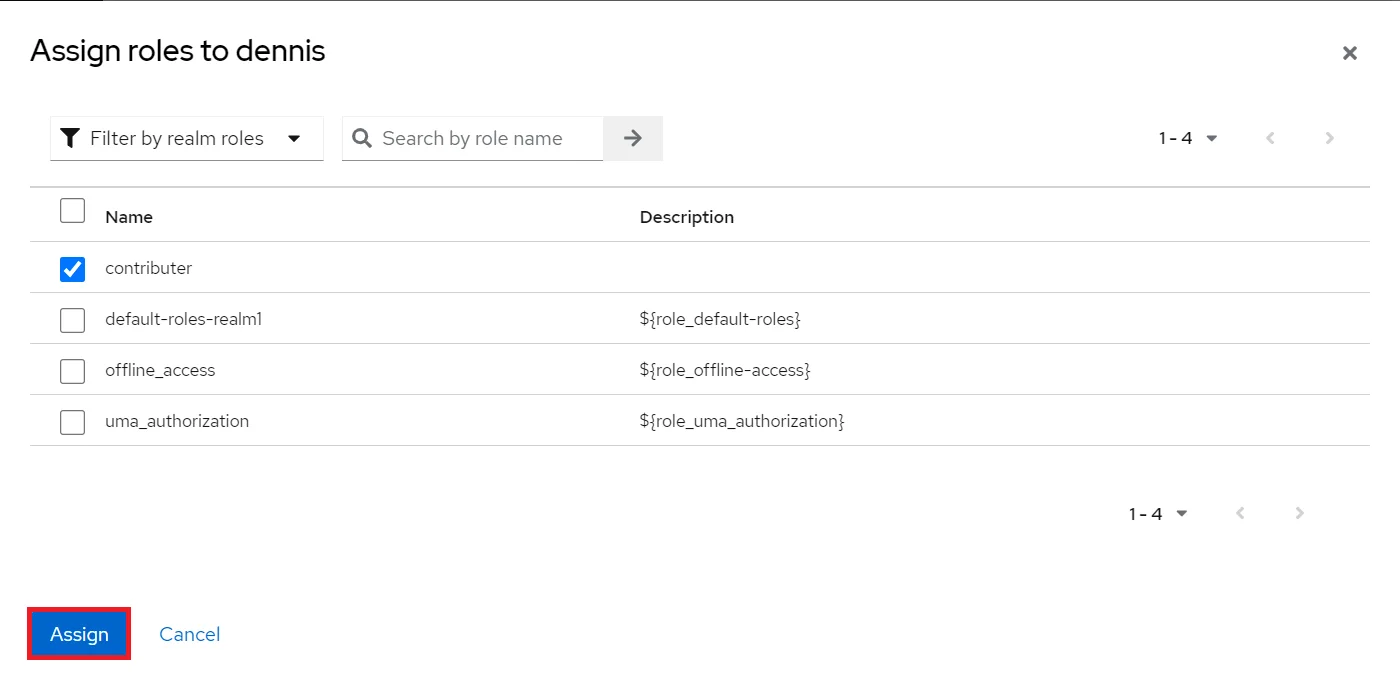
- Now, go to the Users tab from the left section and select the user you want to assign groups. Under the Role mapping tab click on Assign role button.
- Select the Groups you want to assign to a user and click on Assign button.
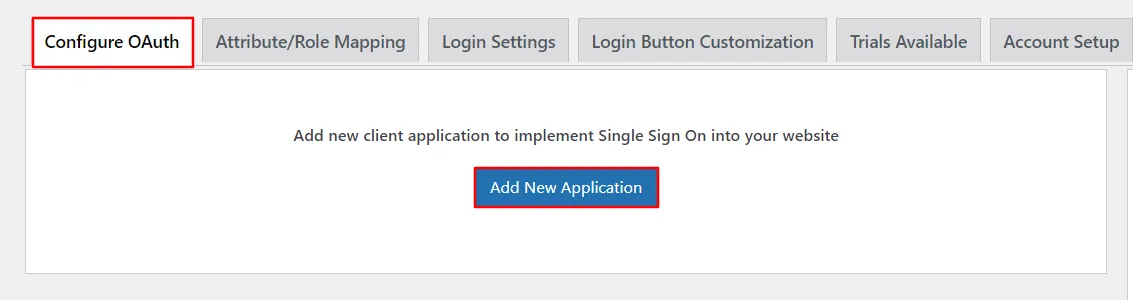
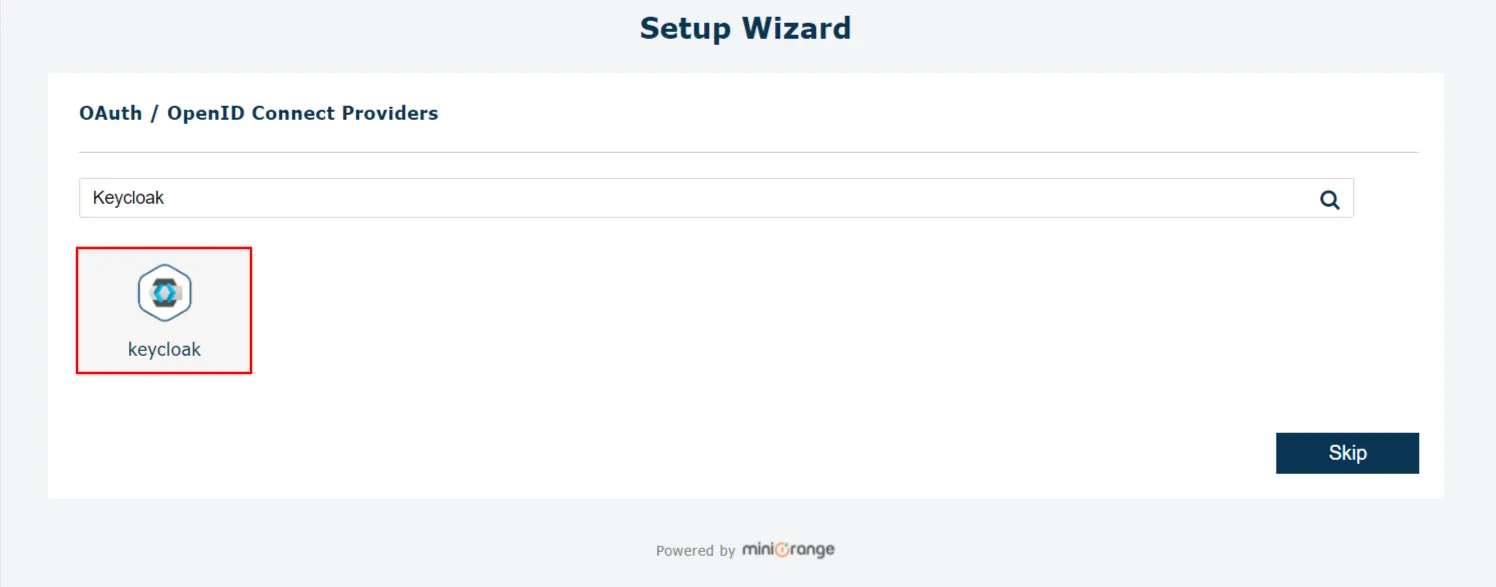
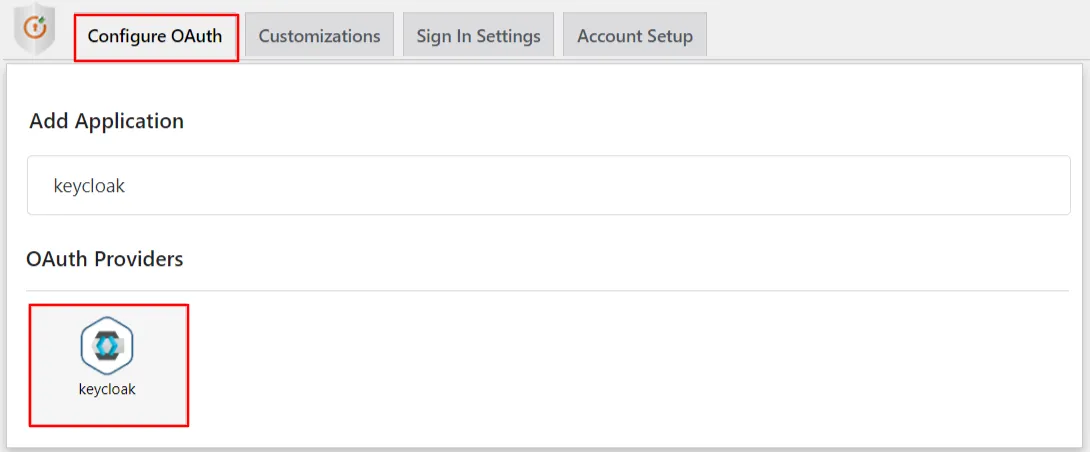
