Contents
SAML Single Sign On (SSO) into Jenkins
Jenkins SAML Single Sign On (SSO) app gives you the ability to enable Single Sign-On (SSO or SAML SSO) through SAML 2.0 for Jenkins. With help of our Jenkins SAML SSO plugin one can easily authenticate the users into Jenkins.
(Click here to Download Jenkins Single Sign On app)
Jenkins SSO app is compatible with all SAML 2.0 Identity Providers like:- Azure AD, Keycloak, ADFS, Okta, Salesforce, Shibboleth 2, GSuite / Google Apps, miniOrange, OneLogin, Centrify, SimpleSAMLphp, OpenAM , PingOne, RSA, Oracle, Bitium , WSO2, Auth0, AuthAnvil and practically any SAML compliant Identity Provider.
Click here to know more about Jenkins Single Sign on.
If you don't find your IDP listed and your application supports SAML 2.0 as an Identity Provider, you can follow the guide given below to enable SSO into Jenkins using your application.
Download and install the plugin in Jenkins
-
To download the miniorange saml SP plugin follow the path: Through Jenkins plugin directory.
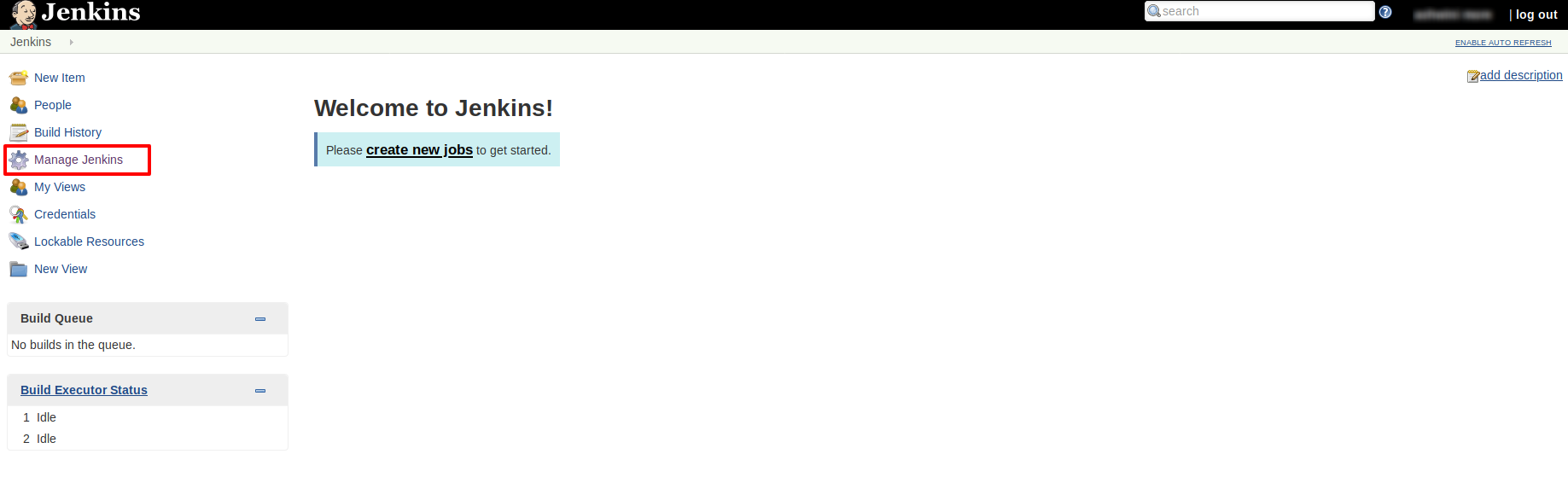
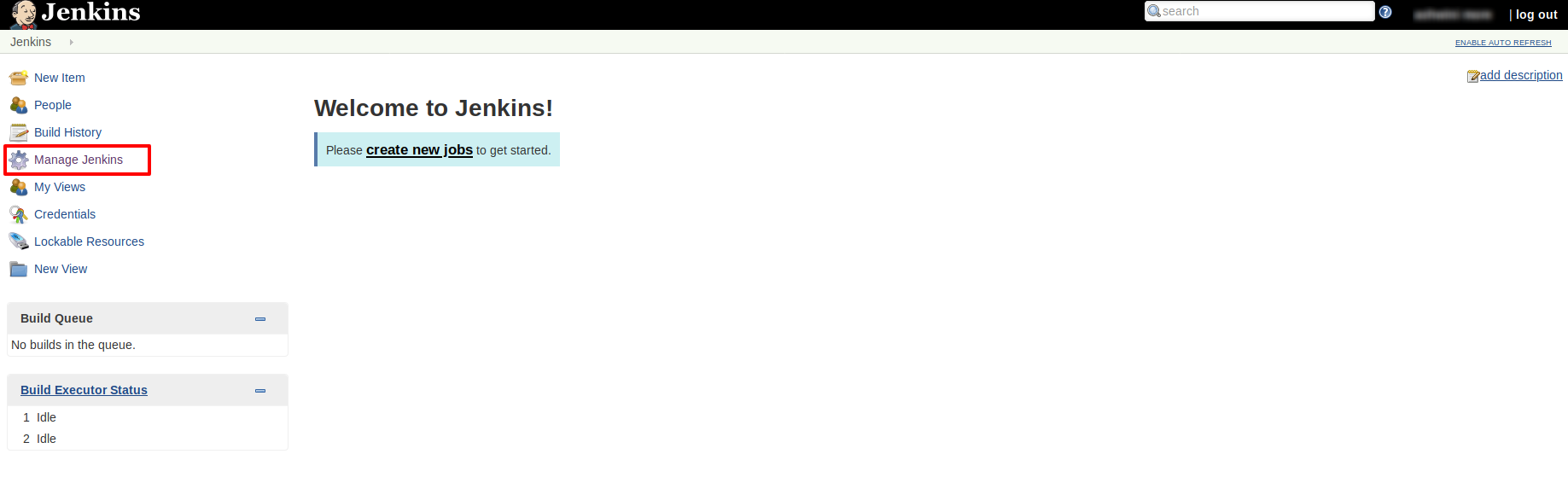
- Login to your Jenkins.
