Need Help? Schedule a free meeting with our experts right away using Calendly
Book Your SlotUse cases supported with our SSO module
Windows Authentication (SSO)
DNN Single Sign-On (SSO) authentication provider module for OAuth/JWT has support for Integrated Windows Authentication(IWA). Integrated Windows Authentication is the preferred approach to authentication whenever users are part of the same Windows domain as the server. Users are authenticated against an existing identity store such as Active Directory which gives seamless login experience.
Single Sign-On (SSO) into Multiple DotNetNuke sites
DNN Single Sign-On (SSO) authentication provider module for SAML also supports login into multiple DotNetNuke sites with one set of credentials using SAML protocol. Once the user will be logged into one of the DNN sites, he/she will be logged into to other DNN sites automatically that is no need to enter login credentials for other sites again.
Single Sign-On (SSO) into single DotNetNuke (DNN) site
DNN Single Sign-On (SSO) authentication provider module for SAML helps you to add functionality for Single Sign-On (SSO) to your DotNetNuke site. Our DNN authentication provider enables users to securely authenticate with multiple applications and websites by logging in only once—with just one set of credentials (username and password).
Multi Factor Authentication (MFA) for passwordless login to your DotNetNuke site
Secure your DotNetNuke site from password thefts using multi-factor authentication (MFA) methods with 15+ authentication types provided by miniOrange. Our multi-factor authentication (MFA) methods prevent unauthorized users from accessing information and resources having password alone as an authentication factor. Enabling second-factor authentication or two factor authentication(2FA)for your DotNetNuke site protects you against password thefts.
IP blocking for your DotNetNuke (DNN) site
DNN Single Sign-On (SSO) module helps you to add IP blocking/IP restriction to your DotNetNuke (DNN) site which adds extra security to DotNetNuke (DNN) site. In this, we provide you option for IP blocking which includes both automatic (based on user behavior) and manual IP blocking which includes blacklisting and whitelisting of IP addresses to provide access restriction, the office only access, intranet access & network restriction
Adaptive Authentication
Using Adaptive Authentication you can also restrict the No. of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. The end users will be able to access services provided by us on this fixed no. of devices.
Key Features
Single Sign On
Easy and seamless access to all resources. Login to your DotNetNuke (DNN) site via any existing OAuth / OpenID / JWT provider that conforms to the OAuth 2.0 and OpenID Connect (OIDC) 1.0 standard.
Role Mapping
Map your Identity Provider roles to your DNN roles and restrict resources to specific roles.
Protect complete Site
You can restrict your site to only logged in users by redirecting the users to your IdP if logged in session is not found.
Multiple OAuth / OpenID / JWT Connect Provider Support
Support for adding login with one or more OAuth / OpenID / JWT Connect Providers.
Attribute Mapping
Offers you to map the attributes from your IdP to your DotNetNuke user attributes.
Account Linking
After user SSO to DNN, if user already exists in DNN, then his profile gets updated or it will create a new DNN User.
Multi-Portal Support
Add support for login to your all DoteNetNuke (DNN) parent as well as child portals using your Identity Provider credentials.
Plans For Everyone
Trial
Start NowFeatures Provided
Unlimited Authentications
Basic Attribute Mapping (Username, Email)
Auto Create Users
Account Linking
Basic Role Mapping
Override Default Login
Custom Redirect after SSO Login
Custom Redirect after SSO Logout
Advanced Attribute Mapping(Firstname Lastname etc.)
Advance Role Mapping
Multiple OAuth / OpenID Providers
Force Authentication
Domain Restriction
Support of SSO on Multiple Portals
PKCE Flow
Advance UserInfo Token Validation
$449*
Buy NowFeatures Provided
Unlimited Authentications
Basic Attribute Mapping (Username, Email)
Auto Create Users
Account Linking
Basic Role Mapping
Override Default Login
Custom Redirect after SSO Login
Custom Redirect after SSO Logout
Advanced Attribute Mapping(Firstname Lastname etc.)