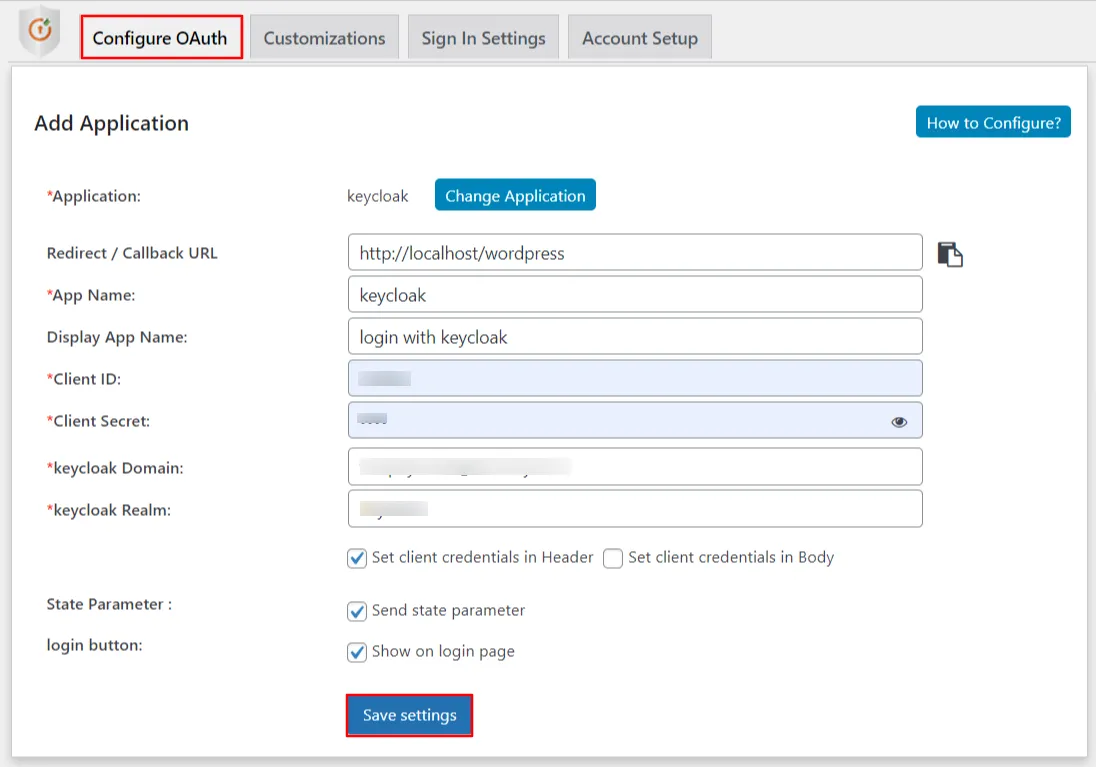
- Go to Configure OAuth tab and click Add New Application to add a new client application into your website.
- Choose your Application from the list of OAuth / OpenID Connect Providers, Here Keycloak
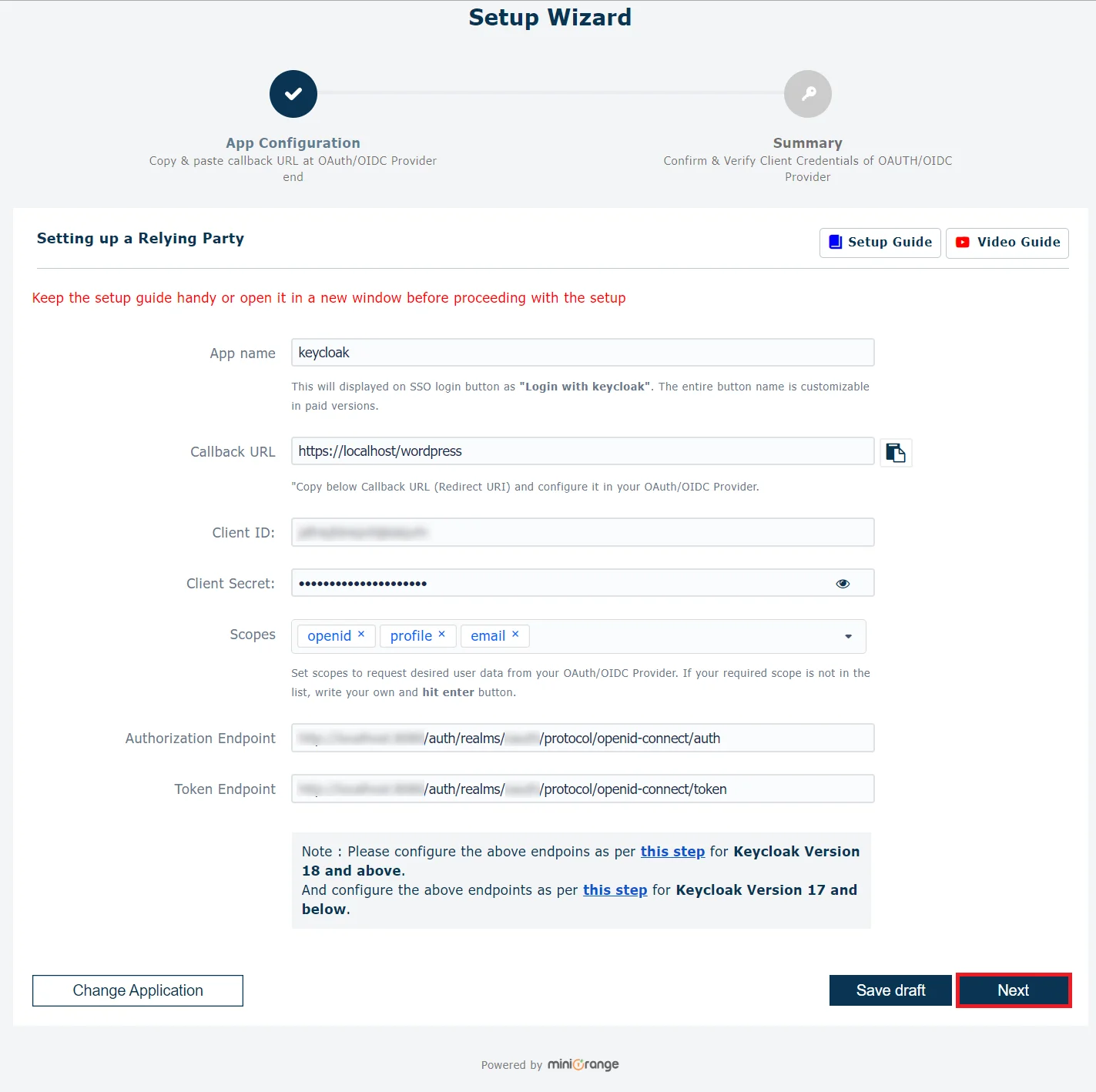
- After selecting the provider copy the Callback URL which needs to be configured in OAuth Provider's SSO application Configuration.