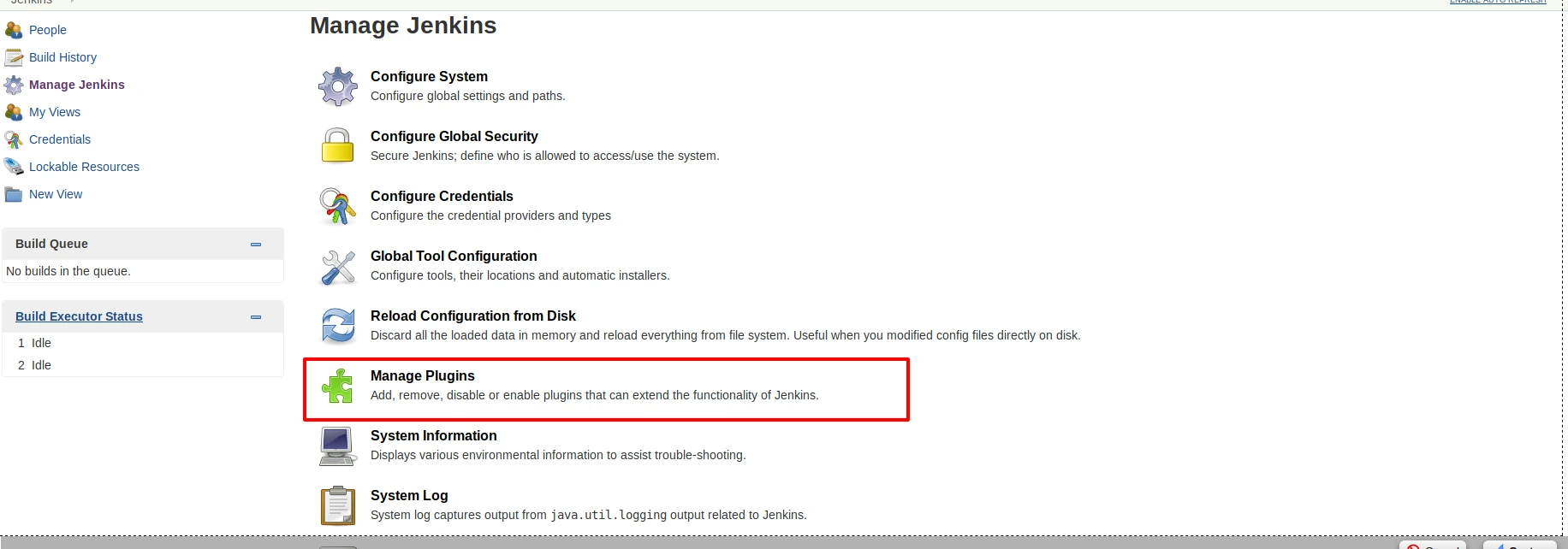
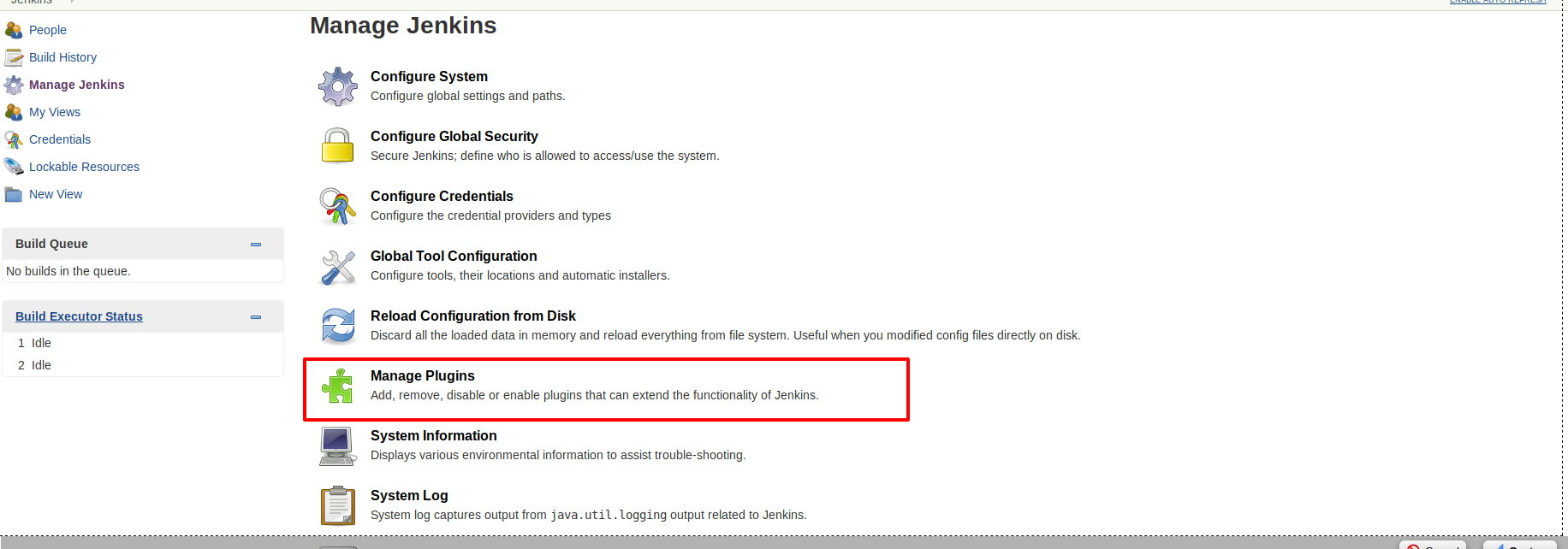
- Go to Manage Jenkins option from the left pane, and open Manage Plugins tab.
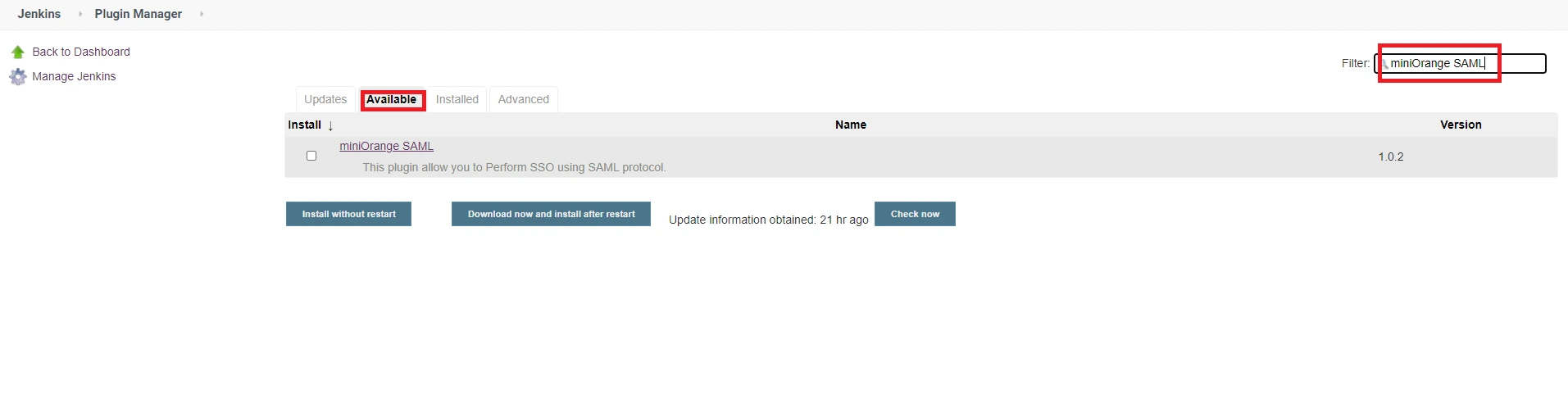
- Search for ‘Miniorange saml’ in the available tab.