Advance Role Mapping
Multiple OAuth / OpenID Providers
Force Authentication
Domain Restriction
Support of SSO on Multiple Portals
PKCE Flow
Advance UserInfo Token Validation
$649*
Buy NowFeatures Provided
Unlimited Authentications
Basic Attribute Mapping (Username, Email)
Auto Create Users
Account Linking
Basic Role Mapping
Override Default Login
Custom Redirect after SSO Login
Custom Redirect afetr SSO Logout
Advanced Attribute Mapping(Firstname Lastname etc.)
Advance Role Mapping
Multiple OAuth / OpenID Providers
Force Authentication
Domain Restriction
Support of SSO on Multiple Portals
PKCE Flow
Advance UserInfo Token Validation
Need Help? We do offer technical support!
* We offer significant discounts on bulk licence purchases and licences for pre-production environments. As the number of licences increases, so does the discount percentage.** The amount of Identity Providers you have costs an additional charge.
Steps to Configure the DNN OAuth Single Sign-On (SSO) Authentication Provider
Step 1: Download and Install the authentication provider in DotNetNuke.
- Download the package for DNN OAuth Single Sign-On (SSO) Authentication Provider.
- Upload the installation package dnn-oauth-single-sign-on_xxx_Install by going in Settings > Extension > Install Extension.
Step 2: Adding Authentication Provider on DNN page.
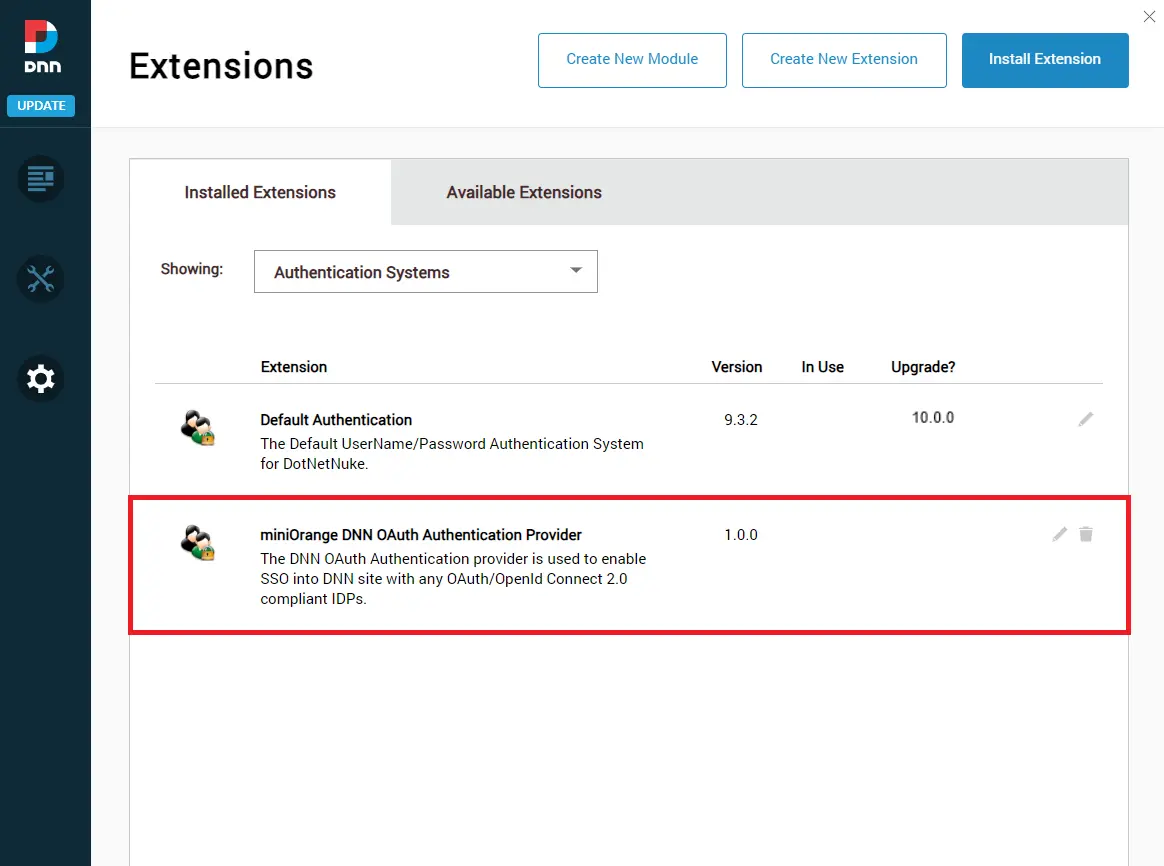
- Now under the Installed extensions tab select Authentication Systems. Here you can see the miniOrange DNN OAuth Authentication Provider.