- Client Credentials like Client ID & Client Secret which you will get from the Keycloak SSO application.
- Configure Domain Name & Realm found from the Keycloak SSO application. For the Scopes & Endpoints click here.
- Click on Next.
- Click on Finish to save the configuration.
- Go to Configure OAuth tab and search your application name to add a new client application into your website, Here Keycloak.
- Configure App Name, Client ID, Client Secret, Domain Name & Realm from Keycloak SSO application.
- Choose your Grant Type from the list of options & Click on Save Settings to save the configuration..
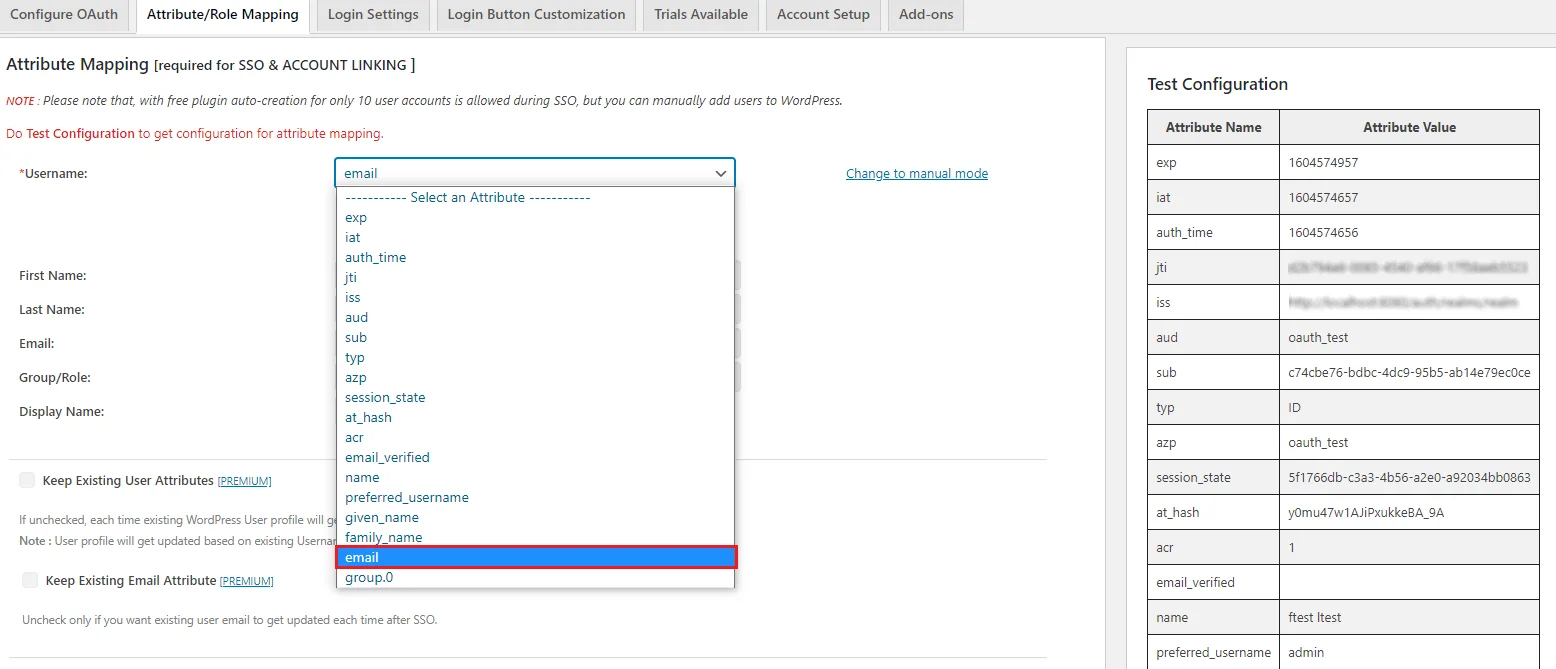
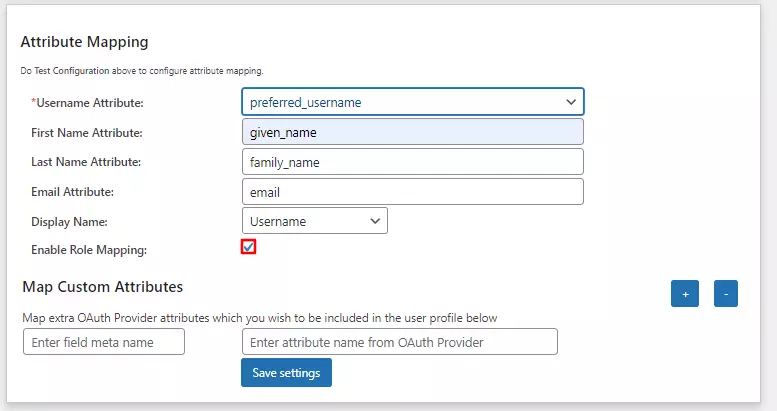
- User Attribute Mapping is mandatory for enabling users to successfully Single Sign-On (SSO) into WordPress. We will be setting up user profile attributes for WordPress using below settings.
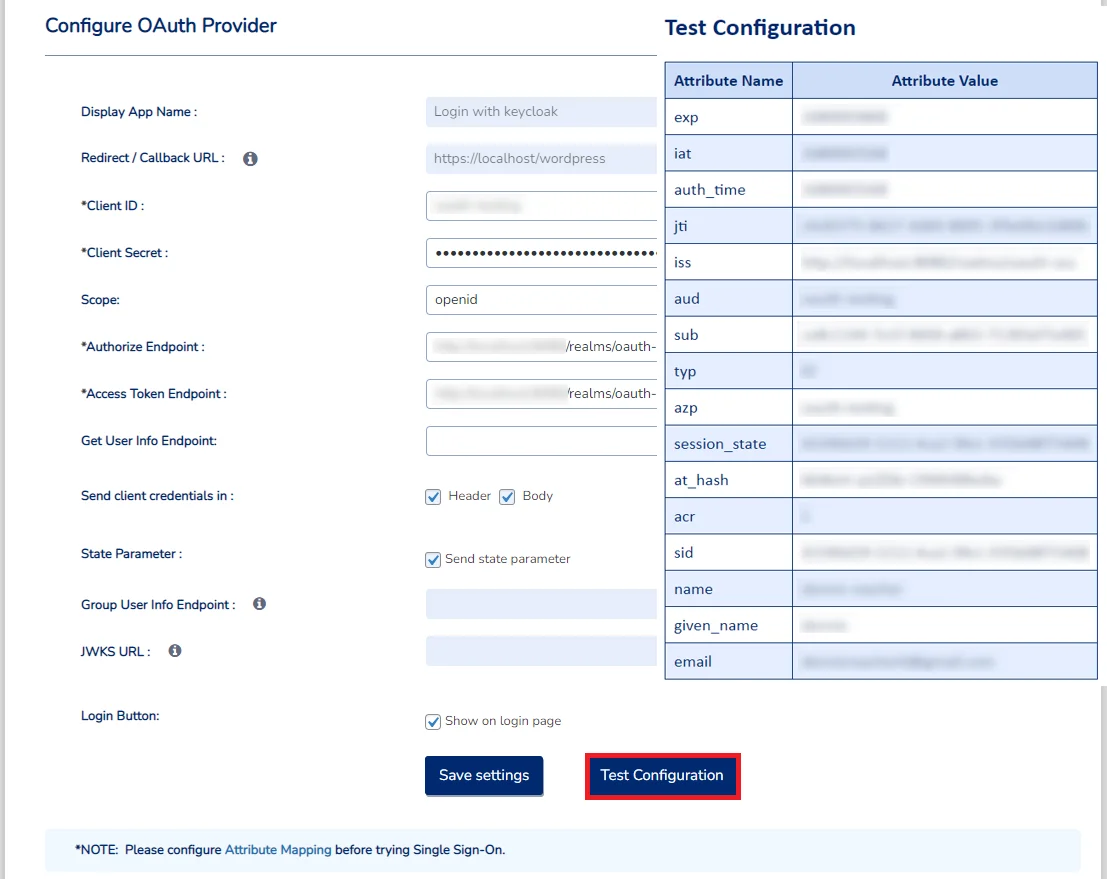
- Go to Configure OAuth tab. Scroll down and click on Test Configuration.