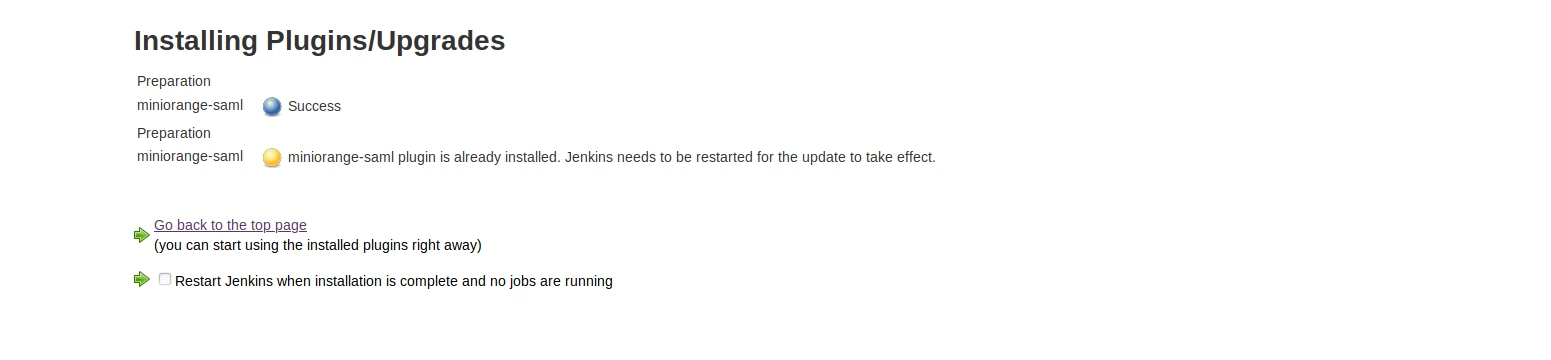
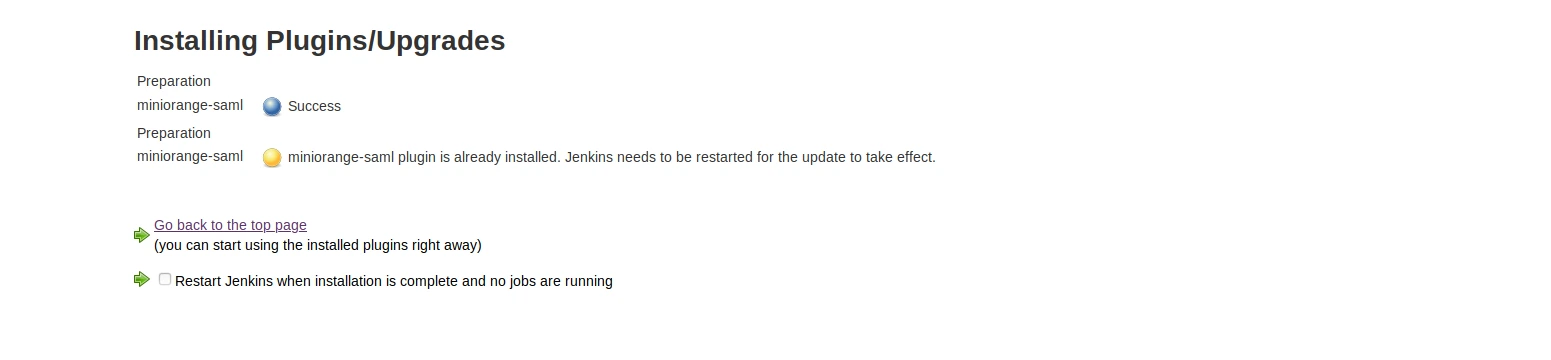
- Download and install with a restart.
-
To download the miniorange saml SP plugin follow the path: Through Manual Configuration.
- Login to your Jenkins.
- Go to Manage Jenkins option from the left pane, and open Manage Plugins tab.