- Just click on the pencil icon as mentioned in the image below to configure the DNN OAuth Authentication Provider.
- You have finished with the installation of the Authentication Provider on your DNN site.
Step 3: Configure Authentication Provider for Setting up OAuth Single Sign-On (SSO)
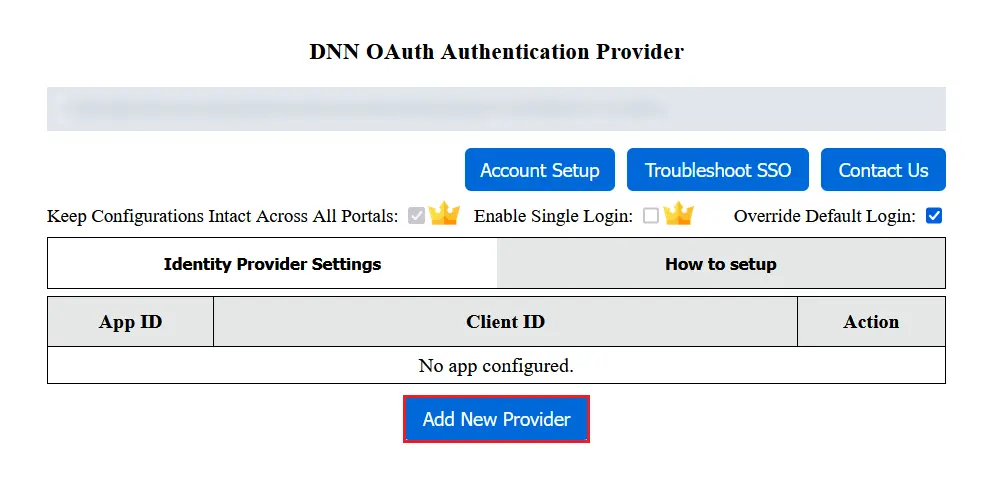
- For configuring application in the authentication provider, click on the Add New Provider button in the Identity Provider Settings tab.