- You will see all the values returned by your OAuth Provider to WordPress in a table. If you don't see value for First Name, Last Name, Email or Username, make the required settings in your OAuth Provider to return this information.
- Once you see all the values in Test Configuration, go to Attribute / Role Mapping tab, you will get the list of attributes in a Username dropdown.
- Click on “Test Configuration” and you will get the list of Attribute Names and Attribute Values that are sent by your OAuth provider.
- From the Test Configuration window, map the Attribute Names in the Attribute Mapping section of the plugin. Refer to the screenshot for more details.
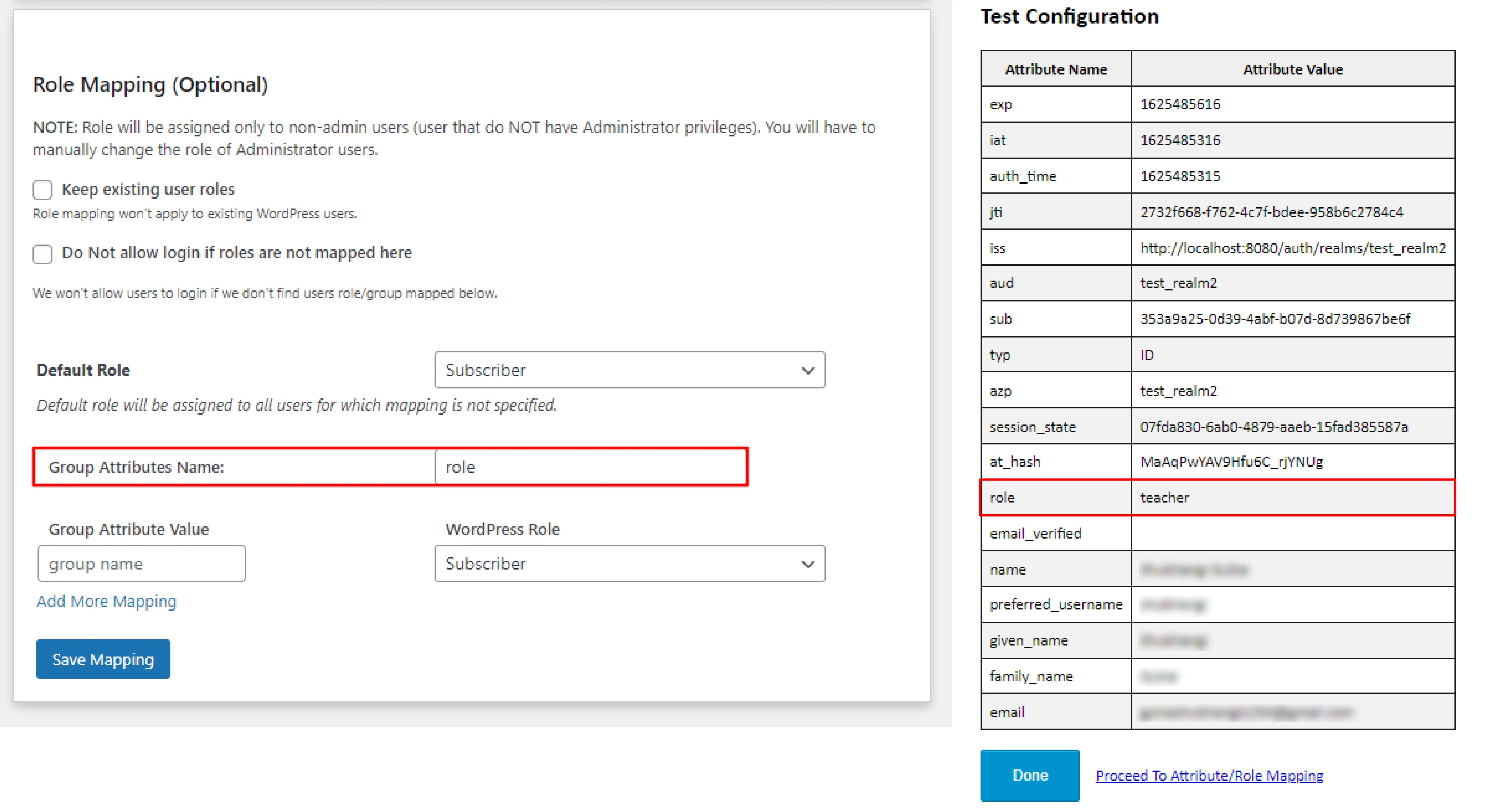
- Enable Role Mapping: To enable Role Mapping, you need to map Group Name Attribute. Select the attribute
name from the list of attributes which returns the roles from your provider application.
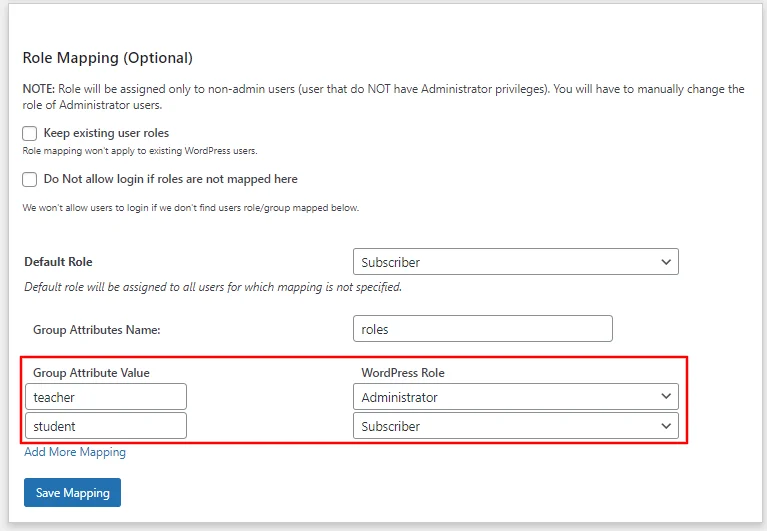
Eg: Role - Assign WordPress role to the Provider role: Based on your provider application, you can allocate the
WordPress role to your provider roles. It can be a student, teacher, administrator or any other depending on
your application. Add the provider
roles under Group Attribute Value and assign the required WordPress role in front of it under WordPress
Role.