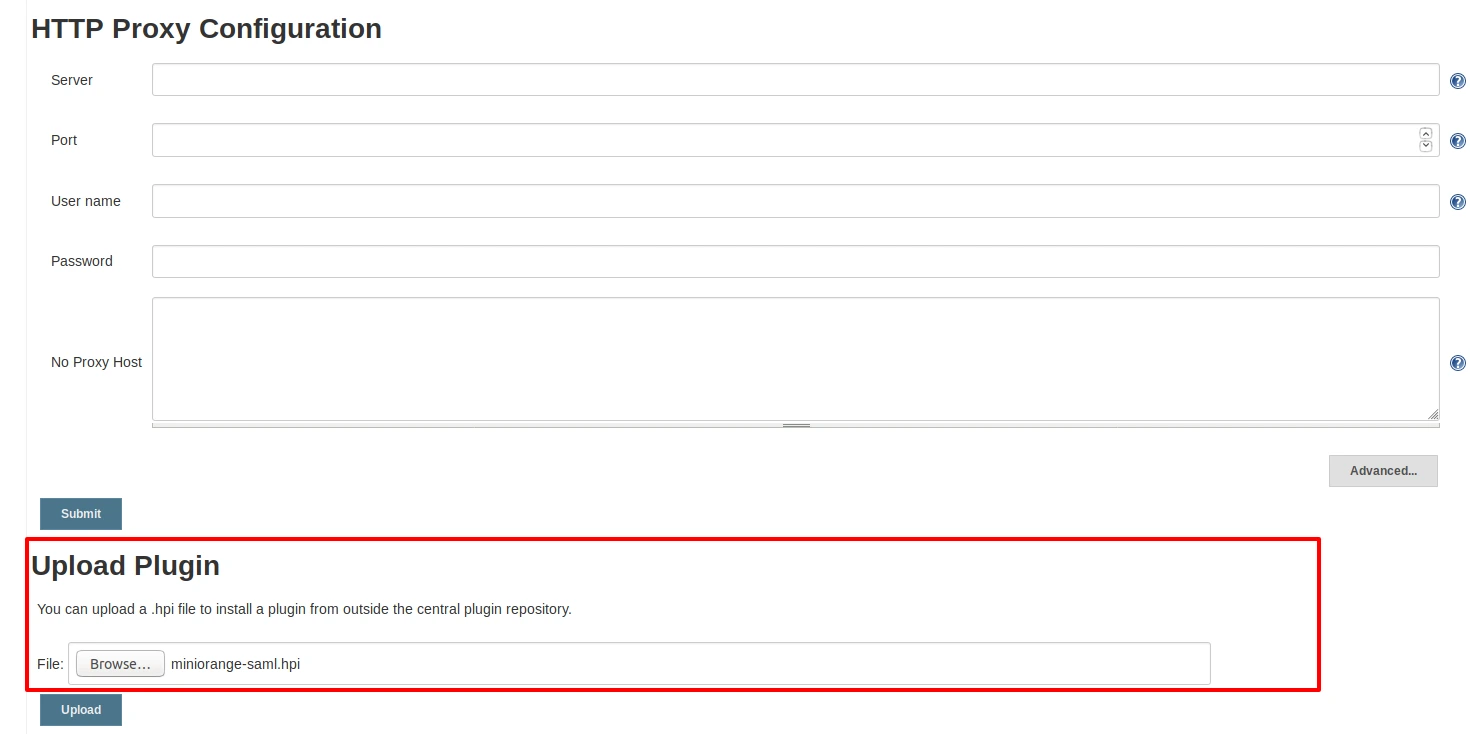
- Go to the advanced tab and upload the hpi file.
- You can get the hpi file by running mvn clean package command on this code. Contact info@xecurify.com if you are facing any issue.
Activate the plugin
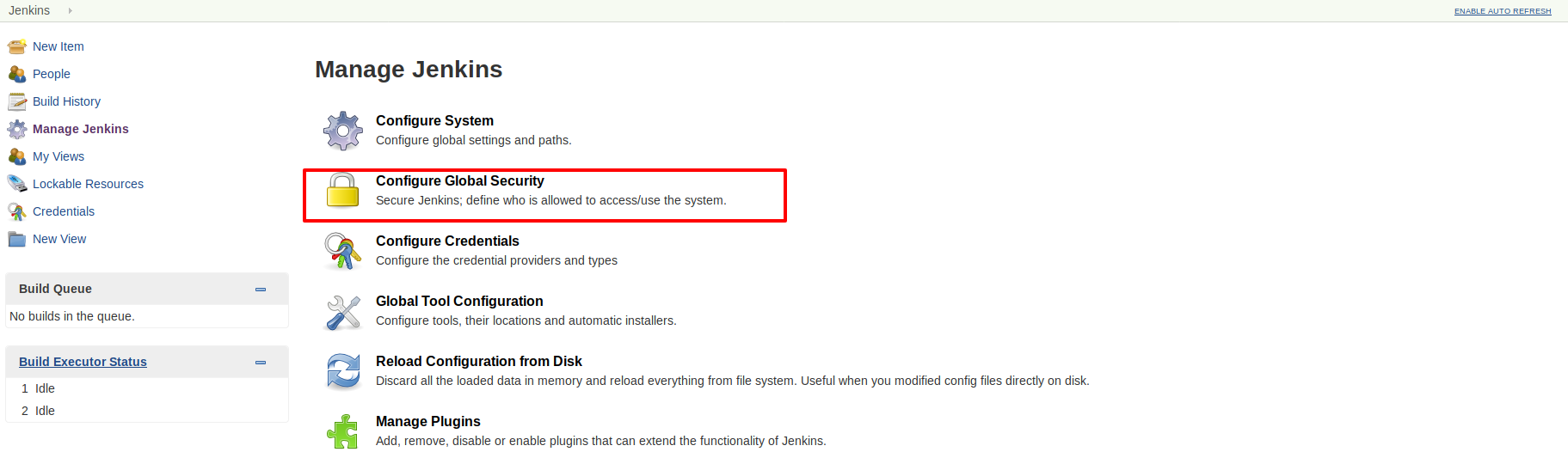
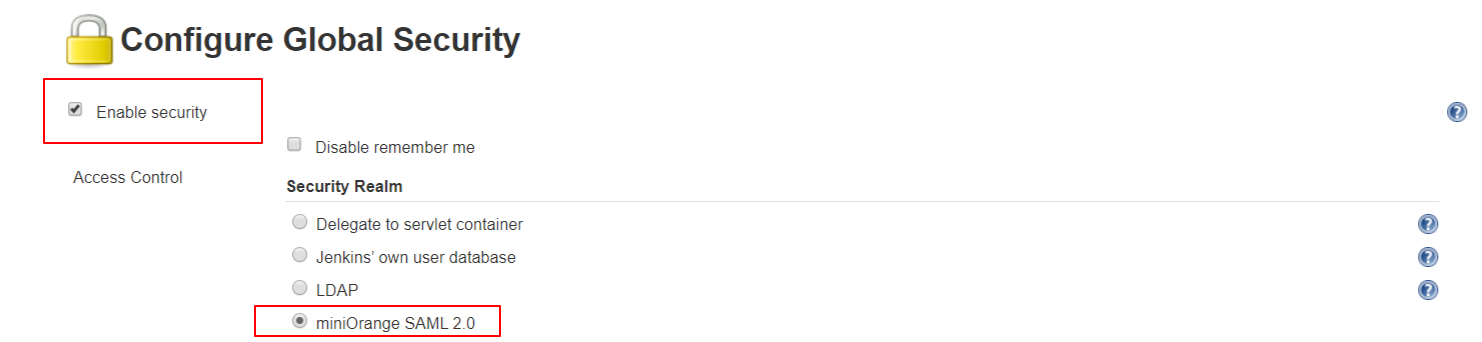
- Open Manage Jenkins and select Configure Global Security.
- Set the Security Realm as miniorange SAML 2.0.
- Make sure that Enable Security checkbox is checked.
Step 1: Setup Identity Provider to enable saml for your module.
Pre-requisite: You will need SAML information from your IDP to configure this app. Please get SAML metadata from your Identity Provider. If your IDP does not have a metadata URL or XML, please ask for the following information:
- Issuer/ Entity ID.