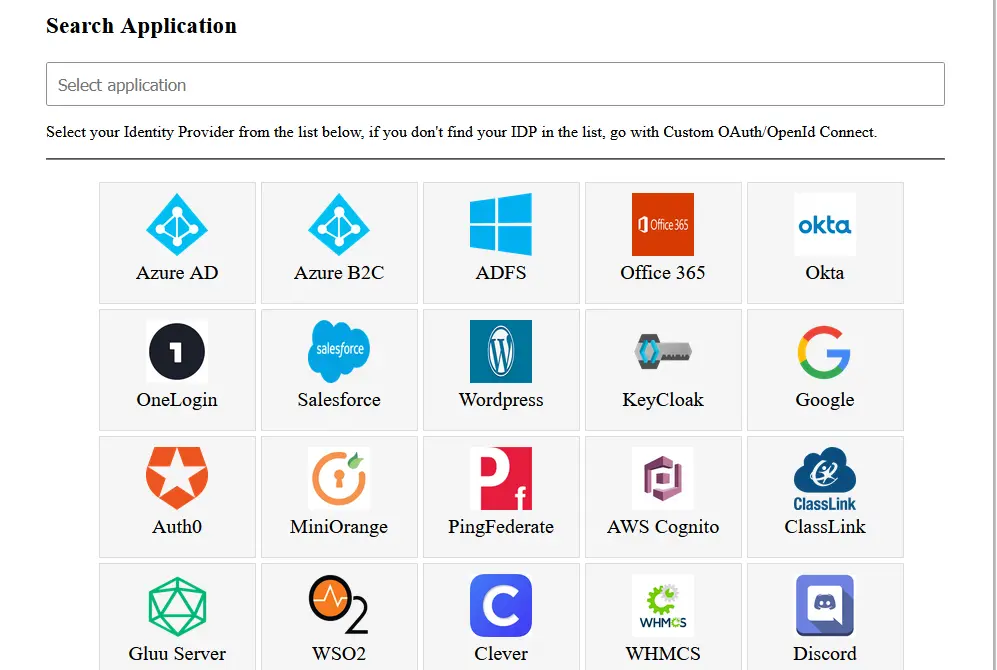
- Select your Identity Provider from the list. If you don't find your Identity provider in the list, select custom OAuth/OpenID provider. You can also search for your Identity Provider using the search box.
Select your Identity Provider
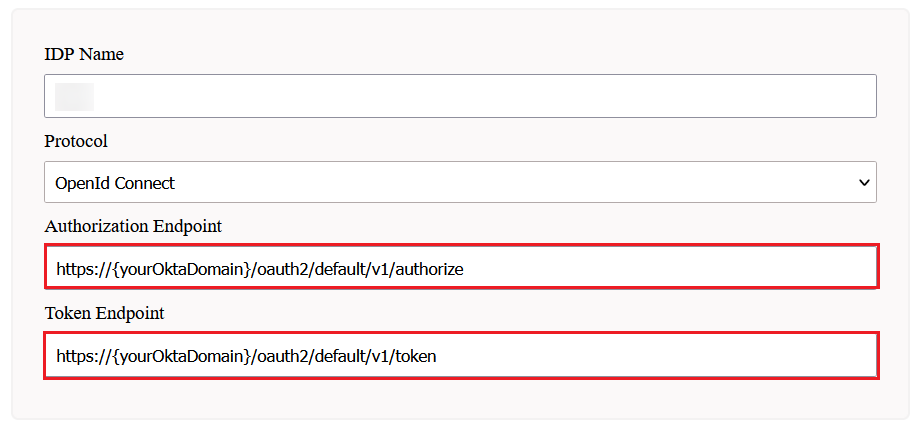
Step 4: Configuring OAuth Provider
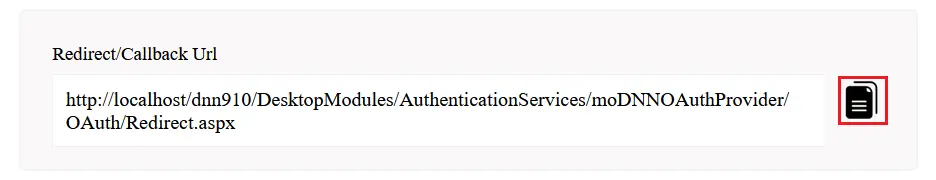
- Copy the Redirect/Callback URL and provide it to your OAuth provider.