For example, in the below image. Teacher has been assigned the role of Administrator & Student is assigned the role of Subscriber. - Once you save the mapping, the provider role will be assigned the WordPress administrator role after Keycloak
SSO.
Example: As per the given example, Users with role ‘teacher’ will be added as Administrator in WordPress and ‘student’ will be added as Subscriber. - The settings in the Single Sign-On (SSO) Settings tab define the user experience for Single Sign-On (SSO) with Keycloak. To add a Keycloak SSO widget on your WordPress page, you need to follow the below steps.
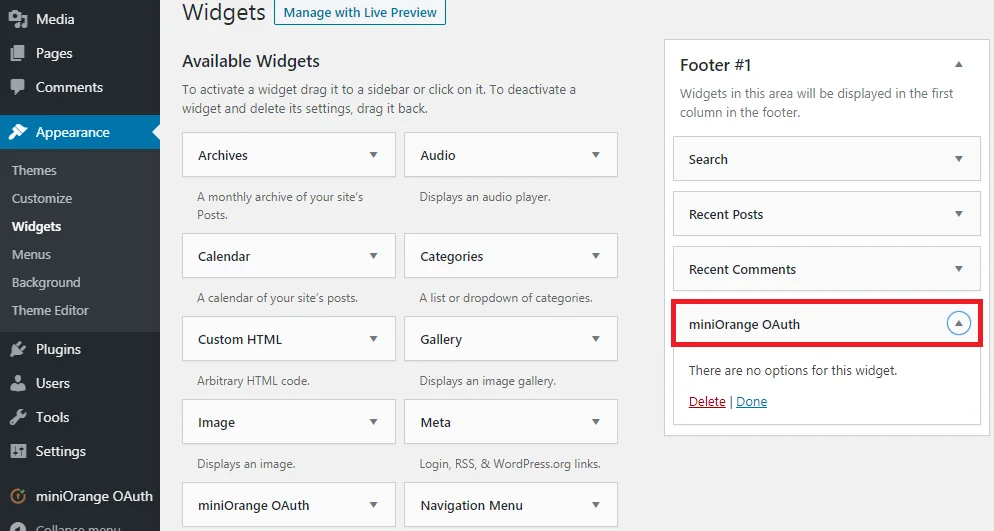
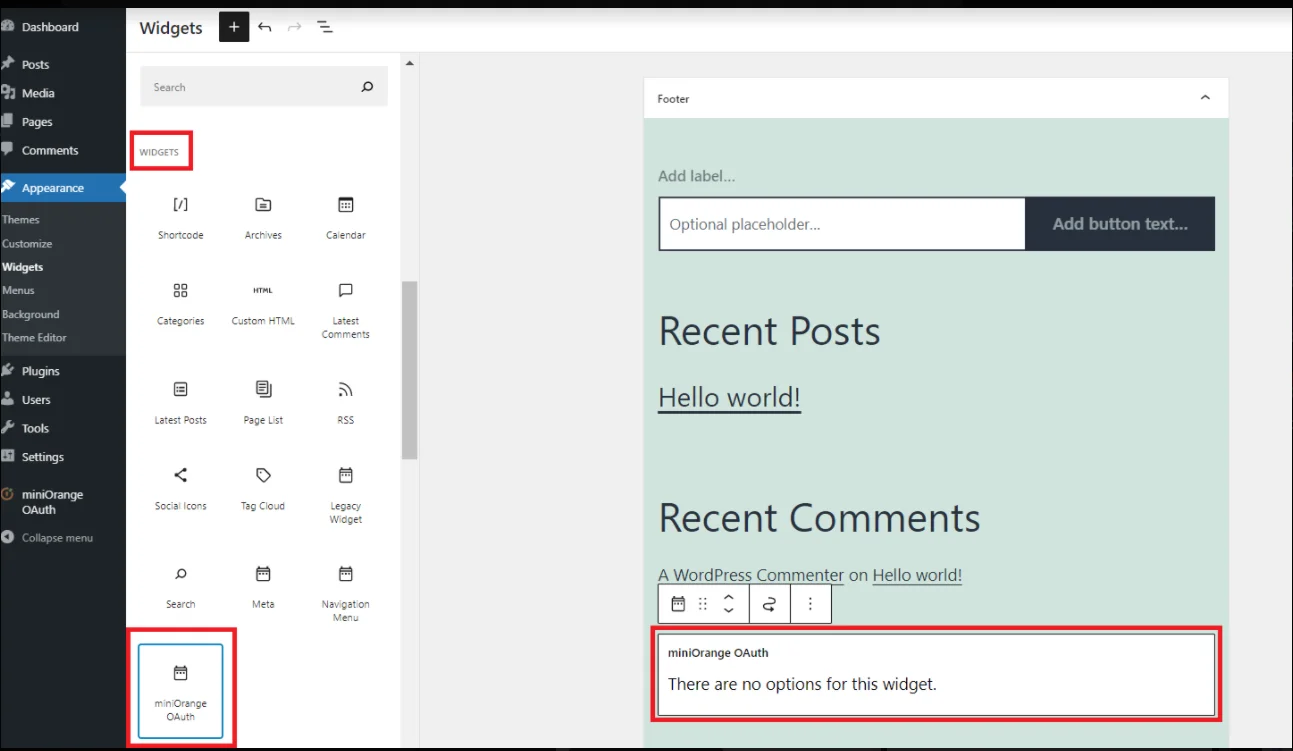
- Go to WordPress Left Panel > Appearances > Widgets.
- Select miniOrange OAuth. Drag and drop to your favourite location and save.
- Go to WordPress Left Panel > Appearances > Widgets.
- Select miniOrange OAuth. Drag and drop to your favourite location and save.
- Open your WordPress page and you can see the Keycloak SSO login button there. You can test the Keycloak Single Sign-On (SSO) - Keycloak OAuth now.