- SAML Login URL.
- SAML Logout URL (only if you want users to logout from IDP when they logout from atlassian application. eg.Jira).
- X.509 Certificate.
- NameID format (optional).
- SAML Login binding type (optional).
- SAML Logout binding type (optional).
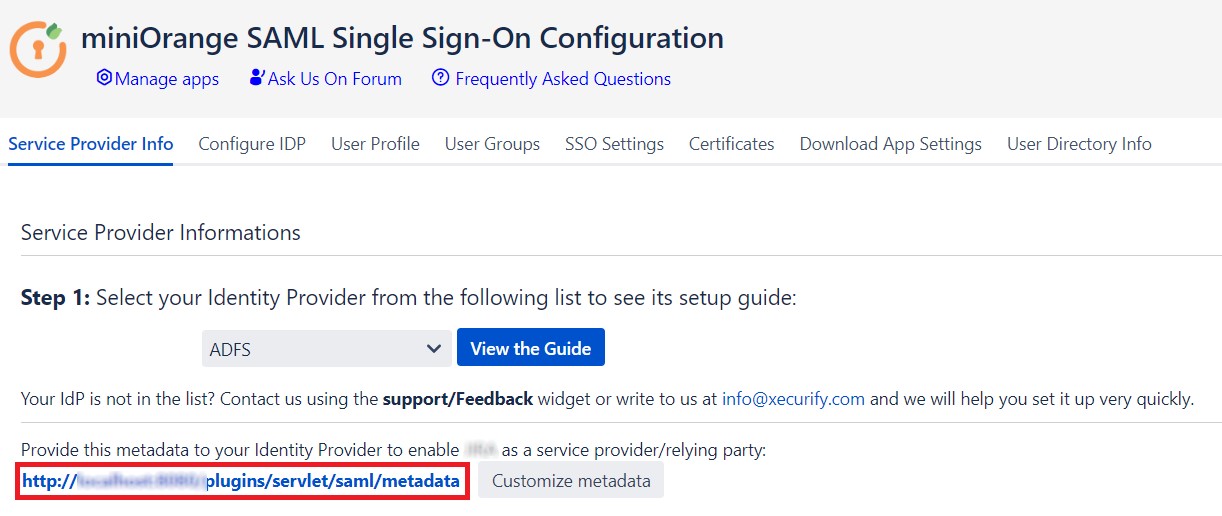
- Provide setup information to your Identity Provider so that they can configure atlassian application as a SAML Service Provider for your account. You can provide them the SAML metadata URL or SAML related information. We have given more information on how you can get each one of them below.
- Go to Service Provider Info and give the link shown below to your Identity Provider. When you click on the link, you will be able to view the metadata for the SAML Single Sign On app.
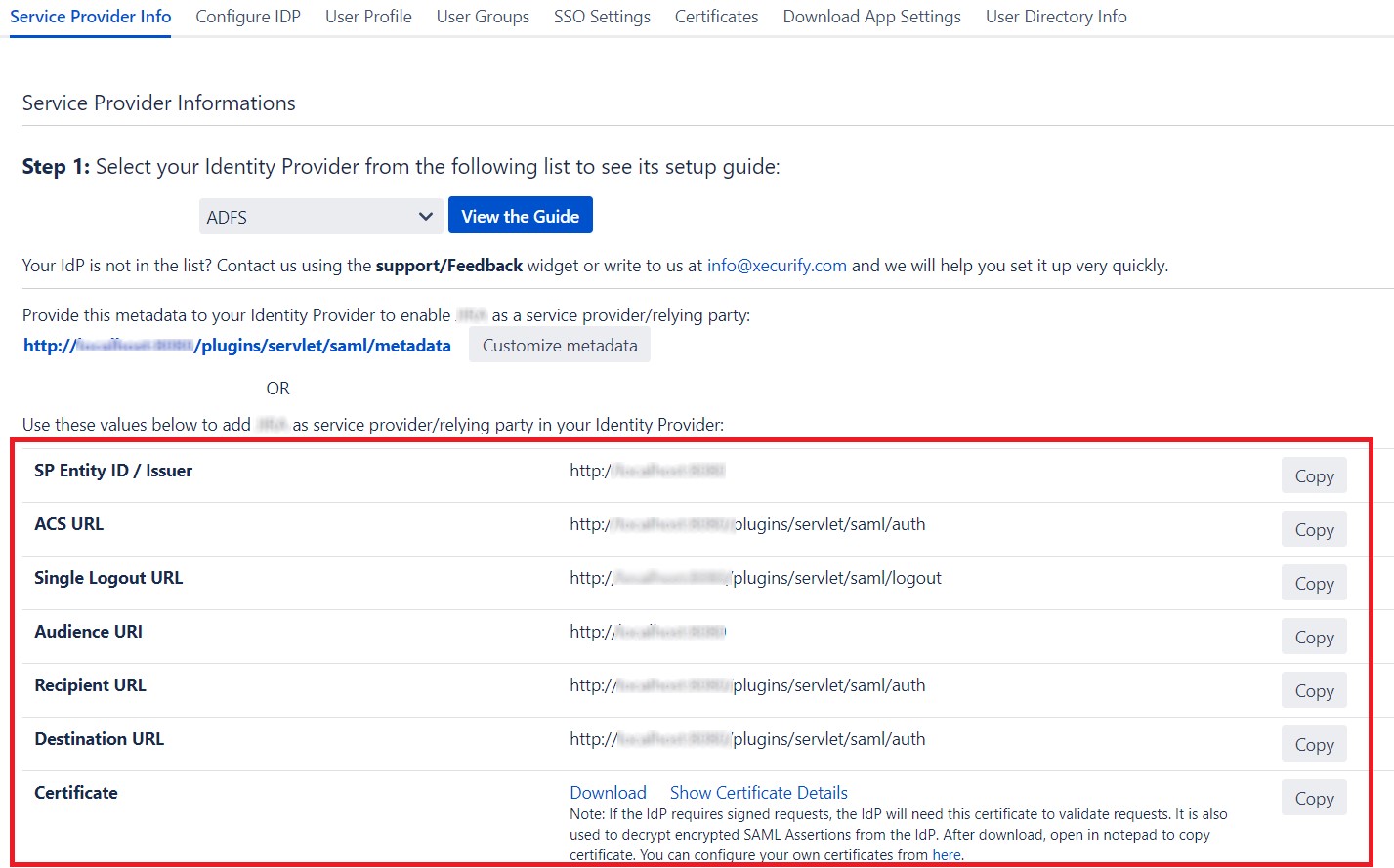
- If the Identity Provider does not accept metadata, you can give them SAML information manually. Go to Service Provider Info tab and get the following information.