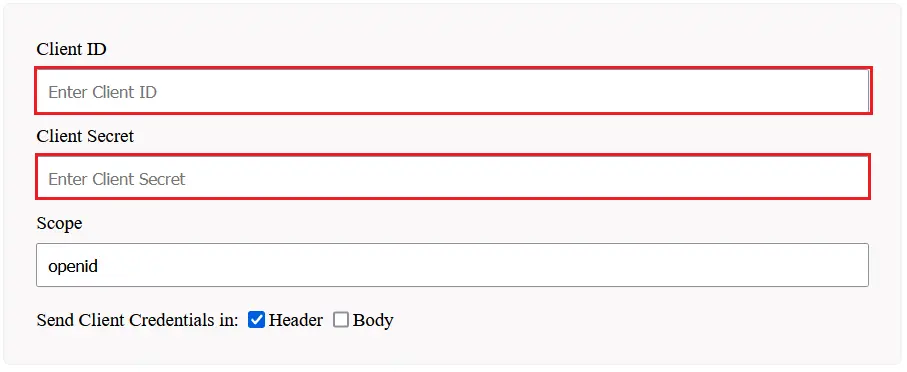
Step 5: Configuring OAuth Client
- Configure Client ID, Client Secret, update the endpoints if required and save the settings.
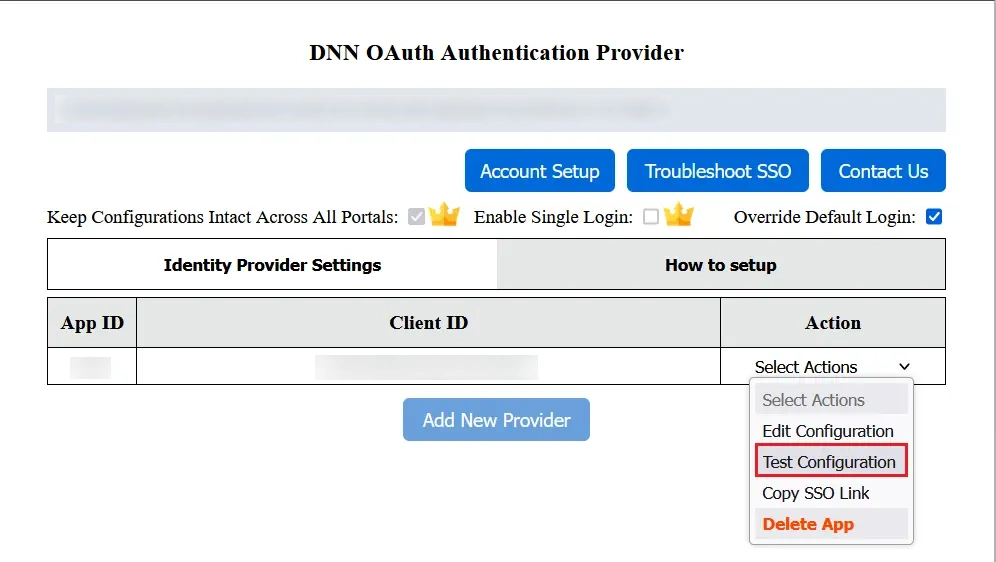
Step 6: Test Configuration
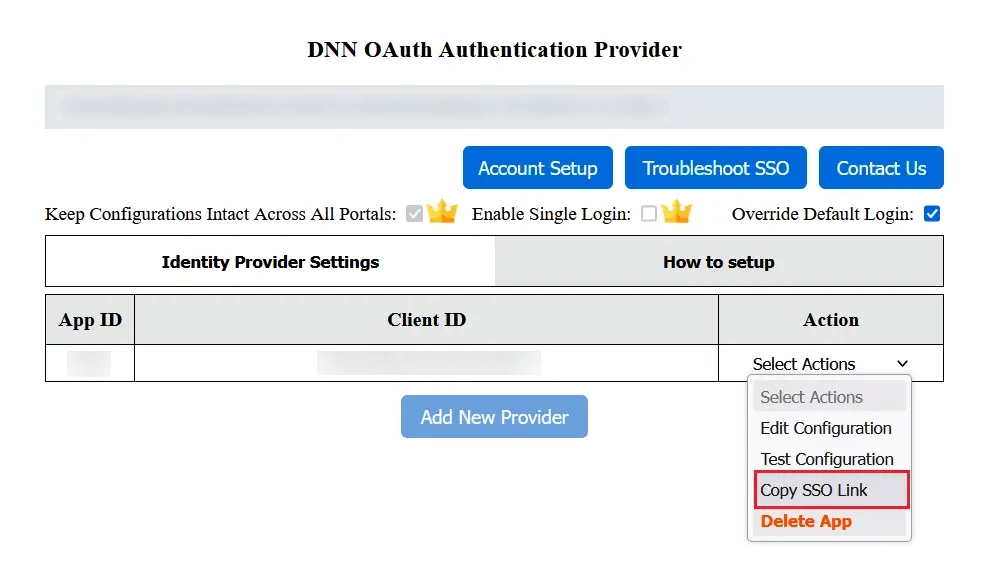
- Now go to the Identity Provider Settings tab.