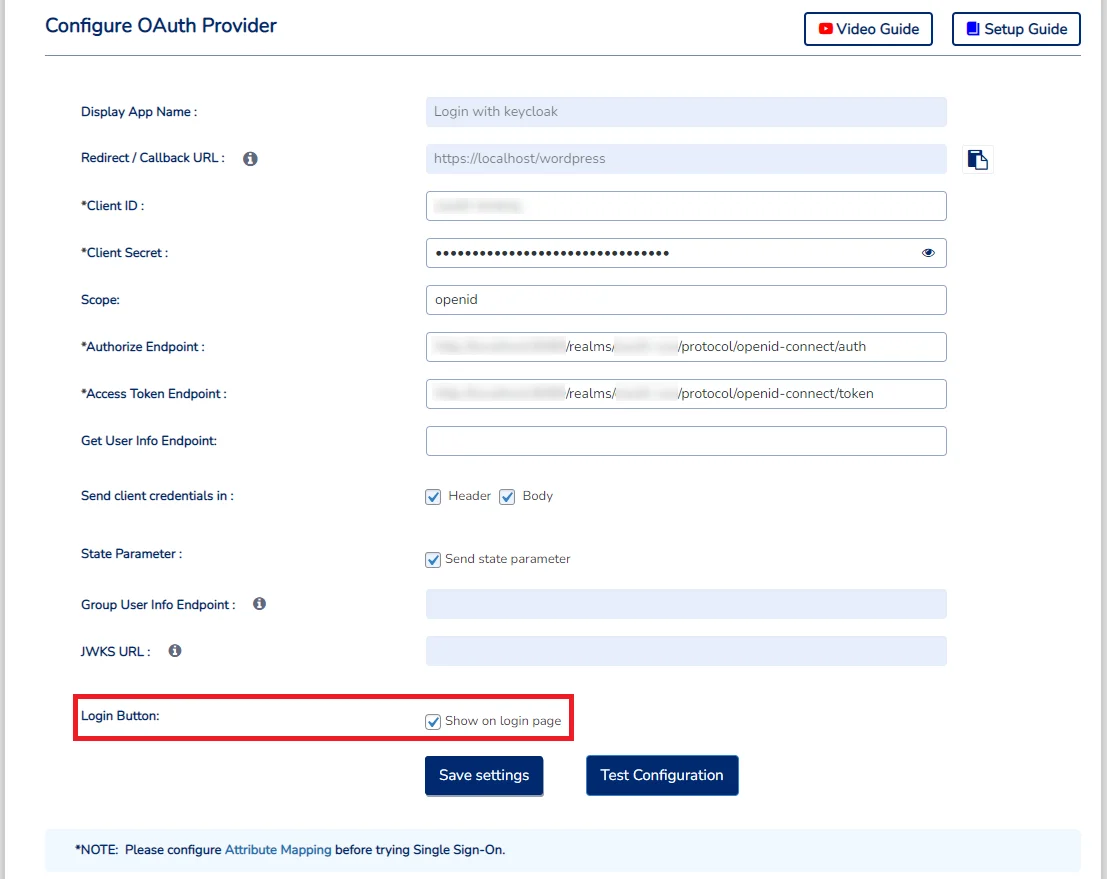
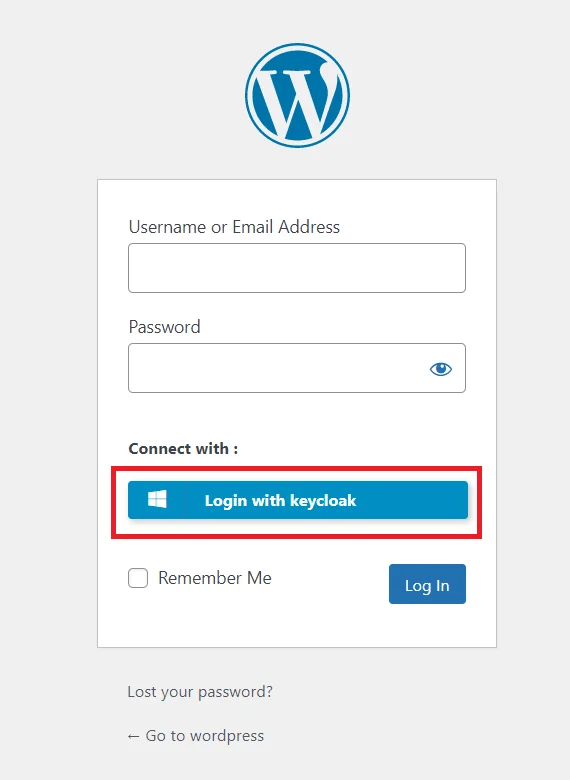
- Make sure the "Show on login page" option is enabled for your application. (Refer to the below image)
- Now, go to your WordPress Login page. (Eg. https://< your-wordpress-domain >/wp-login.php)
- Look out for the Keycloak SSO login button. Once you click the login button, you will be able to test the Keycloak Single Sign-On (SSO).
- Users authentication with Keycloak SSO (Single Sign-On)
- What is Keycloak Single Sign-On (SSO)?
- What is OAuth 2.0 and how does it work?
- What's new about OAuth 2.1 Single Sign-On protocol?
- Frequently Asked Questions (FAQs)
| For the Keycloak Version 16 and below |
Go to the Root Directory of keycloak bin standalone.sh |
| For the Keycloak Version 17 and above |
Go to the Root Directory of keycloak bin kc.bat and run the below commands.
|
- 1) Setting a password for it so click on Credentials and set a new Password for
the user.
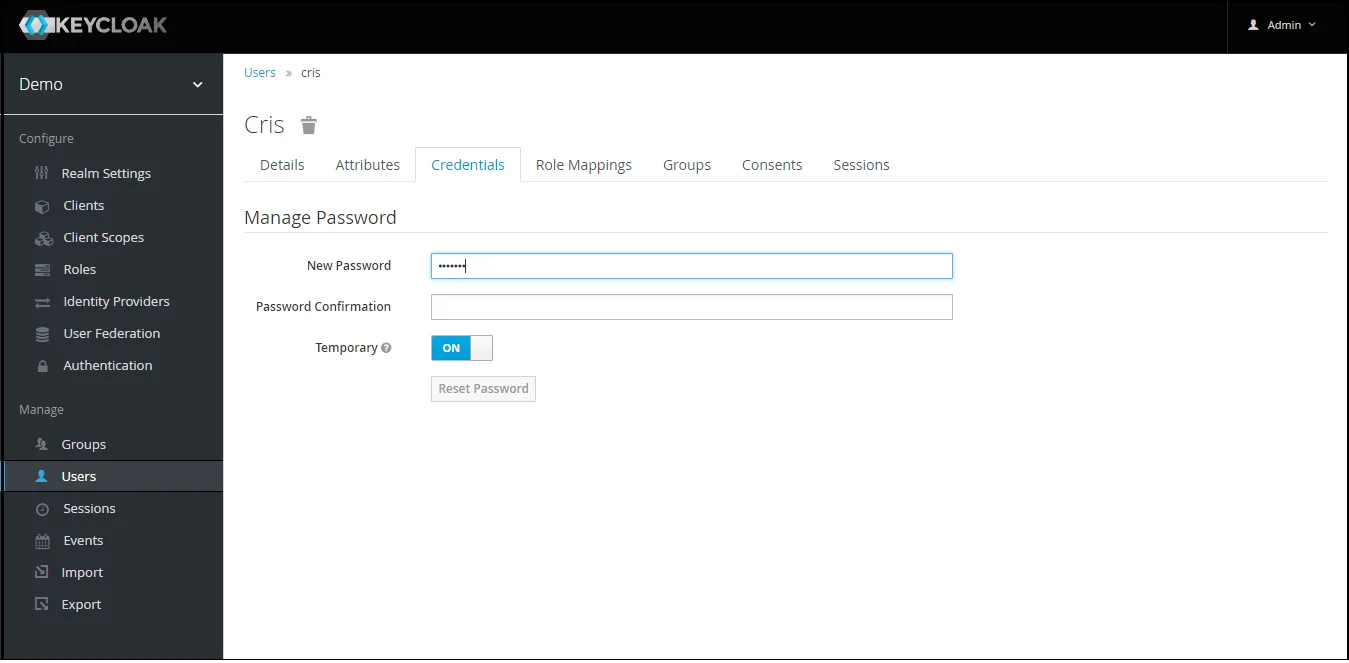
NOTE : Disabling Temporary will make user password permanent.