| SP Entity ID / Issuer | This value contains unique identifier for your Atlassian application. |
| ACS URL | This is the URL the IdP will return SAML authentication requests to. |
| Single Logout URL | This will terminate all server sessions established via SAML SSO. |
| Audience URI | IdP will prepare SAML authentication requests for. |
| Recipient URL | IdP will return SAML authentication requests to. |
| Destination URL | IdP will return SAML authentication requests to. |
| Certificate | This Certificate is used validate SAML request and used to decrypt encrypted SAML assertions from the IDP. |
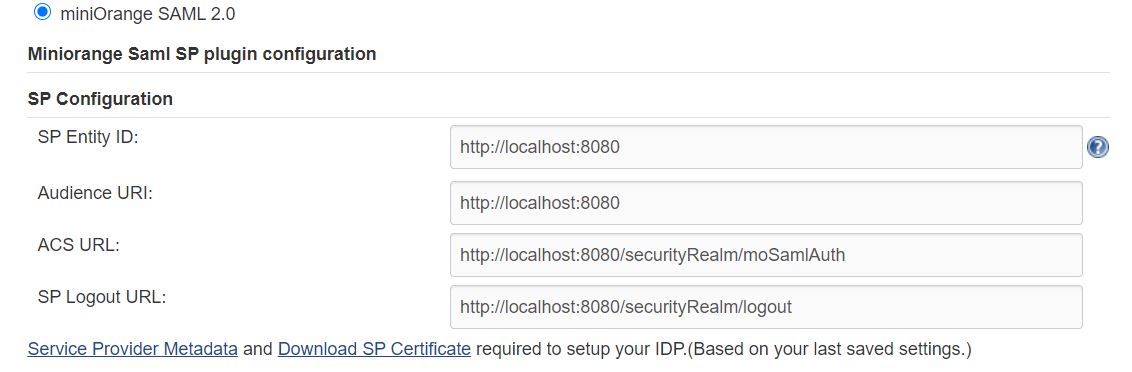
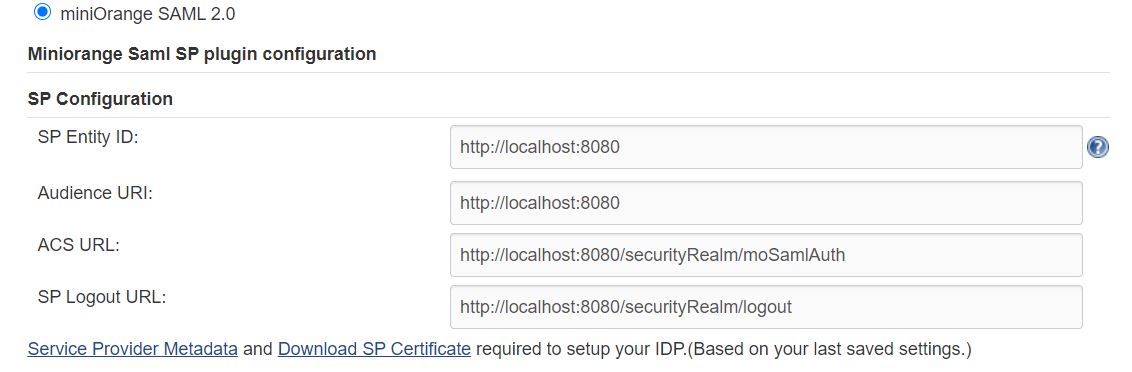
Step 2: Setup Jenkins as Service Provider
You can configure SP settings in IDP in 2 ways:
- By uploading Metadata XML file
- Manual Configuration
- Click on Service Provider Metadata in SP Configuration section.
- Metadata xml file will be downloaded.
- Use this file to setup IDP.