- Under the select actions click on the Test Configuration button to verify if you have configured the authentication provider correctly.
- On successful configuration, you will get Attribute Name and Attribute Values in the Test Configuration window.
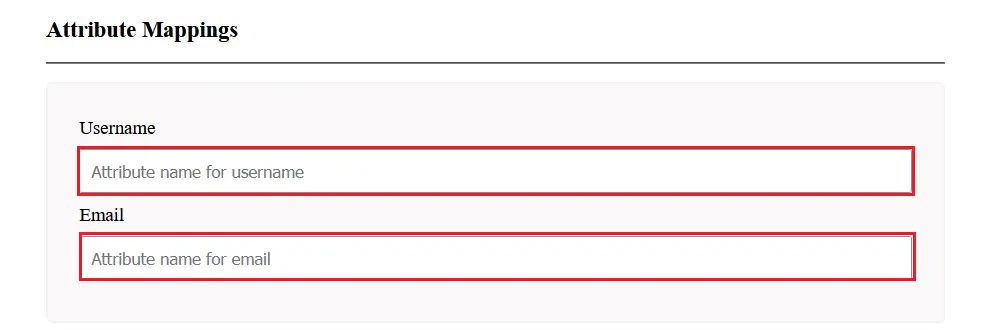
Step 7: Attribute Mapping
- For attribute mapping select the Edit Configuration from the select actions dropdown.
- Map email and username with Attribute Name you can see in Test Configuration window and save the settings.
Step 8: Get the Single Sign-On (SSO) link for your application
- You can find the SSO Link in the Action dropdown in Applications List of the authentication provider.
You also can configure the DNN OAuth 2.0 Single Sign-On (SSO) authentication provider with any Identity Provider such as Azure AD, Azure B2C, Keycloak, Okta, OneLogin, Salesforce, AWS Cognito, PingFederate, Auth0, ClassLink, WSO2, Discord or even with your own custom identity provider.
We also provide ASP.NET SAML Single Sign-On module for setting up Single Sign-On to your ASP.NET Custom Applications. Click Here to know more.
miniOrange also provides you modules for integration with legacy apps such as Active Directory, SiteMinder, Radius, Unix and so on. Using SAML, OAuth, OpenID, ADFS, and WSFED protocols, we can also help you add login/authentication to your Umbraco site.
Additonal Resources:
- DNN SAML Integrations
- ASP.NET SAML Integrations
- nopCommerce SAML Integrations
- DNN OAuth Single Sign-On (SSO)
- DNN SAML Single Sign-On (SSO)
- DNN REST API Authentication
Need Help?
Not able to find your identity provider? Mail us on dnnsupport@xecurify.com and we'll help you set up SSO with your IDP and for quick guidance (via email/meeting) on your requirement and our team will help you to select the best suitable solution/plan as per your requirement.
Request a Live Demo for DNN SSO Now
Explore the Benefits of Our DNN Single Sign On Plugin with a Live Demo by Our miniOrange Expert
Thank you for your response. We will get back to you soon.
Something went wrong. Please submit your query again



Contact us at - +1 978 658 9387 (US) | +91 97178 45846 (India) dnnsupport@xecurify.com