Step 1.1: Steps to fetch Keycloak Groups [Premium]
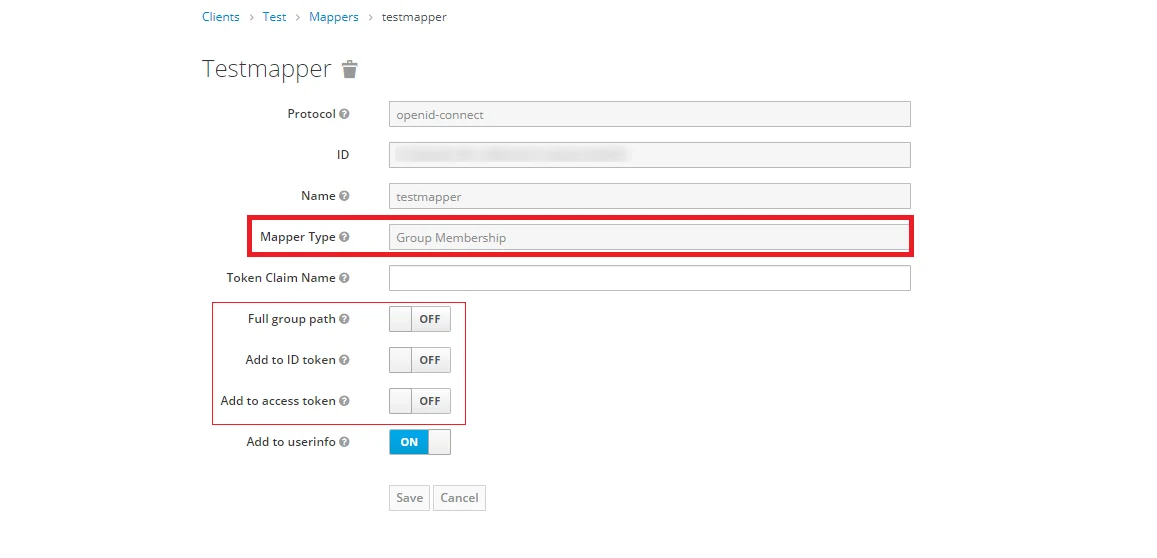
Note: -- If full path is on group path will be fetched else group name will be fetched.
Step 1.2: Steps to fetch Keycloak Roles [Premium]
- 1) Setting a password for it so click on Credentials and set a new Password for
the user.
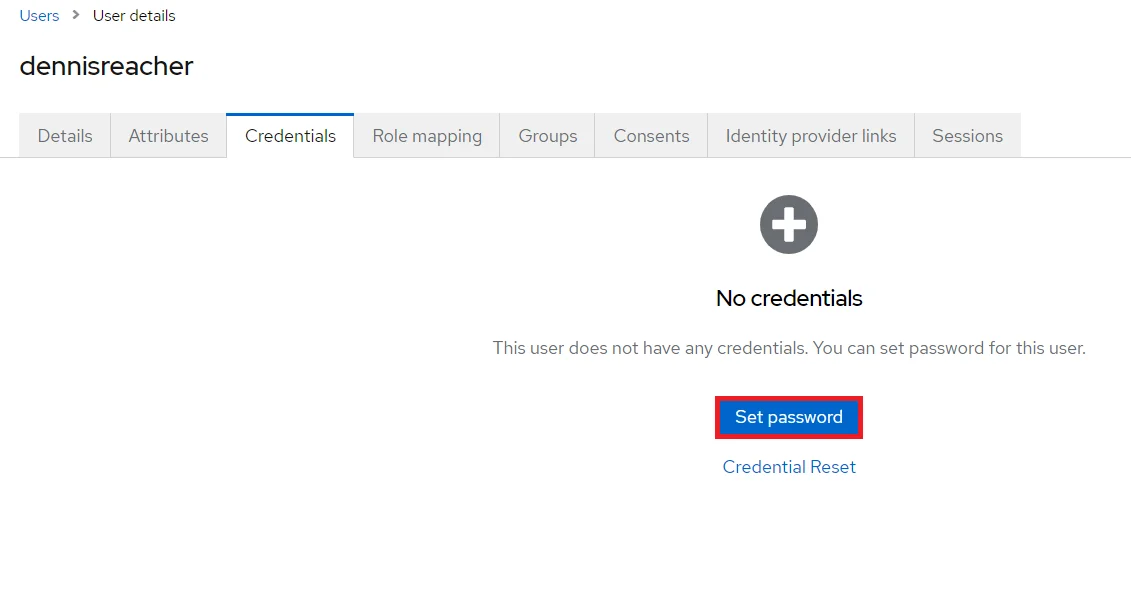
NOTE : Disabling Temporary will make user password permanent.
Step 1.1: Steps to fetch Keycloak Groups [Premium]

In conclusion , You have successfully configured Keycloak as OAuth Provider, for achieving Keycloak Single Sign-On (SSO) with WordPress for user authentication.
2. Setup WordPress as OAuth Client
Note: -- The domain name would be the domain of the machine where your keycloak is running followed by the port number, for e.g if your keycloak is running on localhost then the domain would be http://localhost:8080.
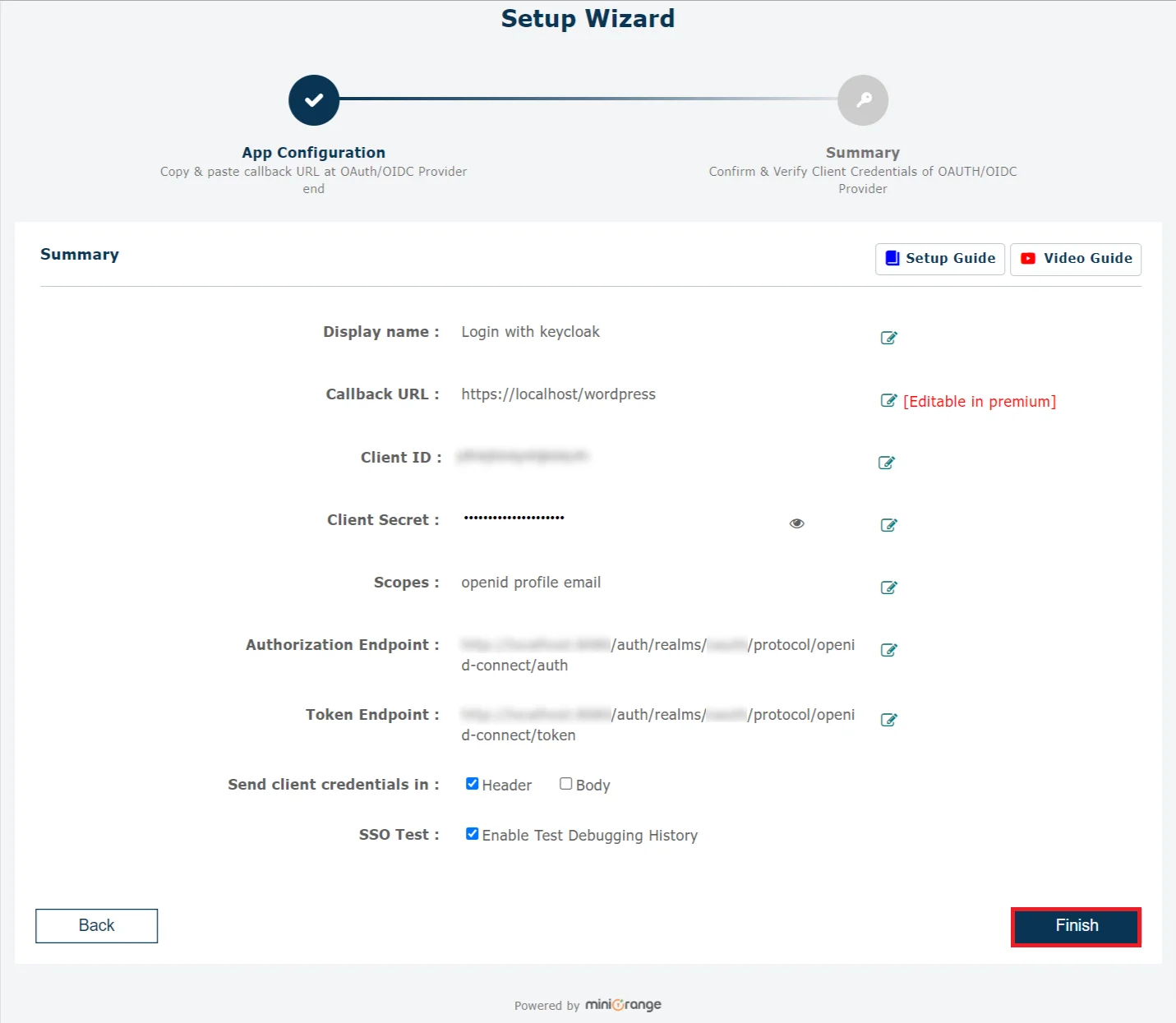
In conclusion , You have successfully configured WordPress as OAuth Client, for achieving Keycloak Single Sign-On (SSO) with WordPress for user authentication.