- To Configure SP Settings at IDP copy below URL and paste in respective fields at IDP end.
- SP Entity ID: https://your-jenkins-domain
- Audience URI: https://your-jenkins-domain
- ACS URL: https://your-jenkins-domain/securityRealm/moSamlAuth
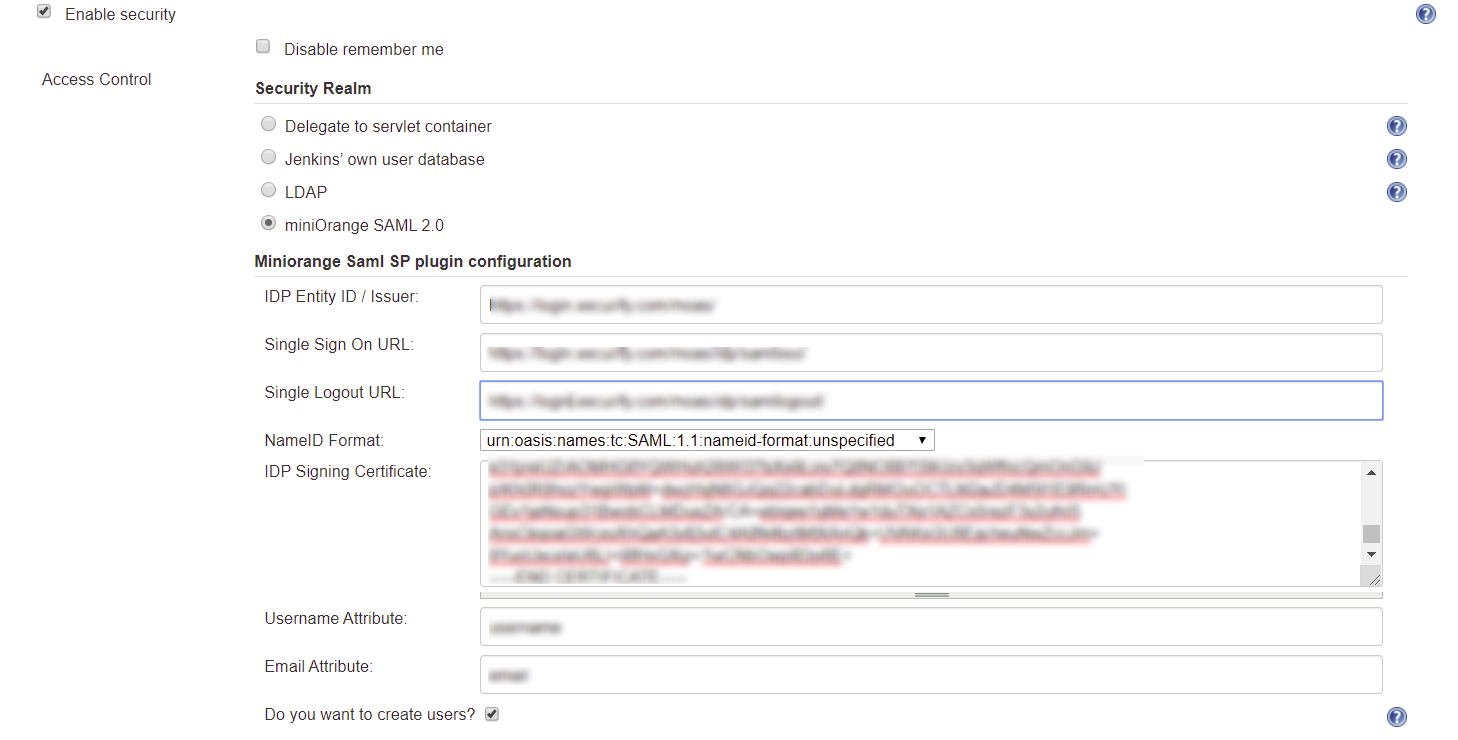
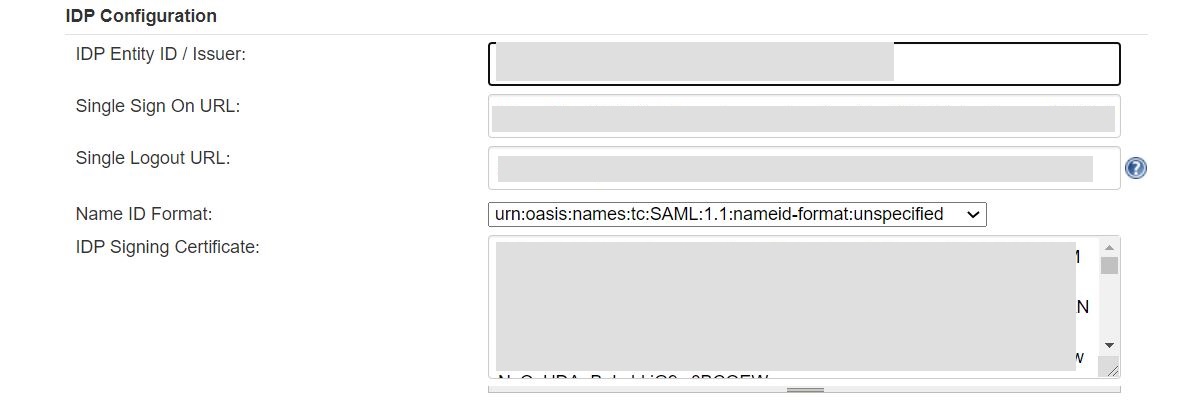
To Configure IDP enter the following details and press apply and save the settings.
- IDP Entity ID
- Single Sign On URL
- Name ID Format
- X.509 Certificate
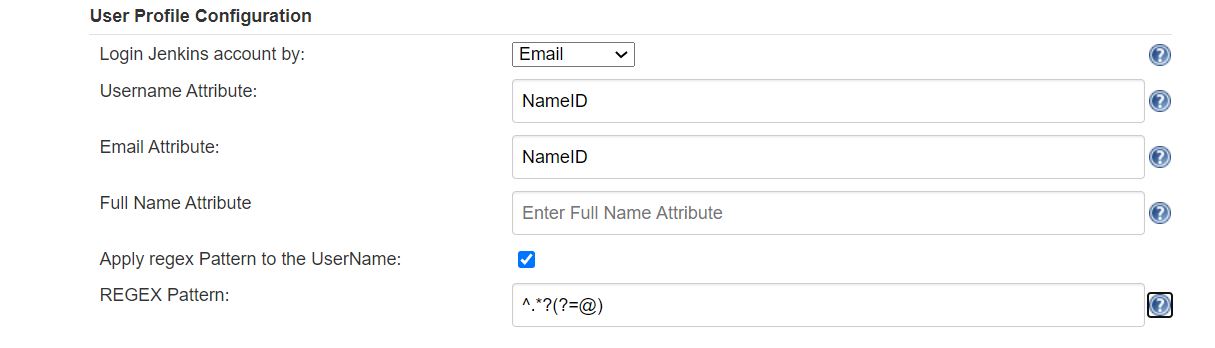
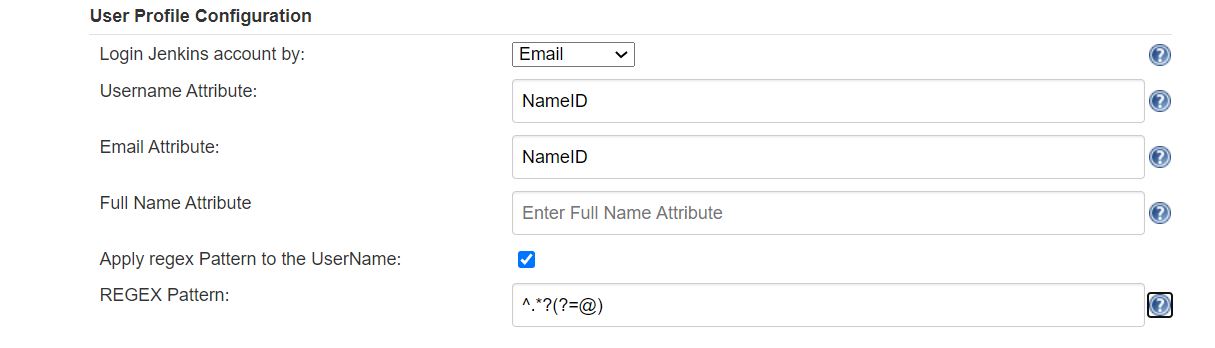
User Profile Configuration
- Select Username or Email for Login Jenkins account by:
- Enter the attribute name from IDP which corresponds to Username in Username Attribute textbox.
- Enter the attribute name from IDP which corresponds to Email in Email Attribute textbox.
- Select the checkbox Apply regex Pattern to the UserNameif the userID returned from SAML is not same as username of Jenkins.