Note: -- The domain name would be the domain of the machine where your keycloak is running followed by the port number, for e.g if your keycloak is running on localhost then the domain would be http://localhost:8080.
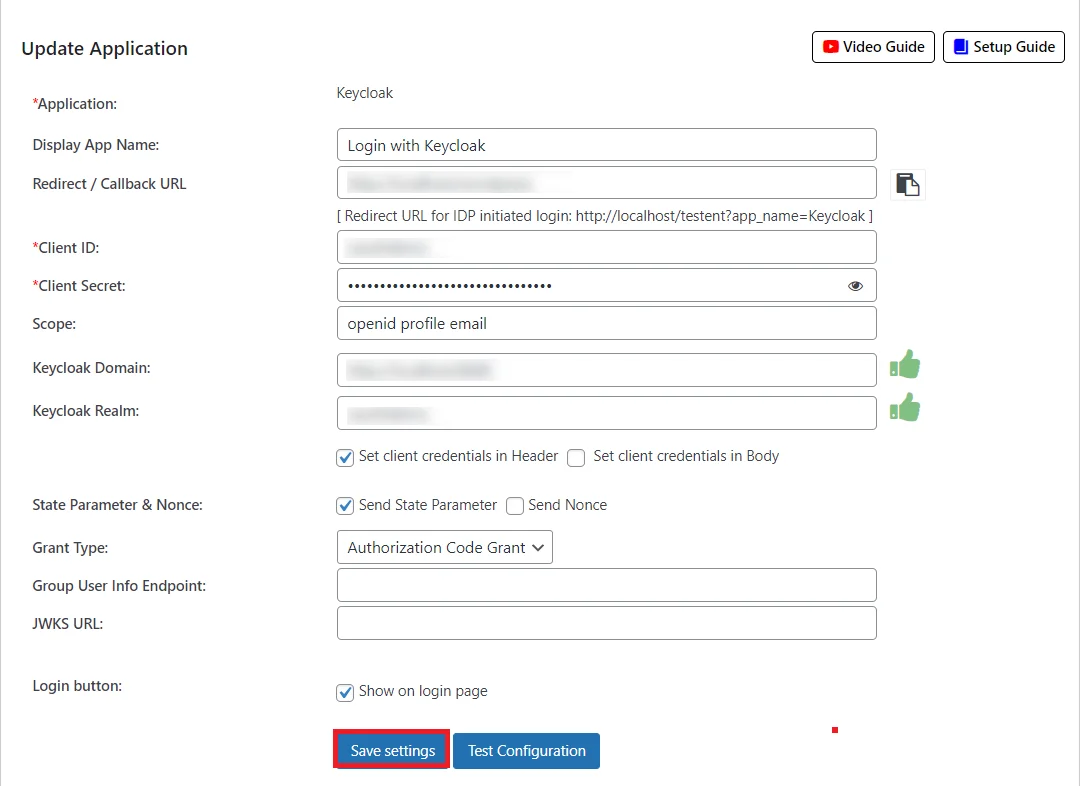
In conclusion , You have successfully configured WordPress as OAuth Client, for achieving Keycloak Single Sign-On (SSO) with WordPress for user authentication.
3. User Attribute Mapping
Finding user attributes
4. Role Mapping [Premium]
5. Sign In Settings
Sign in settings for WordPress 5.7 and before
Sign in settings for WordPress 5.8
Sign in settings for WordPress 5.9
6: Scope and Endpoints
Please refer the below table for configuring the scope & endpoints for Keycloak Version 18 and above in the plugin.
| Scope: | email profile openid |
| Authorize Endpoint: | <keycloak domain>/realms/{realm-name}/protocol/openid-connect/auth |
| Access Token Endpoint: | <keycloak domain>/realms/{realm-name}/protocol/openid-connect/token |
| Get User Info Endpoint: | <keycloak domain>/realms/{realm-name}/protocol/openid-connect/userinfo | Custom redirect URL after logout: [optional] | https://{keycloak domain}/realms/{realm-name}/protocol/openid-connect/logout?post_logout_redirect_uri={encodedRedirectUri}&id_token_hint=##id_token## |
Please refer the below table for configuring the scope & endpoints for Keycloak Version 17 and below in the plugin.
| Scope: | email profile openid |
| Authorize Endpoint: | <keycloak domain>/auth/realms/{realm-name}/protocol/openid-connect/auth |
| Access Token Endpoint: | <keycloak domain>/auth/realms/{realm-name}/protocol/openid-connect/token |
| Get User Info Endpoint: | <keycloak domain>/auth/realms/{realm-name}/protocol/openid-connect/userinfo | Custom redirect URL after logout: [optional] | <keycloak domain>/auth/realms/{realm-name}/protocol/openid-connect/logout?redirect_uri=encodedRedirectUri |
In conclusion, after successfully configuring Keycloak as an OAuth Provider and WordPress as an OAuth Client, you've achieved a smooth and secure authentication process for your users. Through Keycloak Single Sign-On (SSO), you can ensure a robust user experience within the WordPress environment. This allows users the ease of accessing multiple applications with a single set of login credentials. Through the integration of Keycloak OAuth as the primary authentication solution, users can securely log into their WordPress accounts with their existing Keycloak credentials.
Frequently Asked Questions (FAQs)
I cannot find Domain and Realm in Keycloak admin interface.
Login to the Keycloak administration console. Go to the Realm settings -> general section, and you will get the Realm name. Need more assistance with Keycloak SSO?Read more
Additional Resources
Experiencing challenges with Keycloak SSO? Mail us on oauthsupport@xecurify.com for quick guidance(via email/meeting) on your requirement and our team will help you to select the best suitable solution/plan as per your requirement.
Need Help? We are right here!

Thanks for your inquiry.
If you dont hear from us within 24 hours, please feel free to send a follow up email to info@xecurify.com
Cookie Preferences
Cookie Consent
This privacy statement applies to miniorange websites describing how we handle the personal information. When you visit any website, it may store or retrieve the information on your browser, mostly in the form of the cookies. This information might be about you, your preferences or your device and is mostly used to make the site work as you expect it to. The information does not directly identify you, but it can give you a more personalized web experience. Click on the category headings to check how we handle the cookies. For the privacy statement of our solutions you can refer to the privacy policy.
Strictly Necessary Cookies
Always Active
Necessary cookies help make a website fully usable by enabling the basic functions like site navigation, logging in, filling forms, etc. The cookies used for the functionality do not store any personal identifiable information. However, some parts of the website will not work properly without the cookies.
Performance Cookies
Always Active
These cookies only collect aggregated information about the traffic of the website including - visitors, sources, page clicks and views, etc. This allows us to know more about our most and least popular pages along with users' interaction on the actionable elements and hence letting us improve the performance of our website as well as our services.