- Enter the regular expression in REGEX Pattern textbox. It will be applied on user ID from SAML Response and will convert it into the username same as Jenkins. For example, you can use regular expression ^.*?(?=@) to extract demo from username demo@example.com
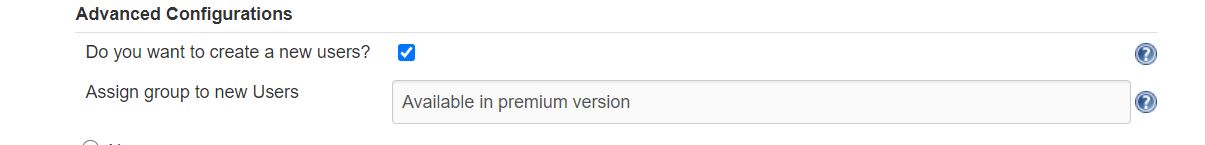
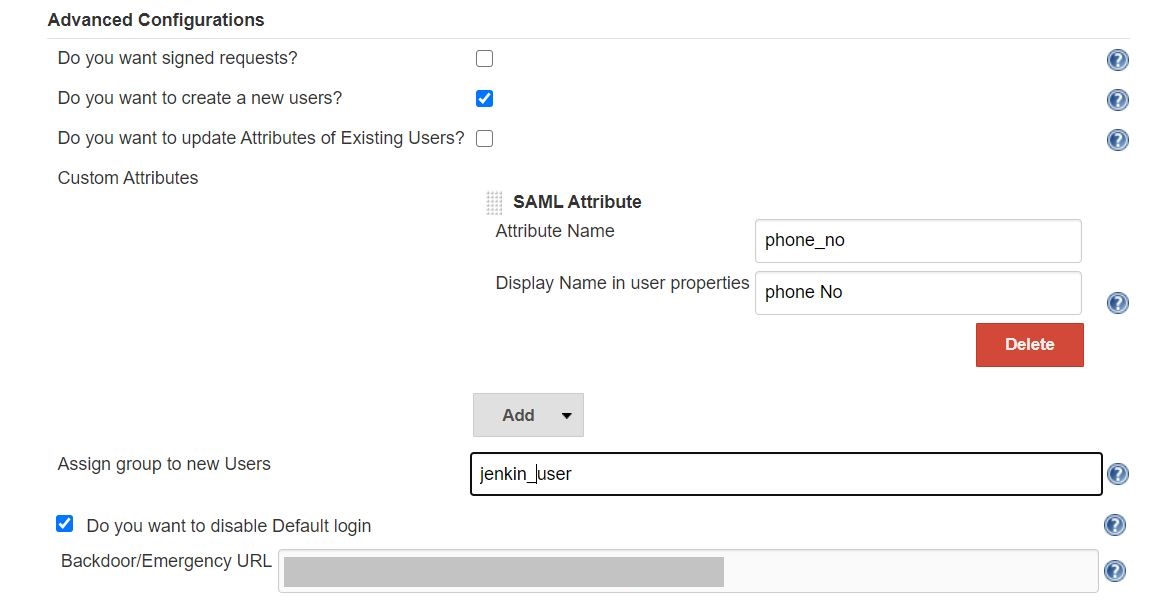
Advanced Configurations
- Select the Do you want to create a new users? to allow user creation through SAML.
You can configure SP settings in IDP in 2 ways:
- By uploading Metadata XML file
- Manual Configuration
- Click on Service Provider Metadata in SP Configuration section.
- Metadata xml file will be downloaded.
- Use this file to setup IDP.
- To Configure SP Settings at IDP copy below URL and paste in respective fields at IDP end.
- SP Entity ID: https://your-jenkins-domain
- Audience URI: https://your-jenkins-domain
- ACS URL: https://your-jenkins-domain/securityRealm/moSamlAuth
To Configure IDP enter the following details and press
- IDP Entity ID
- Single Sign On URL
- Single Logout URL
- Name ID Format
- X.509 Certificate
User Profile Configuration
- Select Username or Email for Login Jenkins account by:
- Enter the attribute name from IDP which corresponds to Username in Username Attribute textbox.
- Enter the attribute name from IDP which corresponds to Email in Email Attribute textbox.
- Enter the attribute name from IDP which corresponds to full name in Full Name Attribute.
- Select the checkbox Apply regex Pattern to the UserNameif the userID returned from SAML is not same as username of Jenkins.
- Enter the regular expression in REGEX Pattern textbox. It will be applied on user ID from SAML Response and will convert it into the username same as Jenkins. For example, you can use regular expression ^.*?(?=@) to extract demo from username demo@example.com
Advanced Configurations
- Select the Do you want signed requests? to send signed login and logout requests. Requests will be signed using public certificate from option Download SP Certificate in SP Configuration section.
- Select the Do you want to create a new users? to allow user creation through SAML.
- Select the Do you want to update Attributes of Existing Users? to update attributes of existing user's each time they sign in Jenkins through SSO.
- To Add custom AttributeS select Add option.
- Set Attribute Name as the one set in IDP eg. lname
- Set display name in user proprties as one you want it appear in jenkins user's config.xml file and in user's configure tab.
- To assign default group to users created through SSO add group name in Assign group to new Users option. Multiple groups can be added using ,(Comma) separater
- If Do you want to disable Default login option is enabled, any unauthenticated user trying to access the default Jenkins login page will get redirected to the IDP login page for authentication. After successful authentication, they will be redirected back to the Jenkins base URL.
- Copy backdoor URL and save it for emergency.
Additional Resources
Bitbucket Git Authentication App | Jenkins SSO | SonarQube SSO
If you are looking for anything which you cannot find, please drop us an email on info@xecurify.com
Need Help? We are right here!

Thanks for your inquiry.
If you dont hear from us within 24 hours, please feel free to send a follow up email to info@xecurify.com
Cookie Preferences
Cookie Consent
This privacy statement applies to miniorange websites describing how we handle the personal information. When you visit any website, it may store or retrieve the information on your browser, mostly in the form of the cookies. This information might be about you, your preferences or your device and is mostly used to make the site work as you expect it to. The information does not directly identify you, but it can give you a more personalized web experience. Click on the category headings to check how we handle the cookies. For the privacy statement of our solutions you can refer to the privacy policy.
Strictly Necessary Cookies
Always Active
Necessary cookies help make a website fully usable by enabling the basic functions like site navigation, logging in, filling forms, etc. The cookies used for the functionality do not store any personal identifiable information. However, some parts of the website will not work properly without the cookies.
Performance Cookies
Always Active
These cookies only collect aggregated information about the traffic of the website including - visitors, sources, page clicks and views, etc. This allows us to know more about our most and least popular pages along with users' interaction on the actionable elements and hence letting us improve the performance of our website as well as our services.
